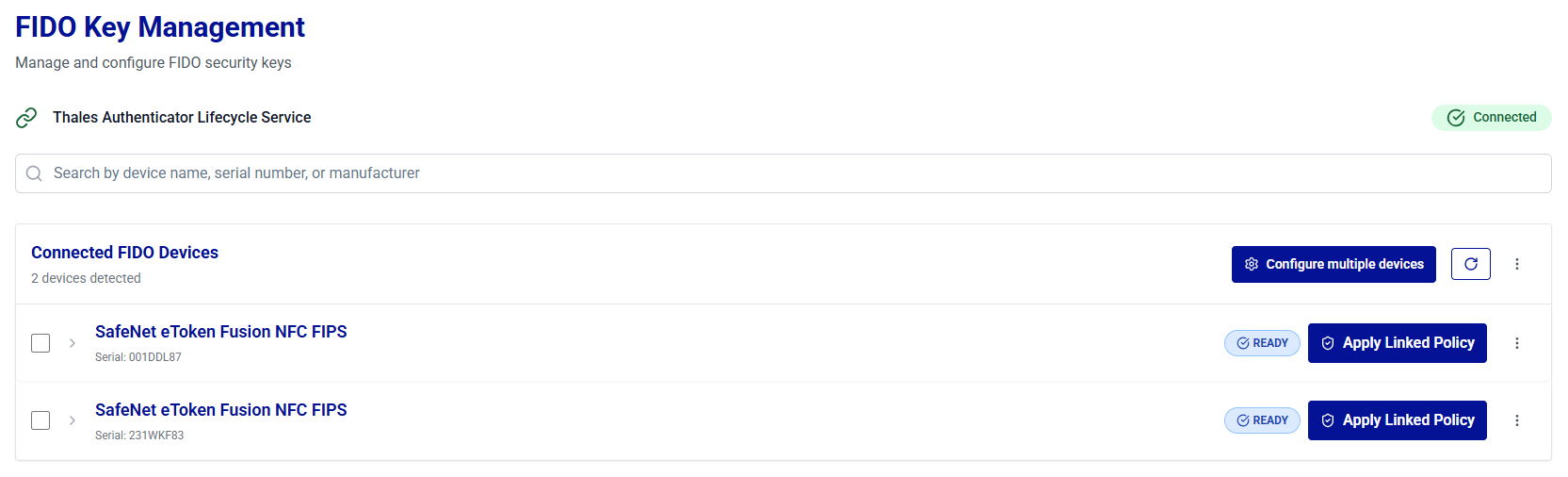
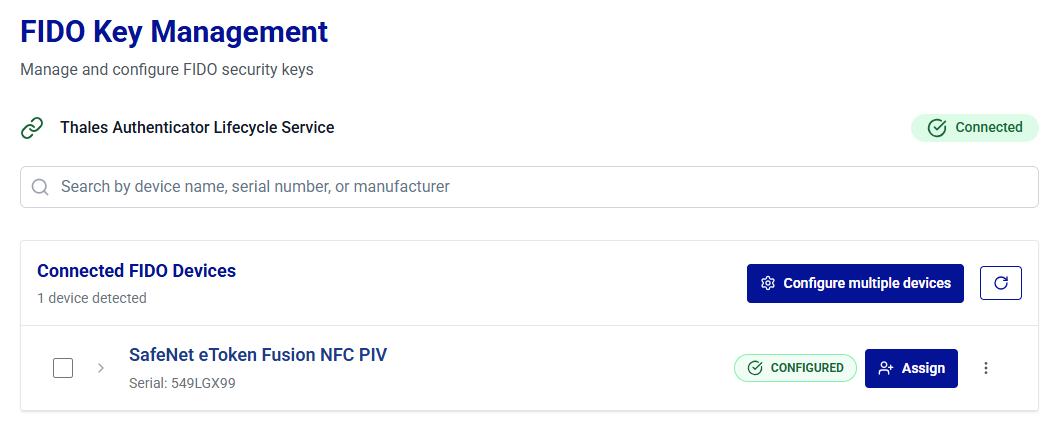
FIDO Key Management
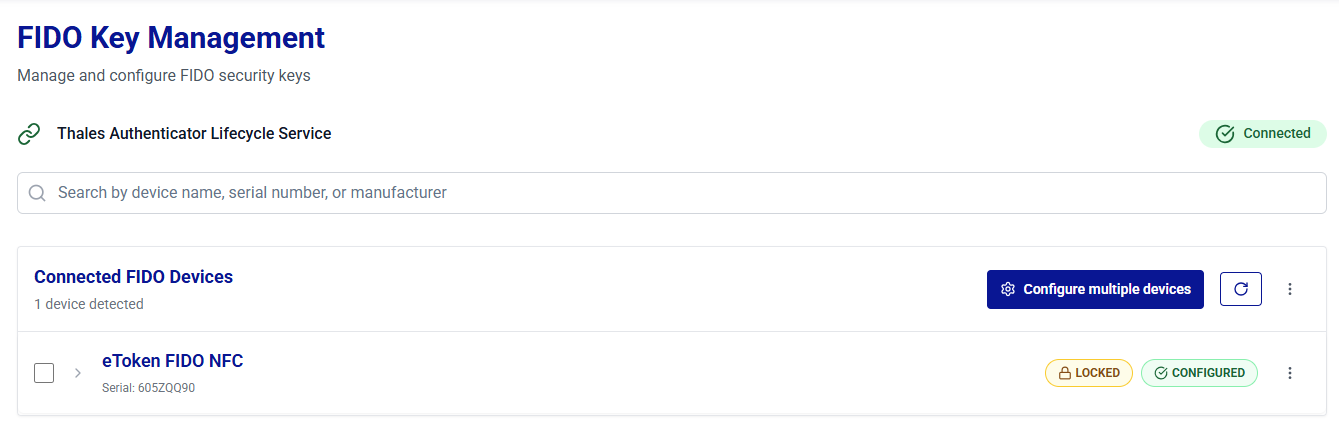
FIDO Key Management provides administrators with secure and real-time control over FIDO authenticators connected to the local workstation. Using the Thales Authenticator Lifecycle Service (running on port 9333), administrators can perform FIDO device discovery, registration, configuration, lifecycle operations (such as device reset and revocation), and functional testing.
The FIDO Key Management window is optimized for routine device operations and complements the Device Inventory by enabling actions that require physical access to a FIDO key.
Under FIDO Key Management, administrators can perform the following operations:
- Connect to the Thales Authenticator Lifecycle Service
- View Connected FIDO Devices List
- Configure FIDO Devices
Connect to the Thales Authenticator Lifecycle Service
For each new login session, Thales Authenticator Lifecycle Manager automatically connects to the Thales Authenticator Lifecycle Service before you perform any operations on FIDO devices.
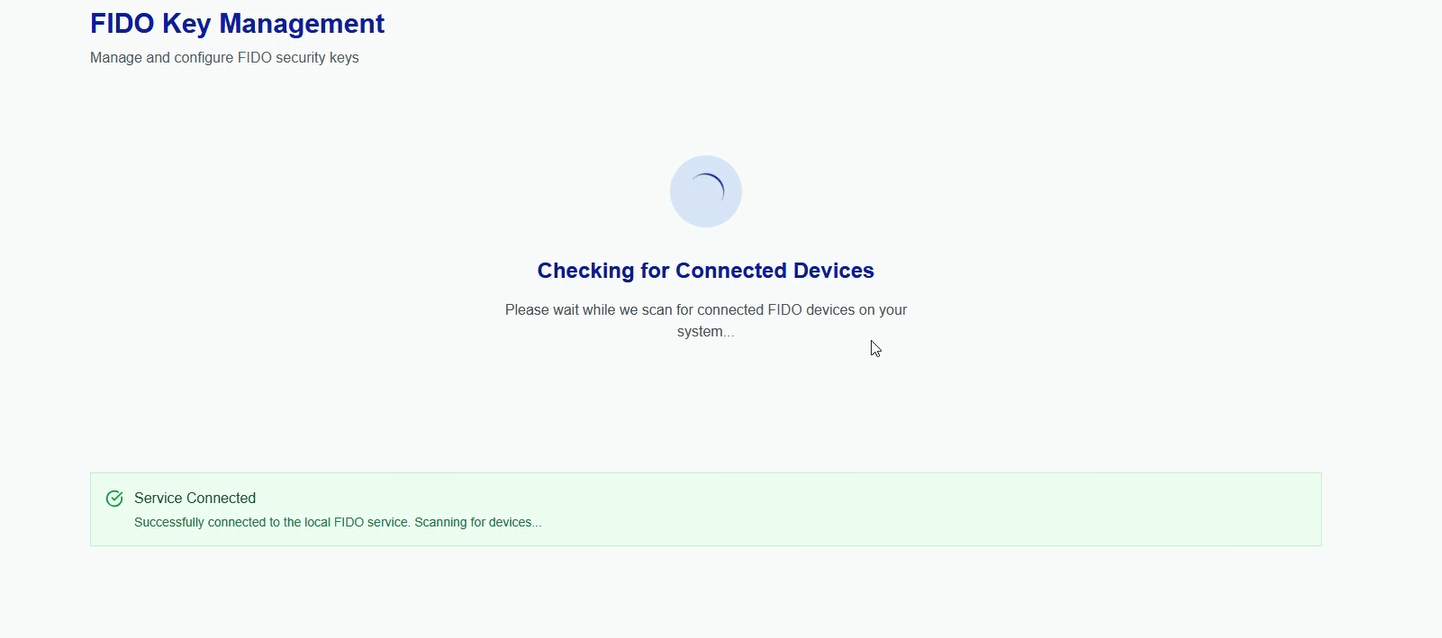
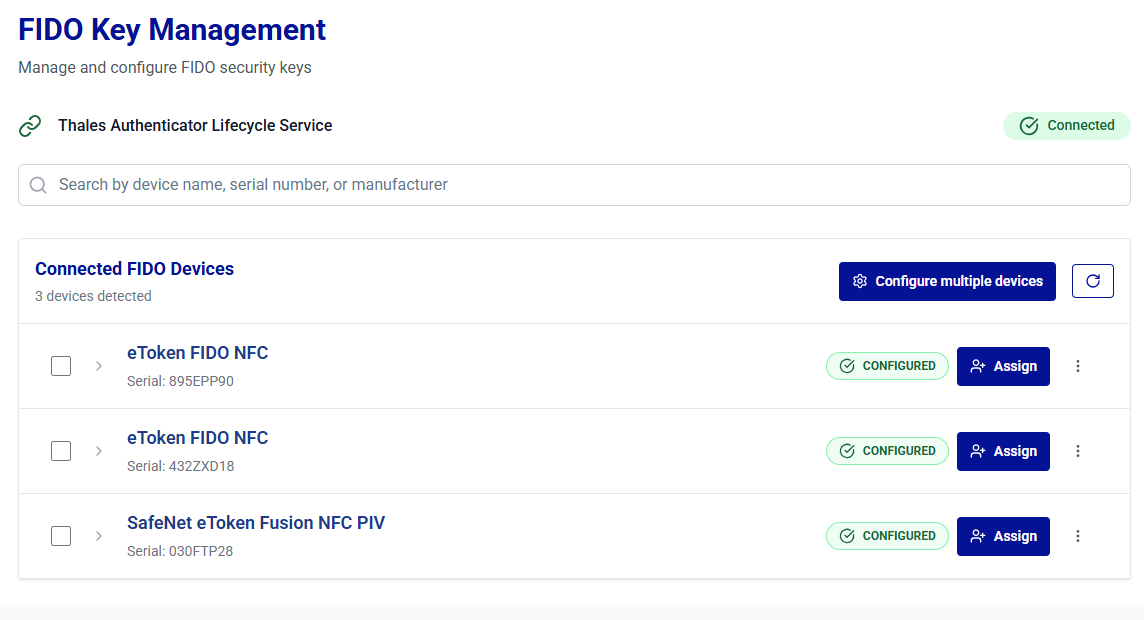
When you open the FIDO Key Management window, the connection to the Thales Authenticator Lifecycle Service (Windows service) is established automatically. If the service is stopped or the automatic connection attempt fails, click Connect to Service to retry.
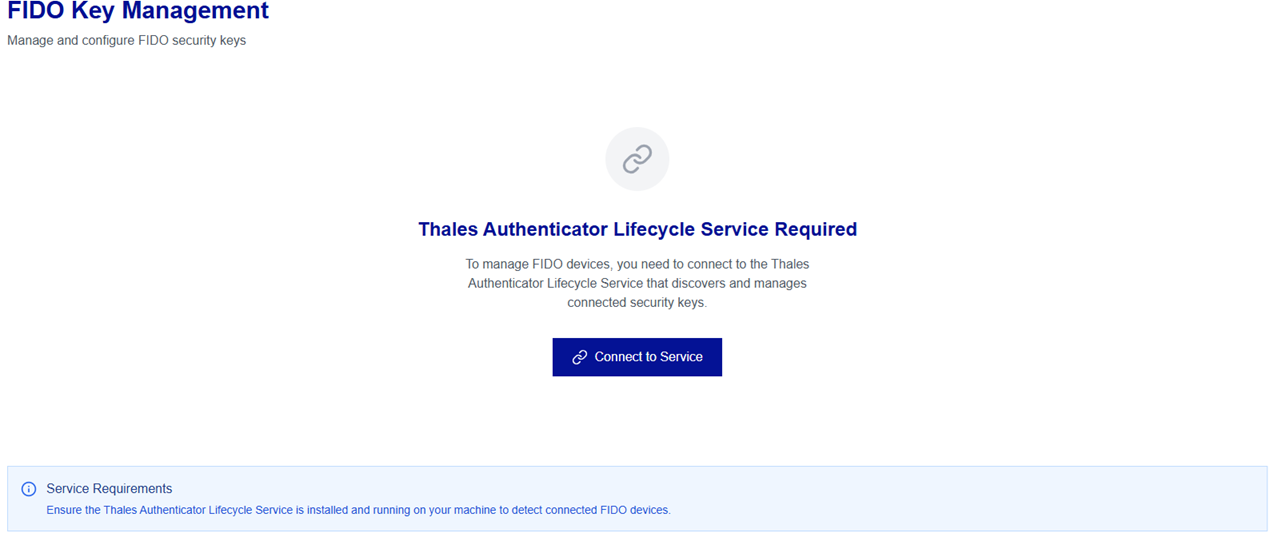
After the connection is successfully established, the Service Connected message is displayed.
Do not perform device operations in multiple browser tabs simultaneously, as performing actions such as configuration, enrollment, reset, or remote unlock across different tabs at the same time may lead to unexpected errors or inconsistent device or service behavior.
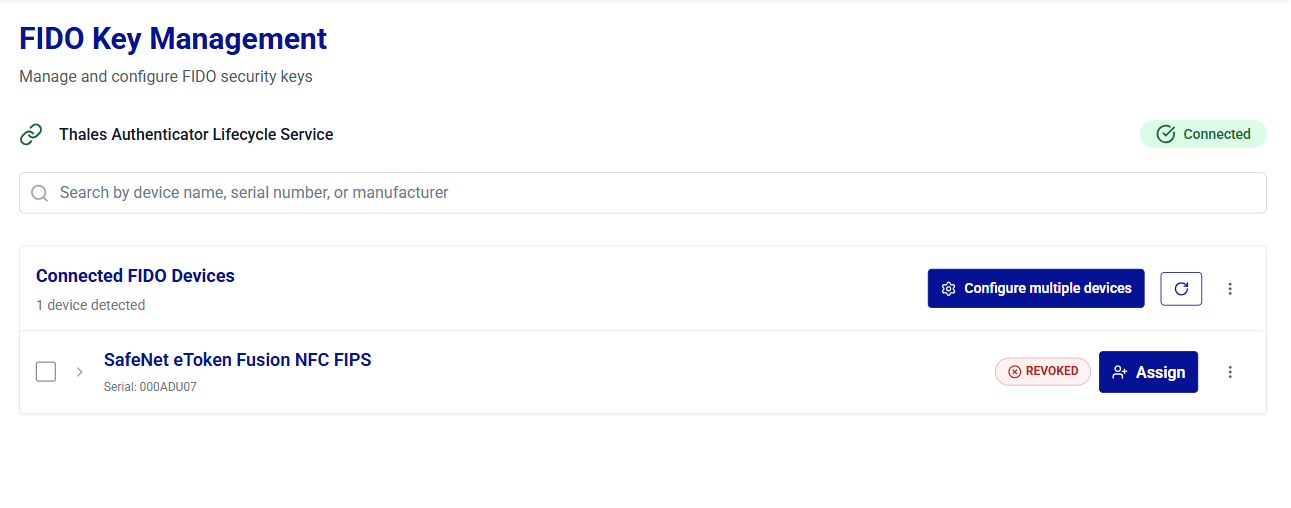
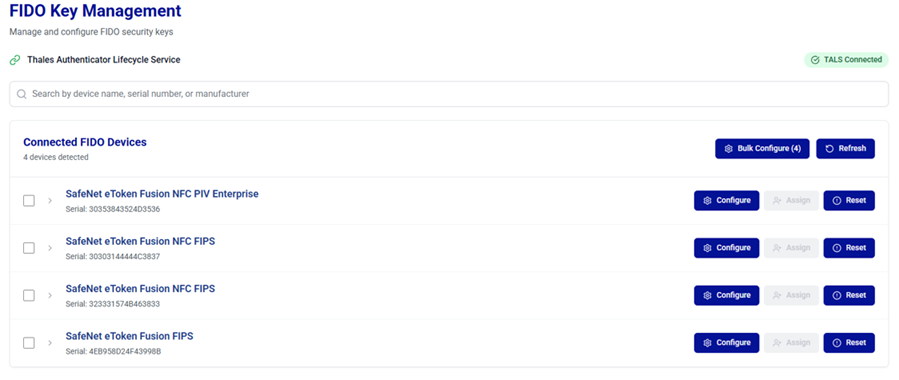
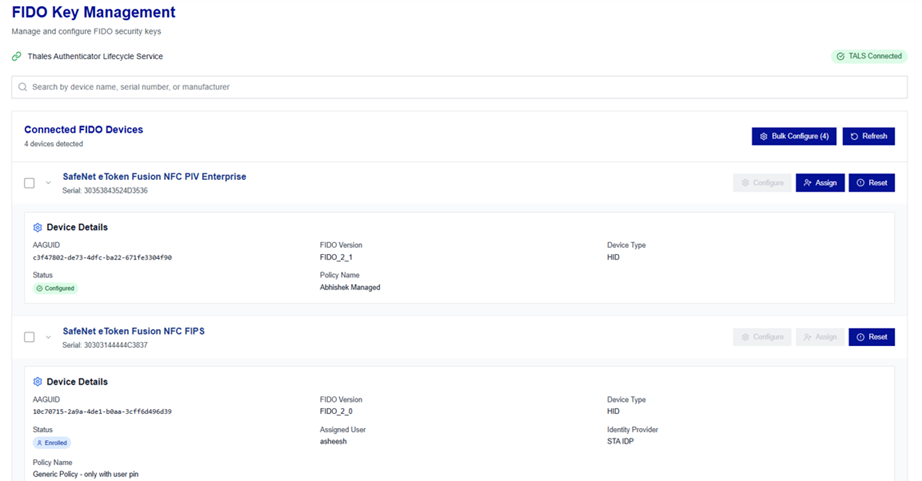
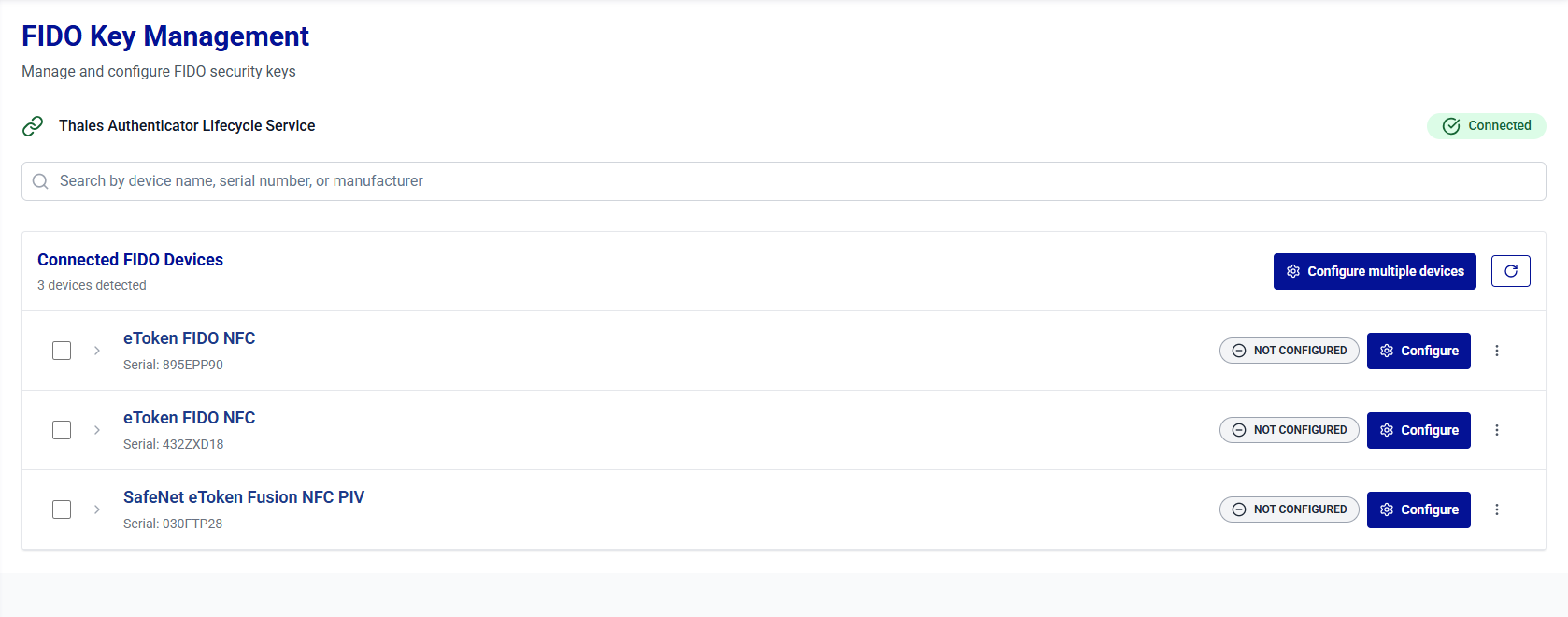
View Connected FIDO Devices List
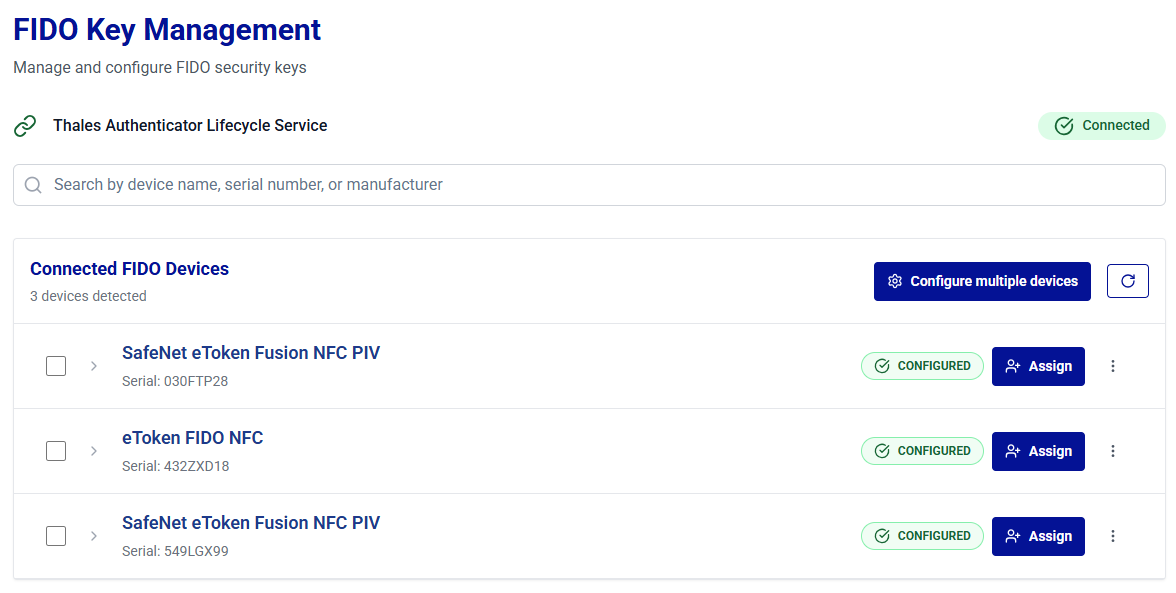
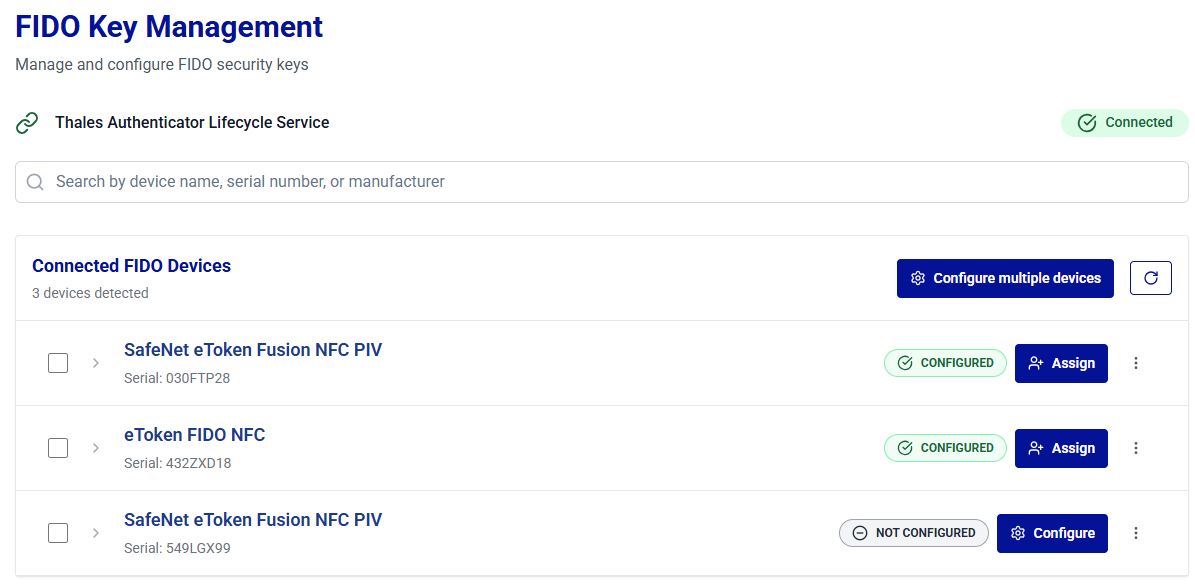
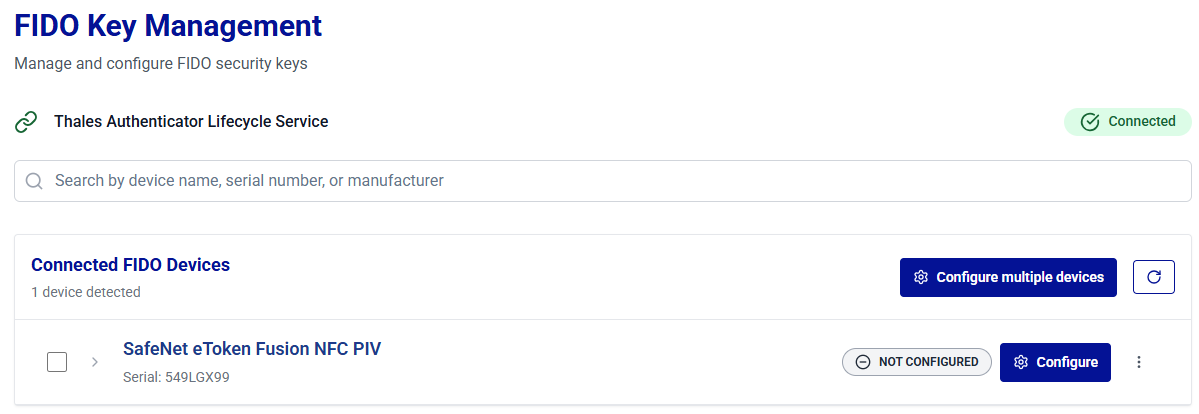
Once the Thales Authenticator Lifecycle Service is connected, it automatically begins scanning for connected FIDO devices. After the scanning is complete, the detected devices are loaded and displayed on the window.
Note
Additional devices can be connected at any time, and clicking the Refresh button will load them and display on the window.
The connected FIDO devices are displayed in a collapsible list. Device details are presented in two views to help administrators access information efficiently.
-
Summary View: Displays essential device details in a compact format for quick identification and action. The summary view displays:
- Device name
- Device serial number
- Device status as NOT CONFIGURED, READY, CONFIGURED, ENROLLED, IN STOCK, and REVOKED
Note
NOT CONFIGURED devices can be configured by using the Configure button and CONFIGURED devices can be assigned to users using the Assign button.
-
Expanded View: Displays complete device information, including lifecycle and compliance details, for in-depth management. After you click the expand arrow
 icon for the desired device, the following additional details are displayed:
icon for the desired device, the following additional details are displayed:- AAGUID
- FIDO Version
- Device Type
- Assigned User
- Identity Provider
- Policy Name
Configure FIDO Devices
Device configuration can be done using the following options:
-
Configure Multiple FIDO Devices - To configure all the devices using a single policy in one operation.
-
Configure Selected FIDO Devices - To configure selected devices using a single policy in one operation.
-
Configure Specific FIDO Devices - To configure a specific device by applying a selected policy.
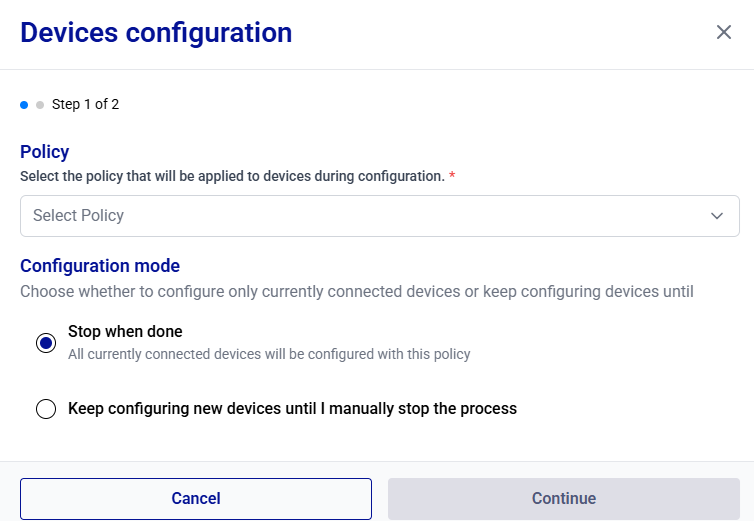
Configure Multiple FIDO Devices
-
Under Connected FIDO Devices, click Configure multiple devices.
-
On the Devices configuration window, you can configure devices using one of the following two options:
- Stop when done: Enables configuration of all devices that are currently connected. The process stops automatically once the configuration of these devices is complete.
- Keep configuring new devices until I manually stop the process: Enables continuous configuration mode. When this option is selected, the system automatically detects and configures each new device connected one by one by the administrator for configuration. The process continues until you manually stop it. Device configuration using this option can be initiated even if no devices are currently connected.
Stop when done
-
Under Policy, select a policy to be applied to the devices.
-
Under Configuration mode, ensure that the Stop when done option is selected.
-
Click Continue anyway.
-
Under Confirm configuration settings, select Start Configuration.
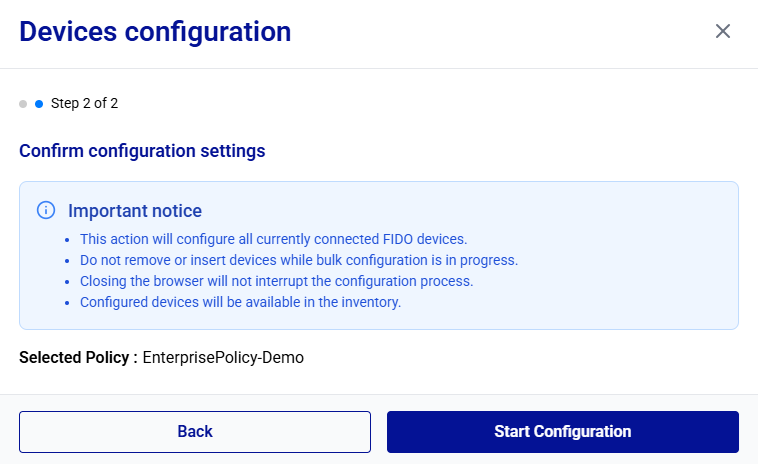
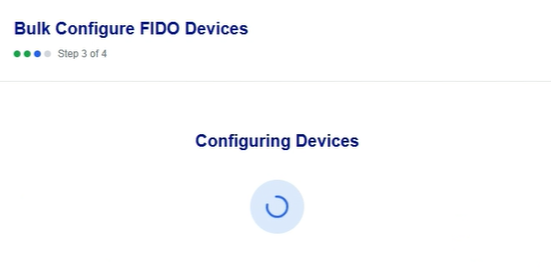
The device configuration is started. It may take some time to complete.
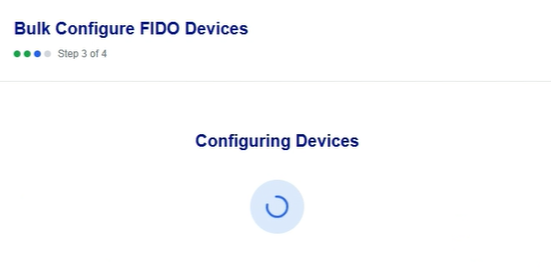
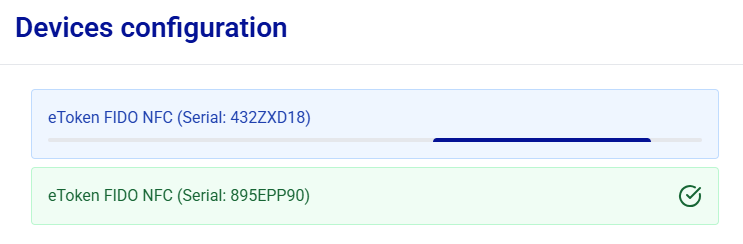
During device configuration, each device appears in green as soon as its configuration is completed.
Removing a device during configuration may result in an inconsistent device state.
-
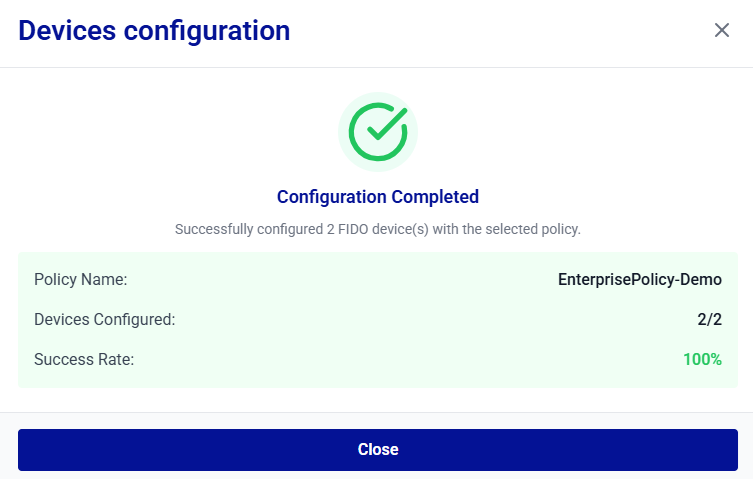
After the configuration completes successfully, the Configuration Completed message is displayed. Click Close.
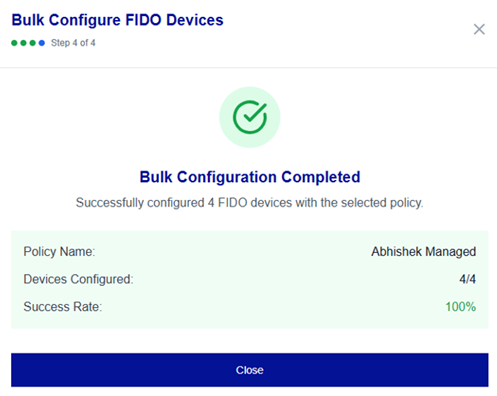
You can export the enrollment logs by clicking the Download report button to save a report (CSV or JSON) of the configuration session.
After you click Close, Thales Authenticator Lifecycle Service automatically begins scanning for the connected FIDO devices. After the scanning completes, the detected devices are reloaded and displayed with their updated status under Connected FIDO Devices.
Keep configuring new devices
-
Under Policy, select a policy to be applied to the devices.
-
Under Configuration mode, select the Keep configuring new devices until I manually stop the process option.
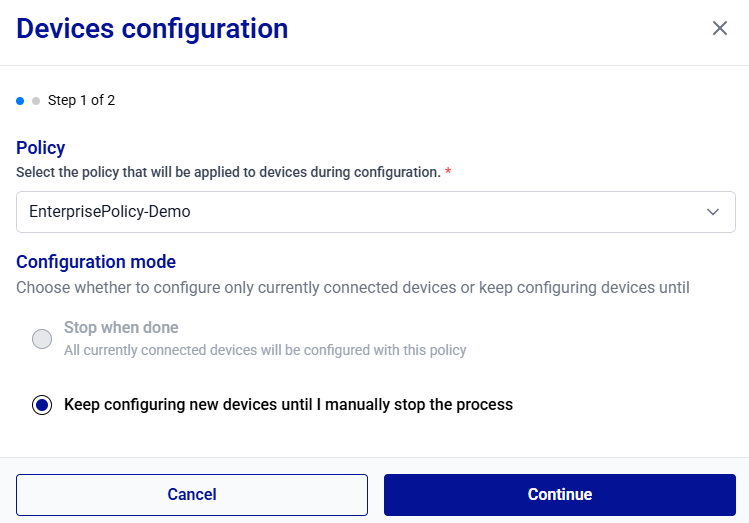
If an admin initiates the device configuration process when no devices are connected, the Keep configuring new devices until I manually stop the process option is selected by default.
-
Click Continue.
-
Under Confirm configuration settings, select Start Configuration.
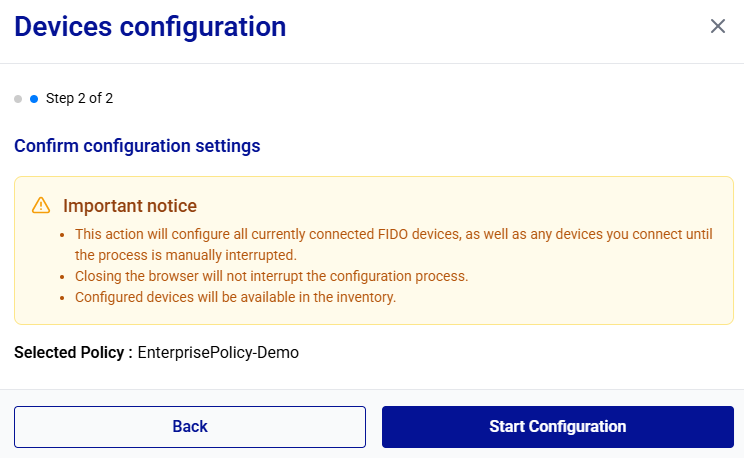
-
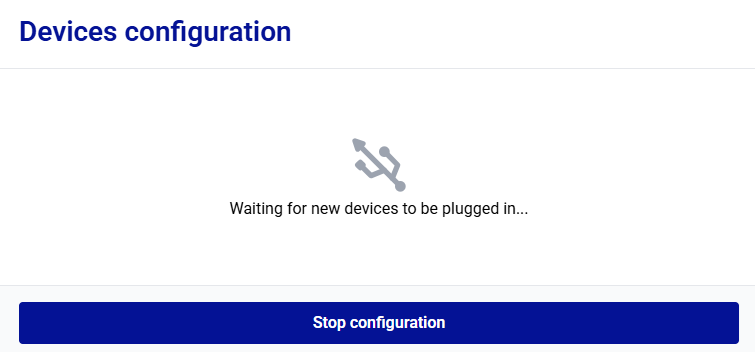
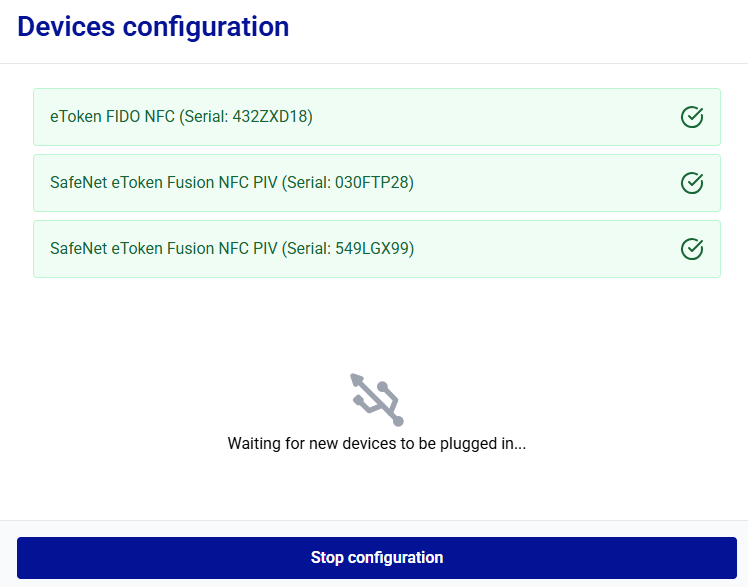
Thales Authenticator Life Cycle Manager waits for you to connect devices for configuration. Start connecting the devices to be configured.
After you begin connecting the devices, Thales Authenticator Lifecycle Manager automatically starts configuring them. Each device is displayed in green as soon as its configuration is completed.
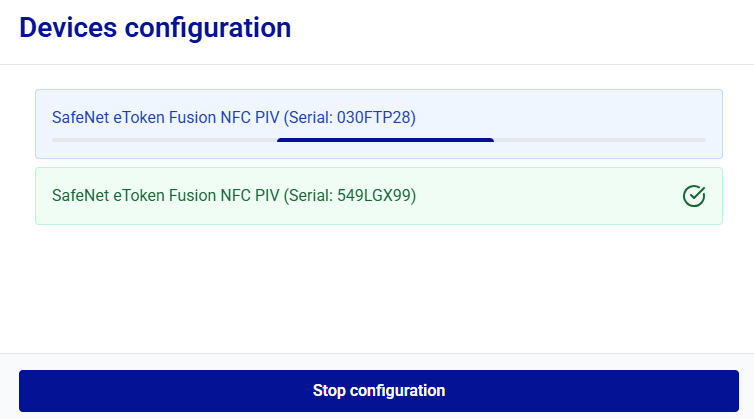
Removing a device during configuration may result in an inconsistent device state.
-
Click Stop configuration when you want to stop configuring additional FIDO devices.
-
After the configuration completes successfully, the Configuration Completed message is displayed. Click Close.
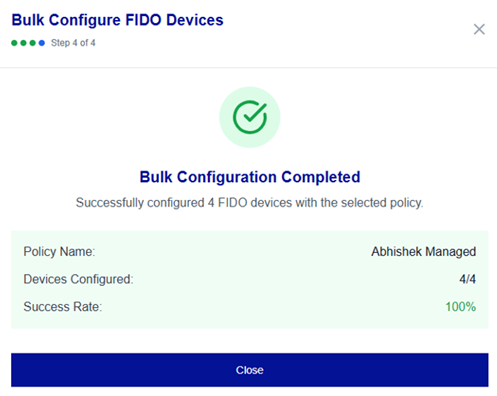
You can export the configuration logs by clicking the Download report button to save a report (CSV)of the configuration session.
After you click Close, Thales Authenticator Lifecycle Service automatically begins scanning for the connected FIDO devices. After the scanning completes, the detected devices are reloaded and displayed with their updated status under Connected FIDO Devices.
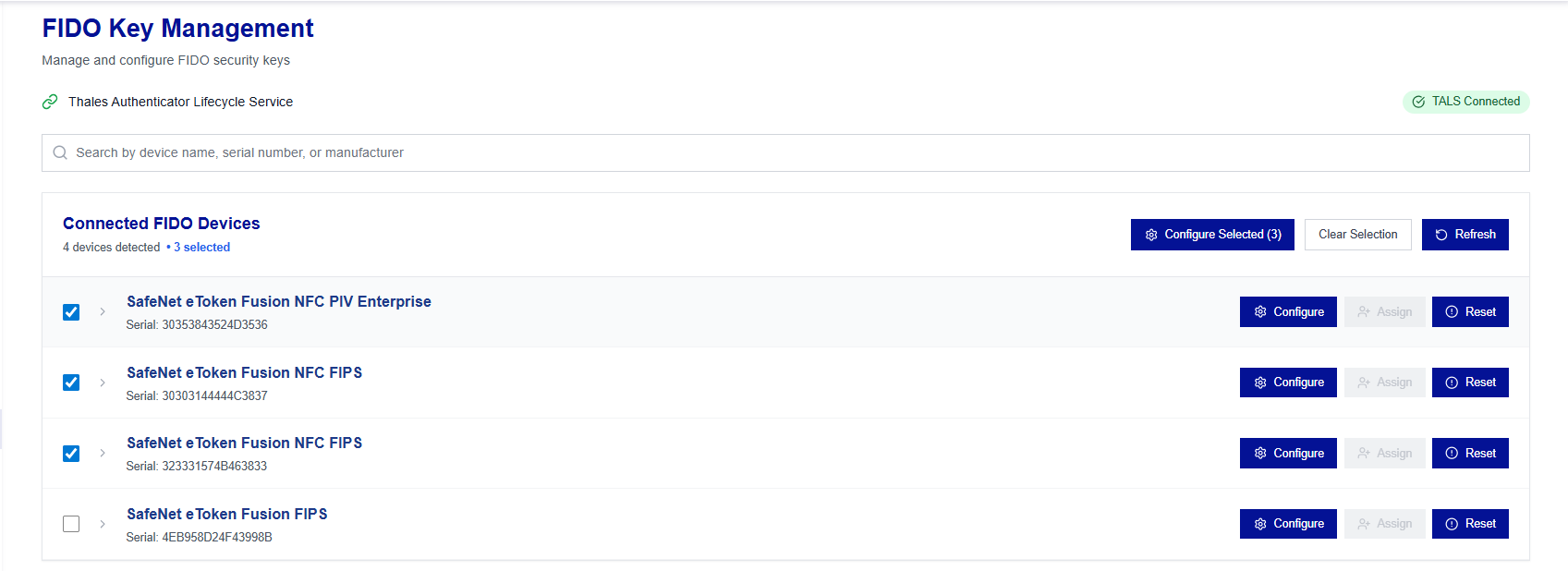
Configure Selected FIDO Devices
-
Under Connected FIDO Devices, select the FIDO devices to be configured, and click Configure devices.
-
Under Device configuration, select a policy to be applied to the selected devices, and click Continue anyway.
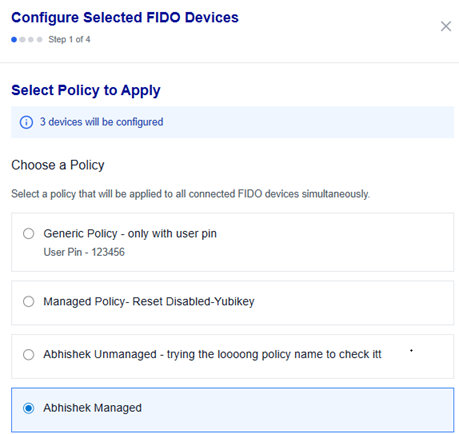
-
Under Confirm configuration settings, select Start Configuration.
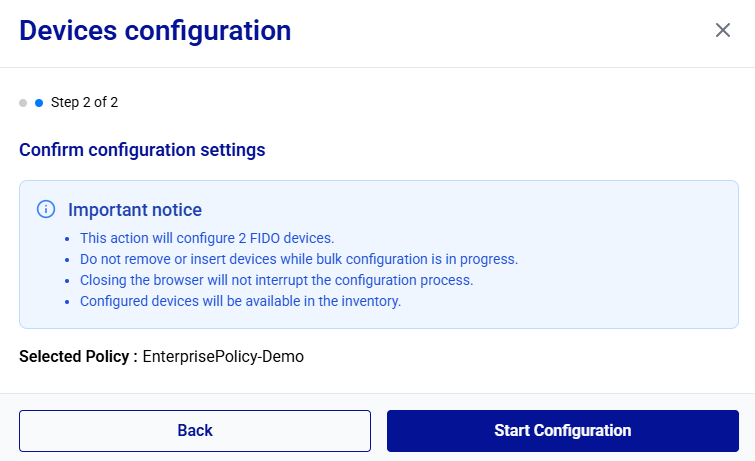
The device configuration is started. It may take some time to complete.
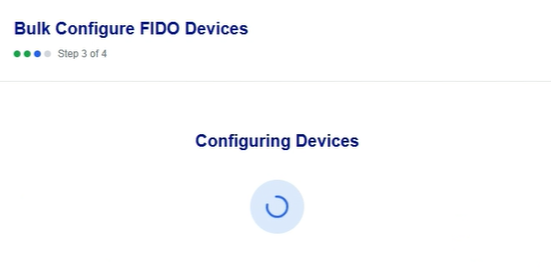
During device configuration, each device appears in green as soon as its configuration is completed.
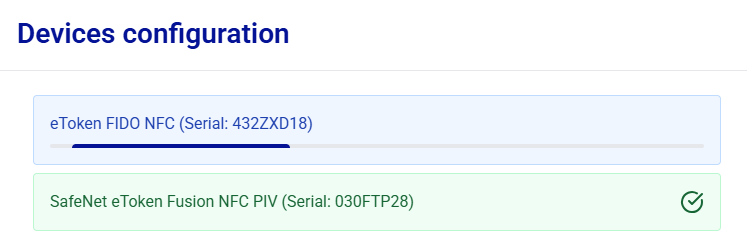
Removing a device during configuration may result in an inconsistent device state.
-
After the configuration completes successfully, the Configuration Completed message is displayed. Click Close.
You can export the configuration logs by clicking the Download report button to save a report (CSV or JSON) of the configuration session.
After you click Close, Thales Authenticator Lifecycle Service automatically begins scanning for the connected FIDO devices. After the scanning completes, the detected devices are reloaded and displayed with their updated status under Connected FIDO Devices.
Configure Specific FIDO Devices
-
Under Connected FIDO Devices, select the target device, and click Configure.
-
On the Configure Device window, select a policy to be applied to the device, and click Continue anyway.
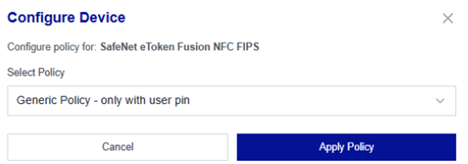
The configuration is started. It may take some time to complete.
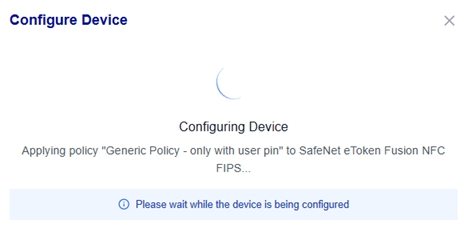
-
After the policy is successfully applied to the device, the Configuration Complete! message is displayed. Click Close.
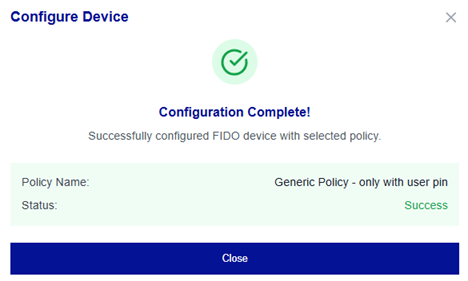
You can export the configuration logs by clicking the Download report button to save a report (CSV or JSON) of the configuration session.
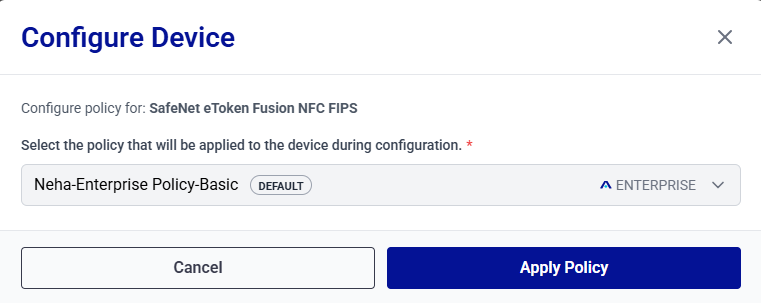
Apply Linked Policy
Use the Apply Linked Policy action to quickly configure connected devices by applying their associated policies.
You can,
Apply Linked Policy to a Ready Device (Single Device)
-
Under Connected FIDO Devices, locate the target device with the Ready status, and click Apply Linked Policy for the device.
-
On the Configure Device window, select the policy to be applied to the device, and click Apply Policy.
-
After the policy is successfully applied to the device, the Configuration Complete! message is displayed. Click Close.
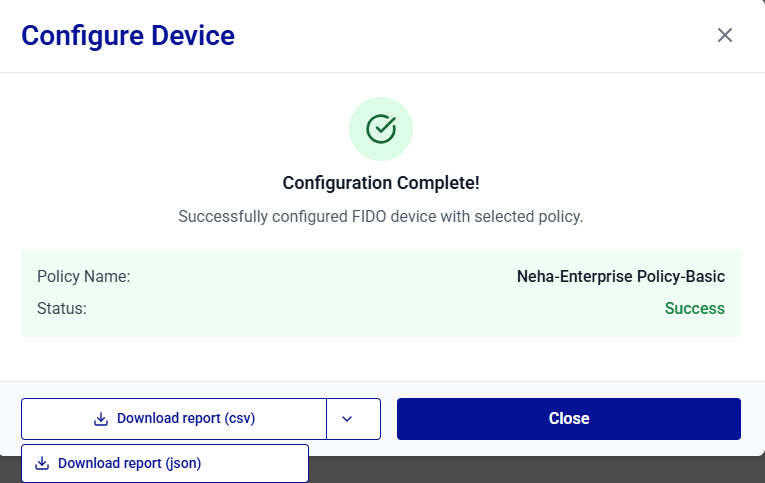
You can export the configuration logs by clicking the Download report button to save a report (CSV or JSON) of the configuration session.
Apply Linked Policy to Ready Devices (Bulk)
-
Under Connected FIDO Devices, next to the Configure multiple device button, click the three-dots
 , and select Apply Linked Policy to Ready Devices.
, and select Apply Linked Policy to Ready Devices.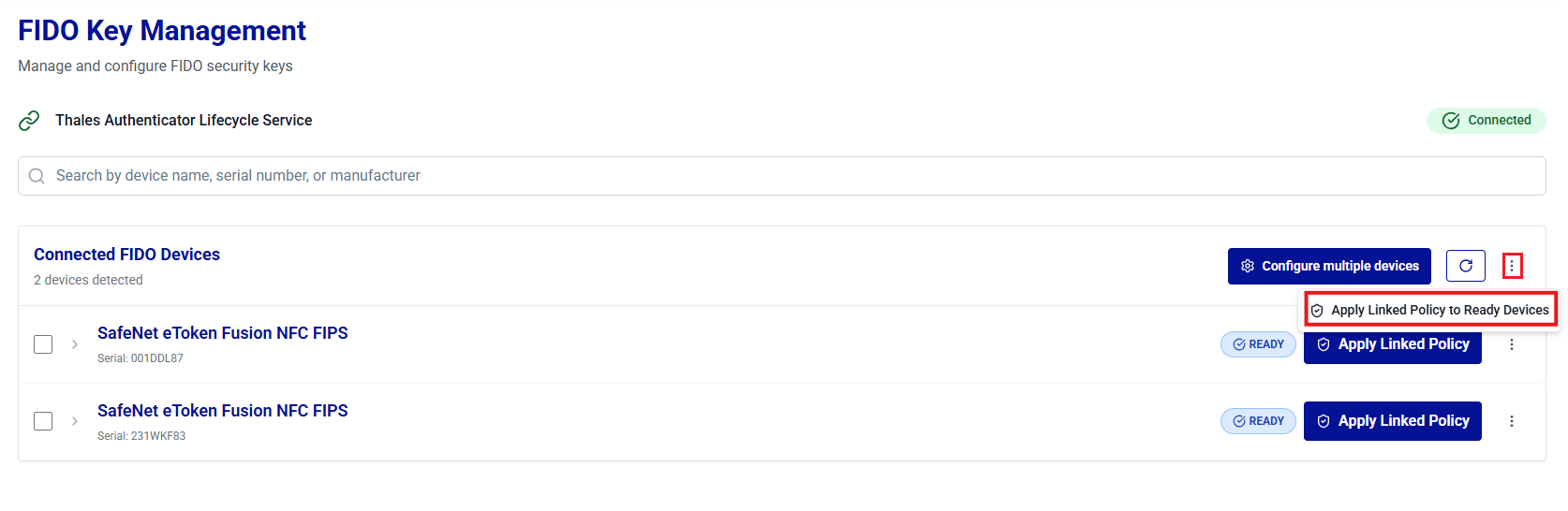
-
Review the list of the detected devices and click Start Configuration to configure the devices.
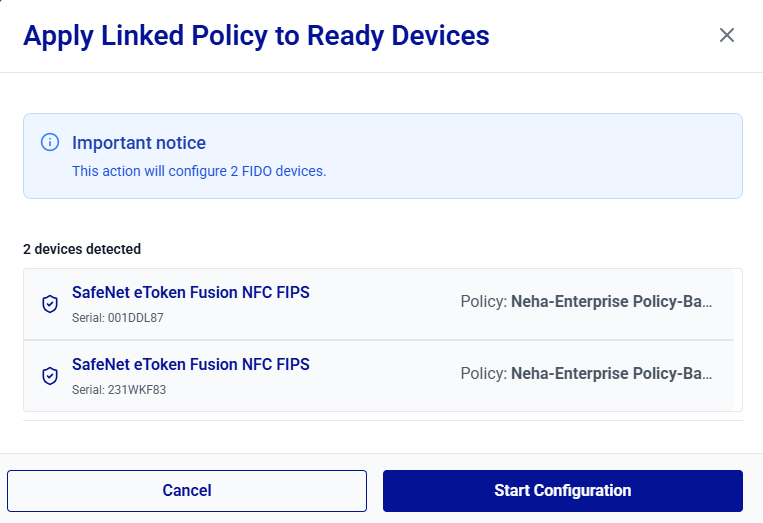
The device configuration is started. It may take some time to complete.
During device configuration, each device appears in green as soon as its configuration is completed.
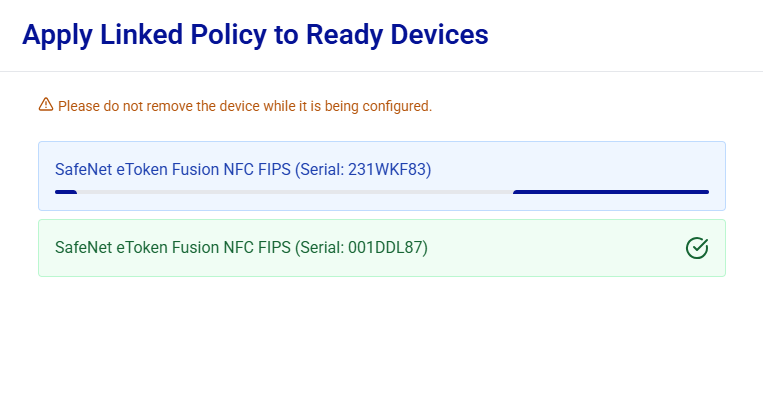
Removing a device during configuration may result in an inconsistent device state.
-
After the configuration completes successfully, the Configuration Completed message is displayed. Click Close.
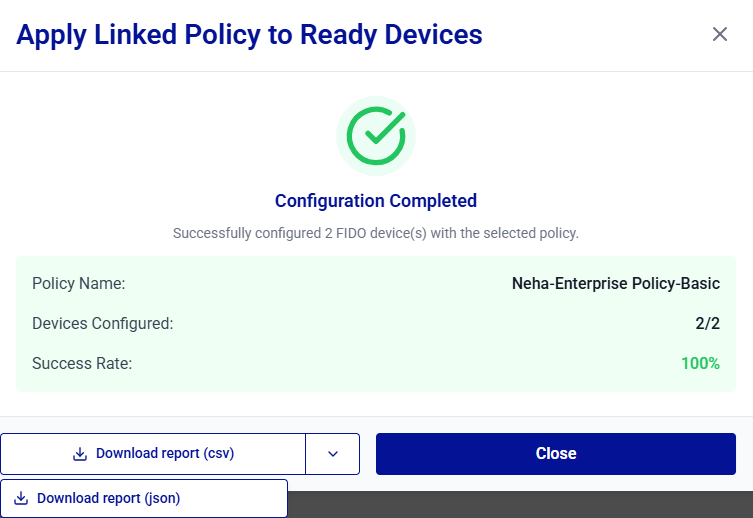
You can export the configuration logs by clicking the Download report button to save a report (CSV or JSON) of the configuration session.
Assign FIDO Devices to Users
Once FIDO devices are configured, administrators can assign them to users for authentication, either individually or in bulk:
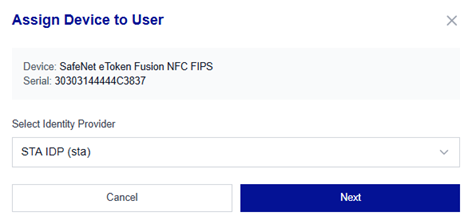
Assign a FIDO Device to a User
-
Under Connected FIDO Devices, search for and locate the device to be assigned to a user, and click Assign.
-
On the Assign Device to User window, in the Select Identity Provider field, select an identity provider, and click Next.
-
Search for the user to whom a device needs to be assigned, select the user, and click Next.
Note
Use the following criteria to search for users across supported identity providers:
Identity Provider Search Users By Partial Search (minimum 3 characters required) Microsoft Entra ID User Principal Name (UPN) or Email address Supported Okta Person name or Username Supported SafeNet Trusted Access Complete User ID Not supported (exact match required) Ping Identity Username Supported 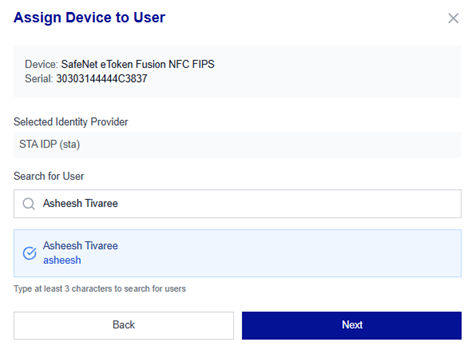
-
Review the device assignment details and click Assign Device.
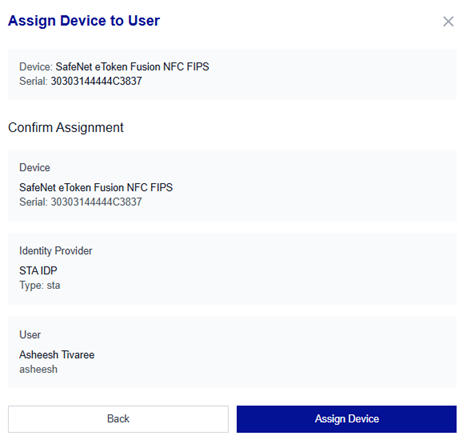
You can enable the Send email notification toggle to notify users upon successful enrollment of their device(s).
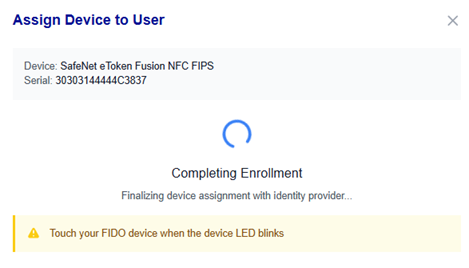
-
The Assign Device to User window is opened to verify the administrator’s presence. Touch the device when prompted (most devices blink).
-
After the device enrollment is complete, the Enrollment Successful message is displayed. Click Done.
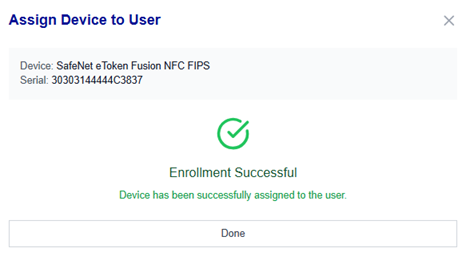
You can export the enrollment logs by clicking the Download report button to save a report (CSV or JSON) of the enrollment session.
Tip
You can verify the device status by clicking the Refresh Devices button on the Connected FIDO Device window or by navigating to the Device Inventory window.
Assign FIDO Devices to Multiple Users
You can assign devices to multiple users in a single operation. During this operation, connected devices in the Ready, Configured, or Revoked state are assigned sequentially to the selected users.
The following conditions apply for this operation:
- Only devices in the Ready, Configured, or Revoked state can be assigned.
- Up to 10 users per operation can be selected.
- The number of users cannot exceed the number of connected devices.
Perform the following steps to assign FIDO devices to multiple users:
-
Under Connected FIDO Devices, next to the Configure multiple devices button, click the three-dots
 icon, and then select Assign Devices to Multiple Users.
icon, and then select Assign Devices to Multiple Users.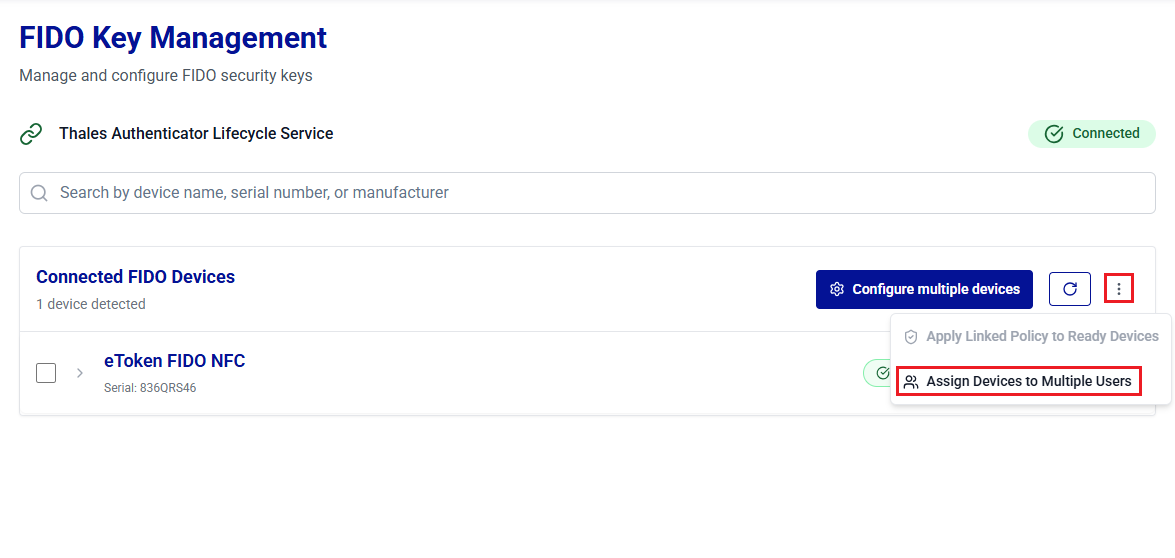
-
On the Assign Devices to Multiple Users window, the Device Assignment Information banner displays the number of available devices and the corresponding maximum number of users that can be selected.
Under Select Identity Provider, select the identity provider associated with users to whom devices will be assigned.
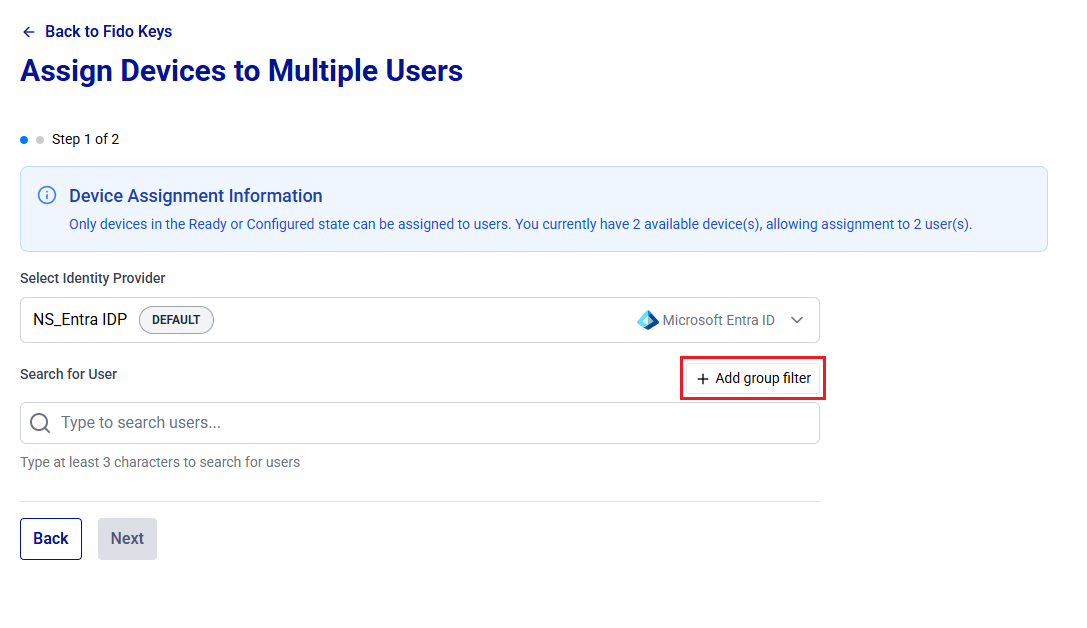
-
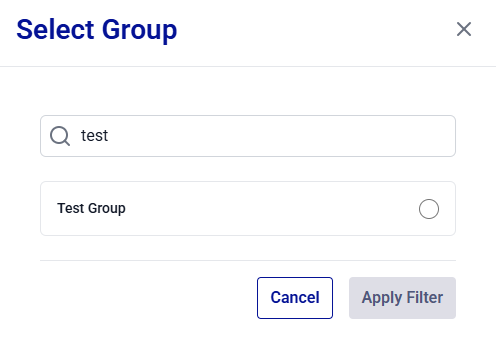
(Optional) To narrow the user search to a specific group, click Add group filter. In the Select Group dialog, search for and select the target group, and then click Apply Filter.
Note
Enter at least three characters to search for groups. For the STA identity provider, only exact matches are supported, and you must enter the complete group name.
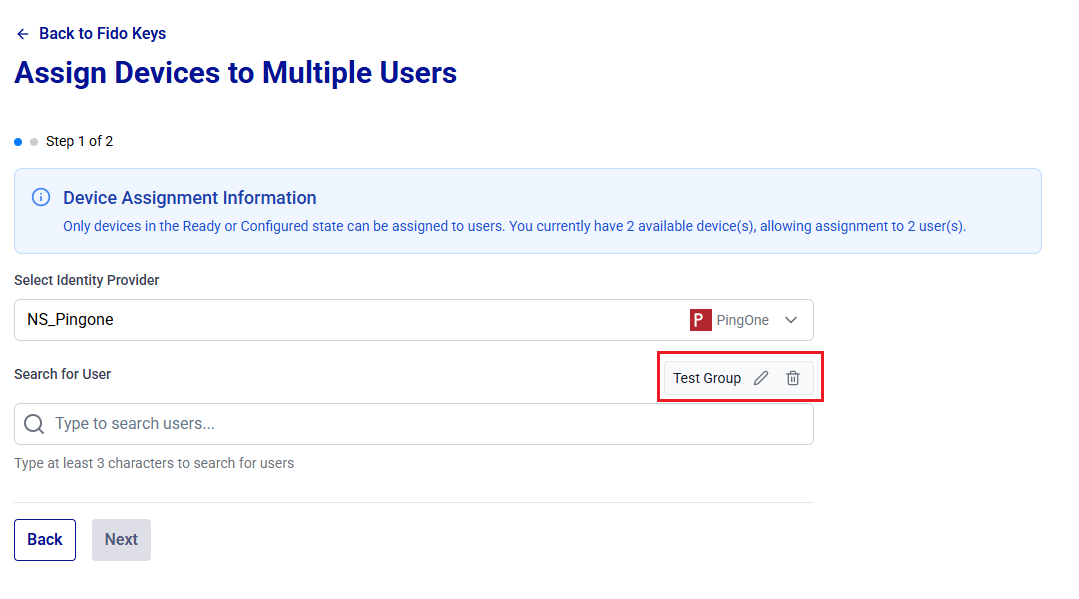
The selected group is displayed next to the Search for User label. You can use the Edit or Delete icon to change or remove the group filter.
-
Search for the users (filtered by the group, if applied) to whom a device needs to be assigned. Matching users are listed below the search box.
Note
Use the following criteria to search for users across supported identity providers:
Identity Provider Search Users By Partial Search (minimum 3 characters required) Microsoft Entra ID User Principal Name (UPN) or Email address Supported Okta Person name or Username Supported SafeNet Trusted Access Complete User ID Not supported (exact match required) Ping Identity Username Supported 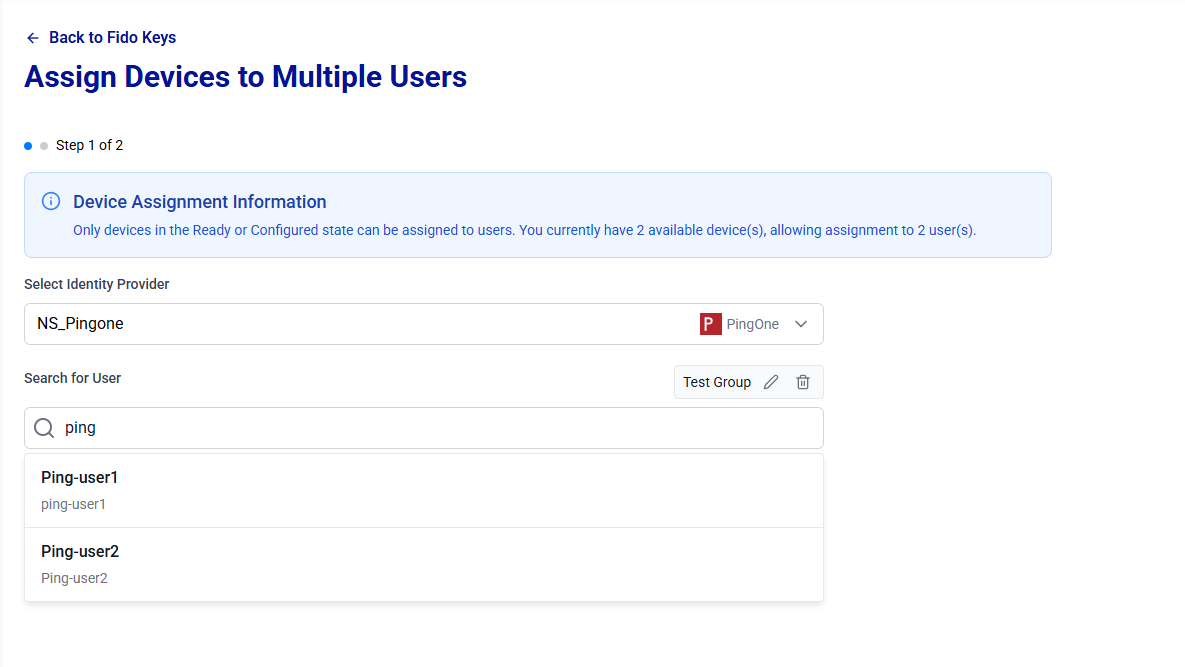
-
Select users to assign devices. To deselect a user, click the deselect icon
 next to the user.
next to the user. 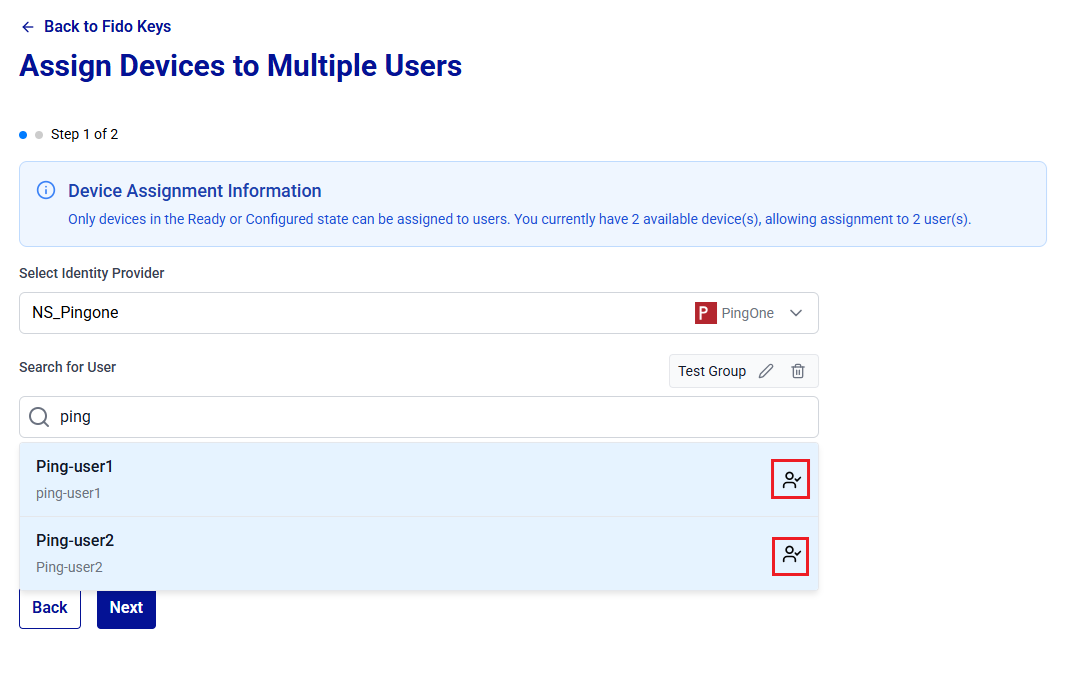
Under Selected Users, user selection count (for example, 2/10) is displayed with the list of selected users. To deselect a user, click
 for the respective user.
for the respective user.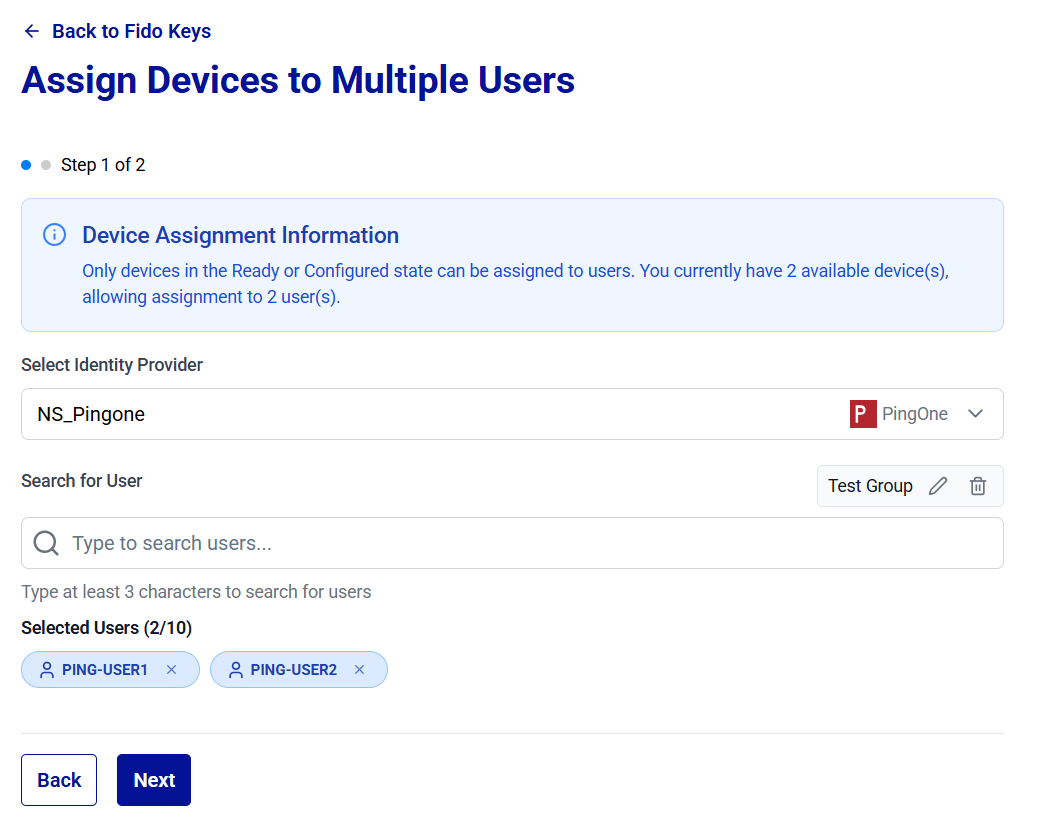
-
Click Next.
-
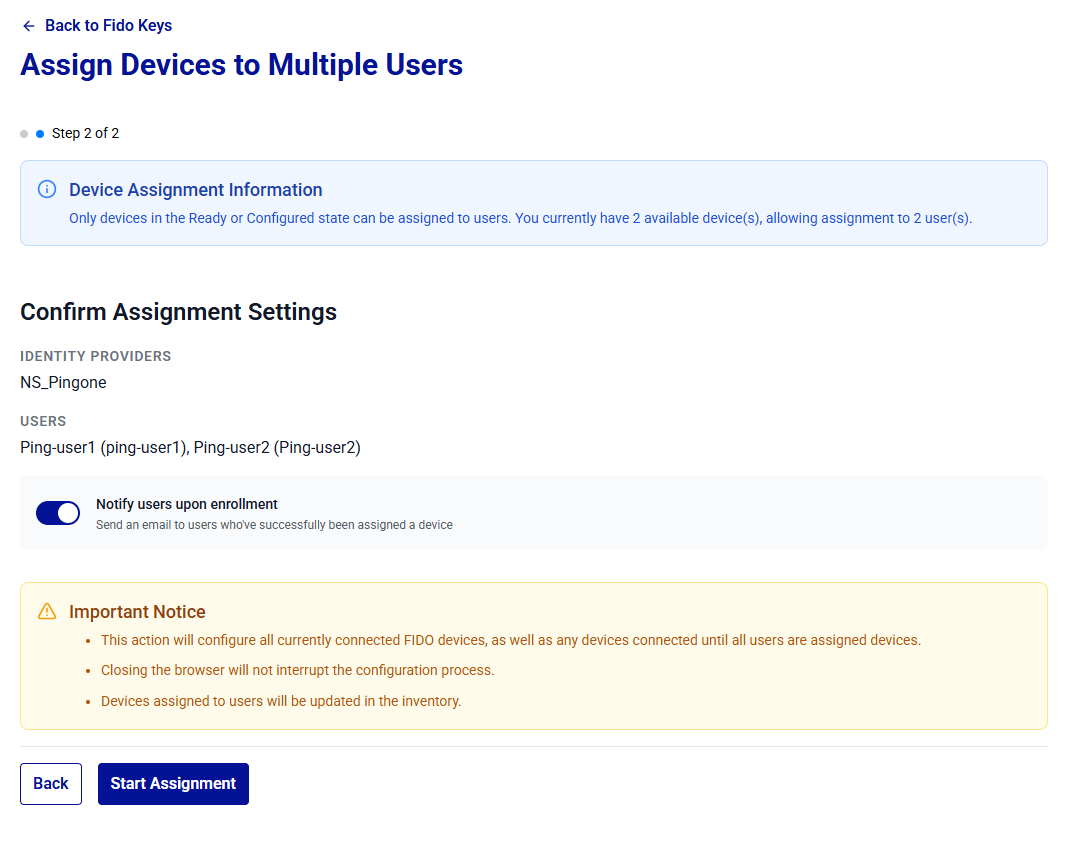
Under Confirm Assignment Settings, review the assignment settings, and click Start Assignment. You can enable the Notify users upon enrollment toggle to notify users when their device is successfully assigned.
Each connected device is enrolled sequentially. When prompted, touch the device to assign it to the next user.
Warning
Removing a device during assignment may result in an inconsistent device state.
-
After the operation completes, the Assignment Completed message is displayed with the Devices Enrolled, Failed Devices, and Success Rate statistics. Click Close.
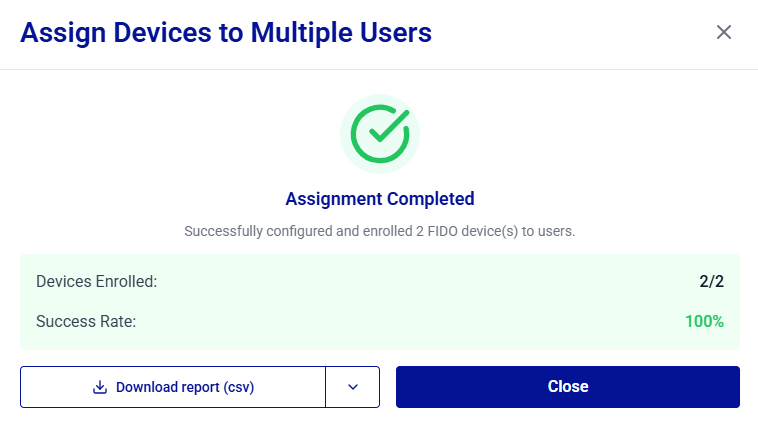
You can export the enrollment logs by clicking the Download report button to save a report (CSV or JSON) of the assignment session.
After you click Close, the assigned devices appear with the Enrolled status under Connected FIDO Devices, and the assignments are reflected in the Device Inventory.
View Initial PIN
Administrators can view a device user PIN and Admin PIN for administrative verification.
Caution
Use this option only in secure environments to prevent unauthorized PIN exposure.
Permission-based visibility
The ability to view PIN values depends on the following permissions assigned to the administrator:
talm_device_userpin_read– Allows viewing the User PIN.talm_device_adminpin_read– Allows viewing the Admin PIN (applicable to enterprise devices that support administrator mode).
PIN Visibility by Permission and Device Type
User PIN Permission talm_device_userpin_read |
Admin PIN Permission talm_device_adminpin_read |
Standard device | Enterprise device |
|---|---|---|---|
| Enabled | Enabled | User PIN | User PIN and Admin PIN |
| Disabled | Enabled | No Initial PIN option | Admin PIN |
| Enabled | Disabled | User PIN | User PIN |
| Disabled | Disabled | No Initial PIN option | No Initial PIN option |
Perform the following steps to view a device user PIN and/or Admin PIN:
-
Under Connected FIDO Devices, search for and locate the device for which you want to view the PIN, click the three-dots
 icon for the device, and then select Initial PIN.
icon for the device, and then select Initial PIN.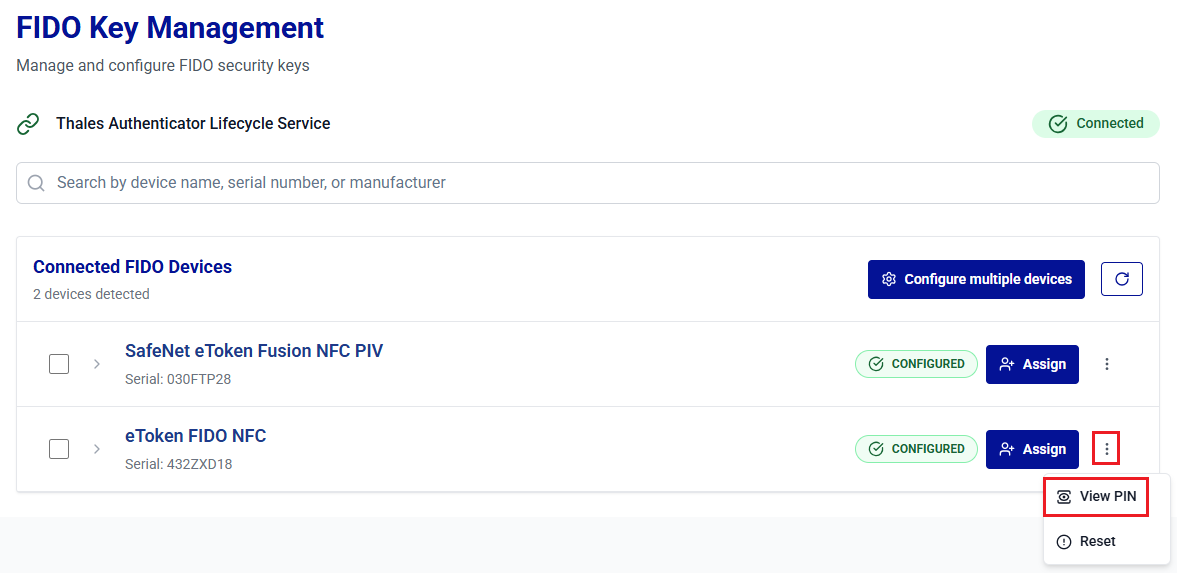
-
On the Device PIN window, click on the Show Password
 icon to view a device user PIN and Admin PIN.
icon to view a device user PIN and Admin PIN.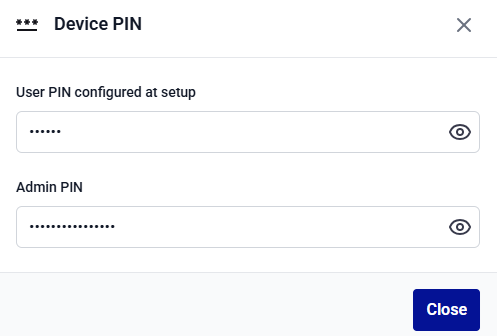
-
Click Close to close the window.
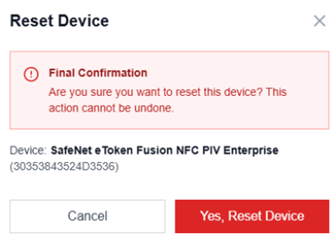
Reset FIDO Devices
The Reset device operation restores a FIDO device to its default state. A reset operation deletes all configurations, including the user PIN.
Caution
Resetting a device is an irreversible operation that permanently deletes all previously enrolled credentials. Ensure that alternative access mechanisms are in place before initiating this operation.
-
Under Connected FIDO Devices, search for and locate the device to be reset, click the three-dots
 icon for the device, and select Reset.
icon for the device, and select Reset.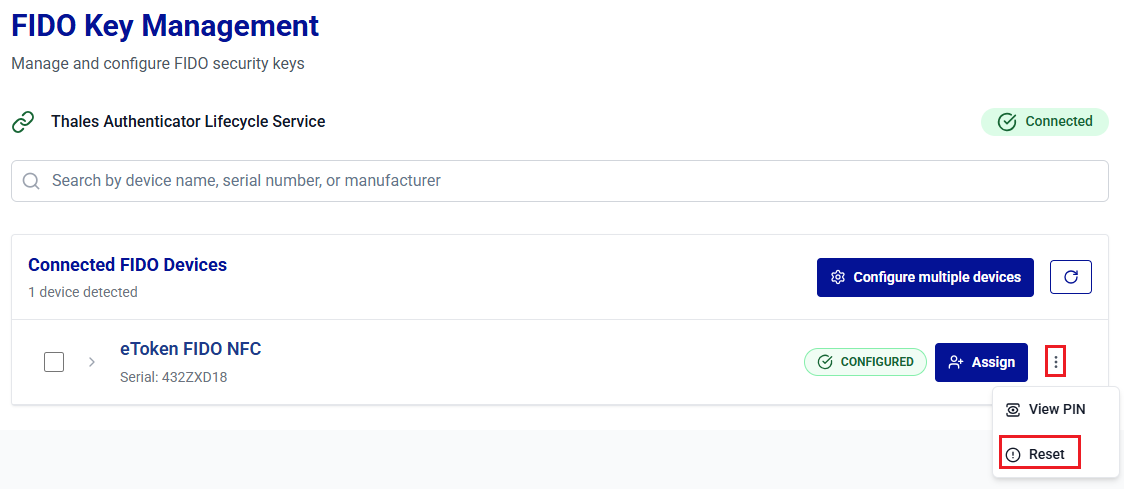
-
On the Reset Device window, click Yes, Reset Device to confirm the operation.
-
The next steps vary depending on whether the device is managed (admin-supported) or unmanaged (self-managed devices).
-
The Reset Device window appears. For managed devices, enter the Admin PIN when prompted, click Continue, and then proceed with the steps given below for unmanaged devices.
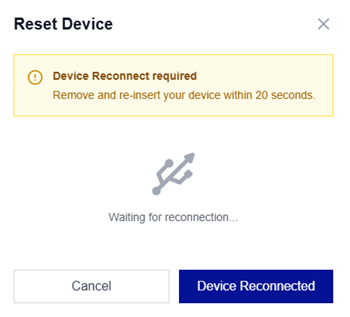
-
For unmanaged devices,
-
Remove the device, reinsert the device, and click Device Reconnected.
-
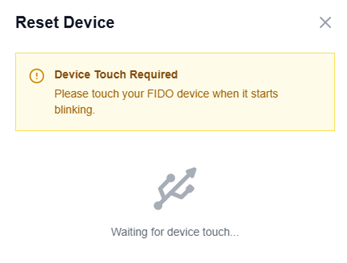
Touch the device when prompted to initiate the reset operation (most devices blink). Wait for the reset operation to complete.
-
-
-
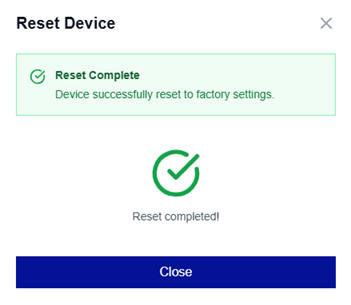
On successful device reset, the Reset Complete message is displayed. Click Close.
Unlock Devices
A FIDO device is locked after repeated incorrect PIN attempts. When the device is locked, the user cannot authenticate until it is successfully unlocked. Thales Authenticator Lifecycle Manager provides two secure options to unlock a device:
- Physical Unlock (Admin Mode): The administrator has physical access to the device and performs the unlock operation directly in Thales Authenticator Lifecycle Manager.
- Remote Unlock (Challenge–Response Method): The locked device stays with the end user, while the administrator assists remotely using Thales Authenticator Lifecycle Manager. This operation can be performed under Device Inventory.
Physical Unlock
The physical unlock option is used when the administrator has direct access to the locked FIDO device. This method does not require interaction with the end user during the unlock process and is performed entirely within Thales Authenticator Lifecycle Manager.
Before starting the physical unlock process, ensure to complete the following prerequisites:
- An administrator account or admin role is required to perform the operation.
- The locked FIDO device is physically available and can be connected to the administrator’s workstation.
Perform the following steps to unlock the FIDO device:
-
Log in to Thales Authenticator Lifecycle Manager as an administrator, go to the FIDO Keys menu, and connect the locked FIDO device to the administrator workstation.
-
The locked device is listed under Connected FIDO Devices. Click the three-dots
 icon for the device and select Unlock.
icon for the device and select Unlock.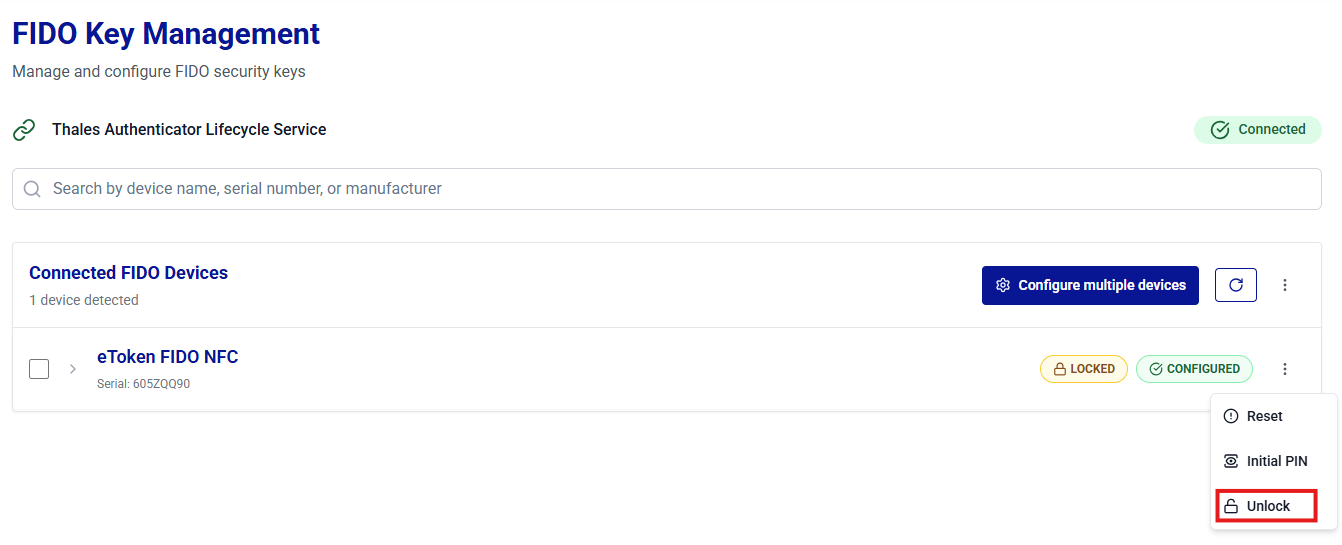
-
Under Unlock device, select one of the following options to generate a new PIN:
-
Use random PIN: Thales Authenticator Lifecycle Manager generates a new PIN automatically for the device.
-
Choose PIN: Manually set a new PIN for the device.
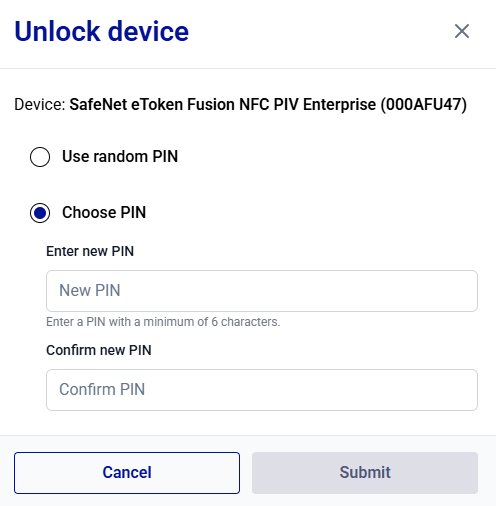
-
-
Click Submit to complete the operation.
After the device is successfully unlocked, the success message is displayed.
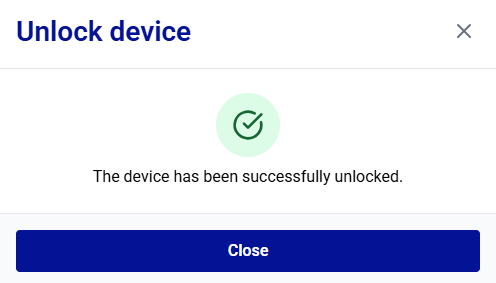
-
Click Close.
Revoke Devices
The Revoke operation permanently disables a device for authentication. Use Revoke when a device is lost, stolen, compromised, or no longer authorized. Revocation changes the device status to Revoked and prevents the device from being used for future authentication.
In addition to the Device Inventory, administrators can also revoke a device directly from the FIDO Key Management window without leaving the connected-devices view.
Warning
Revocation is a permanent action. Once a device is revoked, it is permanently disabled and cannot be used for authentication again. To reuse the device, it must be re-enrolled for a user.
Perform the following steps to revoke a device from the FIDO Key Management window:
-
Under Connected FIDO Devices, search for and locate the target device. Click the three-dots
 icon for the device, and then select Revoke.
icon for the device, and then select Revoke.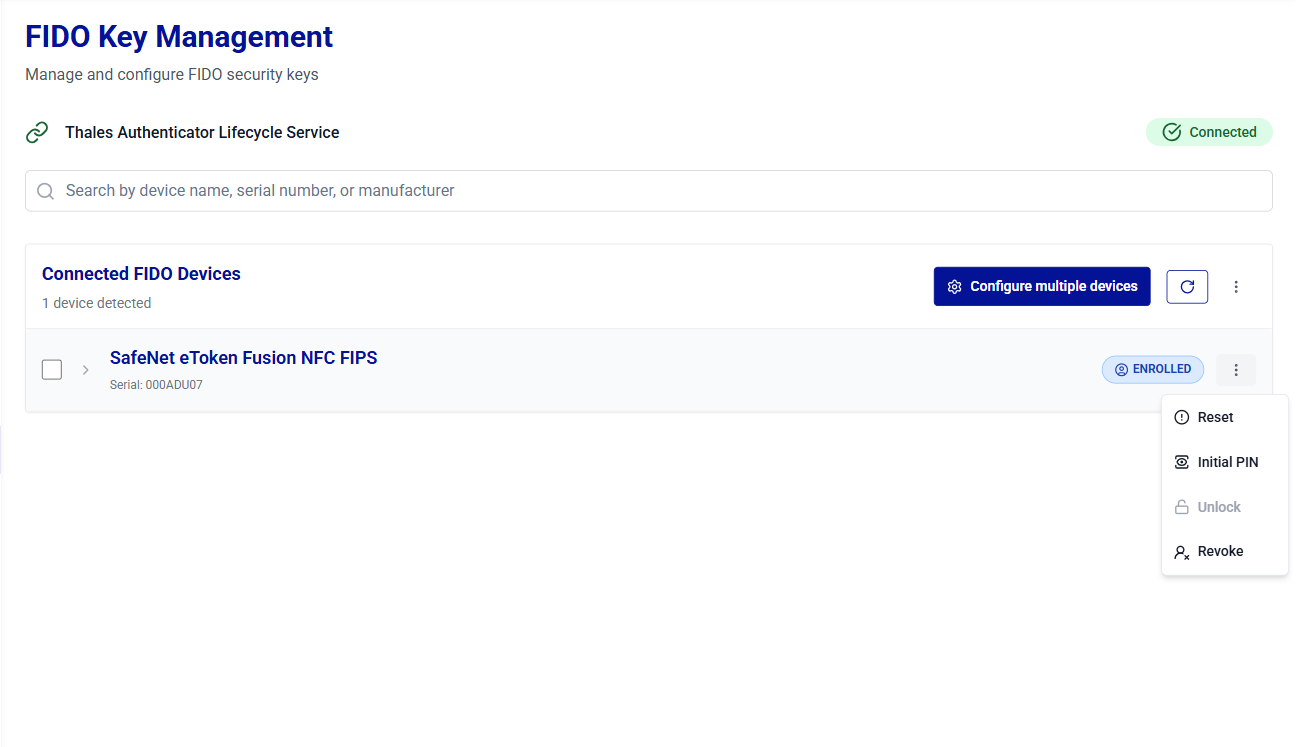
-
The Revoke Device window is displayed, showing the device name and the assigned user. Click Revoke to confirm the operation.
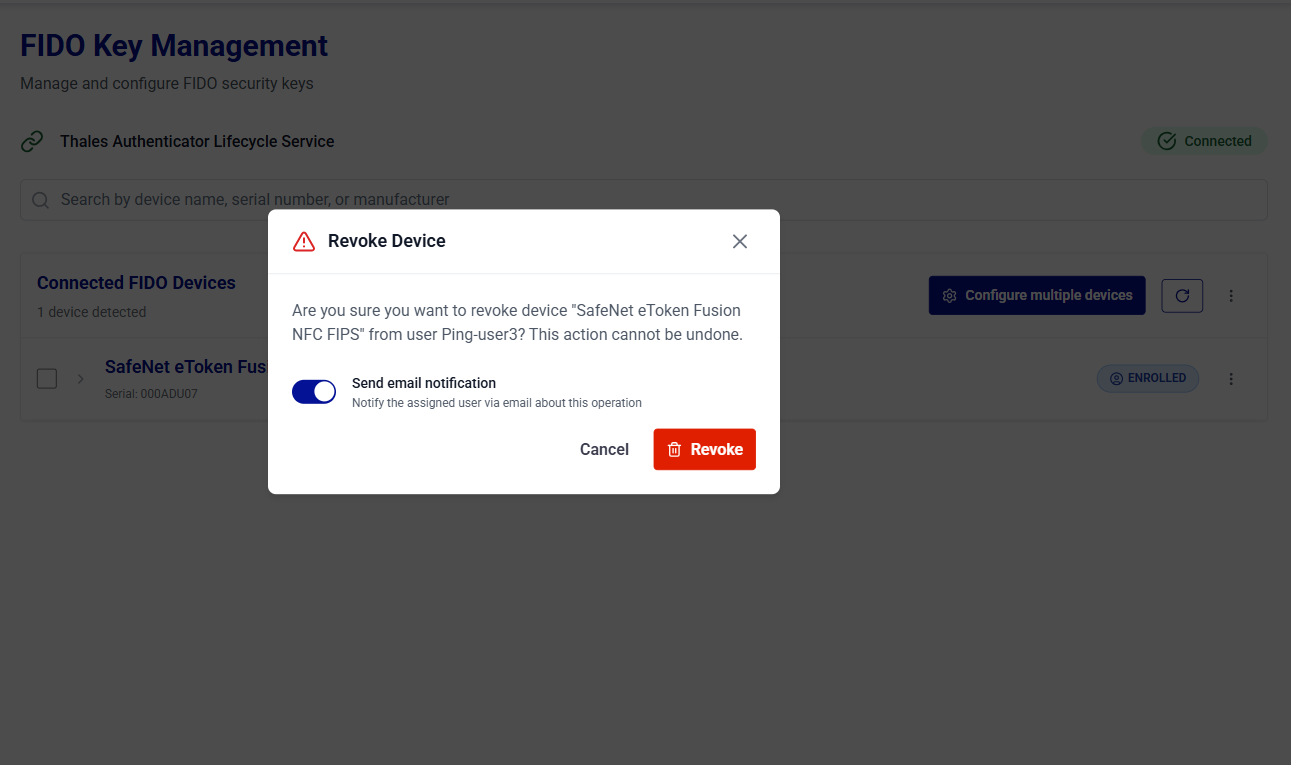
You can enable the Send email notification toggle to notify the assigned user about the revocation.
-
After the device is successfully revoked, the device status under Connected FIDO Devices is updated to Revoked.