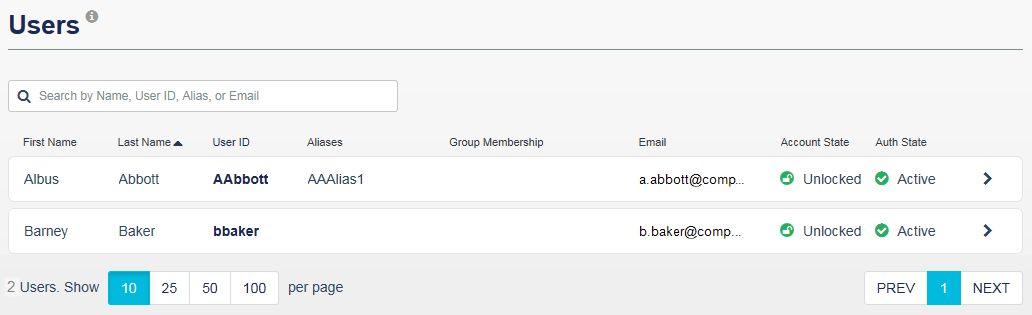
Users on the STA Access Management console
On the STA Access Management console, the Users tab allows you to view information about the users that are configured on the STA Token Management console. On the Users tab, you can search for users and view user details, statistics, and recent access activity.
-
On the STA Access Management console, select the Users tab.
-
To filter the list of users, enter a first or last name, user ID, alias, or email address in the search box.
STA filters the list of users as you type.
A match occurs when the characters that you enter match the first characters in the list of users. For example, if Ashton is in the list of users and you type ash, then Ashton is included in the results. However, if you type sh, then Ashton is not included in the results, unless that user has a name, user ID, alias, or email address that begins with sh.
-
To view a user's details, groups, and applications, select the user and then select the Overview tab.
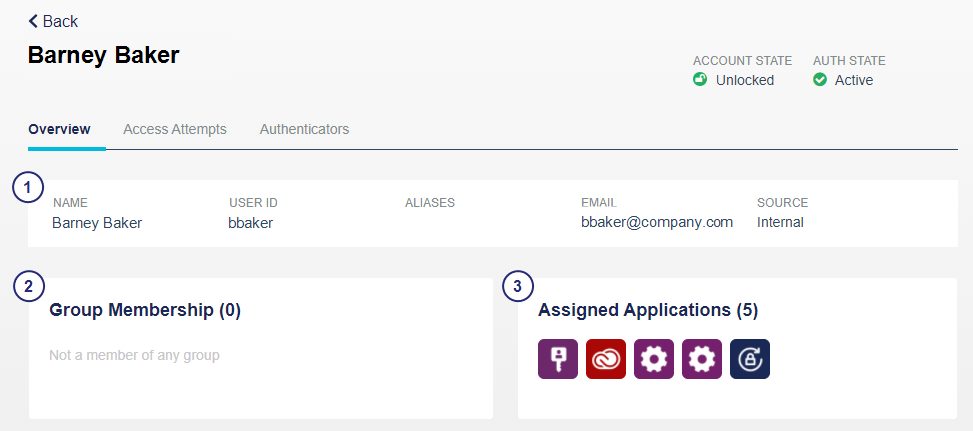

User details:
- The Name, User ID, Aliases, and Email are defined in the user details on the STA Token Management console, in the Assignment tab.
- The Source is one of the following:
- Synchronized when obtained by a SafeNet Synchronization Agent.
- Internal when provisioned in STA.
- Account state is either Locked or Unlocked.
- Authentication State is listed in the following order:
- Locked: Authentication failures exceed the account lockout or unlock policy.
- Active: The user can authenticate against the service.
- Assigned: The user has not yet authenticated with the assigned token.

Group Membership shows the total number and names of the groups to which the user is assigned.

Assigned Applications shows the total number and names of the applications to which the user is assigned.
-
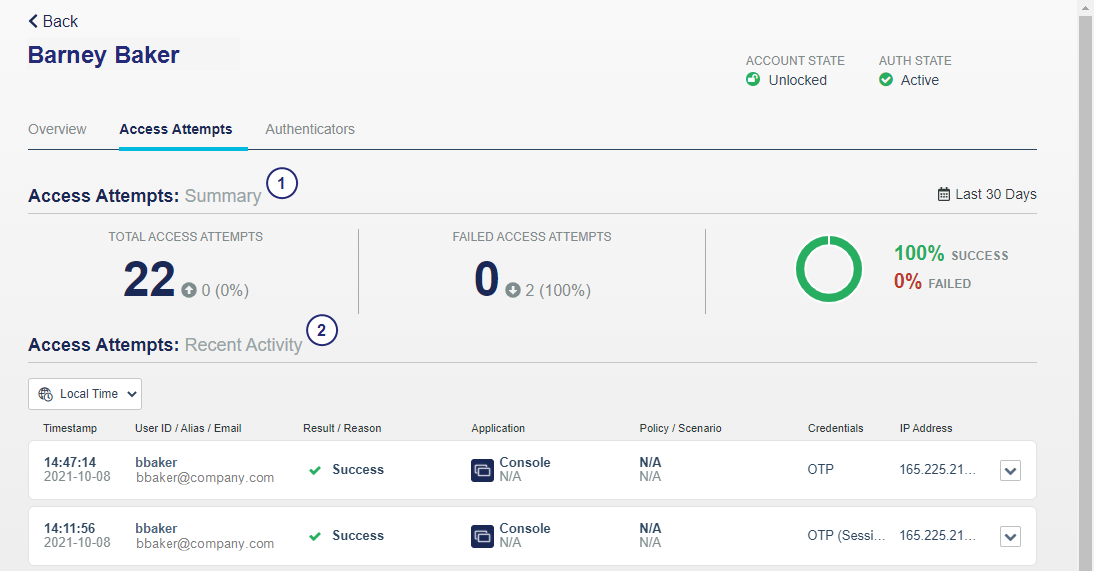
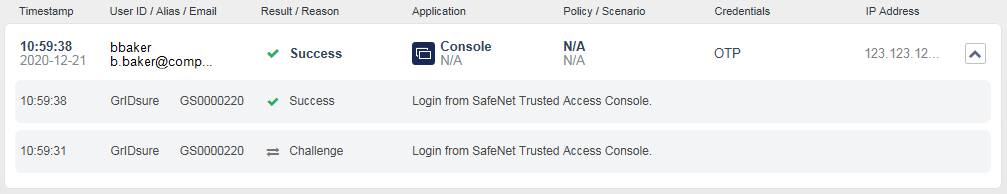
To view a user's access details, select the user and then select the Access Attempts tab.

Access Attempts Summary (last 30 days):
- Total Access Attempts
- Failed Access Attempts
- Percent Success or Failed

Access Attempts Recent Activity displays the access activity for web applications that are configured on the Applications tab. Expand a row to display the associated authentication activity.
The Access Attempts Recent Activity displays the same information as the access logs:
Column Description Timestamp The time of the request is based on the time zone that is configured on the web server that hosts the STA Access Management console.
User ID The identity of the user making the request is defined on the STA Token Management console, on the Users tab.
Result / Reason The result can be Success, Failure, or Denied. For failed or denied requests, the reason is indicated.
Application The application can be either an application name that is specified on the Applications tab, or the resource name that is configured for an auth node.
The access type is also identified. The type can be SAML, OIDC, Agent, or a string that is mapped to an agent ID for auth nodes.
The application icon is displayed for SAML, OIDC, and agents that are configured on the Applications tab. A generic icon is used for RADIUS and auth nodes.
Policy / Scenario The access policy and scenario, which determined the access requirements based on scope and policy matching, and rank, are identified.
Credentials The credentials that were required or used can include OTP, Password, Kerberos, Certificate, and so on.
If the credential requirements are met by an existing SSO session, rather than by the user entering their credentials, this is denoted by (Session). For example, OTP (Session) or Password (Session).
IP Address The public IP address from which the user initiated the access attempt is identified.
If an access attempt was followed by authentication events, then the logs also include each associated authentication event as a child of the access attempt.
-
To view an associated authentication event, expand the access attempt entry. You can expand multiple access event entries at the same time.
You can also view the authentication events in the Authentication Activity module in the STA Token Management console.
-
To view all the authentication events for the user, in the Extended Features menu, select Snapshot > Authentication Activity.
-
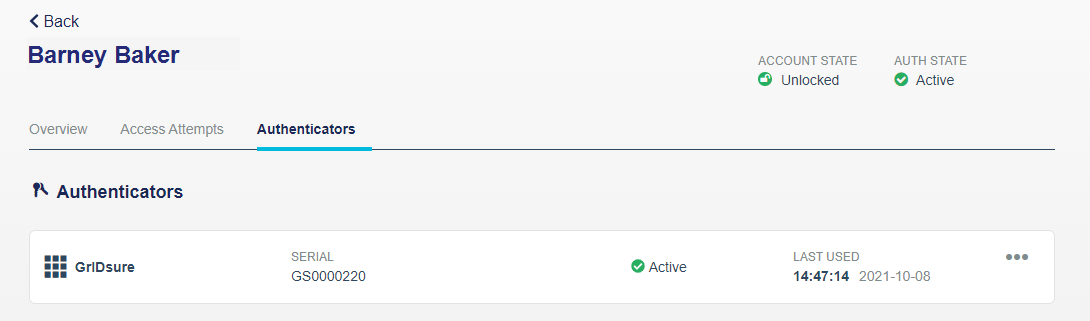
To view a user's authenticator details, select the user and then select the Authenticators tab.
Authenticators include eToken, FIDO, GrIDSure, MobilePASS+, Password, and more.
If you use a global catalog, you must copy the AD maxPwdAge and pwdLastSet attributes to the global catalog. For more information, see https://www.ntweekly.com/2017/10/12/add-attributes-global-catalog-server-windows-server-2016/.
The authenticator states are:
-
Assigned: The token is no longer in inventory. It has either been manually assigned to a user but not activated, or is part of a bulk provisioning operation and has not yet been enrolled by a user.
-
Active: The account is in service.
-
Suspended: The token can be used to authenticate. It is assigned to a user and has been enrolled or used to authenticate.
-
Locked: The token cannot be used to authenticate until the unlock policy is triggered or until the token is reactivated by an operator. This state occurs when a user exceeds the maximum consecutive failed logon attempts threshold. The automatic locking and unlocking of tokens is controlled by the Account Lockout/Unlock Policy.
-
Unavailable: May be used for the expiry date of synchronized passwords.
STA allows users to authenticate using their AD domain password, if configured in the applicable policy, to access cloud applications unless their password is locked, expired, or not synchronized with the AD. When the STA policy requires an AD domain password and the password has expired, STA prompts for the password but denies the access request. The access logs display the outcome as:
-
Result=Failed
-
Reason=Expired password
-
Credentials=Password
-
-
To delete a FIDO authenticator, select the
 icon for the FIDO authenticator and then select Delete.
icon for the FIDO authenticator and then select Delete. -
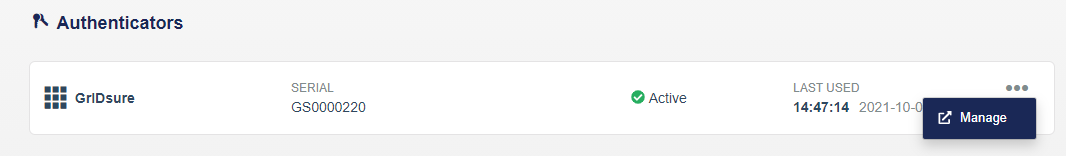
To manage non-FIDO authenticators, select the
 icon for the authenticator and then select Manage.
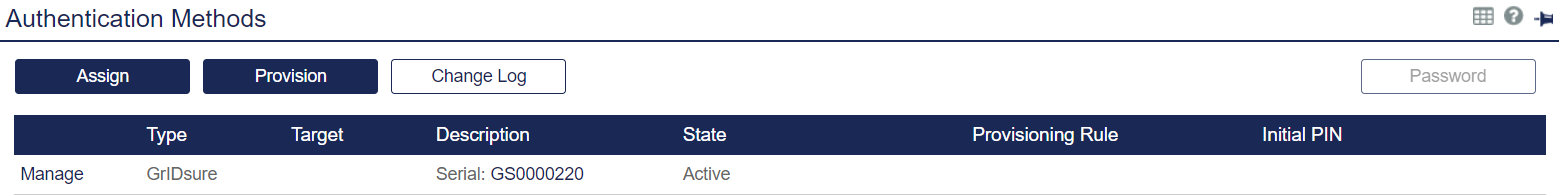
icon for the authenticator and then select Manage.The Authentication Methods module for the user displays.
See Manage tokens for a user for details about managing authenticators.