SafeNet MobilePASS+ for iOS
Product Description
SafeNet MobilePASS+ for iOS is a mobile client application enabling you to access corporate and web-based resources securely. It eliminates the need to remember complex passwords. SafeNet MobilePASS+ for iOS is a cost-effective way for businesses to leverage the security of One Time Passwords (OTP) using mobile phones. Associated with STA, the SafeNet MobilePASS+ for iOS application is a perfect combination of security and convenience. It offers a simple user experience for authenticator activation and authentication using the Push OTP mechanism.
For a list of existing issues as of the latest release, refer to Known Issues.
Release Description
01/13/2026
SafeNet MobilePASS+ for iOS v3.0.0 introduces the following changes:
- Authenticate with device-bound passkeys for a modern, FIDO2-based, phishing-resistant experience.
- MobilePASS+ is FIPS 140-3 compliant.
- Automatically label tokens with their Tenant ID for clear, secure multi-tenant token management.
- Third-party enrollment link: Enroll OTP tokens via a secure, clickable link, no QR code required, using standard otpauth URLs.
- Third-party authenticator device transfer or restore: Securely transfer or restore third-party authenticator tokens when users change devices.
07/28/2025
SafeNet MobilePASS+ for iOS v2.6.2 introduces the following changes:
- Privacy policy: Added link to the privacy policy in the application settings.
06/18/2025
SafeNet MobilePASS+ for iOS v2.6.1 introduces the following changes:
- Firebase Dynamic Link Replacement: Added support for new QR codes to handle the deprecation of Firebase Dynamic Links in August (https://firebase.google.com/support/dynamic-links-faq).
- Accessibility Improvements: Updates for accessibility on devices using screen readers and large text.
- Legal Notices: Added links to legal notices in the application settings.
- Maintenance: Bug fixes and security improvements.
07/15/2024
SafeNet MobilePASS+ for iOS v2.6.0 introduces the following features and resolves the issues listed below:
-
MobilePASS+ Secure Screen: Allows users to add an additional layer of protection by using device biometric authentication to open MobilePASS+ app. When enabled, MobilePASS+ uses Face ID or Touch ID to open the app and whenever a login request requires it.
-
Authenticator Search: Allows users to search for authenticators within MobilePASS+. The search option appears in the app when a user has five or more authenticators in MobilePASS+.
| Issue | Synopsis |
|---|---|
| SASMOB-5595 | Auto unlock doesn't always happen when relaunching the app from the background. |
| SASMOB-4841 | Touch ID authentication dialog sometimes repeatedly pops up when unlock a token. |
| SASMOB-4837 | Authentication dialog comes on top of QR view after the app is brought from background. |
| SASMOB-4193 | Responding to push authentication on a deleted authenticator does not display a toast message as described. |
| SASMOB-4159 | Summary: The app crashes when placed in the background during enrollment of a server PIN token. |
02/27/2024
SafeNet MobilePASS+ v2.5.4 resolves the following issue:
| Issue | Synopsis |
|---|---|
| SASMOB-6146, SASMOB-6112 | Third-party authenticators are now correctly enrolled in MobilePASS+. |
11/27/2023
This service pack release of STA introduces the following feature:
-
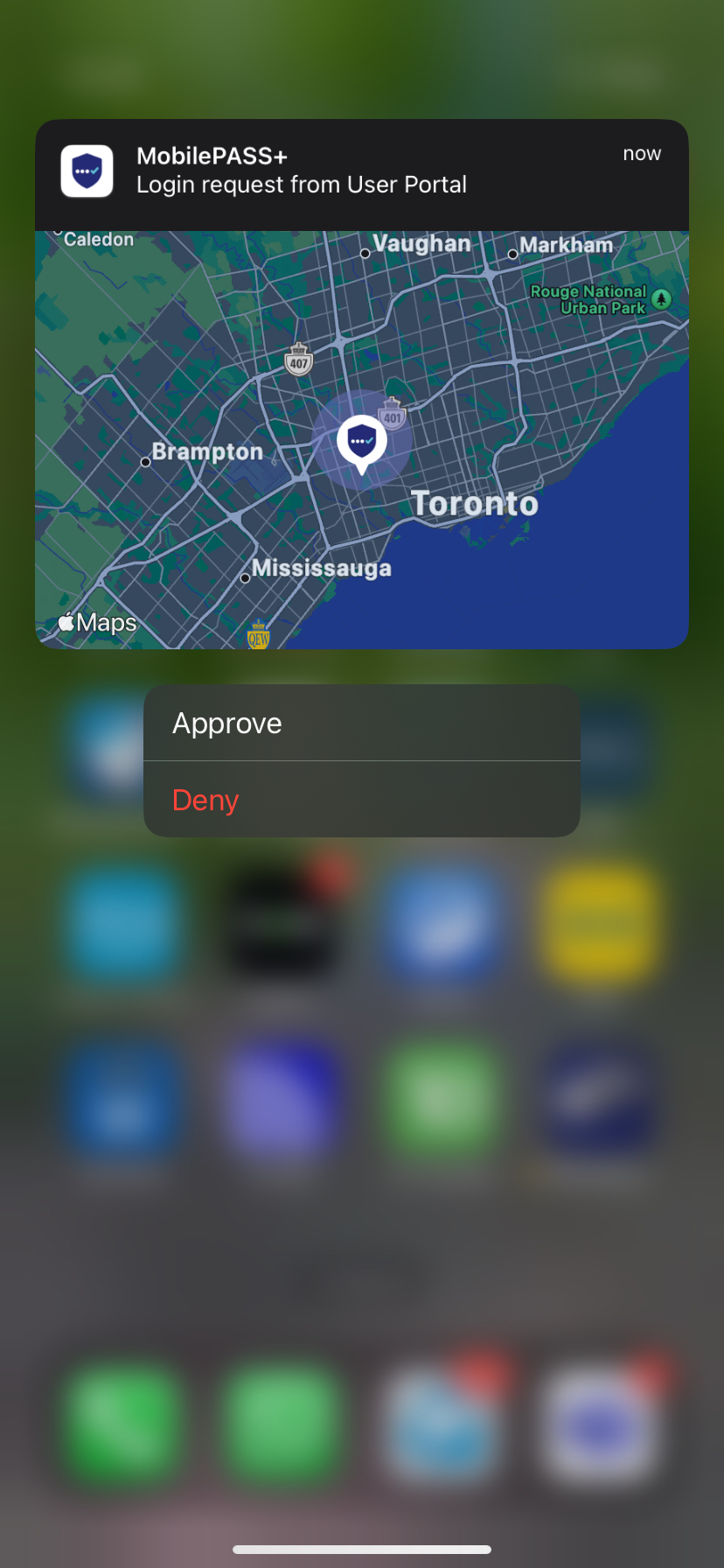
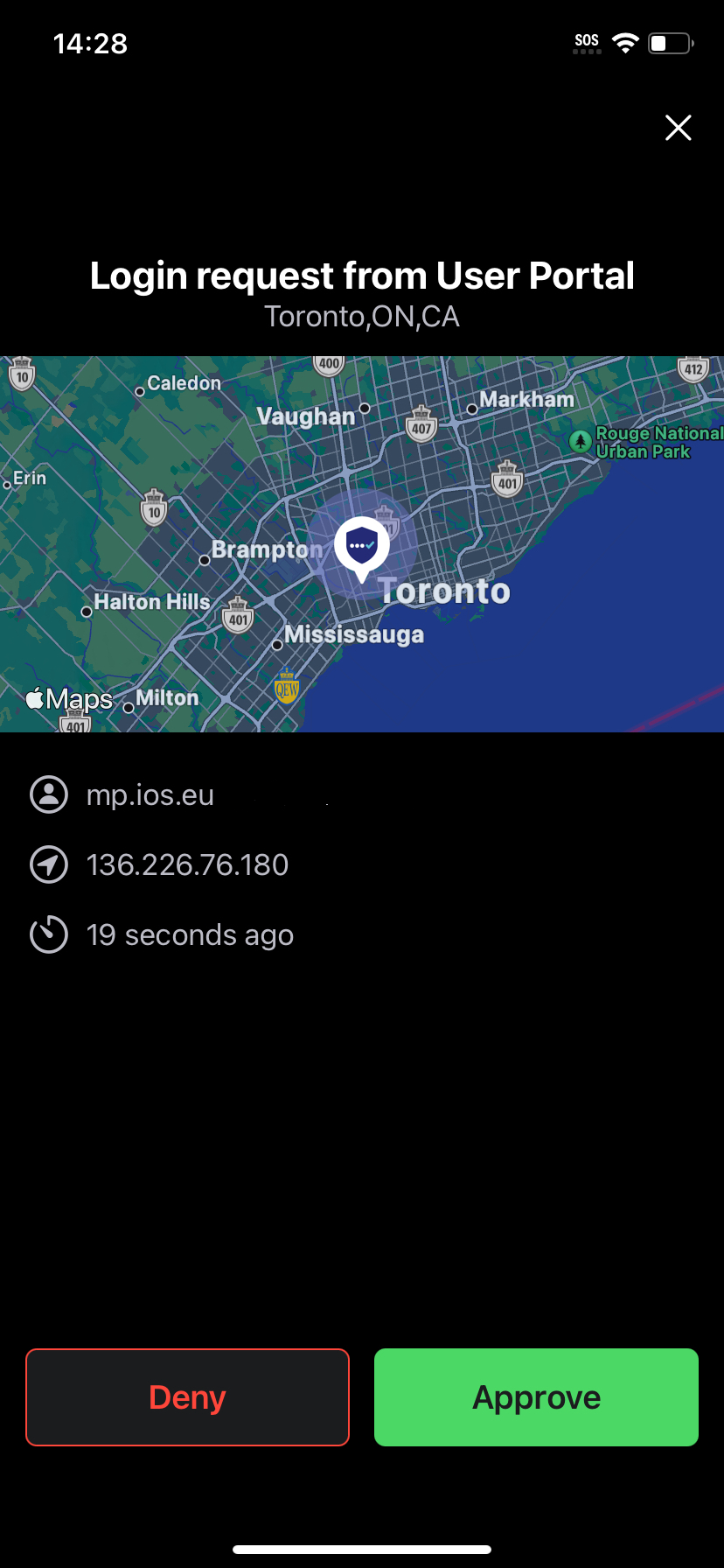
Visual location display in MobilePASS+ push notifications: This feature displays a live map within push notifications to help the user identify any fraudulent push requests. Push notifications show the location from where the authentication attempt was made. Support for displaying maps is available in MobilePASS+ v2.4 and later.
09/15/2023
SafeNet MobilePASS+ for iOS v2.5.3 resolves the issue listed below.
Users are advised to first update to MobilePASS+ for iOS v2.5.3, launch the application or perform a push authentication, and only after that update to iOS 17.
| Issue | Synopsis |
|---|---|
| SASMOB-5863 | MobilePASS+ launches and generates OTPs as expected after the iOS 17 update. |
08/08/2023
SafeNet MobilePASS+ for iOS v2.5.2 resolves the following issue:
| Issue | Synopsis |
|---|---|
| SASMOB-5905 | MobilePASS+ enrollment proceeds correctly in custom domains. |
07/27/2023
SafeNet MobilePASS+ for iOS v2.5.1 resolves the following issue:
| Issue | Synopsis |
|---|---|
| SASMOB-5901 | MobilePASS+ push notifications correctly display the Approve and Deny buttons. |
07/26/2023
SafeNet MobilePASS+ for iOS v.2.5.0 introduces the following feature:
- MobilePASS+ push with number matching: Number matching in MobilePASS+ secures push authentications to protect against MFA fatigue or push bombing attacks. Number matching gives control to the user for every login request, because they must select the number that appears during authentication. Refer to the documentation for details about how to enable this feature.
This feature is available only for MobilePASS+ v2.5.0 onwards.
04/27/2023
SafeNet MobilePASS+ for iOS v2.4.0 introduces the following features:
-
Third-party authenticator support with MobilePASS+: Allows users to enroll third-party authenticators for different web applications to protect their personal and professional accounts. See the documentation for details.
-
Improved logging: Enhanced logging and error codes in MobilePASS+ for better troubleshooting and investigation.
01/31/2023
SafeNet MobilePASS+ for iOS v2.3.1 resolves the following issue:
| Issue | Synopsis |
|---|---|
| SASMOB-5114 | MobilePASS+ for iOS enrollment works correctly now. |
06/28/2022
SafeNet MobilePASS+ for iOS v2.3.0 introduces the following features:
-
Standards-based accessibility support: Enhanced accessibility support provides full functionality of SafeNet MobilePASS+ via voiceover, narrator, or keyboard navigation based on WCAG standards.
-
Italian language support
04/21/2022
SafeNet MobilePASS+ for iOS v2.2.1 resolves the following issue:
| Issue | Synopsis |
|---|---|
| SASMOB-4761 | MobilePASS+ token enrollments proceed correctly on the latest iPad OS versions. |
04/18/2022
SafeNet MobilePASS+ for iOS v2.2.0 introduces the following feature:
- Support for Apple Watch – MobilePASS+ for iOS now supports Apple Watch to run as a companion app, allowing users to respond to push authentication requests and generate OTPs on the watch. Apple Watch wrist detection capability is used as a second biometric authentication factor.
10/12/2021
SafeNet MobilePASS+ for iOS v2.1 introduces the following feature and resolves the issue listed below:
- Dutch language support
Resolved Issue
| Issue | Synopsis |
|---|---|
| SASMOB-4206 | Voice-over functions correctly. |
08/30/2021
SafeNet MobilePASS+ for iOS v2.0 introduces the following features:
-
Enhanced user experience - Next generation mobile authenticator offering the best-in-class user-experience and native user interface for each platform.
-
Language support for German, Chinese, and simplified Chinese - SafeNet MobilePASS+ for iOS now supports German and Chinese in addition to the existing supported languages.
-
Risk Detection – Monitors and displays risk parameters associated with SafeNet MobilePASS+ for iOS devices in the customer’s environment. These parameters include OS jailbreak and root status, OS versions in use, possible application tampering, and malware intrusion in order to detect potential risk to the authenticator's integrity. Refer to the documentation for further details.
-
Push Authentication History - Users can now access their push authentication history on SafeNet MobilePASS+ for iOS under the authenticator settings.
-
Support for Dark Mode - SafeNet MobilePASS+ for iOS now supports dark mode when it is enabled on the user’s mobile device.
-
Unlimited Authenticators - SafeNet MobilePASS+ for iOS no longer limits the number of authenticators that can be enrolled.
Any user-PIN/biometric-PIN enabled tokens enrolled before SafeNet MobilePASS+ for iOS 1.7.0 must be unlocked between v1.7.0 and v1.9.1 at least once before upgrading to SafeNet MobilePASS+ for iOS 2.0 to ensure the successful migration of existing tokens.
Advisory Notes
Working with SafeNet MobilePASS and SafeNet MobilePASS+
SafeNet MobilePASS for iOS and SafeNet MobilePASS+ for iOS can be used on the same device and with the same virtual server. Token enrollments are for either SafeNet MobilePASS for iOS or SafeNet MobilePASS+ for iOS. This is controlled in STA at the virtual server level.
Push OTP
Approving a Push OTP Login Request
SafeNet MobilePASS+ for iOS tokens that are not PIN protected or are configured to work with a server-side PIN can be configured to use the Enhanced Approval Workflow.
The Enhanced Approval Workflow is not available for user-selected PIN protected tokens or for tokens that are not configured to support the workflow.
When the Login request arrives on your mobile device, you can respond from the locked screen or from the SafeNet MobilePASS+ for iOS application.
| Token Configuration | Notification Location | Action to Approve the Push OTP Login Request |
|---|---|---|
| Approving a Push OTP Login Request with standard approval workflow | iOS Locked Screen | Do one of the following:
|
| iOS Unlocked Screen or within another Application |
|
|
| Approving a Push OTP Login Request with Enhanced Approval Workflow | iOS Locked Screen |
|
| iOS Unlocked Screen or within another Application |
|
|
| SafeNet MobilePASS+ for iOS Application | In the Login Request Form window, tap Approve. |
Configuring STA for Enhanced Approval Workflow
To maintain compatibility with SafeNet MobilePASS+ Android and iOS versions earlier than 1.4, do not select Enhanced Approval Workflow.
To enable Enhanced Approval Workflow:
-
In the STA Token Management console, select VIRTUAL SERVERS > POLICY > Token Policies > Software Token & Push OTP Settings.
-
Select Enhanced approval workflow and click Apply.
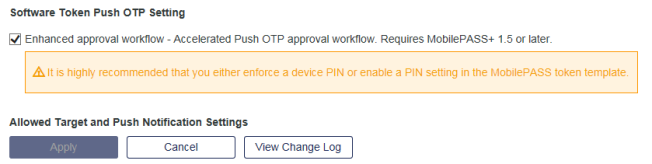
Conditions that will trigger Enhanced Approval Workflow on a mobile device:
-
Enhanced Approval Workflow must be enabled on the server
-
The mobile device must be running iOS 10 or later
-
The mobile device must be provisioned with one token only on the server-side
-
The token must not have a user-PIN
Push OTP Troubleshooting
If an expected push OTP request does not arrive on your mobile device, check that a network connection is present. Heavy traffic and/or service outages from the public push service provider (Apple) may result in delivery delays or disruptions. In such circumstances, use manual OTP generation to complete the authentication.
Configuring STA for QR Code Enrollment
-
In the STA Token Management console, select VIRTUAL SERVERS > POLICY > Automation Policies > Self-Enrollment Policy.
-
Select Enable Multi-Device Instructions.
-
Select Display QR Code.
-
Click Apply.
The enrollment email sent to the user will include a link to the page on the STA Self Service Module where the QR code is displayed.
The QR code will display only if a supported device is selected in the device selection drop down menu.
Biometric PIN
Biometric PIN Prerequisites
-
iOS 13 or later
-
Token configured in STA for biometric PIN
Activating Biometric PIN in Existing Tokens
Tokens previously enrolled without the Biometric PIN feature must be re-enrolled with the Biometric PIN feature enabled in the STA console.
Configuring STA for Biometric PIN (Touch ID and Face ID)
-
In the STA Token Management console, select VIRTUAL SERVERS > POLICY > Token Policies > Token Templates.
-
Select the SafeNet MobilePASS+ for iOS token type and click Edit.
-
In the Edit Token Template window, under PIN Policy, select User-selected PIN and then select Allow Biometric PIN.
The SafeNet MobilePASS+ for iOS token can now, following enrollment, be activated to use Touch ID.
Known Issues
This table provides a list of the known issues as of the latest release.
| Issue | Synopsis |
|---|---|
| SASMOB-5581 | Unable to see the account name field on the key confirmed page in iPad landscape mode. |
| SASMOB-4856 | Voice over reads pending login request message after approving push. |
| SASMOB-4846 | When iPad is in landscape mode, the heading of welcome screen is unable to show if large text is on. |
| SASMOB-4840 | Error message in PIN validation is not obvious when scaled large enough especially in small devices. |
| SASMOB-4838 | Expiration dialog doesn’t show up if push sheet is in minimized state. |
| SAS-21916 | Summary: OCRA tokens prevent non-OCRA tokens from performing authentication. |
Compatibility Information
Operating System
- iOS 16 and later
BETA releases of the operating system are not supported.
Supported Authentication Servers
- STA
- SAS PCE 3.12 or later

