SafeNet Synchronization Agent
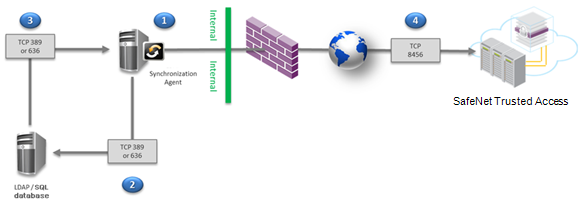
SafeNet Synchronization Agent simplifies user creation in SafeNet Trusted Access (STA) and SafeNet Authentication Service Private Cloud Edition (SAS PCE). Without the agent, the administrator must manually input user information via the web-based management interface. With SafeNet Synchronization Agent, Lightweight Directory Access Protocol (LDAP), or Structured Query Language (SQL) user groups are monitored for membership changes and user information updates are automatically made in STA and SAS PCE.
-
The client organization:
-
Installs SafeNet Synchronization Agent within their secure network on a server that is separate from their LDAP or SQL directory server.
-
Imports an encrypted key file into SafeNet Synchronization Agent.
-
Configures a connection between its LDAP or SQL directory server and the agent.
-
Configures the agent with a list of the user groups in the LDAP or SQL directory server that are to be synchronized with STA or SAS PCE.
-
-
The agent queries the LDAP or SQL directory server for all users within the configured groups.
-
The LDAP or SQL directory server transmits details of the users within the configured groups to the agent. The agent stores these details.
-
When the synchronization service is started, the agent pushes all user and group information to STA or SAS PCE. The agent queries the organization’s LDAP or SQL directory server periodically (by default, every 20 minutes). When a change to the organization’s users or groups is detected, the agent updates STA or SAS PCE.
SafeNet Synchronization Agent features
Most organizations maintain information about their users and groups in an SQL database or in an LDAP directory such as Active Directory (AD). SafeNet Synchronization Agent auto-populates STA or SAS PCE with that information.
Key features of SafeNet Synchronization Agent include the following:
-
Can be used directly with common user repositories
-
Can accommodate custom schemas for most LDAP and SQL directory servers
-
Does not write to the user source
-
Does not require an administrator account to connect to the user source
-
Can synchronize multiple user sources, such as multiple LDAP or SQL directory servers
-
Uses AES encryption between SafeNet Synchronization Agent and STA or SAS PCE
-
Supports SSL between SafeNet Synchronization Agent and the LDAP or SQL directory server
-
Supports optional domain password synchronization from AD user sources
SafeNet Synchronization Agent environment
| Environment | Description |
|---|---|
Supported Platforms |
|
| Additional Software Components |
|
Network Ports |
|
LDAP Directory Server Access or SQL Access |
|
Active Directory Server Access (for optional domain password synchronization) |
|
Supported LDAP or SQL User Groups |
|
Supported LDAP Directory Servers |
|
Supported SQL Servers |
|
High availability recommendations
A high availability configuration with multiple Synchronization Agents ensures there is no single point of failure. Your configuration should include:
-
Multiple Synchronization Agents with identical schema and group configurations
-
Identical content among the LDAP servers that are configured
If agent configurations are not synchronized or the contents of the LDAP directory servers differs, the synchronization agents will work against each other, as all agents are active. Active/passive configuration is not available.

