Creating GuardPoints for Efficient Storage Devices
CTE-Efficient Storage
Storage arrays offer features such as compression and deduplication for storage efficiency. They also provide simplistic encryption that fails to deliver the requisite levels of security. CTE offers a much higher level of security. However, in deployments where storage arrays receive encrypted data streams from the clients protected by a CTE instance (protected clients), the encrypted data streams make the efficiency of storage array systems ineffective. This is because every block written by CTE is different resulting in zero deduplication and compression on these blocks.
CTE offers CTE-Efficient Storage as the solution to the storage efficiency challenge in storage arrays. CTE supports Standard and IDT policies for CTE-Efficient Storage devices. GuardPoints applied to the storage arrays are commonly referred to as Efficient Storage GuardPoints (ESG).
Note
ESGs are supported with ESG-enabled CTE clients. KMIP and CTE feature licenses must be activated on the CipherTrust Manager to register ESG clients.
Steps to create GuardPoints on individual clients and client groups are similar. GuardPoints can be created on the GuardPoints tab of individual clients and client groups.
Before proceeding, thoroughly read and understand the information provided in the "CTE-Efficient Storage" section of the CTE Agent Advanced Configuration and Integration Guide specific to your platform for details. This section provides useful information such as requirements and considerations to fulfill and review before protecting CTE-Efficient Storage devices.
Creating Standard GuardPoints for Efficient Storage Devices
Guarding Efficient Storage devices require policies with XTS keys. Standard policies with XTS keys are supported only with Efficient Storage GuardPoints.
To create a standard GuardPoint for storage devices:
Open the Transparent Encryption application.
Select the client or client group on which you want to create a GuardPoint.
Click a client under the Client Name column (Clients > Clients).
Click a client group under the Client Group Name column (Clients > Client Groups).
On the GuardPoints tab, click Create GuardPoint.
Select a Policy. This is a mandatory field.
Click Select next to the Policy field.
Select a Standard policy that uses ESG compatible (XTS) keys. If no policy exists, create one, as described in Creating Policies.
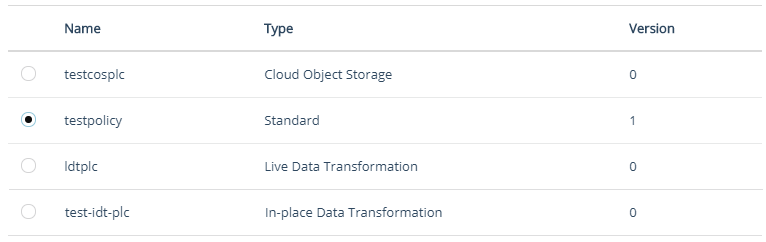
Click Select.
Select the Type of device to protect. This is a mandatory field. Depending on the platform, select from the following options for a Standard policy for Efficient Storage devices:
Type Windows Linux Description Auto Raw or Block Device Yes Yes Select for standard policies for raw (block) devices. Manual Raw or Block Device No Yes Select for standard policies for raw (block) devices to be guarded manually. Note
Manual Raw or Block Device are guarded and unguarded (for example, mounted and unmounted) by running the
secfsd -guardandsecfsd -unguardcommands. Do not run themountandumountcommands to swap GuardPoint nodes in a cluster configuration.Specify the device Path to be protected. This is a mandatory field. Options to specify the GuardPoint paths are:
Enter/Browse Path: Select this option, and enter the GuardPoint paths by either typing or clicking the Browse button.
Note
A maximum of 200 GuardPaths can be specified using the Enter/Browse Path option.
Browse Method (Applicable to Linux Clients)
Click Browse to select a path by browsing the client file system. This method prevents typographical errors and verifies client availability. This is the recommended method to specify individual paths.
File system of a client that is not registered with the CipherTrust Manager cannot be browsed.
In the Search Local Path field, specify a starting path and click Refresh or select from the on-screen file system browser.
Click Add.
Manual Method
Alternatively, on Linux clients, if you know the path, manually enter full paths of one or more directories in the given text box. On Windows clients, enter labels of one or more devices to be protected. Enter one path or label per line.
Upload CSV: Select this option and click Browse to upload the CSV file containing the list of one or more directories. This is the recommended method to specify a large number of paths in one step.
Note
• If a manually entered path does not yet exist, be sure to enter the path correctly. The CipherTrust Manager does not parse manually entered paths for correct syntax.
• See Considerations Before Creating GuardPoints for what to be aware of before creating a GuardPoint.
• If multiple paths are specified, they will all be protected by the same policy.
• A maximum of 1000 GuardPaths per CSV file can be uploaded.Turn on the Efficient Storage toggle.
Note
A GuardPoint can be created for either In-place Data Transformation or Efficient Storage devices, not both.
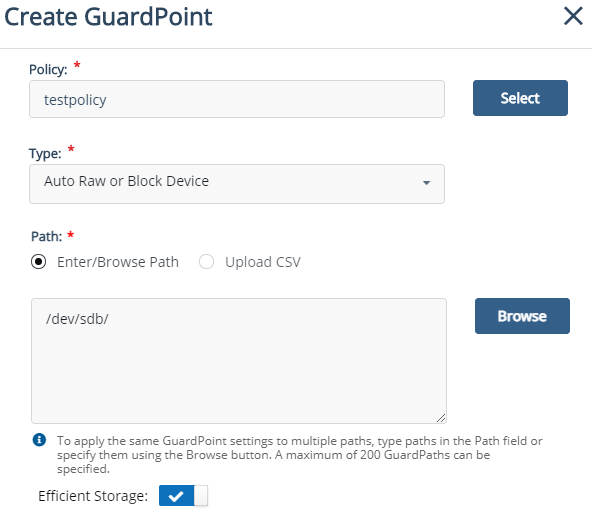
(Optional, Linux only) Select Auto Mount to specify an automount path. For a regular (non-auto) mount path, make sure that the check box is clear.
(Optional, Windows only) Select Secure Start to enable the Secure Start feature. By default, the check box is clear.
If you plan not to enable the Secure Start now, you can do that later, as described in Enabling Secure Start for GuardPoints.
Click Create. A message appears prompting to confirm the reuse of these GuardPoint settings on another path.
Click Yes to use the same settings on another path. The Use Settings on Another Path dialog box is displayed. Perform the following steps:
In the Search Local Path field, specify a starting path and click Refresh or select from the on-screen browser.
Click Add Path. The newly added path appears under the Paths list on the left. Similarly, add as many paths as required.
Click OK.
Click No if you do not want to use the same settings on another path.
Depending on the number of paths you add to a GuardPoint, a status information message may appear. Refer to GuardPoint Status Information for details.
The newly created GuardPoint appears on the GuardPoints tab. The status remains Unknown until the client sends the response after processing the GuardPoint request. Click the Refresh GuardPoints icon ( ) to view the updated status.
) to view the updated status.
Status of a GuardPoint can be checked at any time on the GuardPoints tab. Refer to Viewing GuardPoint Status for details.
Creating IDT GuardPoints for Efficient Storage Devices
Guarding Efficient Storage devices require policies with XTS keys. IDT policies with XTS keys are supported only with Efficient Storage GuardPoints.
To create an IDT GuardPoint for storage devices:
Open the Transparent Encryption application.
Select the client or client group on which you want to create a GuardPoint.
Click a client under the Client Name column (Clients > Clients).
Click a client group under the Client Group Name column (Clients > Client Groups).
On the GuardPoints tab, click Create GuardPoint.
Select a Policy. This is a mandatory field.
Click Select next to the Policy field.
Select a In-place Data Transformation* policy that uses ESG compatible (XTS) keys. If no policy exists, create one, as described in Creating Policies.
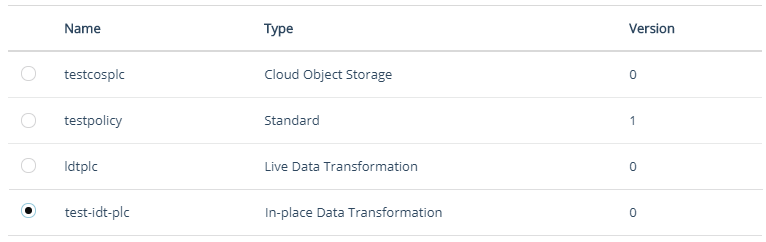
Click Select.
Note
When an IDT policy is selected, the read-only In-place Data Transformation toggle is displayed on the Create GuardPoint dialog box.
Select the Type of device to protect. This is a mandatory field. The options for a In-place Data Transformation policy are:
Type Description Auto Raw or Block Device Select for IDT policies for raw (block) devices. Manual Raw or Block Device Select for IDT policies for raw (block) devices to be guarded manually. Note
Manual Raw or Block Device are guarded and unguarded (for example, mounted and unmounted) by running the
secfsd -guardandsecfsd -unguardcommands. Do not run themountandumountcommands to swap GuardPoint nodes in a cluster configuration.Specify the device Path to be protected. This is a mandatory field. Options to specify the GuardPoint paths are:
Enter/Browse Path: Select this option, and enter the GuardPoint paths by either typing or clicking the Browse button.
Note
A maximum of 200 GuardPaths can be specified using the Enter/Browse Path option.
Browse Method (Applicable to Linux Clients)
Click Browse to select a path by browsing the client file system. This method prevents typographical errors and verifies client availability. This is the recommended method to specify individual paths.
File system of a client that is not registered with the CipherTrust Manager cannot be browsed.
Manual Method
Alternatively, on Linux clients, if you know the path, manually enter full paths of one or more directories in the given text box. On Windows clients, enter labels of one or more devices to be protected. Enter one path or label per line.
Upload CSV: Select this option and click Browse to upload the CSV file containing the list of one or more directories. This is the recommended method to specify a large number of paths in one step.
Note
• If a manually entered path does not yet exist, be sure to enter the path correctly. The CipherTrust Manager does not parse manually entered paths for correct syntax.
• See Considerations Before Creating GuardPoints for what to be aware of before creating a GuardPoint.
• If multiple paths are specified, they will all be protected by the same policy.
• A maximum of 1000 GuardPaths per CSV file can be uploaded.Turn on the Efficient Storage toggle.
Note
A GuardPoint can be created for either In-place Data Transformation or Efficient Storage devices, not both.
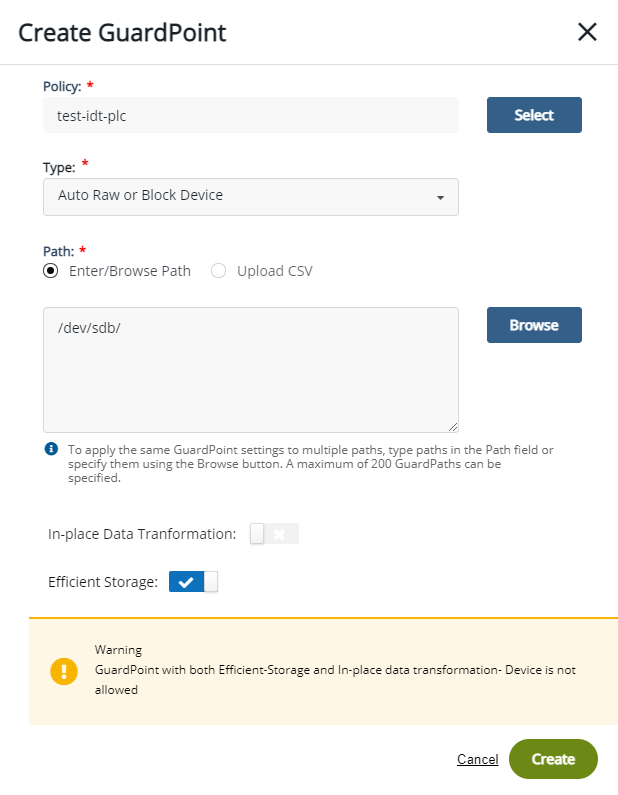
Click Create. A message appears prompting to confirm the reuse of these GuardPoint settings on another path.
Click Yes to use the same settings on another path. The Use Settings on Another Path dialog box is displayed. Perform the following steps:
Specify a new Path.
Click Add Path. The newly added path appears under the Paths list on the left. Similarly, add as many paths as required.
Click OK.
Click No if you do not want to use the same settings on another path.
Depending on the number of paths you add to a GuardPoint, a status information message may appear. Refer to GuardPoint Status Information for details.
The newly created GuardPoint appears on the GuardPoints tab. The status remains Unknown until the client sends the response after processing the GuardPoint request. Click the Refresh GuardPoints icon ( ) to view the updated status.
) to view the updated status.
Status of a GuardPoint can be checked at any time on the GuardPoints tab. Refer to Viewing GuardPoint Status for details.

