Overview
CipherTrust Cloud Key Manager (CCKM, also referred to as CCKM Embedded) centralizes the management of key life cycle for various cloud services providers. The CCKM complies with data security mandates in cloud storage environments while retaining the custodianship of the encryption keys. Enterprises can back up keys on-premise, destroy keys when no longer needed, and manage the entire life cycle of the cloud keys.
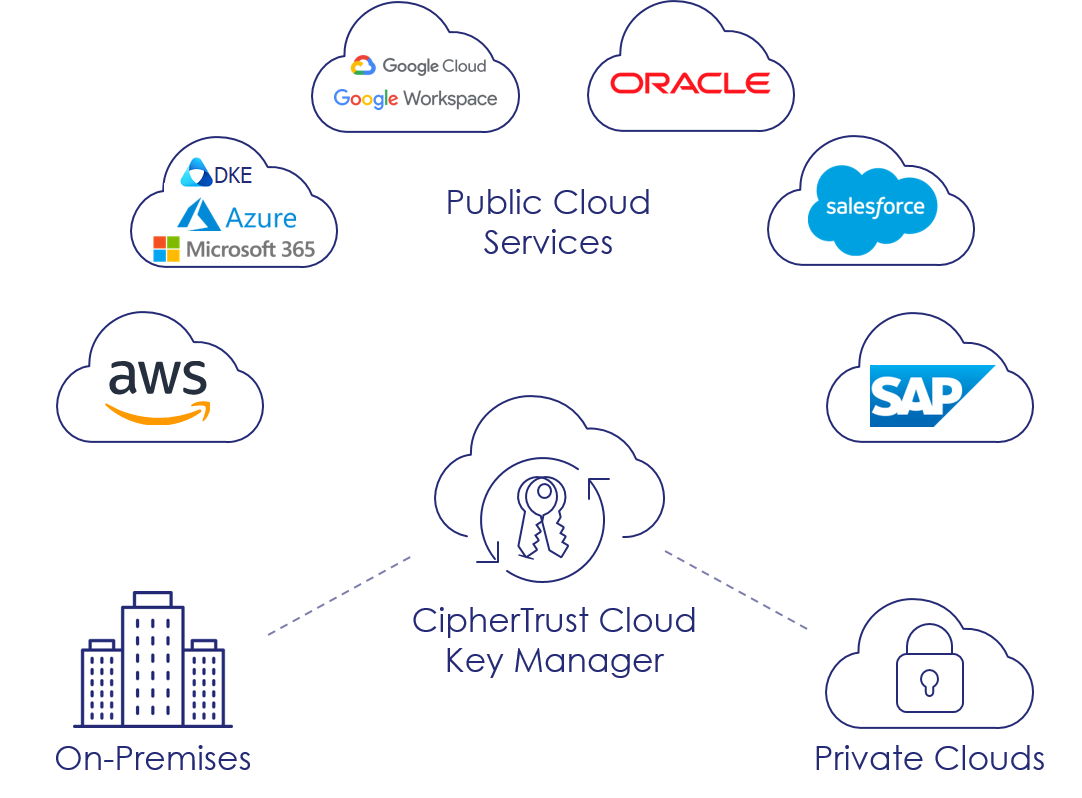
The following diagram shows the high level CCKM overview:
 CCKM Components
CCKM Components
The CCKM solution comprises the following components:
CCKM GUI on the CipherTrust Manager for administrators and users
At least one of the supported clouds
A supported trusted key source
A supported Internet browser
The product is delivered as a licensed component of the CipherTrust Manager appliance that can be installed on any one of the supported deployment methods.
 Supported Clouds
Supported Clouds
Amazon Web Services (AWS)
AWS China
AWS GovCloud
Azure Cloud
Azure China Cloud
Azure US Government
Google Cloud
Oracle Cloud
Salesforce
- Salesforce Sandbox
SAP Data Custodian
Note
AWS China cloud does not support uploading 256-bit keys. It supports 128-bit keys only. CCKM automatically uploads 128-bit keys to the AWS China cloud through the GUI. Other AWS clouds support upload of 256-bit keys.
AWS China cloud does not support creation of native asymmetric keys.
Azure China cloud requires that the CipherTrust Manager and automated systems are deployed in the same VPC and subnet.
 Supported Cloud Services
Supported Cloud Services
AWS Customer Managed CMKs
AWS Custom Key Stores
AWS CloudHSM Key Stores
External Key Stores (XKS)
Azure Cloud BYOK
Azure Key Vault Managed HSM
Azure Stack (Azure Active Directory, Azure AD)
Azure Stack (Active Directory Federation Services, AD FS)
Google Workspace Client Side Encryption (CSE)
Google Cloud CustomerManaged Encryption Keys (CMEK)
Google Cloud External Key Manager (EKM)
Google Ubiquitous Data Encryption (EKM+UDE)
Microsoft Double Key Encryption (DKE)
Oracle Cloud Infrastructure (OCI) (BYOK)
OCI External Key Management Service (EKMS)
Salesforce Bring Your Own Key (BYOK)
Salesforce Cache-Only Key Service
SAP Data Custodian Key Management Service (BYOK)
 Supported Key Sources
Supported Key Sources
CCKM uses the following as the trusted key sources for the encryption keys employed within the supported clouds:
CipherTrust Manager
External CipherTrust Manager
Azure Dedicated HSM
Luna Network HSM (referred to as Luna HSM in this document): This release supports:
Luna Network HSM Software and Firmware versions v7.3.x and higher.
PED and Password-based HSM configurations.
Import of RSA-4096 keys from Luna HSM Software and Firmware versions 7.4.x and higher.
Symmetric and asymmetric keys with Luna HSM.
Note
CCKM doesn't support FM-enabled Luna HSM as a key source.
Data Security Manager (DSM): This release supports DSM v6.4 Cumulative Patch 3 and higher.
The CipherTrust Manager supports all clouds that CCKM supports. The CipherTrust Manager stores its own keys and the backup keys from the supported clouds.
Note
On the CipherTrust Manager, CCKM cannot manage source keys created on the CCKM Appliance v1.x.
 Supported Deployment Methods
Supported Deployment Methods
The CCKM is delivered as part of the CipherTrust Manager appliance. So, CCKM can be automatically deployed with the deployment of the CipherTrust Manager in the following supported environments:
Amazon Web Services
Google Cloud Platform
Microsoft Azure
Oracle Cloud
Private Clouds - Oracle VMware vSphere, Microsoft Hyper-V, and OpenStack
Physical Appliances
Refer to the CipherTrust Manager Deployment Guide for the complete list of supported environments and deployment instructions.
 Supported Internet Browsers
Supported Internet Browsers
The CCKM supports the following Internet browsers:
Chrome 51.0.2704 (64-bit) or later
Firefox 45.0 or later
Microsoft Edge 91.0.864.37 or later
 CCKM Functionality
CCKM Functionality
The CCKM provides following functionalities for the supported cloud services:
Life cycle management of keys, key versions, and attributes:
View Keys
Update Keys
Upload Keys
Rotate Keys
Delete Keys
Disaster recovery of keys:
Backup Keys
Restore Keys
Hybrid key management:
On-premise keys storage
Management of both keys originating from trusted key sources and cloud-provider-sourced keys
Key synchronization
Compliance management:
On-premise key storage with up to FIPS 140-2 Level 3 certification (CipherTrust Manager K570 with K7 card, Luna Network HSM, DSM)
Key storage in public or private clouds, inaccessible to cloud services with FIPS 140-2 Level 1 (Luna Network HSM, DSM)
Key visibility reporting:
Key Activity Report: Inspect individual key histories by operations, for example, when they were refreshed, rotated, edited, or deleted. Also, use this report to compare key activities between CCKM and a cloud service.
Key Aging Report: Track keys by their expiration dates. Audit a range of dates, from past material deletions to future scheduled deletions, within a cloud service.
Service/Usage Report: Monitor key usage by tracking services and applications consuming the keys. View when and where a service requests the use of each key.
Note
Reporting is not supported for the Azure Stack cloud. All clouds do not support all types of reports. Refer to related sections of the CCKM documentation for cloud-specific reports.
 User Roles
User Roles
CCKM has the following users with different responsibilities in administering and using the resources of supported clouds and key sources.
 CCKM Admins
CCKM Admins
There is a System Defined Group named "CCKM Admins". Users within the "CCKM Admins" group are CCKM Administrators. Additionally, the CCKM administrators need the Key Users, Connection Admins, and User Admins permissions to perform key operations on the supported clouds.
A CCKM Administrator is responsible for creating and managing the following resources:
AWS KMS Accounts, AWS Keys, AWS Custom Key Stores
Azure Key Vaults, Azure Subscriptions, and Azure Keys
Luna HSM Partitions, Luna Keys
DSM Domains, DSM Keys
Google Cloud Projects, Key Rings, and Keys
Google EKM endpoints
Microsoft DKE endpoints
Salesforce Organizations, Tenant Secrets
SAP Groups, SAP Keys
CCKM Schedules
CCKM Reports
 CCKM Users
CCKM Users
There is a System Defined Group named "CCKM Users". CCKM users registered with the CipherTrust Manager are part of this group. Additionally, the CCKM users need the Key Users permissions to perform key operations on the supported clouds. As well, they need custom key store permissions to manage AWS custom key stores.
 Additional ACLs/Permissions
Additional ACLs/Permissions
Additional ACLs/permissions can be granted to different CCKM roles on individual cloud resources such as AWS Accounts, Azure Key Vaults, DSM Domains, Google Key Rings, Luna HSM Partitions, Oracle Vaults, Salesforce Organizations, and SAP Groups.
Refer to the CCKM documentation of the respective clouds.
 Support for Changing the Default Port of Web Interface Setting
Support for Changing the Default Port of Web Interface Setting
The web interface port within CipherTrust Manager can be changed from the default port of 443 to another port. The web interface is used to serve both the GUI and the REST API in CCKM. Changing the web interface port does not affect the BYOK use cases in CCKM. However, it does affect the following cloud services:
AWS XKS
Google EKM
Google Workspace CSE
Microsoft DKE
OCI EKMS (HYOK)
SFDC Cache-only Key
If you plan to change the default port for the CipherTrust Manager web interface, ensure to change it before configuring these cloud services on CCKM.
Note
Changing the default port after configuring these cloud services is not supported.
To change the web interface port when configuring a CSE, DKE, Google EKM, or SFDC Cache-only endpoint, specify the new port number along with the hostname when adding the hostname. For example, example.com:8443.
In the case of AWS XKS and Google Cryptospace, AWS KMS and Google only accept and send requests on the default port of 443. If you wish to use a different port for the web interface other than the default, add a network component, such as a load balancer or a firewall, in front of CipherTrust Manager. Then configure port mapping on this component by mapping port 443 to the non-default port on the CipherTrust Manager you plan to use.
For more information about the CipherTrust Manager web interface, refer to Interfaces.
 Proxy Configuration
Proxy Configuration
If you plan to run the CipherTrust Manager appliance behind a proxy, you must configure the proxy, as described in Proxy Configuration.
Note
For CCKM, configure an HTTPS proxy.
For the list of URLs to be whitelisted, refer to URLs to Whitelist for Running CipherTrust Manager Behind Proxy.
Now, you should be able to connect CCKM with the cloud through the proxy.
 URLs to Whitelist for Running CipherTrust Manager Behind Proxy
URLs to Whitelist for Running CipherTrust Manager Behind Proxy
The following URLs must be whitelisted before you run the CipherTrust Manager behind a proxy.
 Amazon Web Services
Amazon Web Services
| Service | URL | Purpose |
|---|---|---|
| CloudWatchLogs | logs.<region-name>.amazonaws.com | Fetch AWS reports. |
| EC2 | ec2.amazonaws.com | Required to fetch AWS regions. After all the regions are fetched, the service is no longer needed. |
| EC2 | ec2.us-east-1.amazonaws.com | Required to fetch AWS regions. After all the regions are fetched, the service is no longer needed. |
| EC2 | ec2.<region-name>.amazonaws.com | Required to fetch AWS regions. This URL is used if aws_sts_regional_endpoints is set to regional when adding an AWS connection. After all the regions are fetched, the service is no longer needed. |
| IAM | iam.amazonaws.com | Manage access to AWS services and resources securely. |
| KMS | kms.<region-name>.amazonaws.com | Communicate with AWS KMS for key management. |
| STS | sts.amazonaws.com | Authenticate AWS users. |
| STS | sts.<region-name>.amazonaws.com | Authenticate AWS users. This URL is used if aws_sts_regional_endpoints is set to regional when adding an AWS connection. |
| AWS | aws.amazon.com | Redirects to service URLs. |
 AWS GovCloud
AWS GovCloud
| Service | URL | Purpose |
|---|---|---|
| CloudWatchLogs | logs.<region-name>.amazonaws.com | Fetch AWS reports. |
| EC2 | ec2.amazonaws.com | Required to fetch AWS regions. After all the regions are fetched, the service is no longer needed. |
| EC2 | ec2.us-gov-east-1.amazonaws.com | Required to fetch AWS regions. After all the regions are fetched, the service is no longer needed. |
| EC2 | ec2.<region-name>.amazonaws.com | Required to fetch AWS regions. This URL is used if aws_sts_regional_endpoints is set to regional when adding an AWS connection. After all the regions are fetched, the service is no longer needed. |
| IAM | iam.amazonaws.com | Manage access to AWS services and resources securely. |
| KMS | kms.<region-name>.amazonaws.com | Communicate with AWS KMS for key management. |
| STS | sts.us-gov-east-1.amazonaws.com | Authenticate AWS users. |
| STS | sts.<region-name>.amazonaws.com | Authenticate AWS users. This URL is used if aws_sts_regional_endpoints is set to regional when adding an AWS connection. |
 AWS China Cloud
AWS China Cloud
| Service | URL | Purpose |
|---|---|---|
| CloudWatchLogs | logs.<region-name>.amazonaws.com.cn | Fetch AWS reports. |
| EC2 | ec2.amazonaws.com.cn | Required to fetch AWS regions. After all the regions are fetched, the service is no longer needed. |
| EC2 | ec2.cn-north-1.amazonaws.com.cn | Required to fetch AWS regions. After all the regions are fetched, the service is no longer needed. |
| EC2 | ec2.<region-name>.amazonaws.com.cn | Required to fetch AWS regions. This URL is used if aws_sts_regional_endpoints is set to regional when adding an AWS connection. After all the regions are fetched, the service is no longer needed. |
| IAM | iam.amazonaws.com | Manage access to AWS services and resources securely. |
| KMS | kms.<region-name>.amazonaws.com.cn | Communicate with AWS KMS for key management. |
| STS | sts.cn-north-1.amazonaws.com.cn | Authenticate AWS users. |
| STS | sts.<region-name>.amazonaws.com.cn | Authenticate AWS users. This URL is used if aws_sts_regional_endpoints is set to regional when adding an AWS connection. |
 Azure Public Cloud
Azure Public Cloud
| URL | Purpose |
|---|---|
| management.azure.com | Fetch subscriptions and key vaults |
| login.microsoftonline.com | Authenticate Azure credentials |
| graph.windows.net | For Azure Stack |
| vault.azure.net | Manage keys |
| *.vault.azure.net | Manage keys |
| api.loganalytics.io | Fetch Azure reports |
| managedhsm.azure.net | Manage keys |
| *.managedhsm.azure.net | Manage keys |
 Azure Public Cloud (for Microsoft DKE)
Azure Public Cloud (for Microsoft DKE)
| URL | Purpose |
|---|---|
| login.microsoftonline.com | Authenticate Azure credentials |
| graph.microsoft.com | Fetch users and user roles |
 Azure US Gov Cloud
Azure US Gov Cloud
| URL | Purpose |
|---|---|
| management.core.usgovcloudapi.net | Fetch subscriptions and key vaults |
| management.usgovcloudapi.net | Fetch subscriptions and key vaults |
| login.microsoftonline.us | Authenticate Azure credentials |
| vault.usgovcloudapi.net | Manage keys |
| *.vault.usgovcloudapi.net | Manage keys |
| graph.windows.net | For Azure Stack |
| api.loganalytics.us | Fetch Azure reports |
 Azure China Cloud
Azure China Cloud
| URL | Purpose |
|---|---|
| management.core.chinacloudapi.cn | Fetch subscriptions and key vaults |
| management.chinacloudapi.cn | Fetch subscriptions and key vaults |
| login.chinacloudapi.cn | Authenticate Azure credentials |
| vault.azure.cn | Manage keys |
| *.vault.azure.cn | Manage keys |
| graph.chinacloudapi.cn | For Azure Stack |
 Google Cloud CMEK
Google Cloud CMEK
| URL | Purpose |
|---|---|
| https://oauth2.googleapis.com | Authenticate Google cloud service accounts |
| https://cloudresourcemanager.googleapis.com | Fetch Google cloud projects |
| https://cloudkms.googleapis.com | Manage Google cloud keys, and fetch Google cloud locations and key rings |
| https://logging.googleapis.com | Fetch Google cloud reports |
 Google Cloud EKM
Google Cloud EKM
| URL | Purpose |
|---|---|
| https://www.googleapis.com/ | Verify and validate authentication and authorization JWTs |
| https://compute.googleapis.com | Creates and runs virtual machines on Google Cloud platforms. Required for EKM Ubiquitous Data Encryption (UDE) upstream verification. |
 Google Workspace CSE
Google Workspace CSE
| URL | Purpose |
|---|---|
| https://www.googleapis.com/ | Verify and validate authorization JWTs |
| https://admin.google.com | • Configure endpoint URLs and Identity Provider (IdP) settings on the Google Admin Console • Cross-Origin Resource Sharing (CORS) URL to allow requests from the Origin URL |
| https://krahsc.google.com | CORS URL to allow requests from the Origin URL |
| https://docs.google.com | Encrypt and decrypt Google Docs |
| https://drive.google.com | Encrypt and decrypt Google Drive |
| https://meet.google.com | Encrypt and decrypt Google Meet calls |
| https://calendar.google.com | Encrypt and decrypt Google Calendar events |
| https://mail.google.com | Encrypt and decrypt Gmail messages |
| https://client-side-encryption.google.com | CORS URL to allow requests from the Origin URL |
| Identity Provider URL | Verify and validate the authentication JWTs |
The following redirect callabck URIs need to be configured on the IdP application (for example, auth0) for authentication.
https://client-side-encryption.google.com/callback
https://client-side-encryption.google.com/oidc/cse/callback
https://client-side-encryption.google.com/oidc/drive/callback
https://client-side-encryption.google.com/oidc/gmail/callback
https://client-side-encryption.google.com/oidc/meet/callback
https://client-side-encryption.google.com/oidc/calendar/callback
https://client-side-encryption.google.com/oidc/docs/callback
https://client-side-encryption.google.com/oidc/sheets/callback
https://client-side-encryption.google.com/oidc/slides/callback
 Oracle Cloud
Oracle Cloud
| Service | URL | Purpose |
|---|---|---|
| Audit | audit.<region>.oraclecloud.com | Fetch OCI audit logs that will be used for OCI report generation. |
| Identity | identity.<region>.oci.oraclecloud.com | Required to test connection and fetch Oracle compartments and other related resources. |
| Identity Domain | <identity domain URL> | Required to verify and validate the authorization JWT. |
| Vault (KMS) | kms.<region>.oraclecloud.com | Communicate with OCI vaults for key management. |
| Object Storage | objectstorage.<region>.oraclecloud.com | Communicate with OCI buckets for key backup/restore. |
 Salesforce Cloud
Salesforce Cloud
| URL | Purpose |
|---|---|
| login.salesforce.com | Authenticate Salesforce user credentials |
| test.salesforce.com | Verify SFDC Sandbox users (used to test connection with the Salesforce Sandbox) |
| <YourInstance>.salesforce.com | Manage keys |
 SAP Data Custodian
SAP Data Custodian
| Service | URL | Purpose |
|---|---|---|
| KMS | <instance-subdomain>.datacustodian.cloud.sap | Communicate with SAP KMS for authorization, audit, cryptography, keys, groups, and backups. |
 Connecting CCKM in Amazon Virtual Private Cloud (VPC)
Connecting CCKM in Amazon Virtual Private Cloud (VPC)
When AWS KMS is in Amazon VPC:
IAM is not supported, as it is a global AWS service. Therefore, CCKM users cannot fetch IAM roles and users.
CCKM cannot connect with the EC2, KMS, Logs, and STS services using public IP addresses. If their endpoints are not added on AWS, you cannot add AWS connections and AWS keys on the CipherTrust Manager. For successful connection, add the IP addresses of VPC endpoints for these services for your AWS regions to the DNS hosts on the CipherTrust Manager.
For example, you need to add the IP addresses of VPC endpoints of sts.amazonaws.com, ec2.us-east-1.amazonaws.com, logs.us-east-1.amazonaws.com, and kms.us-east-1.amazonaws.com service URLs to the DNS hosts list.
To add the IP address of a VPC endpoint:
On AWS Console
Create the VPC endpoint for a service.
Copy the DNS name of the service.
Ping the DNS name to find out the associated IP address.
Copy the IP address.
On CipherTrust Manager
Log on to the CipherTrust Manager GUI.
In the left pane, click Admin Settings > DNS Hosts.
Click Add DNS Host.
In the Hostname field, enter the service URL, for example,
sts.amazonaws.com.In the IP Address field, paste the copied IP address.
Click Save.
Similarly, add the DNS host entries for all three services, for all your AWS regions.