Managing Signature Sets
File signing checks the authenticity and integrity of executables and applications before they are allowed to access GuardPoint data. When you initiate file signing on the CipherTrust Manager, the CTE Agent calculates the cryptographic signatures of the executables that are eligible to access GuardPoint data. Files are individually signed as part of a set and the set is configured in a policy that defines the processes to allow.
When an executable tries to access a GuardPoint, the secfs service checks the fingerprint, a SHA-2 (Secure Hashing Algorithm) message digest, of the executable against the fingerprint stored in the CTE database. If they match, the executable’s authenticity is verified and it can be allowed to access protected data. A hostile or compromised executable, such as a Trojan application, malicious code, or rogue process, with a missing or mismatched signature, is denied access.
Once a set of files to be signed is created, the executables are signed on a selected client and a copy of each signature is stored on the CTE. This is done as a background process on the selected client. The time it takes to complete signing depends upon the number of files to be signed, the response time of the client system, and other load factors. The completion status is indicated in the Signature Sets window.
Completed signature sets are configured in a (CTE Agent) policy so that not only are the executables attempting GuardPoint access identified, but their signatures are checked to ensure that they had not been compromised.
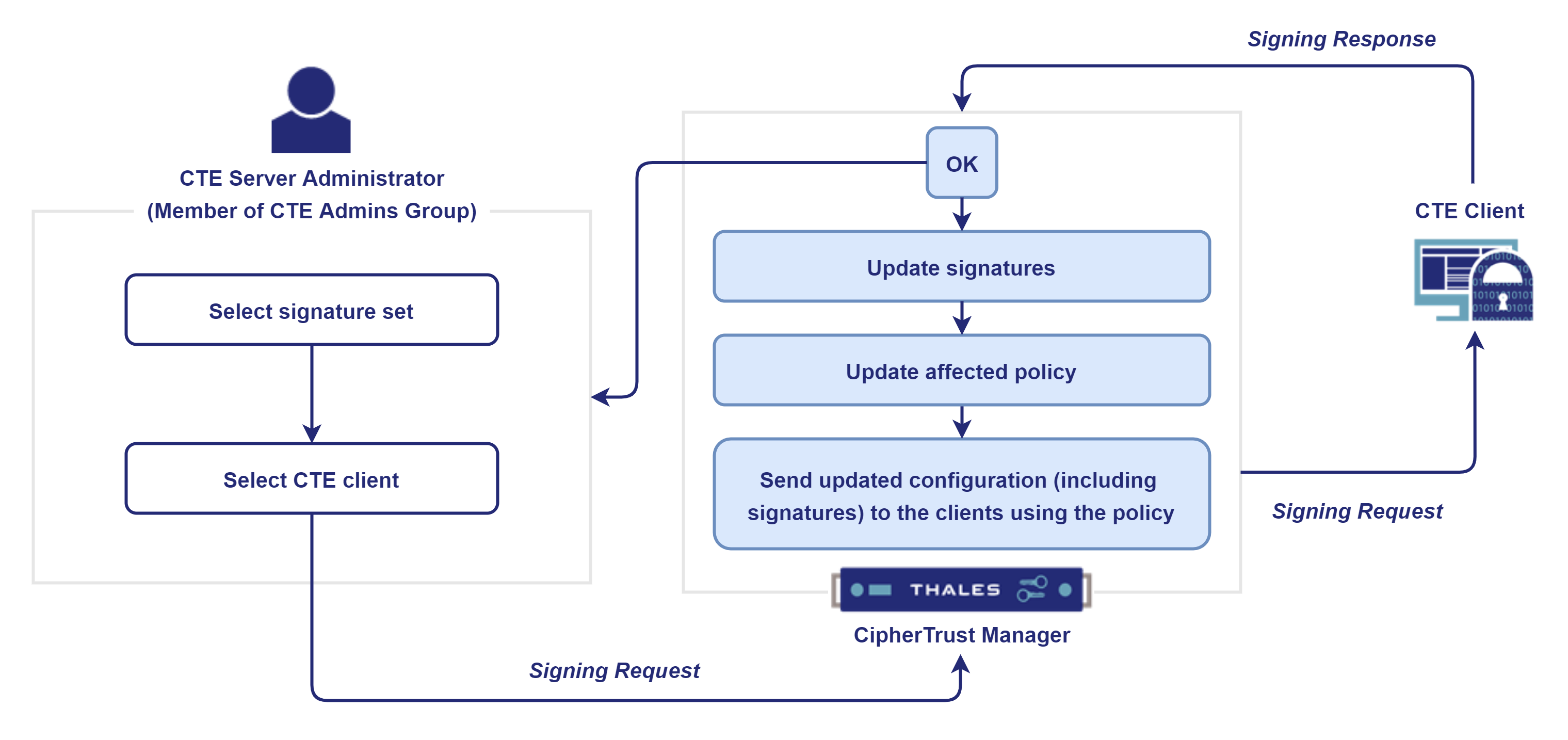
The Signing Process
The basic steps involved in the signature signing process are:
The CTE Server Administrator creates signature sets. Refer to Creating Signature Sets for details.
The CTE Server Administrator initiates the signature signing request. The administrator selects the signature set to be signed and the CTE client that will sign the set. Refer to Signing Files in a Signature Set for details.
The CipherTrust Manager forwards the request to the selected CTE client.
The CTE client signs the set and sends it to the CipherTrust Manager.
The CipherTrust Manager:
Updates the signatures in the set.
Updates the affected policies.
Sends the updated configuration files including the signatures to the clients that are using the affected policies.
In future, if any processes in the signature set are updated, the signature set should be signed again. The CTE Server Administrator can initiate the signature signing process again. This is referred to as the signature re-signing process.
The following diagram shows the high level signature signing process:
Using Signature Sets in a Policy
Policies can be configured to identify the executables trying to access GuardPoint data and to verify that the executables themselves are unchanged since they were signed. You must, however, anticipate the effect of encryption on file signatures.
When a file inside a GuardPoint is copied to a location outside the GuardPoint, the two files have different signatures. The file in the GuardPoint is encrypted, but the file outside the GuardPoint is not.
Encryption makes the two files different. The VMD process does not decrypt guarded files before checking their signatures. So, when you rekey guarded files, their signatures also change. Re-sign the files that use the signatures of those files in process sets.
If both files must access the GuardPoint data, add both files to the signature set and sign them. If encryption is not applied, both files have the same signature; a signature mismatch should not occur.
Creating Signature Sets
A signature set is a collection of file names and/or directory names. You can enter the full path of files and directories manually or use the browser to locate and select them. Specify a directory to sign all the files in that directory and all the subdirectories that it may contain.
Signing many files can take a while. To shorten processing time, verify that the files and directories in the signature set exist. It takes longer to process non-existent files. If they do not exist, it is recommended that you delete them as sources from the signature set. Refer to Deleting Source from Signature Sets for details.
To create a signature set:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab.
Click Create Signature Set. The Create Signature Set wizard is displayed.
On the General Info screen:
Enter a unique Name for the set.
The name must start with a character. The maximum length can be 64 characters.
The name can contain alphanumeric characters, underscores (
_), and dashes (-).The name cannot contain the following special characters:
? : ; | ! @ # $ % ^ & * < = > + ( ) { } ~ , \ / [ ] ' "
Provide a Description for the set.
Click Next. The Add Sources screen is displayed. On this screen, you can add files to be signed, as described below.
Adding Files to a Signature Set
Specify path of the directory or file to be signed. If a directory is specified, all files in the directory and its subdirectories are signed.
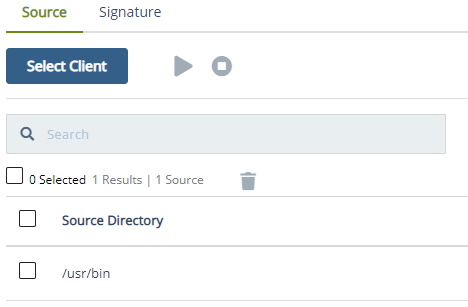
Click Select Client. The list of registered clients is displayed.
Select the desired client.
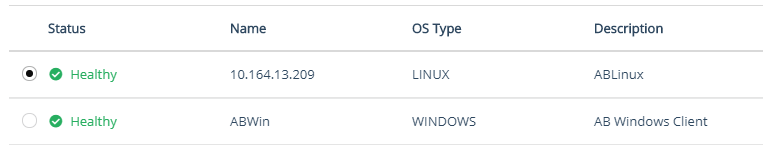
Click Select. The selected client appears next to Select Client.
Click Add Source. The file system of the selected client is displayed. The file system of a client marked for deletion cannot be browsed.
The Client drop-down box shows the selected client. If needed, change the client from the list.
Select the path to be signed. Select the path either typing manually or by using the browser.
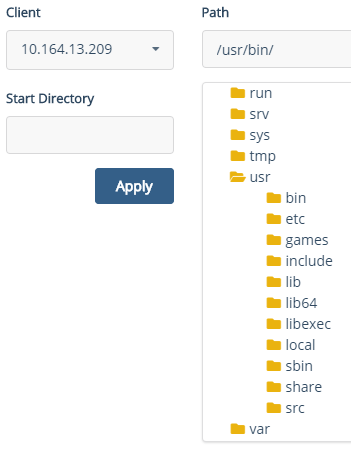
To jump to a specific directory, enter the directory path in the Start Directory field and click Apply. The browser shows the subdirectories and files, as shown below.
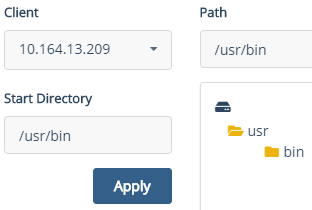
You cannot browse above the Start Directory. Enter a start point that is higher in the directory hierarchy than all the directories and files that you want to select, or you will have to re-enter start points to locate and select the desired files. The default is the top-level, either slash (Linux) or backslash (Windows).
Alternatively, if you know the directory path, you can enter it manually in the Path field.
Click Add. The selected source is displayed in the Source Directory list.
Optionally, you can add a new source by clicking Add Source. To remove a source, click the overflow icon (
 ) corresponding to the source and click Remove.
) corresponding to the source and click Remove.
Click Next. The Confirmation screen shows general information about the set and the selected sources.
Verify the set details. If the details are incorrect or you want to modify them, click Back and update the details.
Click Save.
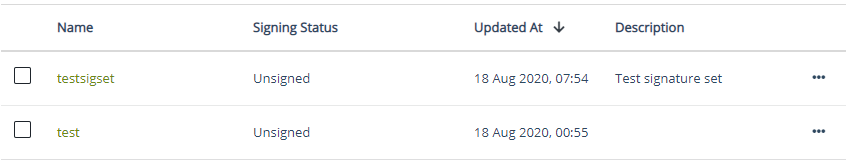
The newly created set appears on the Signature Sets tab. By default, the signature set has the status UNSIGNED.
It is recommended that the signature set is signed before you apply policies to processes. This ensures that a tampered with or compromised process executable is not granted permissions to access protected GuardPoints. Refer to Signing Files in a Signature Set for details.
Signing Files in a Signature Set
Signing involves calculating a hash value for a file and storing the value on the CipherTrust Manager. Later, when a policy checks signatures, the signature of the process or executable accessing the GuardPoint is calculated and compared against the value in the CipherTrust Manager. If the two values match, the process or executable satisfies the Process requirement of a policy and may be granted access to the guarded data.
Note
If the executable itself is volatile, or subject to frequent change, it may not be worthwhile to use a file signature as a criteria in a policy because you have to re-sign the executable after each change. If the volatile executables are members of a large signature set, it can take a while to re-sign the files because the signature of every file in the signature set is recalculated. If the volatile files are few, it might be quicker to add the volatile files to a different signature set and sign that set, rather than re-sign all the files in the original signature set.
To sign the files in a signature set:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab. The list of configured signature sets is displayed.
Click the desired signature set.
Select a client to sign the signature set. A signing client is required to start the signing process.
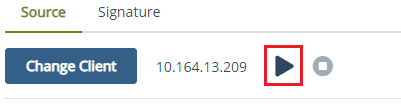
On the Source tab, click Select Client. The list of registered clients is displayed. Select any client to sign the signature set.
Select the client.
Click Select. The selected client appears next to the Select Client button. The Sign icon (
 ) is now enabled.
) is now enabled.
Note
Do not select check boxes when signing a signature set. They are used to select source directories to be deleted from the set.
Click the Sign icon (
 ). The signing process starts.
). The signing process starts.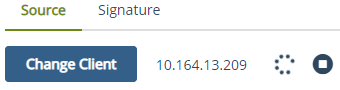
The signing status of the signature set becomes InProgress.
- To view the percent completion of the signing process, hover over the Spinner (
 ) progress bar.
) progress bar. - To stop the signing process before it completes, click the Stop Signing icon (
 ). Refer to Stopping the Signing Process for details.
). Refer to Stopping the Signing Process for details.
The time for the signing process to complete depends on the number of files being processed. Signing occurs as a background process. So, you can use the CipherTrust Manager GUI for other administrative functions during this process.
When the signing completes, the signing status of the signature set becomes Finished. Refer to Checking Signing Completion Status for details about the signing status.
The resulting signatures are available on the Signature tab of the signature set.
Checking Signing Completion Status
To view the signing completion status of a signature set:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab. The list of configured signature sets is displayed.
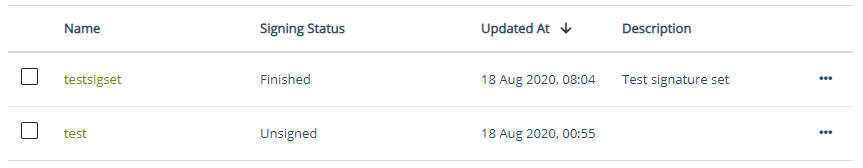
View the Signing Status for the signature set. The Signing Status can be:
Status Description Unsigned Signature set is unsigned. Either no files exist in the set or no attempt is made to sign them yet. InProgress The CipherTrust Manager is actively signing the files in the set. This can take some time depending on the system load, accessibility, and the number of files being signed at one time. Finished All the files in the set are signed successfully. The set is ready for use. FinishedWithWarning All the files in the set are processed, but one or more files in the set could not be signed. Possible causes are missing files or inadequate access permissions. Check the VMD logs for details:
• On Unix, vorvmd_root.log.
• On Windows,vorvmd.log. Alternatively, view the logs in Event Viewer > CipherTrust Encryption Expert.
Refer to Checking Agent Logs if Signing Fails for details.Aborted Signing was started but stopped before completion.
Stopping the Signing Process
Interrupt the signing process at any time before it completes. Click the Stop Signing ( ) icon on the Source tab of the Signature Sets tab. The CipherTrust Manager does prompt you to verify your choice.
) icon on the Source tab of the Signature Sets tab. The CipherTrust Manager does prompt you to verify your choice.
It takes a while for the signing process to stop. After the process is stopped, the Signing Status displayed on the Signature Sets tab is set to abort. All the files that were signed until you stopped the process remain intact and can be viewed on the Signature tab of the signature set.
Displaying Signatures of Files in a Signature Set
CipherTrust Manager provides options to display signatures of all or specific files in a signature set.
Displaying Signatures of All Files in the Signature Set
To display the signatures of all files in a signature set:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab. The list of configured signature sets is displayed.
Under Name, click the desired signature set.
Click the Signature tab.
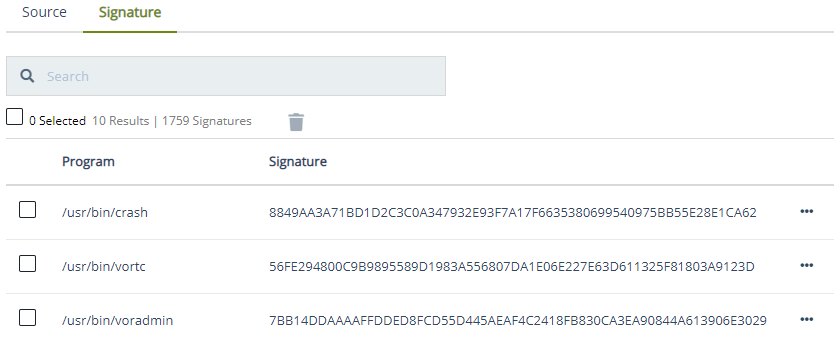
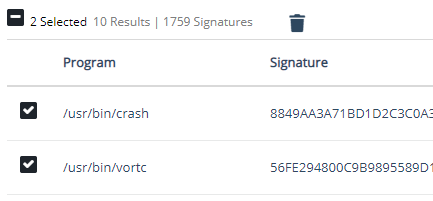
The list of all files (programs) in the signature set with their signatures is displayed. By default, 10 records per page are displayed. Adjust the pagination to view more records.
Displaying Specific Signed Files in the Signature Set
To display specific signed files in a signature set:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab. The list of configured signature sets is displayed.
Under Name, click the desired signature set.
Click the Signature tab. By default, all signed files in the set are displayed in alphanumeric order.
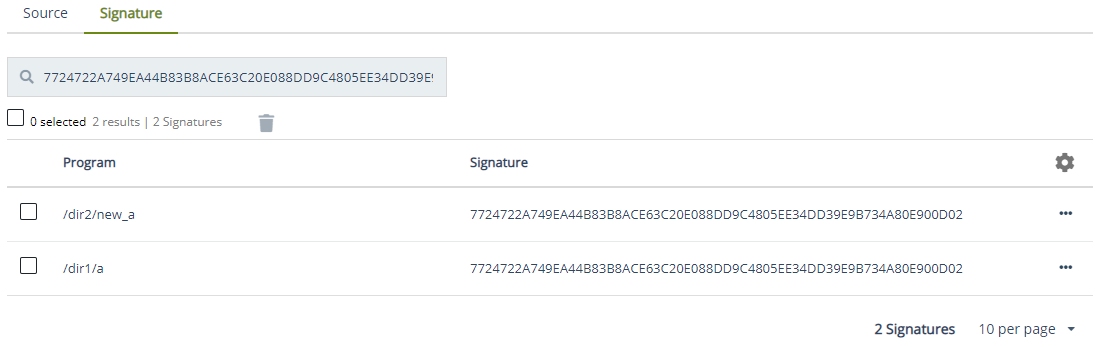
In the Search box, enter the string that matches the partial or full name of the program whose signature you are searching for.

The search is case-insensitive. All files that contain the string in their names are displayed.
Detecting Duplicate Files
Unless the content of a file is modified, its signature remains the same regardless of the file name and location. Also, the signature of all copies of a file remains the same. So, to determine the duplicates of a file, display the files based on their signature. If you search using a signature, it is recommended to enter the complete signature.
To detect the duplicates of a file:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab. The list of configured signature sets is displayed.
Under Name, click the signature set in which you want to detect duplicate files.
Click the Signature tab. The signatures of the files in the set are displayed.
Copy the signature of a file from the Signature column.
Paste the signature in the Search box. Remove any extra space, if inserted when pasting.
Notice the search result.
If multiple records are displayed, duplicates of the file exist. If a single record is displayed, duplicates of the file do not exist. For example, the following figure shows two files with different names and locations, but with identical content based on their signature.
Deleting Signatures from Signature Sets
Delete either individual signatures from a set or the complete signature sets. Refer to Deleting Signature Sets for information on deleting complete signature sets.
Delete signatures from a signature set when you want to continue to use the signature set to authenticate processes, but you no longer want to authenticate the files that you are deleting from the set.
You can delete signatures individually or one page at a time.
Deleting Single Signatures
To delete a single signature from a signature set:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab.
Click the desired signature set.
Click the Signature tab. The list of signatures in the signature set is displayed.
Click the overflow icon (
 ) corresponding to the desired signature.
) corresponding to the desired signature.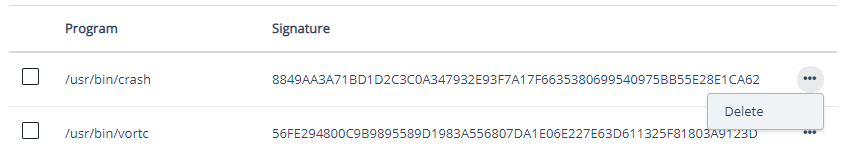
Click Delete. A dialog box appears prompting you to confirm the action.
Click Delete.
The selected signature is removed from the list and the CipherTrust Manager database.
Deleting Multiple Signatures
To delete single or multiple signatures from a signature set:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab.
Click the desired signature set.
Click the Signature tab.
Select the check boxes corresponding to the signatures you want to delete.
To select all signatures for deletion, select the top check box to the left of the Signature heading.
Click the delete icon (
 ). A dialog box appears prompting you to confirm the action.
). A dialog box appears prompting you to confirm the action.Click Delete.
The selected signatures are removed from the list and the CipherTrust Manager database.
Deleting Source from Signature Sets
Signing many files can take a while. To shorten processing time, verify that the files and directories in the signature set exist. It takes longer to process non-existent files. If they do not exist, it is recommended that you delete them as sources from the signature set.
Deleting Single Sources
To delete a single source from a signature set:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab.
Click the desired signature set. The Source tab shows the list of source directories.
Click the overflow icon (
 ) corresponding to the desired source directory.
) corresponding to the desired source directory.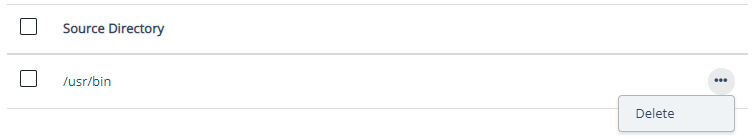
Click Delete. A dialog box appears prompting you to confirm the action.
Click Delete.
The selected source is removed from the list and the CipherTrust Manager database.
Deleting Multiple Sources
To delete single or multiple sources from a signature set:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab.
Click the desired signature set. The Source tab shows the list of source directories.
Select the check boxes corresponding to the desired source directories.

To select all sources for deletion, select the top check box to the left of the Source Directory heading.
Click the delete icon (
 ). A dialog box appears prompting you to confirm the action.
). A dialog box appears prompting you to confirm the action.Click Delete.
The selected sources are removed from the list and the CipherTrust Manager database.
Deleting Signature Sets
Delete either individual signatures from a set or the complete signature sets. Refer to Deleting Signatures from Signature Sets for information on deleting individual signatures.
An active (in use) signature set cannot be deleted. Before deleting a signature set from the CipherTrust Manager, make sure that no policies are using it.
CipherTrust Manager provides options to delete single or multiple signature sets.
Deleting Single Signature Sets
To delete a single signature set:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab. The list of configured signature sets is displayed.
Click the overflow icon (
 ) corresponding to the desired signature set.
) corresponding to the desired signature set.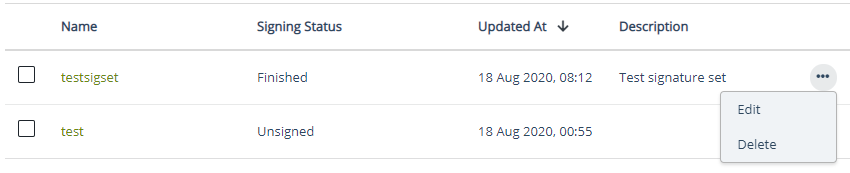
Click Delete. A dialog box appears prompting you to confirm the action.
Click Delete.
The selected signature set is removed from the list.
Deleting Multiple Signature Sets
To delete single or multiple signature sets:
Open the CTE application.
Click Policies > Policy Elements.
Click the Signature Sets tab. The list of configured signature sets is displayed.
Select the check boxes corresponding to the desired signature sets.
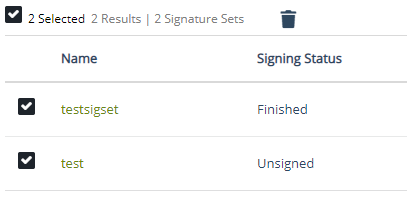
To select all sets for deletion, select the top check box to the left of the Name column.
Click the delete icon (
 ). A dialog box appears prompting you to confirm the action.
). A dialog box appears prompting you to confirm the action.Click Delete.
The selected signature sets are removed from the list.
Re-Signing Files in a Signature Set
Signatures are computed values. Unless the files in a signature set are compromised or modified, the signature always remains the same for a given file. If the files are modified, they must be re-signed to ensure that their signatures match the signatures on the CipherTrust Manager.
To re-sign the files, you can:
Create and sign a new signature set with the files and directories to be signed. Use this option if the set contains only a few files and directories.
Create and sign a new signature set with the paths of the directories that contain the files to be signed. Use this option if the directories contain only a few files or most files in the directories need re-signing.
Open and re-sign the existing signature set that is originally used to sign the files. Use this option if you have the time or the signature set is small.
Computing the signature of every file in a large signature set takes a long time.
Re-signing the files in a set takes longer than signing the files the first time. It requires additional handling to update information on the CipherTrust Manager. If you plan to re-sign a large number of files (say hundreds of thousands), it can be quicker to:
Delete the existing signature set. Refer to Deleting Signature Sets for details.
Create the signature set again, from scratch. Refer to Creating Signature Sets for details.
Sign the files of the signature set again. Refer to Signing Files in a Signature Set for details.
Checking Agent Logs if Signing Fails
If signing fails, or you want more information about the signing process such as which files were skipped, check the CTE Agent logs captured on the client.
Messages are logged to:
(UNIX)
/var/log/vormetric/vorvmd_root.logwith Log to File enabled and to a Syslog server with Syslog enabled.(Windows)
\Documents and Settings\...\agent\log\vorvmd.logwith Log to File enabled.
In the vorvmd_root.log/vorvmd.log file on the client, look for messages like:
[VMD] [WARN ] [3732] [VMD3824W] Failed to create the signature for
E:\apps\lib\dx1\aa_dir\dataxform_auto_config for the signature
request 9, error code 3
The following table lists error codes with their description:
| Code | Description |
|---|---|
| 0 | System is okay. |
| 1 | Does not exist. |
| 2 | DO NOT USE. |
| 3 | Invalid argument. |
| 4 | Operation not supported. |
| 5 | Out of memory. |
| 6 | No space left on device. |
| 7 | Timeout reached. |
| 8 | I/O error. |
| 9 | Interrupted. |
| 10 | Permission denied. |
| 11 | Too many keys in key group. |
| 12 | Error in soap rpc layer. |
| 13 | Returned buffer is partially full. |
| 14 | Given target buffer is too small. |
| 15 | Unable to compress buffer. |
| 16 | Internal test failed. |
| 17 | Overflow. |
| 18 | Error setting up logging. |
| 19 | Overloaded error. |
| 20 | Server responded to a file upload with “bad request”. |
| 21 | Unknown user name or bad password. |
| 22 | The directory service is not available. |

