Key Setup Guide
This guide provides instructions on creating an AES256 encryption key in the Key Broker for Google Cloud EKM service page. The AES256 encryption key can be used as an external key in Google Cloud EKM.
Create a key in the Key Broker for Google Cloud EKM (NA) or (EU) page. Keys are assigned to Key Rings that exist in a Thales Key Store. Policies are applied to Key Rings, and by association any assigned Keys to restrict access and use of the resources.
Follow the Before you Begin page in the Managing Cloud EKM Keys section for detailed instructions on getting started, using the Google Cloud Platform, and using the external key. Refer to this documentation for more information about using the service and generating the master key.
Note
Ensure billing for your Google Cloud Project is enabled. Please enable billing before integrating with Key Broker for Google Cloud EKM.
Access the Key Broker for Google Cloud EKM page by logging in to the DPoD tenant and selecting the service name in the View Services Table.
Following the IDP migration users should clear the cookies in their browser or use private/incognito mode to log in to Key Broker for Google Cloud EKM.
Policies
Policies are a set of access and usage rules that are enforced on Keys on a Key Ring. A policy can be bound to Authorized Client ids such as a Google Cloud Platform Service Account or Project Number. The Authorized Client id acts as a resource identity and allows an application to access any Keys on Key Rings bound to the Policy.
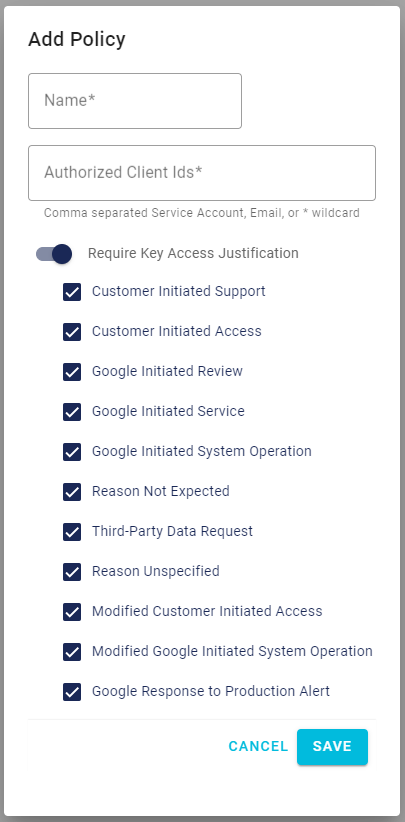
Click +ADD on the Policies page in Key Broker for Google Cloud EKM (NA) or (EU) to create a new policy. When you add a new policy you specify the following:
- Name - a name for the policy
- Approved Client ids - a comma separated list of Google Cloud Platform Service Accounts, Service Project Numbers, Emails, or * wild cards.
- Require Key Access Justification - enable or disable Key Access Justification for external keys on this key ring on the Google Cloud Platform. This setting must align with the policy setting on Google Cloud Platform.
- Justification reason codes - provide a set of approved justification reason codes for Key Access Justification. See Key Access Justification Reason Codes for more information.
You can click the Policy name to open the Edit Policy screen. You can edit all settings on a policy.
Tip
If using a Service Account, we recommend using a service account with the cryptoKeyEncrypter and cryptoKeyDecrypter IAM roles. See Permissions and Roles as they relate to cryptographic keys, for more information about providing the minimal set of permissions to the service account in Google Cloud Platform.
If using a Service Project Number provide it in the format <service-project-number>@gcp-sa-ekms.iam.gserviceaccount.com. Consult Identifying Projects for more information about identifying the service project number.
If using wild cards when adding service accounts to a policy, ensure you only authorize the correct service accounts when adding to the list of Approved Client Ids.
Key stores
The Key Store secures your Key Broker for Google Cloud EKM master key inside of a FIPS certified Thales DPoD service. Click on Key Stores to view available key stores and the regions where they are available in Key Broker for Google Cloud EKM (NA) or (EU).
When you create a Key Ring use a Key Store in a region that is near the Google Cloud Platform region you are using to reduce network latency issues between the service and the service Key Store. Review the External key managers and regions documentation for more information about choosing a region.
Key rings
Key Rings are Policy enforced key operation jurisdictions. Key Rings contain a set of customer managed encryption Keys.
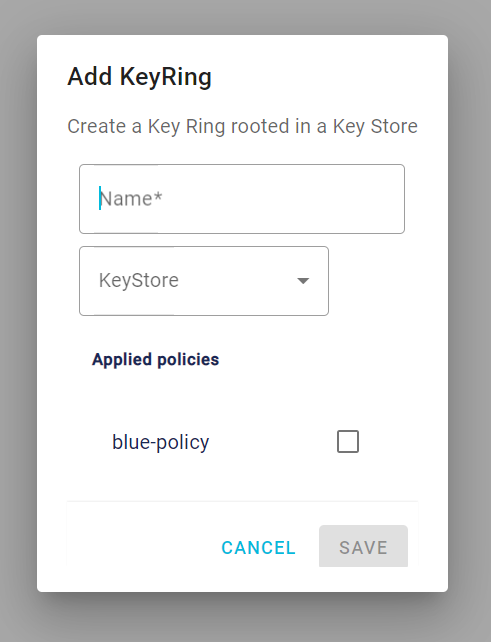
Click +ADD on the Key Rings page in Key Broker for Google Cloud EKM (NA) or (EU)to create a new key ring. When you create a new key ring you provide:
- Name - a name for the key ring.
- Key Store - select a key store where the external key will be stored. Review Key Stores for more information.
- Enforced Policies - select and enforce a policy set from the available policies. The Key Ring must be associated with a Policy to be used Google Cloud EKM. Multiple policies, with variations in permissions, can apply to the same key ring. Review Policies for more information.
You can click the Key Ring name to open the Edit Policy screen. You can edit all settings except for the KeyStore.
Keys
The Key is an AES256 encryption key that can be used in Google Cloud EKM as an external key to secure your data at rest. When you create the key, it appears on the Keys page with a unique Key URI. The Key Broker for Google Cloud EKM key appears alongside your other Cloud KMS and Cloud HSM keys, with protection level EXTERNAL, inside of the Google Cloud Platform. The external key is never exposed to Google.
Both the Cloud EKM key version and the external key are required for each encryption and decryption request. If you lose access to either key, your data cannot be recovered. It is not possible to re-create an identical Cloud EKM key version by using the same external key URI.
Click +ADD on the Keys page in Key Broker for Google Cloud EKM (NA) or (EU) to create a master key. When you create a master key you provide:
- Name - provide a name for the key.
- KeyRing - select and bind the key to an existing key ring. Review Key Rings for more information. The location for a key is determined by the location of the key ring. Keys cannot be moved from one key ring to another after creation and cannot be exported.
Click the Status toggle to disable or enable a key.
Using the key
Refer to your key by its fully-qualified resource ID when using your key over the SDK or REST API. Once you have a Key you can retrieve the key resource ID of the new key and begin using it to protect data. The key resource id appears in the format:
projects/<project_id>/locations/<location>/keyRings/<key_ring>/cryptoKeys/<key_name>
Example:
projects/cloud-ekm-Thales/locations/us-central1/keyRings/EKMSDemo_KeyRing/cryptoKeys/EKMSThales_Key
See Cloud KMS resources for more information about the format of the resource ID. See the User Guide or the Google EKM Key Documentation for more information about getting started using the key to secure data at rest in Google Cloud Platform.
Rotating the key
You can rotate a Key Broker for Google Cloud EKM key in Google Cloud Platform. Rotating a Cloud EKM key in Google automatically and transparently rotates the key in the service. The result of a key rotation is a new key version.
After you rotate a Cloud EKM key, you can still decrypt data that was encrypted using a previous version of the external key, as long as the previous version of the external key is still available at the external key URI on the Key Broker for Google Cloud EKM service.
For more information see about rotating keys in Google Cloud Platform see Rotate an external key.
Updating the key URI
You cannot update Key Broker for Google Cloud EKM Key URI.

