
Luna SA Online Help
The SafeNet Luna SA is an Ethernet-attached HSM (Hardware Security Module) Server designed to protect critical cryptographic keys and to accelerate sensitive cryptographic operations across a wide range of security applications. Luna SA includes many features that increase security, connectivity, and ease-of-administration in dedicated and shared security applications.
Luna SA comes in one of two model families, according to the level of authentication and access control. Your Luna SA was factory configured to operate as either:
The standard appliance is the 1U-high, rackmount, device:

which replaces the Luna SA 4.x device.

Here are some of the important physical features of the Luna SA appliance.
First, the front (this illustration shows the appliance with its decorative bezel removed)...
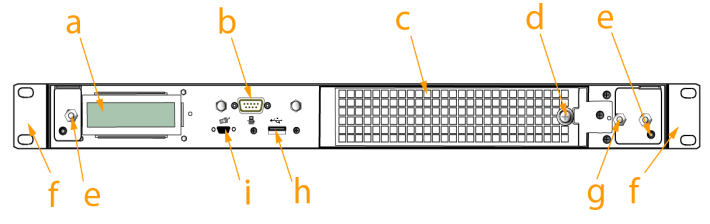
| Item | Description |
|---|---|
| a | LCD system status screen - shows IP info and scrolls through system status messages |
| b | Serial (console) port - local connection for initial setup, and for admin account reset (local-only action for security reasons) |
| c | Ventilation-fan filter cover - removable bracket allows cleaning of air filter |
| d | Fan filter cover retaining screw - a captive thumb-screw (no tool needed) ( "Power Supply and Fan Maintenance" ) |
| e | Mounts for removable front bezel - the decorative/protective front bezel mounts on the appliance front panel. Spring clips behind the bezel engage the mounting posts at the left and right ends of the appliance front panel. |
| f | Rack-mount tabs (removable) - use these on the front, and the sliding tabs toward the rear to support your Luna appliance in a compatible equipment rack |
| g | Securing screw for fan bay - Torx screw secures the fan bay; opening to swap fan modules triggers a tamper event on the appliance |
| h | USB port - use to connect Luna Remote Backup HSM (for backup of your HSM partition contents), Luna G5 HSM, or Luna DOCK 2 (for PKI and for migration of cryptographic material from older backup token HSMs); same as USB port on back panel |
| i | PED port - attach Luna PED 2, Pin Entry Device, reads the hardware (iKey) authentication devices for Trusted Path (FIPS 140 level 3) access control |
Then, the back...
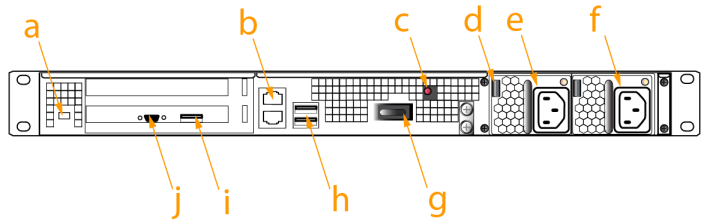
| Item | Description |
|---|---|
| a | Kensington Security Slot - attach an industry-standard locking cable for additional physical security |
| b | Ethernet ports - for network connection of your Luna appliance |
| c | Decommissioning button - recessed for safety; renders HSM contents unusable ( "HSM "Emergency Decommission" Button" ) |
| d | Power supply release tab - press tab to release the catch, and slide the power supply out |
| e | Removable power supply - one of two redundant power supplies ( "Power Supply and Fan Maintenance" ) |
| f | 2nd removable power supply - the other of two redundant power supplies |
| g | Start/stop switch - use to stop the system if the command-line shutdown is not available; use to restart the system if it has been switched off |
| h | USB ports - use to connect Luna Remote Backup HSM (for backup of your HSM partition contents), Luna G5 HSM, or Luna DOCK 2 (for PKI and for migration of cryptographic material from older backup token HSMs); same as USB port on front panel |
| i, j | Unused ports - these ports are not used for Luna SA; we recommend that you do not remove the covers that were installed at the factory |
At any given time, , and a newer not-yet-validated version might also be available. The usual practice is to ship units pre-loaded with the firmware and software at the FIPS-validated level, by default, while providing the option to update the Client software, Appliance software, and Appliance firmware to the newer version. This allows customers who need FIPS validation to have that configuration from the factory, and customers who need newer features (and do not need FIPS validation) to upgrade by simply installing the newer software and following the upgrade procedure.
To check the progress of HSM versions that are submitted for FIPS 140-2 validation visit the NIST site at:
( http://csrc.nist.gov/groups/STM/cmvp/validation.html ).
Similarly, some versions of product are submitted for Common Criteria EAL evaluation ( "Common Criteria" ).
You can also check SafeNet Sales or SafeNet Customer Support to inquire about certification status of SafeNet HSM products. If FIPS validation or CC EAL certification are not requirements for you, then the newest version is normally the preferred option.
The SafeNet HSM's integrated SafeNet-Luna Cryptographic Engine is used to perform cryptographic operations and provide secure storage for sensitive cryptographic keys.
The SafeNet-Luna Cryptographic Engine enables the Luna SA functionality by providing:
The SafeNet-Luna Cryptographic Engine can also be used in conjunction with the optional Trusted Path Authentication feature to provide FIPS 140-2 Level 3 validated HSM operation. That option is factory-configured and not subject to change in the field.
HSMs, in general, are designed to provide dedicated cryptographic functionality, including key generation, key storage, and digital signing, on a one-to-one basis to their host applications. For example, a database server using an HSM would require one HSM, while a secure website using SSL on the same network would require a second, separate HSM. As the number of secure applications requiring an HSM grows, so does the number of ordinary HSMs deployed.
Luna SA bypasses this limitation by implementing multiple virtual HSMs, or HSM Partitions on a single HSM server. Partitions are accessed via a Network Trust Link ( "Prepare the Client for Network Trust Link" ).
The following block diagram is a conceptual overview of the Luna SA HSM Server depicting internal systems, communications, and interaction with application servers.
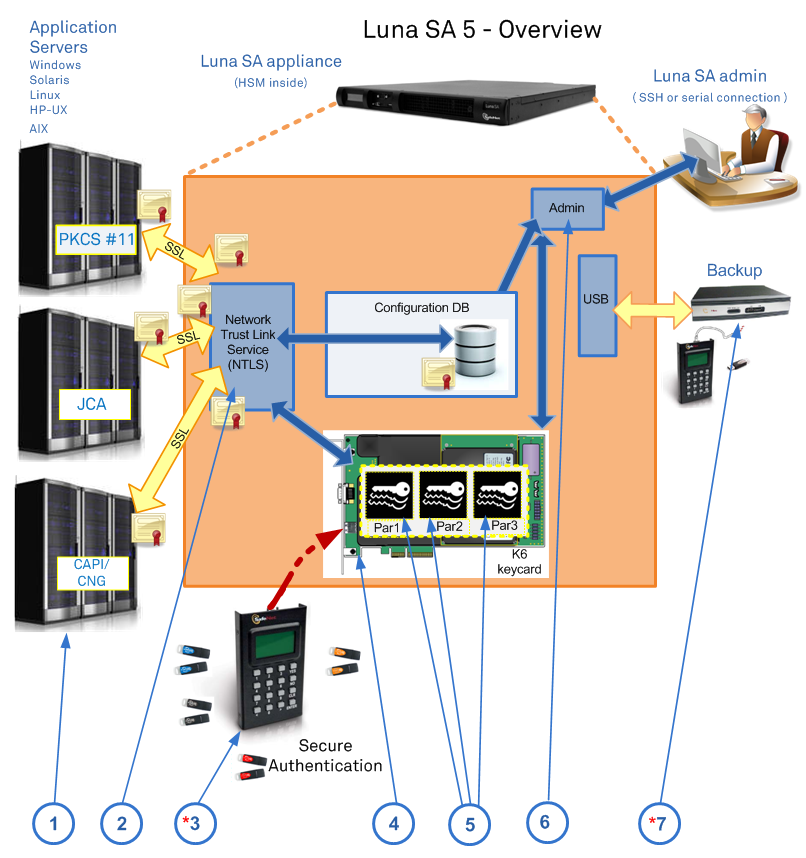
There are 7 major elements to the Luna SA operations. Some of these elements are optional configuration items, and might not be present in your system:
(* The Secure Backup HSM, and Luna PED (Trusted Path Authentication and Access Control) are options that might not be included with your system.)
The product name "Luna" was taken from the name of the Luna moth, to conform with the originating company name "Chrysalis-ITS". The company name was derived from the hidden or secret existence of the moth as it developed within its cocoon, or the chrysalis. This was evocative of the hidden world of cryptography. Other moth names were considered for additional product lines, but the "Luna" brand very quickly achieved marketplace recognition and efforts were aligned under that brand.
After years of growing success with the Luna brand in the crypto markets, Chrysalis-ITS was acquired by SafeNet. Because the brand was well recognized and respected in the HSM marketplace, SafeNet maintained it.
Our SNMP MIB is still called CHRYSALIS.
From the Table of Contents, choose one of the guides for specific help on:
|
|
|
|
|
|
|
In no particular order, here are some other familiarization pages that might be of use before you begin configuring your Luna SA:
- "Luna Do and Don't Suggestions"
- "Notes about using Luna shell (lunash)"