Device Inventory
Device Inventory provides a centralized, real-time view of all registered FIDO authenticators in an organization. It enables administrators to quickly locate, monitor, and manage configured and assigned devices, as well as devices held in stock (unassigned devices).
The Device Inventory section includes the following tabs for device management:
-
Configured & Assigned – Displays devices that are configured and assigned to users.
-
Stock – Displays devices that have been added to the inventory but are not yet assigned to users.
Configured & Assigned
On the Configured & Assigned tab, administrators can perform the following actions to manage configured and assigned devices:
- View Configured and Assigned Devices
- Search Devices
- Export Devices
- Revoke Devices
- Initial Device PIN
- Unlock Devices
View Configured and Assigned Devices
The following two views are provided to help administrators access device information:
- Summary View: Displays essential device details in a compact format for quick identification and action.
- Expanded View: Provides complete device information, including lifecycle and compliance details, for in-depth management.
Summary View
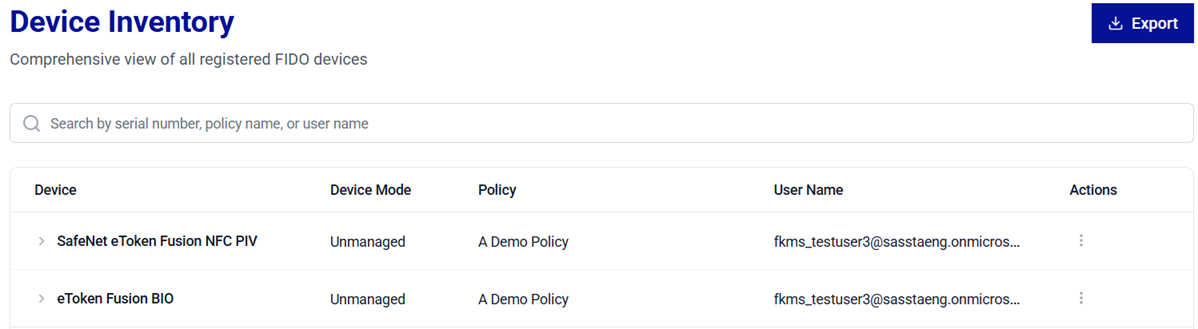
| Column | Description |
|---|---|
| Device | Displays the names of the FIDO authenticators (for example, SafeNet eToken Fusion NFC PIV Enterprise). |
| Device Mode | Indicates whether a device is Managed or Unmanaged. Managed devices are Thales FIDO 2.1 devices, which support setting an admin PIN and enterprise features. Some of the enterprise features include configuring a minimum PIN length, enforcing PIN changes, enforcing user verification, and whitelisting web services. |
| Policy | Displays the authentication policies assigned to devices. |
| User Name | Displays the usernames of users associated with the devices. |
| STATUS | Indicates the current state of the device (REVOKED, ENROLLED, and CONFIGURED). |
| Actions: Revoke | Provides an option to revoke a device from use. |
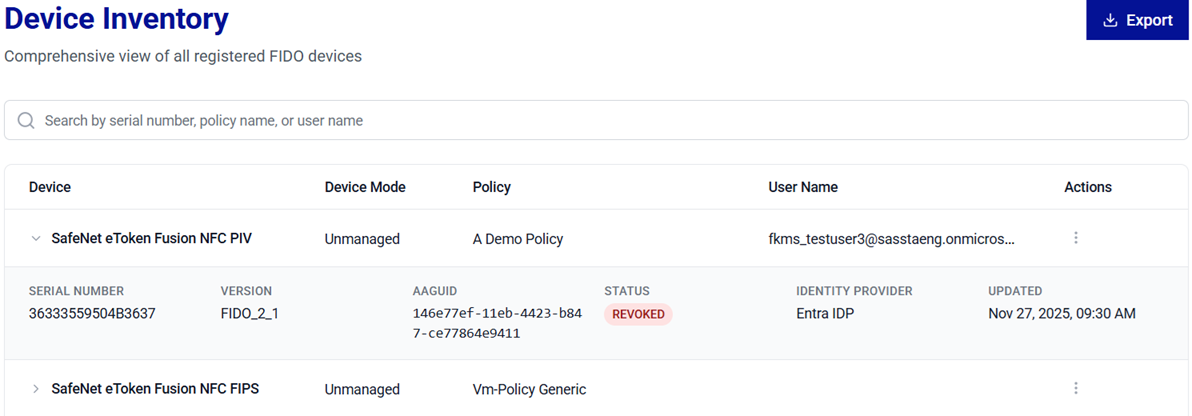
Expanded View
In addition to the information available in the Summary view, the Expanded view provides more device-specific details that support device lifecycle management and compliance tracking.
To view these details, under Device Inventory, click on the expand arrow  icon for the desired device.
icon for the desired device.
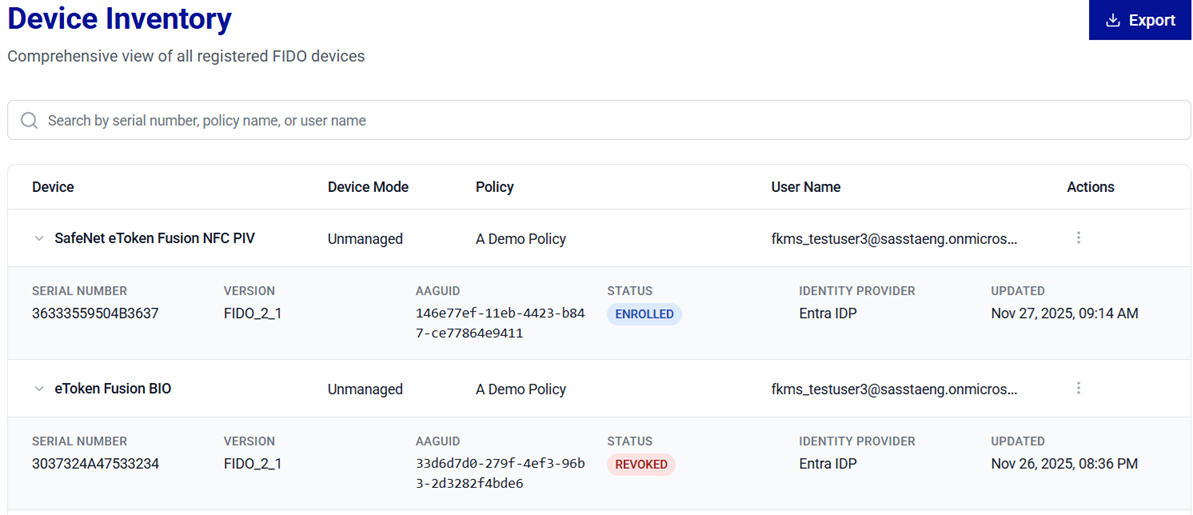
| Column | Description |
|---|---|
| SERIAL NUMBER | Displays the unique serial number of the device. |
| VERSION | Displays the device version (for example, FIDO_2_1). |
| AAGUID | Provides Authenticator Attestation Globally Unique Identifier (AAGUID), a unique identifier for device identification. |
| IDENTITY PROVIDER | Displays name of the identity provider. |
| UPDATED | Displays the last updated date and time for the device record. |
Search Devices
The Search operation allows administrators to quickly locate devices across large inventories. Use the search bar to filter configured devices and view their details based on any of the following criteria:
-
Serial Number – To search for a device using its unique serial number.
-
Policy Name – To list all devices to which a specific policy is applied.
-
User Name – To list device(s) assigned to a specific user.
Tip
For best results, search using the full value (for example, a complete Serial Number) . If the exact value is unavailable, begin with a partial serial Number, the policy name, or user name to narrow down the results.
Export Devices
The Export operation generates complete details (in a .csv file) of all the devices listed under Device Inventory. The exported file includes information from the Summary view and the Expanded view for devices listed in the current inventory list.
To export devices' details, under Device Inventory, on the Configured & Assigned tab, click Export.

Note
If required, use the Search operation to refine the device list and then click Export.
Caution
Exported files may contain sensitive information such as serial numbers and assignment details. Store and share the exported files in accordance with your organization’s data handling and security policies.
Revoke Devices
The Revoke operation permanently disables a device for authentication. Use Revoke when a device is lost, stolen, compromised, or no longer authorized. Revocation changes the device status to Revoked and prevents the device from being used for future authentication.
Perform the following steps to revoke a device:
-
Under Device Inventory, search for and locate the device that you want to revoke.
-
In the Actions column, click the three-dots
 icon for the device, and then select Revoke.
icon for the device, and then select Revoke.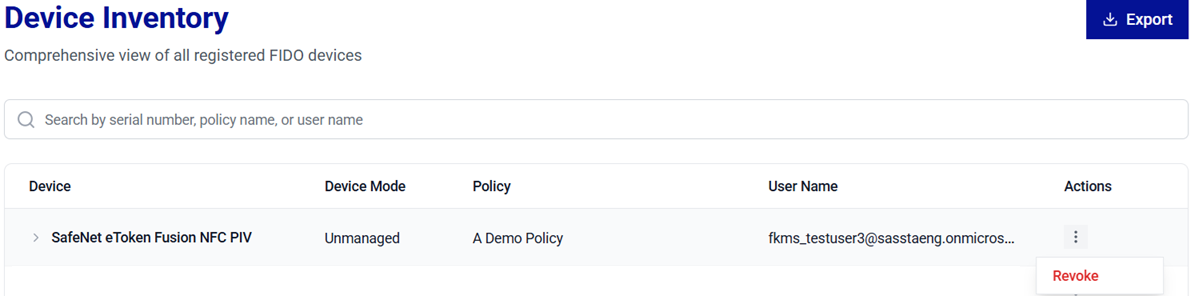
-
The Revoke Device window is displayed. Click Revoke to confirm the operation.
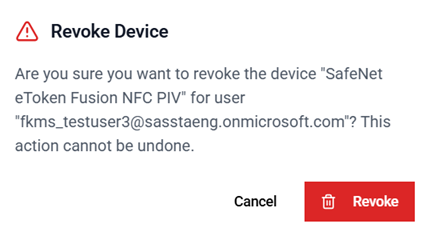
You can enable the Send email notification toggle to notify users when their device(s) are revoked.
After the device is successfully revoked, the STATUS of the device is changed to Revoked.
Warning
Revocation is a permanent action. Once a device is revoked, it is permanently disabled and cannot be used for authentication again.
To reuse the device, it needs to be re-enrolled for a user.
View Initial Device PIN
Administrators can view the initial device PIN for administrative verification.
Caution
Use this option only in secure environments to prevent unauthorized PIN exposure.
Permission-based visibility
The ability to view PIN values depends on the following permissions assigned to the administrator:
talm_device_userpin_read– Allows viewing the User PIN.talm_device_adminpin_read– Allows viewing the Admin PIN (applicable to enterprise devices that support administrator mode).
PIN Visibility by Permission and Device Type
User PIN Permission talm_device_userpin_read |
Admin PIN Permission talm_device_adminpin_read |
Standard device | Enterprise device |
|---|---|---|---|
| Enabled | Enabled | User PIN | User PIN and Admin PIN |
| Disabled | Enabled | No Initial PIN option | Admin PIN |
| Enabled | Disabled | User PIN | User PIN |
| Disabled | Disabled | No Initial PIN option | No Initial PIN option |
Perform the following steps to view a device user PIN and/or Admin PIN:
-
Under Device Inventory, search for and locate the device for which you want to view the PIN.
-
In the Actions column, click the three-dots
 icon for the device, and then select Initial PIN.
icon for the device, and then select Initial PIN.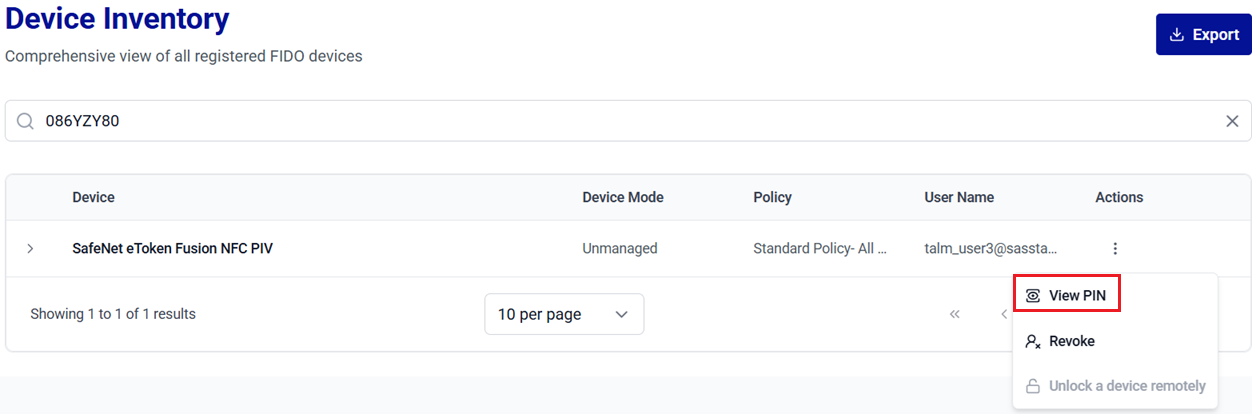
-
On the Device PIN window, click on the Show Password
 icon to view the initial device PIN.
icon to view the initial device PIN.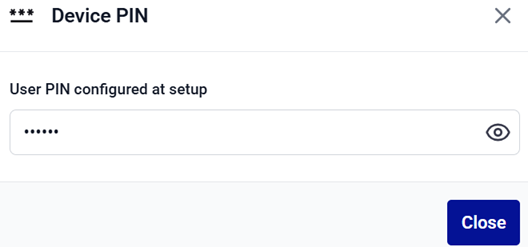
-
Click Close to close the window.
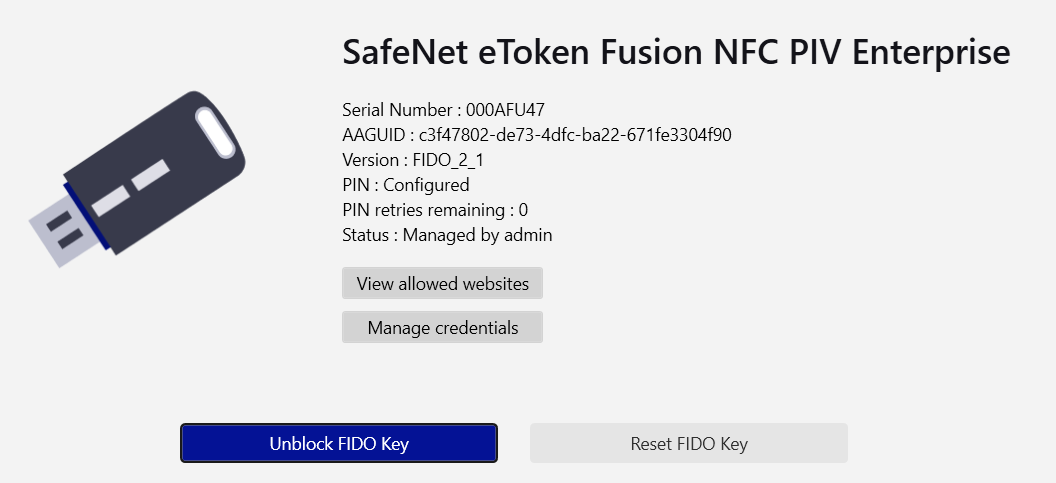
Unlock Devices
A FIDO device is locked after repeated incorrect PIN attempts. When the device is locked, the user cannot authenticate until it is successfully unlocked. Thales Authenticator Lifecycle Manager provides two secure options to unlock a device:
- Remote Unlock (Challenge–Response Method): The locked device stays with the end user, while the administrator assists remotely using Thales Authenticator Lifecycle Manager.
- Physical Unlock (Admin Mode): The administrator has physical access to the device and performs the unlock operation directly in Thales Authenticator Lifecycle Manager. This operation can be performed under FIDO Key Management.
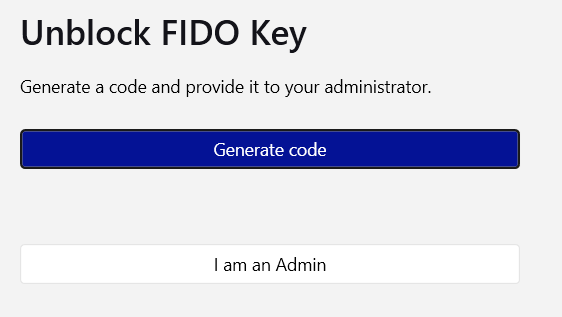
Remote Unlock
The remote unlock option is used when the locked device remains with the end user. This method uses a secure challenge–response mechanism. The user generates a challenge in SafeNet FIDO Key Manager (FKM), and the administrator generates the corresponding response in Thales Authenticator Lifecycle Manager. The user enters the response to reset the PIN and unlock the device.
Before starting the remote unlock process, ensure to complete the following prerequisites:
- The end user must have SafeNet FIDO Key Manager (FKM) installed.
- The FIDO device remains connected throughout the process.
- The end user must have an authorized support channel (for example, Teams, Slack, ticketing system, etc.) to contact the Thales Authenticator Lifecycle Manager administrator.
User Steps
-
Insert the FIDO device, open SafeNet FIDO Key Manager (FKM), and click Unblock FIDO Key.
Caution
Do not remove the FIDO device at any point during the unlock process.
-
Click Generate Code to generate a challenge.
-
Click Copy to copy the generated code and share it with the Thales Authenticator Lifecycle Manager administrator.
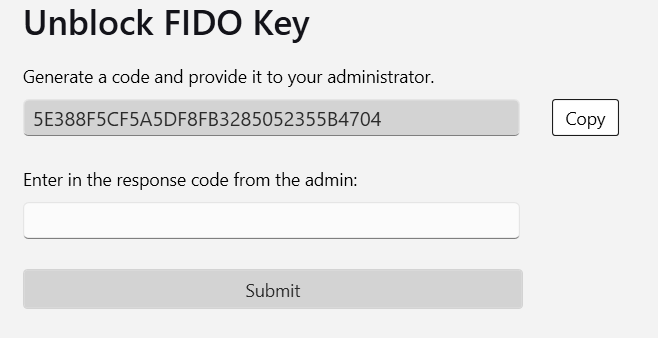
After sharing the challenge, wait for the administrator to complete the corresponding unlock steps in Thales Authenticator Lifecycle Manager and provide you with a response code. Refer to the Administrator Steps section.
-
After receiving the response code from the administrator, enter it in the response code field and click Submit.
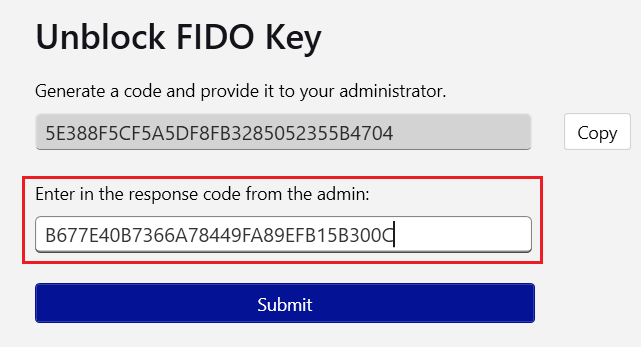
-
When prompted, enter a new PIN and re-enter it to confirm, then click Submit.
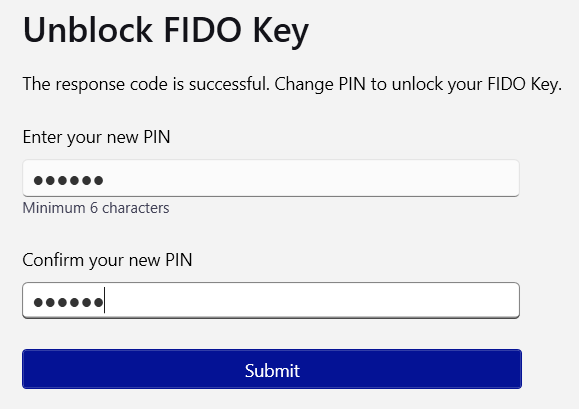
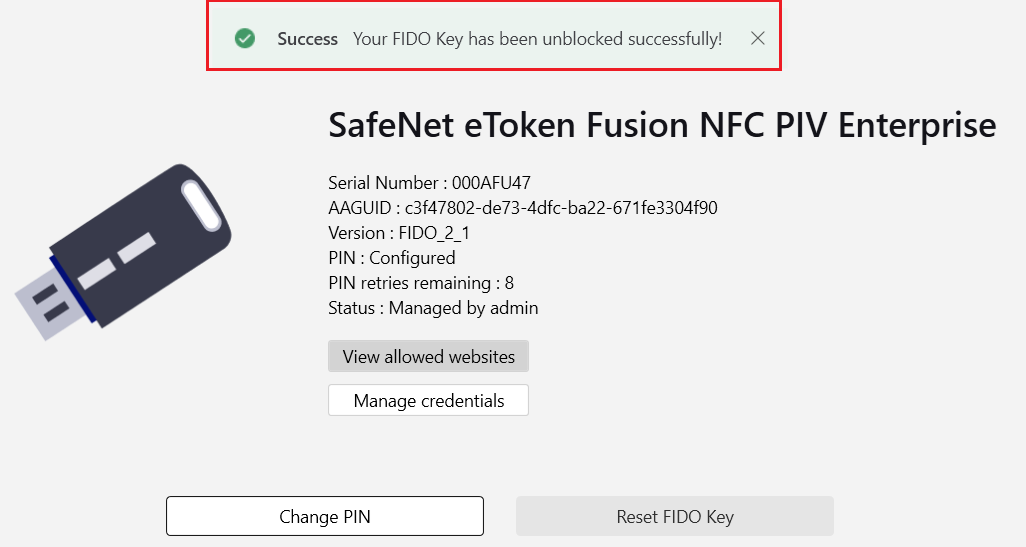
After the device is successfully unlocked, the success message is displayed.
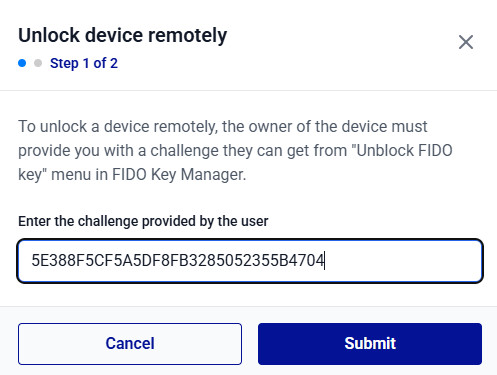
Administrator Steps
-
Log in to Thales Authenticator Lifecycle Manager and go to the Inventory menu.
-
In the Device Inventory list, search for and locate the device to be unlocked.
-
In the Actions column, click the three-dots
 icon and select Unlock a device remotely.
icon and select Unlock a device remotely. 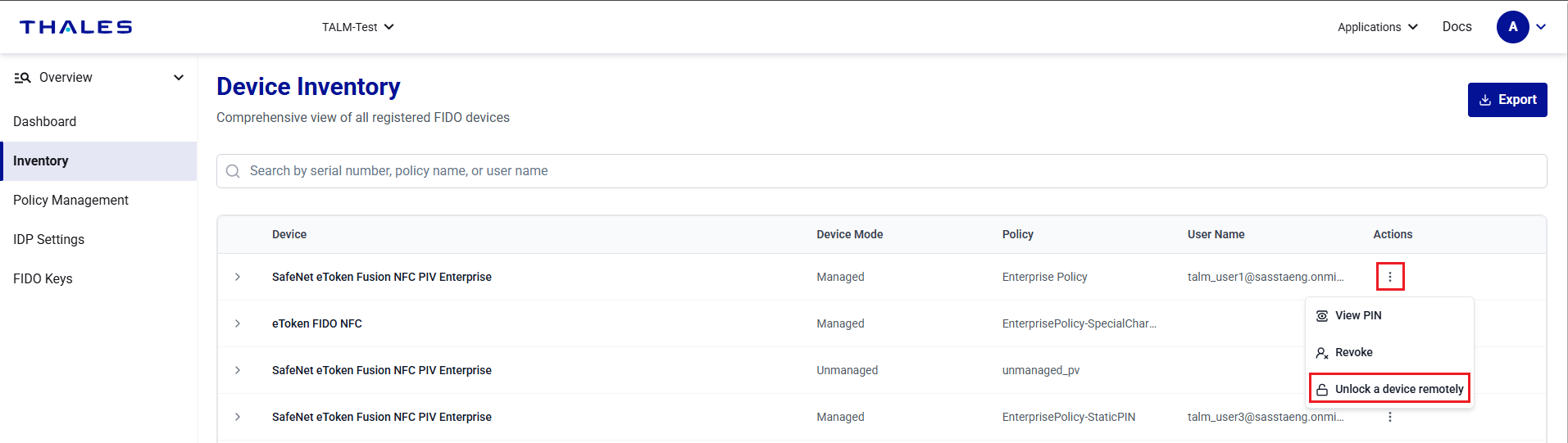
-
Under Unlock device remotely, enter the challenge code provided by the user, and click Submit.
-
Click the Copy to clipboard icon
 to copy the generated response code. Share this code with the user and click Finish.
to copy the generated response code. Share this code with the user and click Finish. 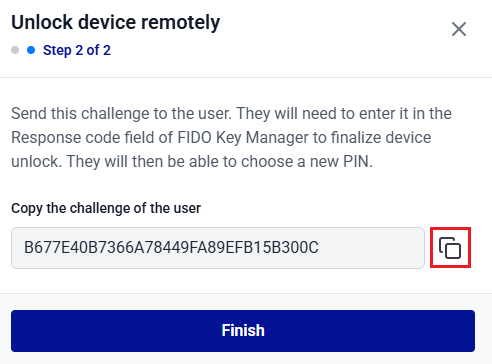
Next steps for users: The user must continue from user step 4 to enter the response code and reset the device PIN.
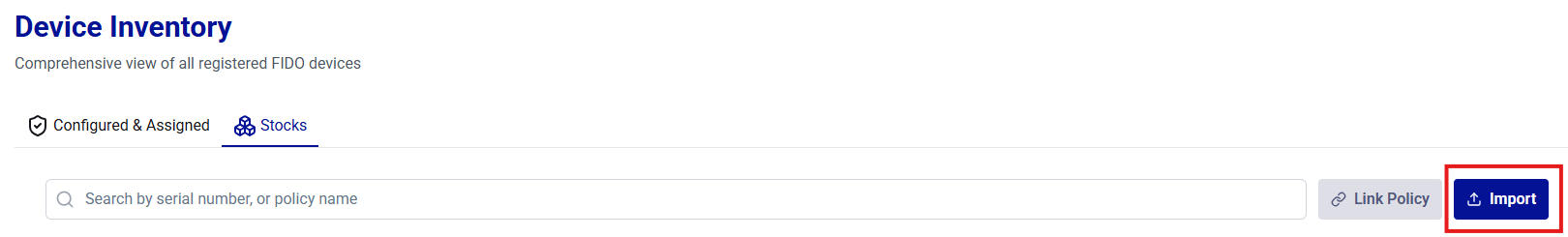
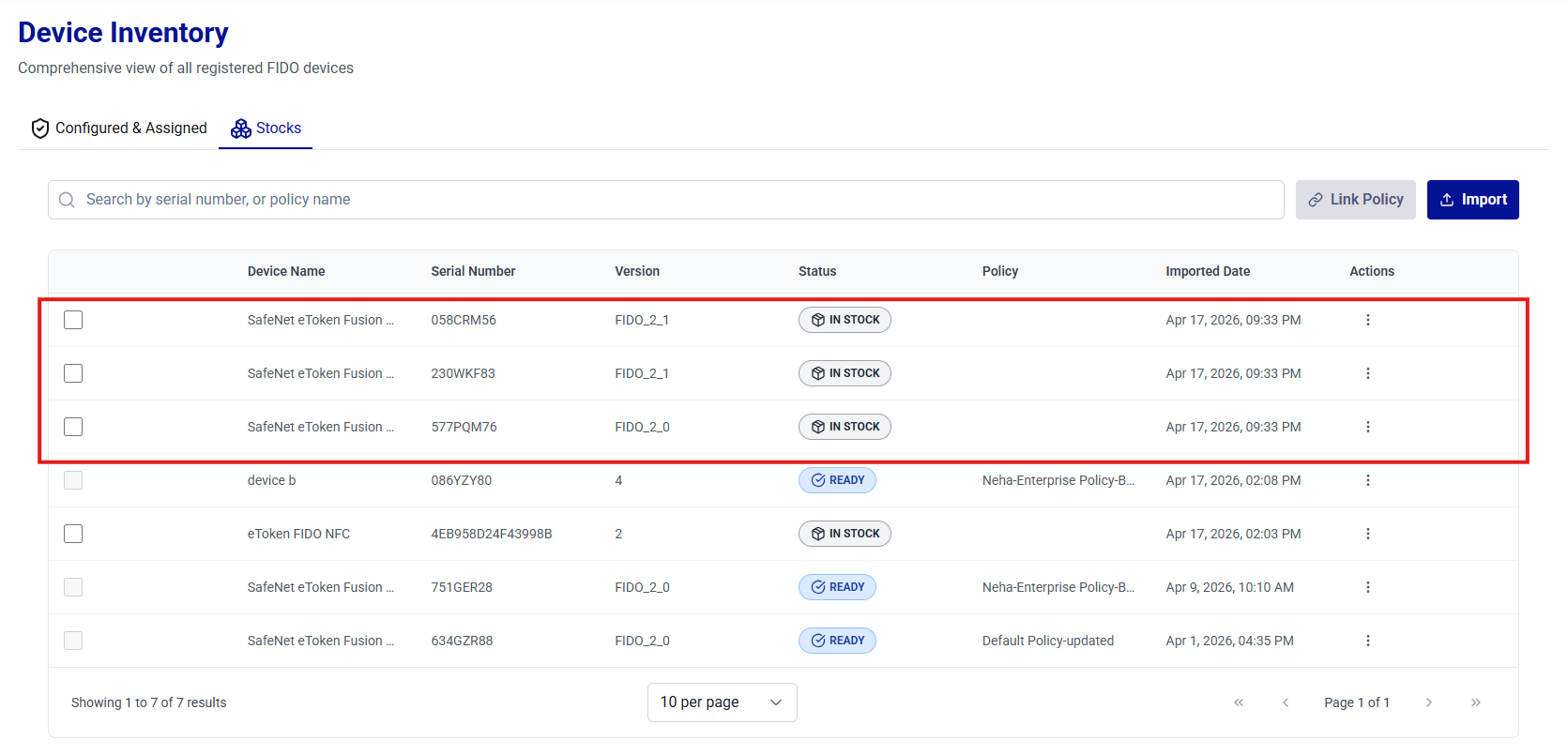
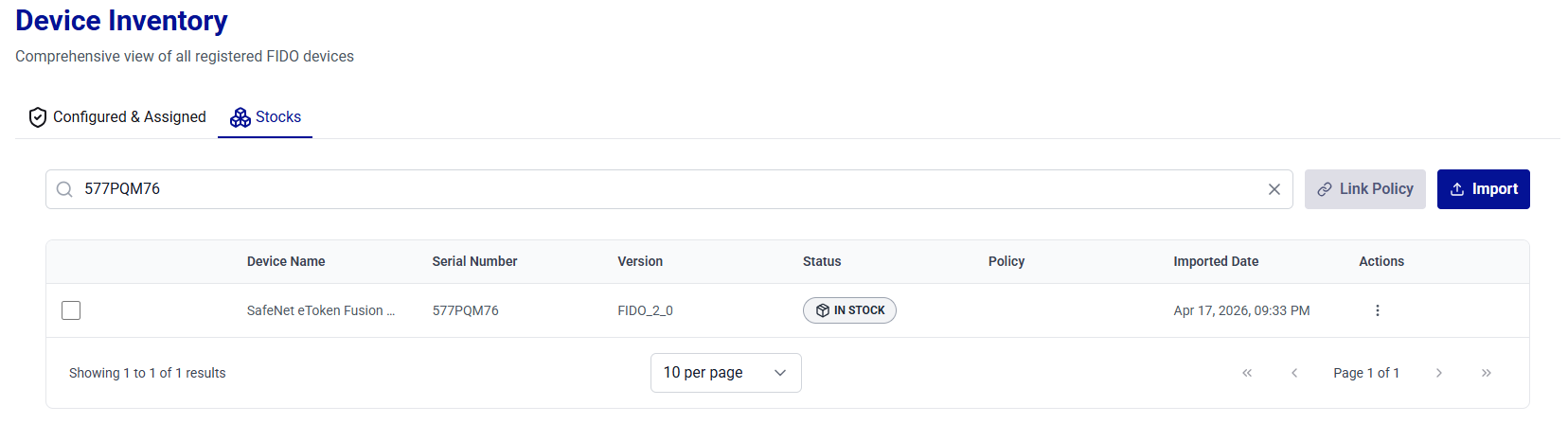
Stock
On the Stock tab, administrators can perform the following actions to manage unassigned devices:
- View Devices in Stock
- Search Devices in Stock
- Import Devices into Stock
- Link Policy to Devices
- Link a Policy to a Single Device
- Unlink a Policy from a Single Device
- Delete a Device from Stock
View Devices in Stock
Administrators can view complete information about devices held in stock.
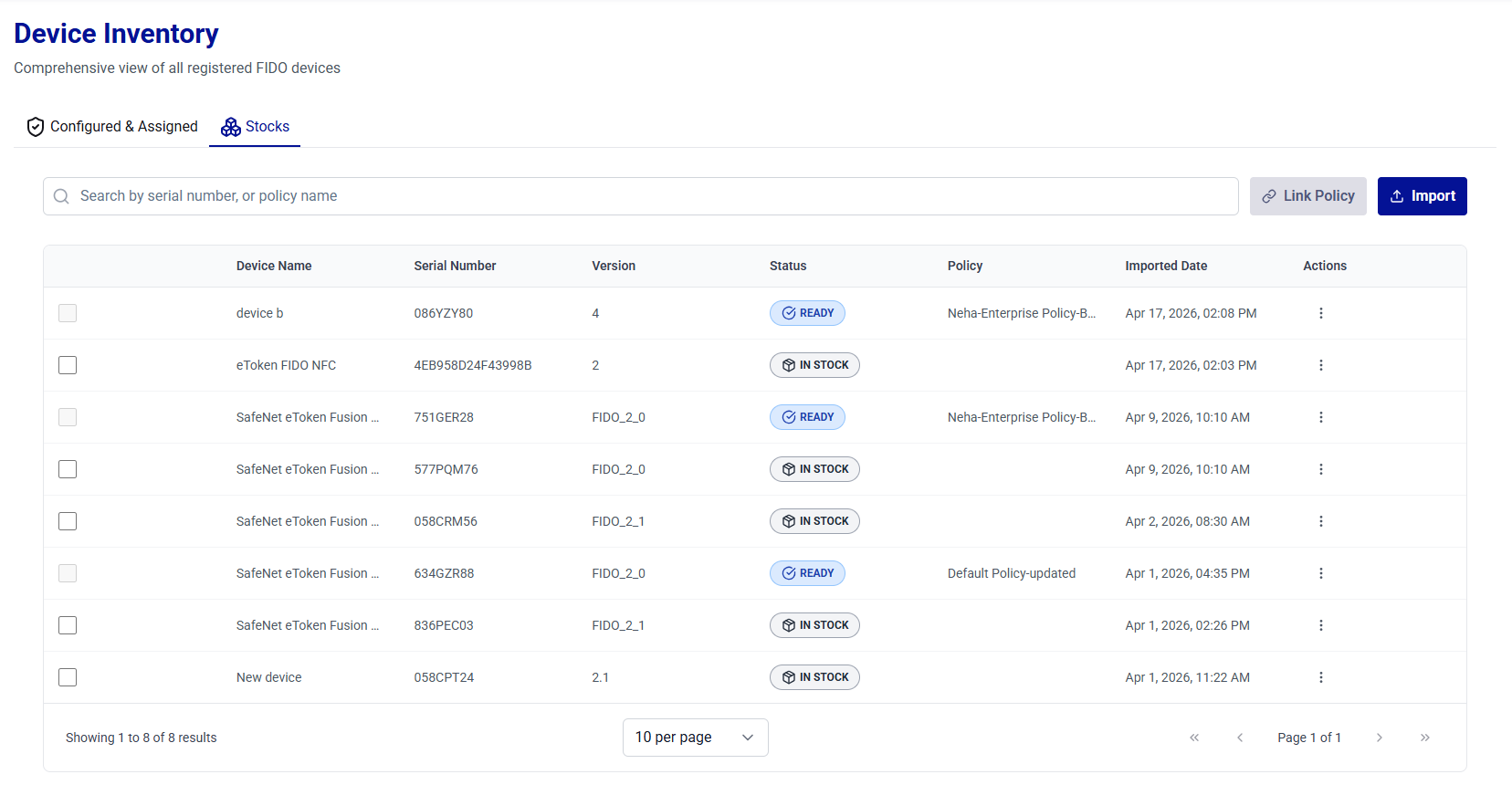
| Column | Description |
|---|---|
| Device Name | Displays the names of the FIDO authenticators (for example, SafeNet eToken Fusion NFC PIV Enterprise). |
| Serial Number | Displays the unique serial number of the device. |
| Version | Displays the device version (for example, FIDO_2_1). |
| Status | Indicates the current state of the device (for example, READY, IN STOCK). |
| Policy | Displays the authentication policies assigned to devices (if any). |
| Imported Date | Date on which the device record was imported into stock. |
| Actions | Provides options to perform the following actions on devices: - Link a policy to a device - Delete a device |
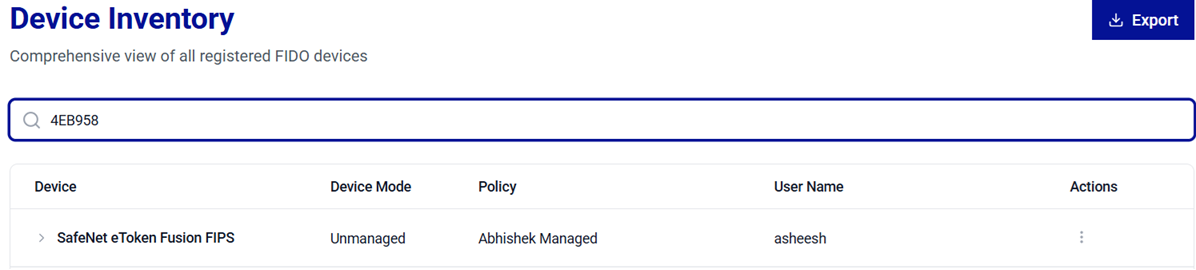
Search Devices in Stock
The Search operation allows administrators to quickly locate devices from the list. Use the search box to filter devices in stock and view their details based on any of the following criteria:
-
Serial Number – To search for a device using its unique serial number.
-
Policy Name – To list all devices to which a specific policy is applied.
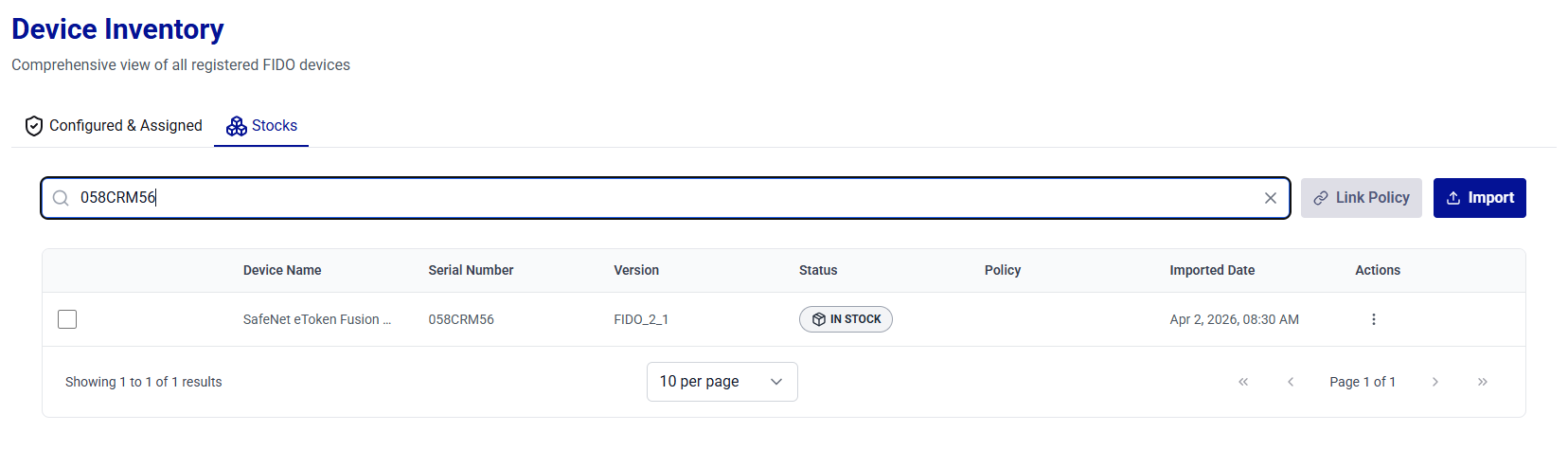
Tip
For best results, search using the full value (for example, a complete Serial Number) . If the exact value is unavailable, begin with a partial serial number, or policy name to narrow down the results.
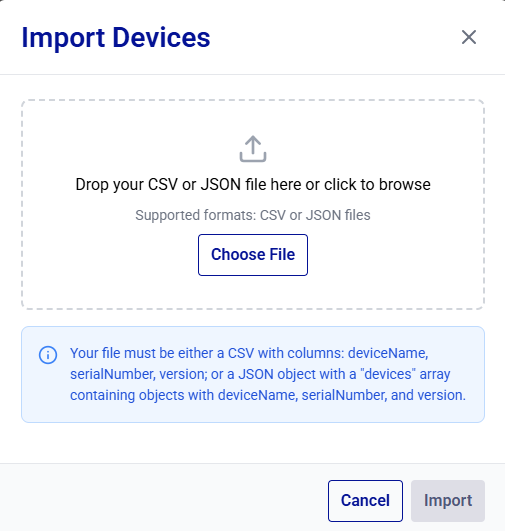
Import Devices into Stock
The Import operation allows administrators to add multiple unassigned devices to stock in a single action.
-
On the Stock tab, click Import.
-
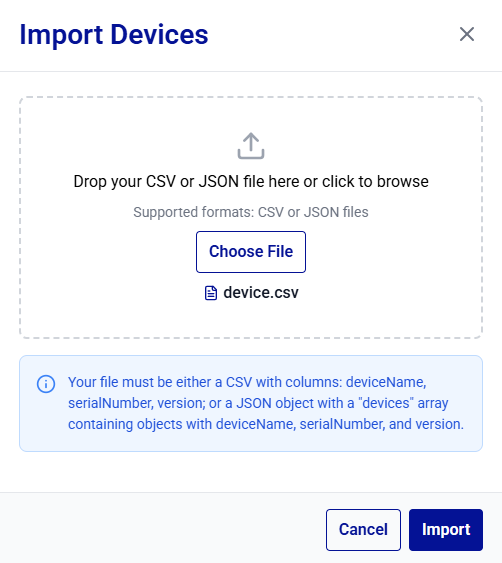
In the Import Devices dialog box, drag and drop the file into the drop zone or click Choose File to browse for the file.
-
Select a supported format and ensure the file structure matches the requirements:
- CSV – The file must include the columns, deviceName, serialNumber, and version.
-
JSON – Provide an object that contains a
devicesarray. Each entry in the array must include the deviceName, serialNumber, and version fields.Caution
Ensure that the file matches the required structure and that serial numbers are unique within your environment.
-
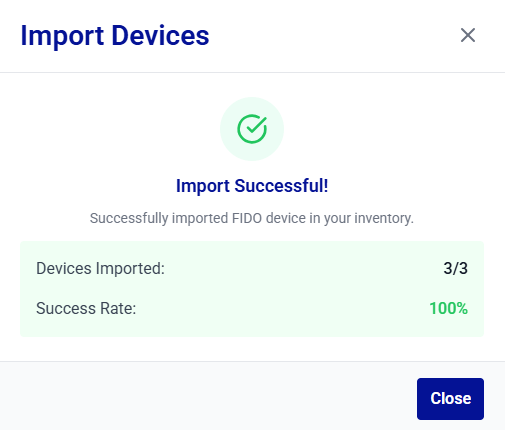
Click Import to upload and process the file.
The Import Successful! message is displayed.
-
Newly imported Device records are displayed in the device list with their corresponding import date.
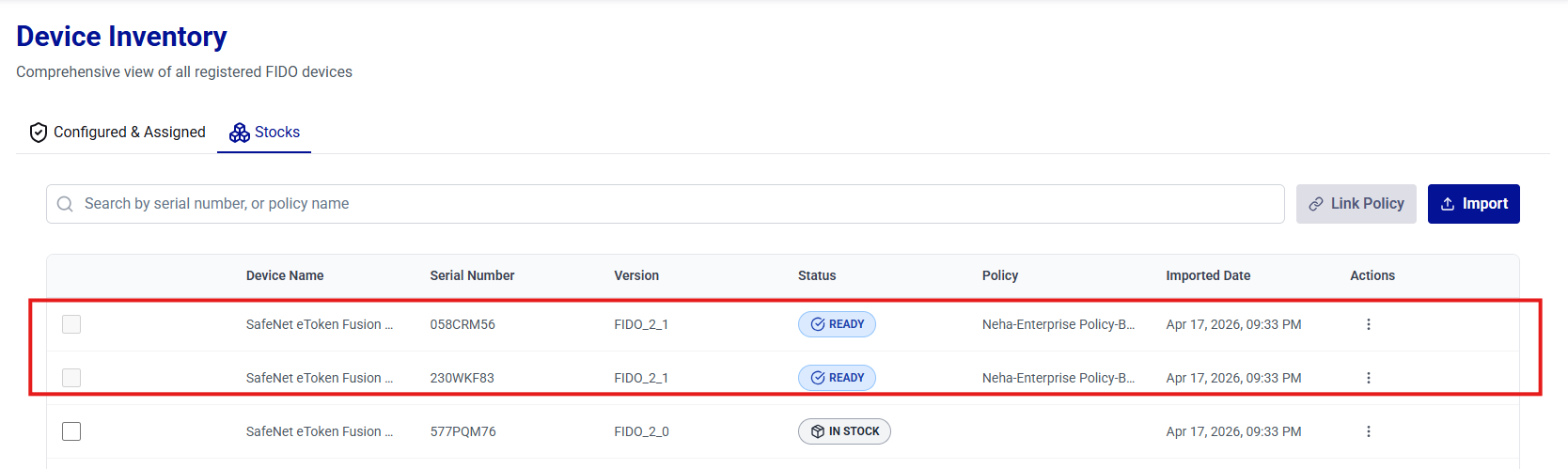
Link a Policy to Devices
The Link Policy operation allows administrators to associate devices with an authentication policy, ensuring consistent policy enforcement when the devices are assigned to users.
-
On the Stock tab, select the devices to be linked to a policy, and click Link Policy.
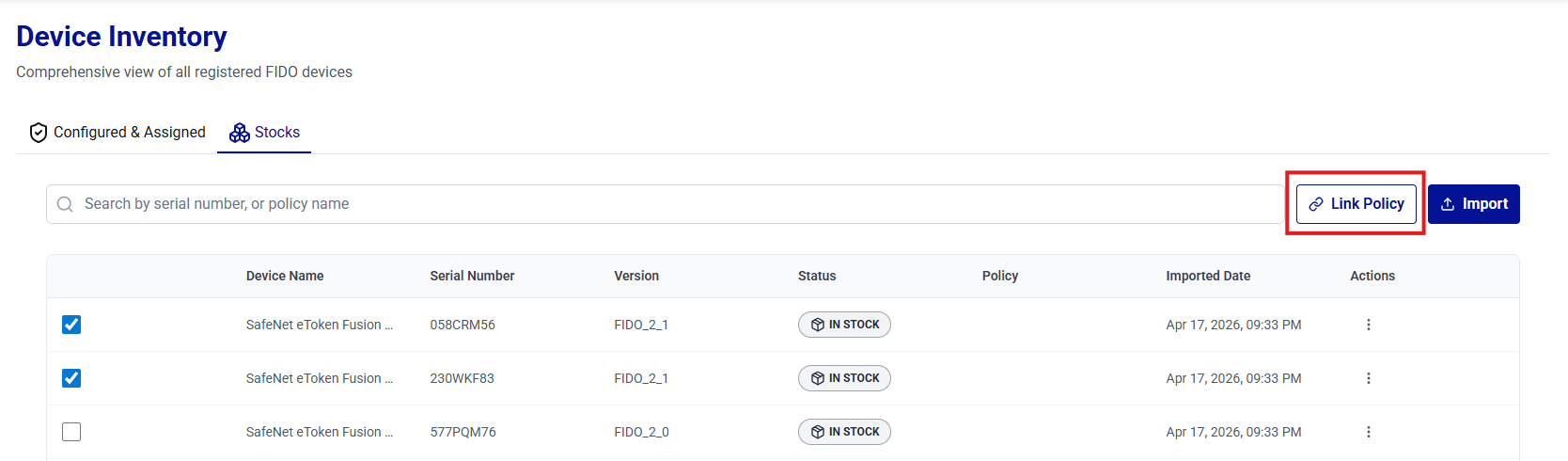
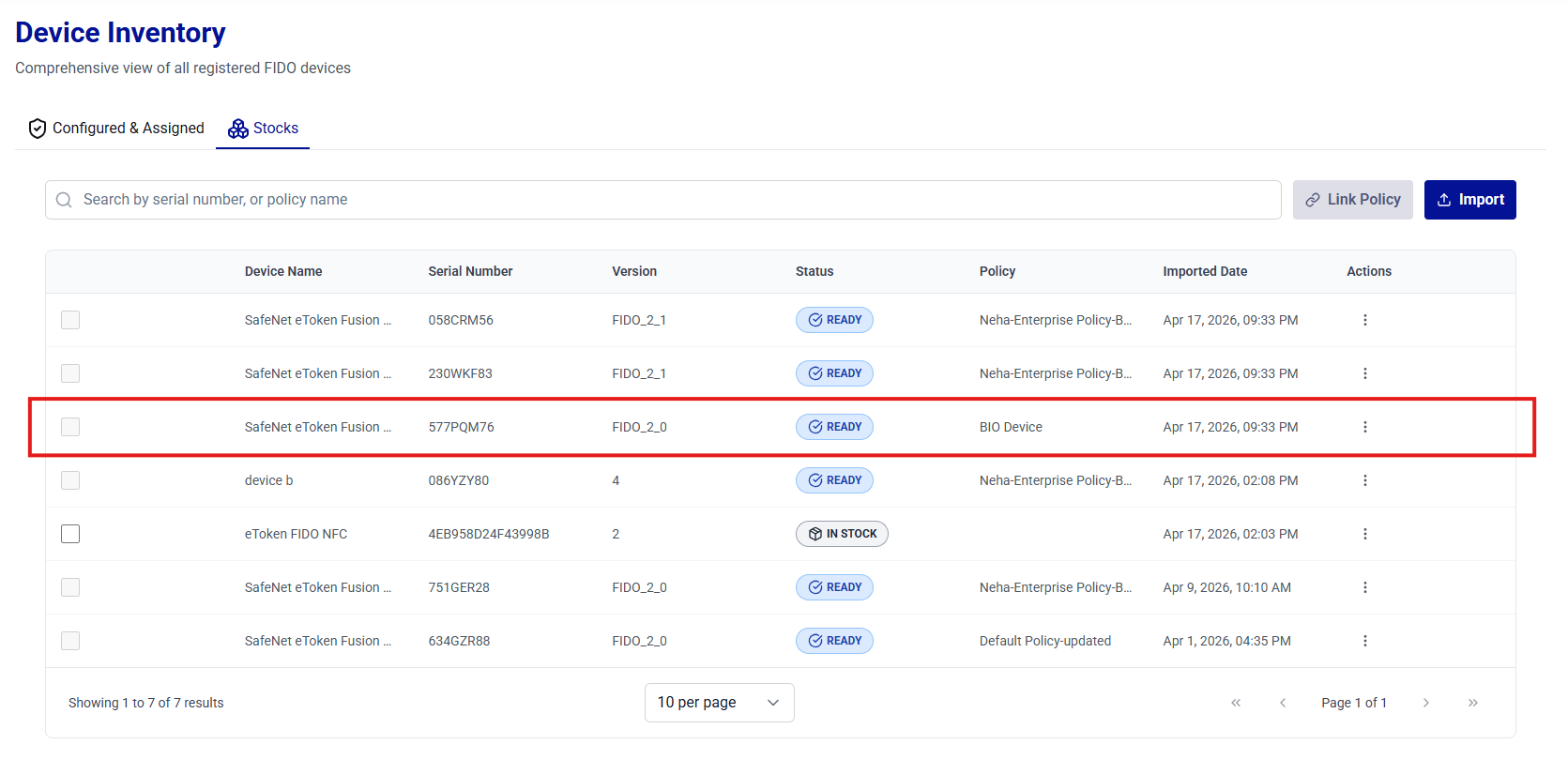
-
In the Link Policy dialog box, select the policy to be linked to device(s), and click Link Policy.
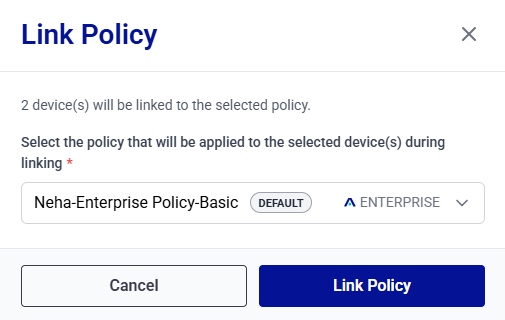
-
The Policy column is updated for the selected devices. Verify that the correct policy is displayed for each device.
Link a Policy to a Single Device
This operation allows administrators to associate a device with an authentication policy.
-
On the Stock tab, search for and locate the device you want to associate with an authentication policy.
-
In the Actions column, click the three-dots
 icon for the device, and then select Link to a Policy.
icon for the device, and then select Link to a Policy.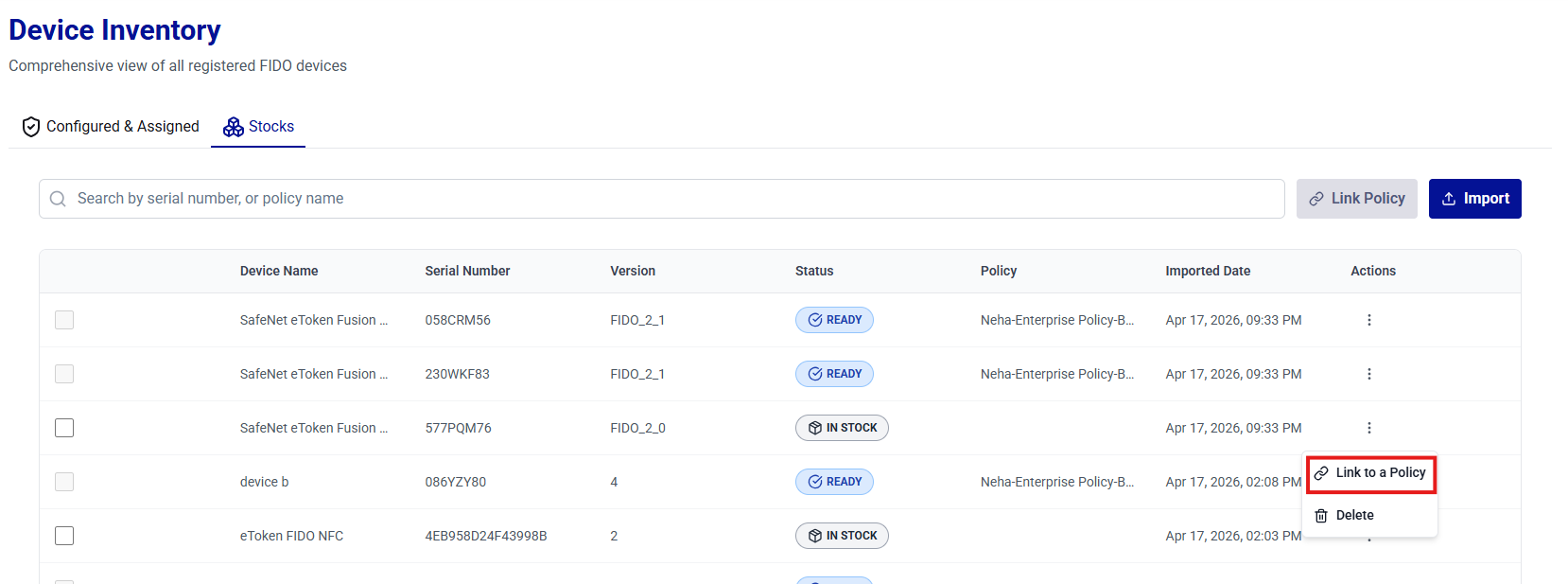
-
In the Link Policy dialog box, select the policy to be linked to the device, and click Link Policy.
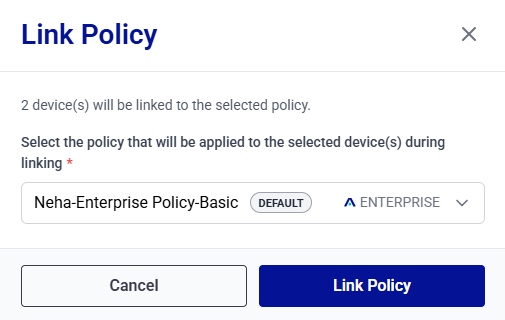
-
The Policy column is updated for the device. Verify that the correct policy is displayed for the device.
Unlink a Policy from a Single Device
This operation allows administrators to remove the policy association from a single device.
Note
Policies can be unlinked from devices only when the device state is Ready or In Stock.
-
On the Stock tab, search for and locate the device from which you want to unlink the authentication policy.
-
In the Actions column, click the three-dots
 icon for the device, and then select Unlink Policy.
icon for the device, and then select Unlink Policy.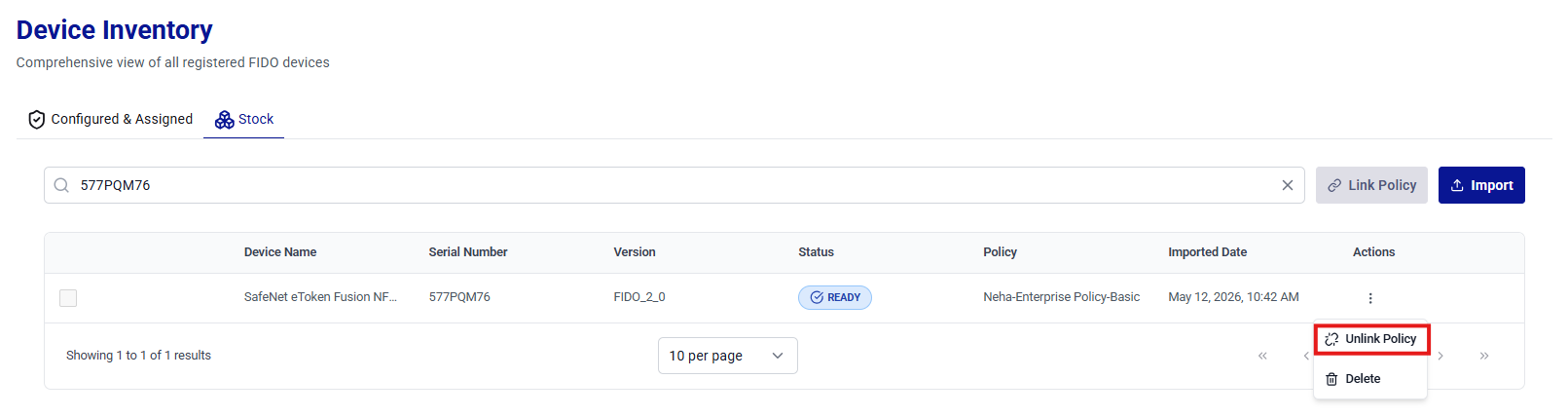
Caution
Before unlinking the policy, ensure that the operation is performed on the correct device to avoid unintended changes.
-
In the Unlink Policy dialog box, click Yes, Unlink Policy to confirm.
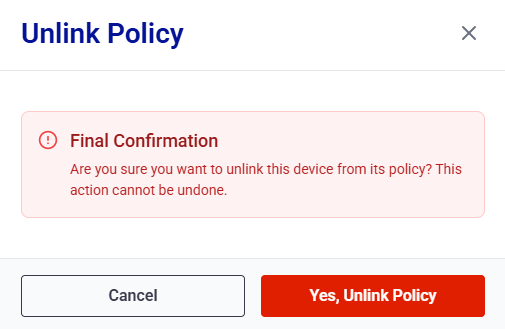
-
The policy is unlinked from the device. Verify that the Policy column is cleared for the device.
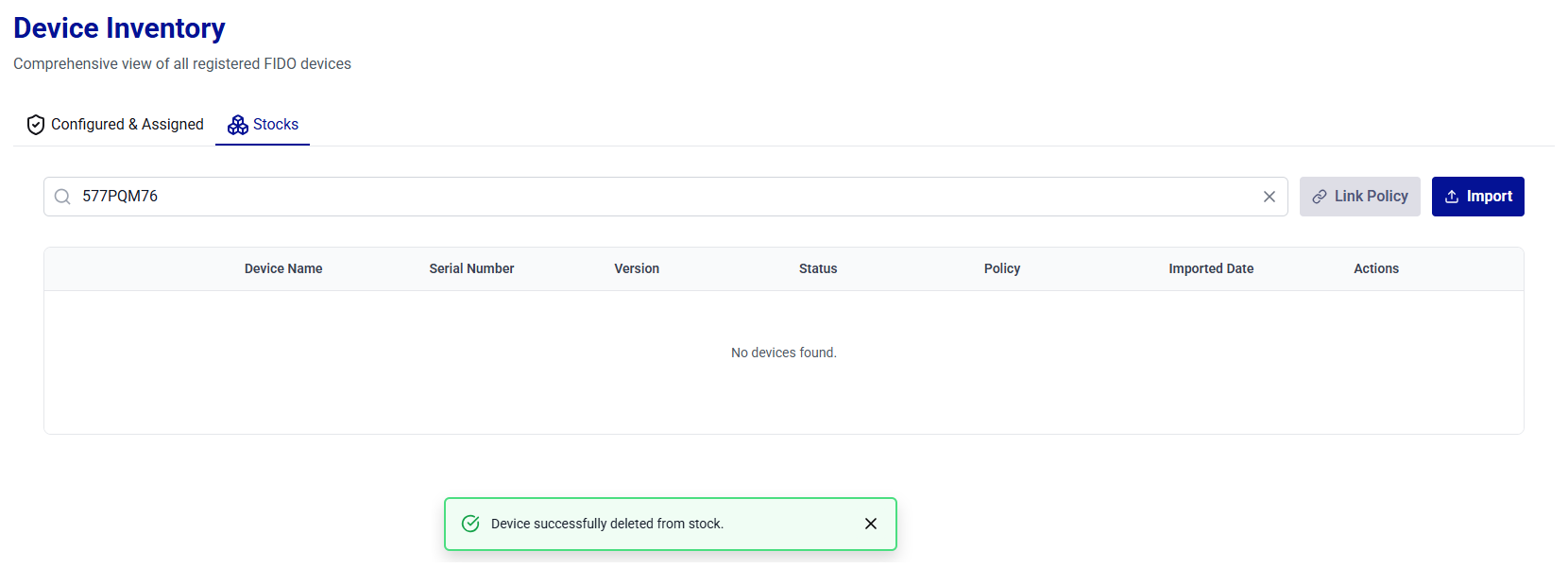
Delete a Device from Stock
This operation allows administrators to delete a device from stock.
-
On the Stock tab, search for and locate the device that you want to delete.
-
In the Actions column, click the three-dots
 icon for the device, and then select Delete.
icon for the device, and then select Delete.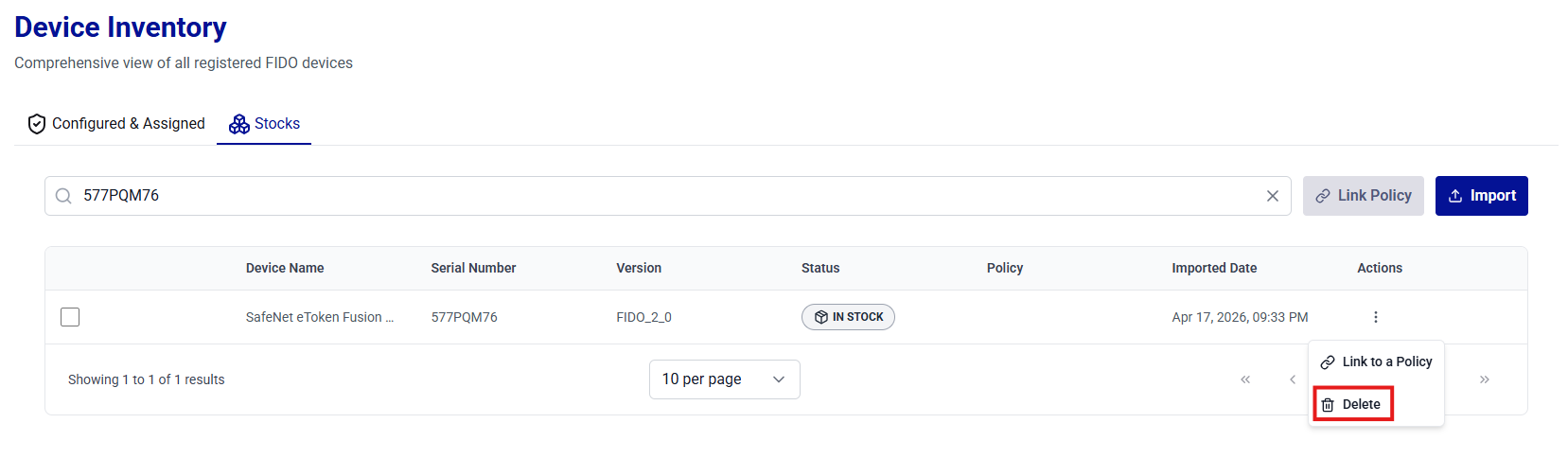
Caution
Deleting a device permanently removes it from the inventory. Ensure that the operation is performed on the correct device to avoid unintended changes.
-
In the Delete Device dialog box, review the device name, and click Yes, Delete Device to confirm.
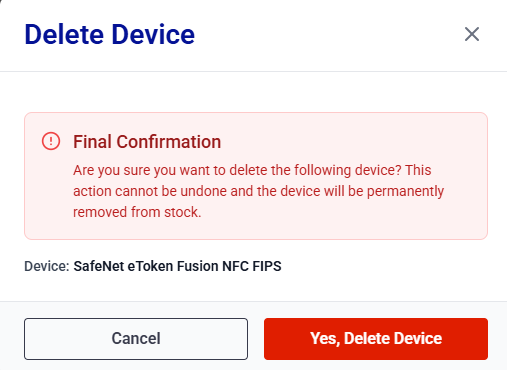
-
The Device successfully deleted from stock. message is displayed. Verify that the device no longer appears in the device list under Stock.