Token templates
Token templates provide the operating parameters, such as passcode or PIN strength, for a token. The templates are applied every time a token is enrolled.
The operating parameters in a template vary depending on the token type. In addition, the selection of one option may affect the availability of another option.
Token templates are provided for the following token types:
- eToken
- GOLD
- Google Authenticator
- GrIDsure
- KT-1
- KT-2/3
- KT-4
- KT-5
- Legacy 6.X
- MobilePASS
- OATH
- RADIUS
- RB
- SecurID
- SMS
Legacy 4.X and 5.X token types are no longer supported in STA cloud environments. To continue using STA cloud services, migrate to a supported token type.
By default, all tokens use AES 256-bit encryption. Certain third-party tokens use 3DES or OATH. STA applies the strongest algorithm that the token type supports.
You can customize the token templates, and therefore token operation, to adapt to changes in your security policy. Customizing a template does not affect tokens that are already initialized and does not affect tokens that are assigned to users.
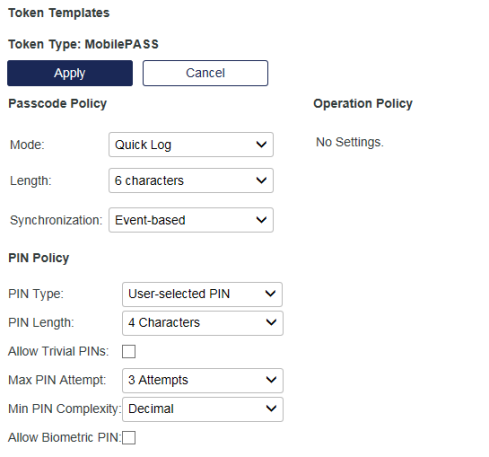
The operating parameters in a template vary depending on the token type. The token templates can include the following parameters:
Passcode policy parameters
| Parameter | Description |
|---|---|
| Mode | Tokens can operate in either Challenge-Response or Quick Log mode. Quick Log mode is recommended because it greatly simplifies the User logon experience and strengthens security by eliminating the requirement to have the user key a challenge into a token to get an OTP. Default value: Quick Log. |
| Complexity | The OTPs generated by the token can be comprised of numbers, letters, and additional characters as follows:
|
| Encryption | This option determines the hashing algorithm used for signing:
|
| Length | This option determines the number of characters displayed as the OTP. Options are 5, 6, 7 or 8 characters. For software tokens, the default is 6 characters, although 8 can be configured by request. For hardware tokens, the default depends on how they are programmed in the factory or during operator token initialization. |
| Synchronization |
|
| Display Mask | If set to Telephone Mode, the fourth character of the OTP will always be a dash (“-“). Typically, this is used with a decimal OTP, length of 8. Example OTP: 123-5678. If set to None, the fourth character is unmodified. Example OTP: 12345678. Telephone mode can be used with any token complexity and length setting. Default value: None. |
| Password/Cycle | This option is used in conjunction with Operation Policy (Manual Shut-Off, Auto Shut-Off). Tokens can be limited to generating 1 password per cycle or allow multiple passwords to be generated in a cycle. Default value: Single. |
Operation policy parameters
| Parameter | Description |
|---|---|
| Manual Shut-Off | If Enabled, the user can clear the OTP from the display and turn the token off at any time by pressing the appropriate button, depending on the token type. If Disabled, the OTP will be displayed until the Auto Shut-off value expires. Default Value: Disabled. |
| Auto Shut-Off | This value determines the length of time the password will be displayed, 30, 60 or 90 seconds. On expiration of this value, the token automatically clears the display and shuts off. Default Values: 60. |
For tokens with a No PIN or Server-side PIN policy, the selection of Single in combination with Manual Shut-Off set to Disabled means that the token will not generate another password until the Auto Shut-Off value has expired. For example, if the value is 60 seconds, the user must wait 60 seconds before another password can be generated.
For tokens with a Fixed or User selected PIN, selection of Manual Shut-off set to Disabled means that the token will not generate another password until the Auto Shut-Off value has expired and the user enters their PIN into the token.
Thales recommends using the Operation Policy Group default settings for RB and KT series tokens configured for QUICKLog operation. Doing so ensures that the user must wait at least 60 (default) seconds before the token will generate another passcode.
PIN policy parameters
| Parameter | Description |
|---|---|
| PIN Type | This setting determines the type of PIN to be used with the token:
Server-side PINs require the user to append or prepend the PIN to the token generated password during login, allowing the PIN to be evaluated by the Virtual Server. For example, if the user PIN is ABCD, and it must be prepended to the password 12345678, the user would enter ABCD12345678 at the password prompt. All other PIN types require the user to key the correct PIN into the token before a password is generated. In this case, the user provides only the password at the password prompt. For example, if the user PIN is 8432 and the password is 12345678, the user will enter 12345678 at the password prompt. Generally, server-side PINs are used with KT tokens. |
| Initial PIN | Determines the nature of the initial PIN created for a token during initialization. If Random, SafeNet Trusted Access will generate a random PIN that conforms to the minimum PIN Policy options set in the drop-downs for this group for each token during initialization. If Fixed, all tokens will be initialized with the same PIN. Default value: Random |
| Min. PIN Length | Determines the minimum PIN length that can be used with the token.
|
| Allow Trivial PINs | If enabled, a PIN may be three or more consecutive numbers (for example, 1234), or three or more identical digits (for example, 2222). Default value: Cleared. |
| Max. PIN Attempts | Determines the maximum number of consecutive failed PIN attempts permitted by the token. If this number is exceeded, the token will enter the Locked state and cannot be used for authentication until it is reinitialized. This option is available only if PIN Type is set to Fixed PIN or User selected PIN. |
| PIN Complexity |
|
| Allow Biometric PIN | If enabled, subscribers can use a fingerprint sensor or facial recognition instead of typing a PIN to access their MobilePASS+ token. Default value: Disabled. This option requires that:
The Biometric PIN (Touch ID for iOS devices or Windows Hello for Windows devices) policy setting on STA is applied to tokens at the time of enrollment only. After a token is enrolled, policy changes on STA do not affect the availability of the Biometric PIN feature on that token. |
Edit a token template
-
On the STA Token Management console, select Policy > Token Policies.
-
Click Token Templates.
-
Select a token Type.
-
Click Edit and modify the settings, as needed.
-
Click Apply to apply changes to the template.
Changes to the template are applied to tokens during initialization. Previously initialized tokens are not affected by later changes to a template.

