Modifying Policies and Rules
On the Policies page, you can view details of policies, update their description, and delete that policies that are no longer needed. Additionally, you can modify the key and security rules linked to the policy.
Note
Any updates to a policy will be applied without confirmation if the policy is not in use by any Enabled/Active GuardPoints.
Displaying Policies
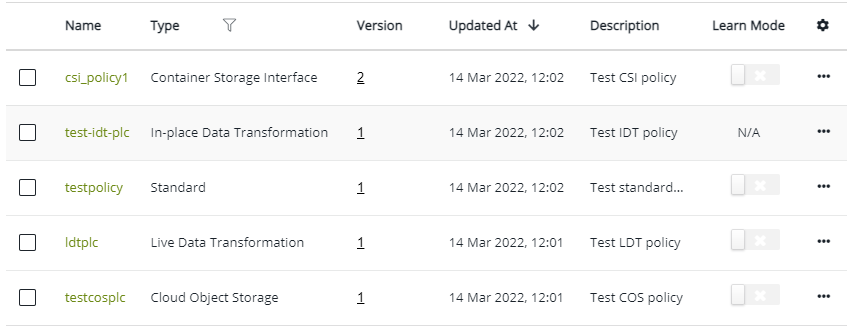
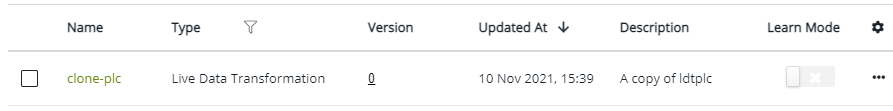
The Policies page shows the list of configured policies with their details such as names, types, and versions. You can view the version history of policies from the Policies page. Additionally, you can delete policies from this page. In the detail view, you can view types of rules linked with the policies.
Additionally, the Policies page shows a warning banner at the top with the number of policies that have Learn Mode enabled for more than 3 days.
This section covers the following information:
Viewing Policies
To view the complete list of configured policies:
Open the Transparent Encryption application.
Click Policies. The Policies page shows the following details:
Column Description Name Unique name of the policy. Type Type of the policy can be:
• Standard
• Live Data Transformation
• Cloud Object Storage
• In-place Data Transformation
• Container Storage InterfaceVersion Version of the policy. Click to view the version history of the policy. Refer to Viewing Policy Version History for details. Updated At Time when the policy is created or updated. Description Optional description of the policy. Learn Mode Whether the Lean Mode is turned on for the policy. Use the toggle to turn on/off Lean Mode for the policy. Turn off Learn Mode for the policy for which you have analyzed the valid processes and users. Restrict Update Whether the updates to the policy are restricted. Use the toggle to restrict or allow updates to the policy. Turning on the toggle restricts updates to the policy, which can be useful when the policy is in use by GuardPoints. However, turning off the toggle allows updates to the policy. Refer to Controlling Updates to Policies.
The Restrict Update column is hidden by default. To show/hide a column, click the custom view icon ( ), select/clear the desired column, and click OK.
), select/clear the desired column, and click OK.
By default, the policies are displayed in descending order by Updated At. By default, 10 records per page are displayed. Adjust pagination and/or the number of records to display per page to view more records.
To add a new policy, click Create Policy. Refer to Creating Policies for details.
Viewing Details of Policies
The detail view of a policy shows the security rules, key rules, and data transformation rules, as appropriate. The Restrict Update and Learn Mode toggles are also provided. Use these toggles to turn on or off learn mode and updates to the policy.
To view the details of a policy:
Open the Transparent Encryption application.
Click Policies. The list of configured policies is displayed.
Under Name, click the desired policy. The edit view of the policy is displayed. The rules linked with the policy are displayed on the following tabs:
Security Rules
Key Rules
Data Transformation Rules (Applicable to Standard policies that contain data transformation rules)
Note
If a policy is in Learn Mode, a warning banner stating the following is displayed at the top of the page:
Warning: This Policy is in Learn Mode
To disable Learn Mode, turn off the Learn Mode toggle on the right.If the Restrict Update toggle is turned on, updates to a policy that is in use by active GuardPoints are restricted. Security rules and key rules linked with the policy cannot be changed.
Click the Security Rules tab. This tab displays the following details:
Column Description Order Sequence to enforce security rules. Rules higher in the order take higher priority. Click to edit the rule. Resource Set (Not applicable to Cloud Object Storage and Container Storage Interface policies) Resource set linked with the rule.
To modify an existing resource set, click the desired set link, modify the Description, and click Apply. The edit view also provides the Add Resource button to add new resources to the set.User Set User set linked with the rule.
To modify an existing user set, click the desired user set link, modify the Description, and click Apply. The edit view also provides the Browse users and Manually add user buttons to add new users to the set.Process Set Process set linked with the rule.
To modify an existing process set, click the desired process set link, modify the Description, and click Apply. The edit view also provides the Add Process button to add new processes to the set.Action Action applied to the rule. Refer to Actions for the complete list of supported actions. Effect Effect applied to the rule. Browsing Whether browsing of directories under the GuardPoint down to the resources in the rule is allowed. For Cloud Object Storage policies, No is displayed. To add a new security rule, refer to Step 2: Add Security Rules for details.
Click the Key Rules tab. This tab displays the following details:
Standard Policies
Column Description Order Sequence to enforce key rules. Rules higher in the order take higher priority. Click to edit the rule. Resource Set Resource set linked with the key rule.
To modify an existing resource set, click the desired set link, modify the Description, and click Apply. The edit view also provides the Add Resource button to add new resources to the set.Key Name / Current Key Name Encryption key currently applied to the resource. For Data Transformation policies, the name is Current Key Name. Live Data Transformation Policies
Column Description Order Sequence to enforce key rules. Rules higher in the order take higher priority. Click to edit the rule. Resource Set Resource set linked with the key rule.
To modify an existing resource set, click the desired set link, modify the Description, and click Apply. The edit view also provides the Add Resource button to add new resources to the set.Current Key Name Encryption key currently applied to the resource. Transformation Key Name Encryption key to perform data transformation for LDT policies. Exclusion Rule Whether to exclude the resource set from the policy. Cloud Object Storage Policies
Column Description Key Name Name of the key. In-place Data Transformation Policies
Column Description Current Key Name of the current encryption key. Transformation Key Encryption key to perform data transformation for IDT policies. To add a new key rule, refer to Step 3: Add Key Rules for details.
Container Storage Interface Policies
Column Description Order Sequence to enforce key rules. Rules higher in the order take higher priority. Click to edit the rule. Key Name Encryption key currently applied to the resource. Click the Data Transformation Rules tab. This tab is displayed if the policy contains data transformation rules. This tab displays the following details:
Column Description Order Sequence to enforce key rules. Rules higher in the order take higher priority. Click to edit the rule. Resource Set Resource linked with the key rule.
To modify an existing resource set, click the desired set link, modify the Description, and click Apply. The edit view also provides the Add Resource button to add new resources to the set.Transformation Key Name Transformation key to use for rekeying. To add a new data transformation rule, refer to Step 4: Add Data Transformation Rules for details.
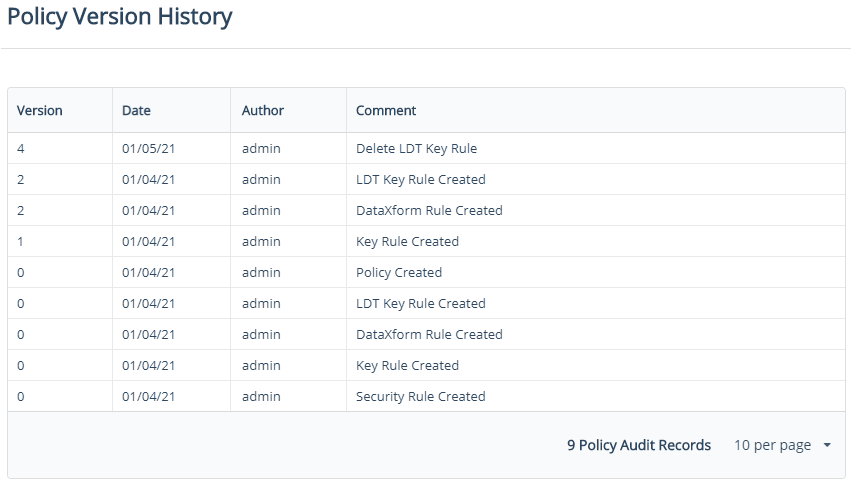
Viewing Policy Version History
The policy version defines the number of times a policy has been changed. This number indicates the current revision only. It cannot be used to roll back to a previous version. Restore a backup to revert to a previous online policy version. The version count starts at zero when the policy is initially created and increments by one each time it is saved thereafter.
To view the version history of a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the version number of the policy. The Policy Version History popup displays the following details:
Field Description Version Version of the policy. Date Date when the version is created. Author User who changed the policy. Comment Description of change. Click OK.
Controlling Updates to Policies
CTE provides options to restrict or allow changes to a policy that is in use by active GuardPoints. When updates are restricted, security rules and key rules linked with the policy cannot be changed.
To restrict or allow changes to a policy:
Open the Transparent Encryption application.
Click Policies. The list of configured policies is displayed.
Under Name, click the desired policy. The edit view of the policy is displayed.
Turn on/off the Restrict Update toggle.
Turning on the toggle restricts updates to the policy. Any attempts to change the policy will result in an error. Turning off the Restrict Update toggle allows updates to the policy.
Updating Policy Description
To update the description of a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the overflow icon (
 ) corresponding to the desired policy.
) corresponding to the desired policy.Click Edit.
Add or modify the Description. The policy Name and Type cannot be modified.
Click Update.
The updated description appears in the policies list.
Cloning a Policy
Cloning is an efficient and simple method to create a copy of an existing policy. The clone is a separate policy and contains all the configurations of its parent policy. When cloning a policy, specify a new unique name for the clone. Also, enable or disable Learn Mode and Restrict Update for the clone, if required.
To duplicate a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the overflow icon (
 ) corresponding to the desired policy.
) corresponding to the desired policy.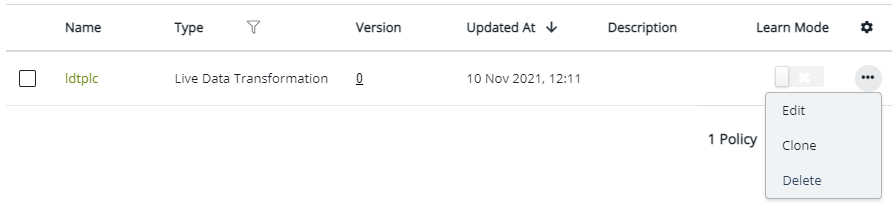
Click Clone.
Enter a unique Name for the clone.
(Optional) Provide a Description for the clone.
(Optional) Turn on/off the Learn Mode toggle. Refer to Learn Mode for details.
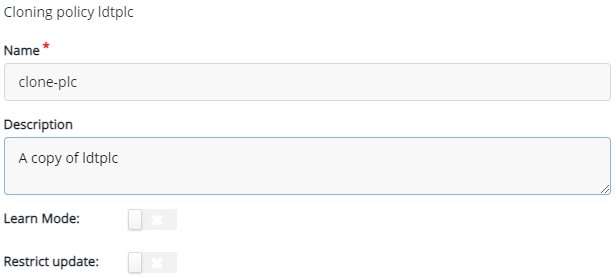
(Optional) Turn on/off the Restrict Update toggle. Refer to Controlling Updates to Policies for details.
The clone with the specified name appears at the top of the policies list.
Adding New Security Rules
To add a new security rule to a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
On the Security Rules tab, click Add Security Rule. The Add Security Rule dialog box is displayed.
Specify the required details. The fields on the Add Security Rule dialog box are same as the fields on the Create Security Rule dialog box. Refer to Step 2: Add Security Rules for details.
Click Add.
The newly added security rule appears in the security rules list. Similarly, you can add more security rules to the policy.
Adding New Key Rules
To add a new key rule to a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
Click the Key Rules tab.
Click Add Key Rule.
An IDT policy can have only one key rule. So, the Add Key Rule button is not available for IDT key rules.
Specify the required details. The fields on the Add Key Rule dialog box are same as the fields on the Create Key Rule dialog box. Refer to Step 3: Add Key Rules for details.
Click Add.
The newly added key rule appears in the key rules list. Similarly, you can add more key rules to the policy.
Adding New Data Transformation Rules
This section is applicable to policies that contain data transformation rules.
To add a new data transformation rule to a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
Click the Data Transformation Rules tab.
Click Add Data Transformation Rule. The Add Data Transformation Rule dialog box is displayed.
Specify the required details. The fields on the Add Data Transformation Rule dialog box are same as the fields on the Create Data Transformation Rule dialog box. Refer to Step 4: Add Data Transformation Rules for details.
Click Add.
The newly added data transformation rule appears in the data transformation rules list. Similarly, you can add more rules to the policy.
Modifying Security Rules
Editing Security Rules
To edit a security rule in a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
Click the Security Rules tab.
Click the overflow icon (
 ) corresponding to the desired rule.
) corresponding to the desired rule.Click Edit. The Edit Security Rule dialog box is displayed.
Change the required fields. The fields on the Edit Security Rule dialog box are the same the fields on the Create Security Rule dialog box. Refer to Step 2: Add Security Rules for details.
Click Update.
The updated details appear in the security rules list.
Changing Order of Security Rules
To change the order of a security key rule in a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
Click the Security Rules tab.
Select the desired rule. Depending on the current order, the following ordering icons are activated.
Icon Description Bottom (  )
)Move the rule to the bottom. Unavailable for the rule at the bottom. Down (  )
)Move the rule one place lower. Unavailable for the rule at the bottom. Up (  )
)Move the rule one place higher. Unavailable for the rule at the top. Top (  )
)Move the rule to the top. Unavailable for the rule at the top. Click the desired icon.
The rules list shows the updated order.
Deleting Security Rules
To delete security rules from a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
Click the Security Rules tab.
Select the check boxes corresponding to the desired rules.
To select all rules visible on the page for deletion, select the top check box to the left of the Order heading.
Click the delete icon (
 ).
).
The selected rules are removed from the security rules list.
Modifying Key Rules
Modifying key rules linked with a policy involves:
Editing Key Rules
To edit a key rule in a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
Click the Key Rules tab.
Click the overflow icon (
 ) corresponding to the desired rule.
) corresponding to the desired rule.Click Edit. The Edit Key Rule dialog box is displayed.
Change the required fields. The fields on the Edit Key Rule dialog box are the same the fields on the Create Key Rule dialog box. Refer to Step 3: Add Key Rules for details.
Click Update.
The updated details appear in the key rules list.
Changing Order of Key Rules
To change the order of a key rule in a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
Click the Key Rules tab.
Select the desired rule. Depending on the current order, the following ordering icons are activated.
Icon Description Bottom (  )
)Move the rule to the bottom. Unavailable for the rule at the bottom. Down (  )
)Move the rule one place lower. Unavailable for the rule at the bottom. Up (  )
)Move the rule one place higher. Unavailable for the rule at the top. Top (  )
)Move the rule to the top. Unavailable for the rule at the top. Click the desired icon.
The key rules list shows the updated order.
Deleting Key Rules
To delete key rules from a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
Note
The key rule linked with an IDT policy cannot be deleted from the CipherTrust Manager. However, you can update the key rule when required (refer to Editing Key Rules).
Click the Key Rules tab.
Select the check boxes corresponding to the desired rules.
To select all rules visible on the page for deletion, select the top check box to the left of the Order heading.
Click the delete icon (
 ).
).
The selected rules are removed from the key rules list.
Modifying Data Transformation Rules
Modifying data transformation rules linked with a policy involves:
Editing Data Transformation Rules
To edit a data transformation rule in a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
Click the Data Transformation Rules tab.
Click the overflow icon (
 ) corresponding to the desired rule.
) corresponding to the desired rule.Click Edit. The Edit Data Transformation Rule dialog box is displayed.
Change the required fields. The fields on the Edit Data Transformation Rule dialog box are the same the fields on the Create Data Transformation Rule dialog box. Refer to Step 4: Add Data Transformation Rules for details.
Click Update.
The updated details appear in the data transformation rules list.
Changing Order of Data Transformation Rules
To change the order of a data transformation rule in a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
Click the Data Transformation Rules tab.
Select the desired rule. Depending on the current order, the following ordering icons are activated.
Icon Description Bottom (  )
)Move the rule to the bottom. Unavailable for the rule at the bottom. Down (  )
)Move the rule one place lower. Unavailable for the rule at the bottom. Up (  )
)Move the rule one place higher. Unavailable for the rule at the top. Top (  )
)Move the rule to the top. Unavailable for the rule at the top. Click the desired icon.
The rules list shows the updated order.
Deleting Data Transformation Rules
To delete data transformation rules from a policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the desired policy.
Click the Data Transformation Rules tab.
Select the check boxes corresponding to the desired rules.
To select all rules visible on the page for deletion, select the top check box to the left of the Order heading.
Click the delete icon (
 ).
).
The selected rules are removed from the data transformation rules list.
Deleting Policies
CipherTrust Manager provides options to delete single or multiple policies.
Deleting Single Policies
To delete a single policy:
Open the Transparent Encryption application.
In the left pane, click Policies.
Click the overflow icon (
 ) corresponding to the desired policy.
) corresponding to the desired policy.Click Delete.
The selected policy is removed from the policies list.
Deleting Multiple Policies
To delete single or multiple policies:
Open the Transparent Encryption application.
In the left pane, click Policies.
Select the check boxes corresponding to the desired policies.
To select all policies visible on the page for deletion, select the top check box corresponding to the left of the Name heading.
Click the delete icon (
 ).
).
The selected policies are removed from the policies list.
Exporting Policies
CipherTrust Manager provides options to back up CTE policies and restore them to other CipherTrust Manager appliances. Refer to Backup and Restore for details.

