HAProxy
This guide will walk you through the process of securing the SSL keys used for SSL termination in HAProxy by utilizing a Thales Luna HSM in conjunction with the OpenSSL toolkit, enhanced with GemEngine support. HAProxy is a powerful, open-source load balancer that efficiently distributes network or application traffic across multiple servers, ensuring high availability and reliability. By integrating HAProxy with the Thales Luna HSM, we enhance security for SSL termination, providing a robust solution for secure data transport. The Thales Luna HSM provides a dedicated, tamper-resistant environment for cryptographic operations, ensuring that private keys are never exposed to the application layer.
The key benefits of this integration are:
-
Secure generation, storage, and protection of the identity signing private keys using either FIPS 140-2 or FIPS 140-3 Level 3 validated hardware.
-
Full life cycle management of the keys to ensure their integrity and reliability throughout their usage.
-
Maintenance of a comprehensive HSM audit trail for transparency and accountability in key operations.
-
Significant performance enhancements by offloading cryptographic operations from application servers.
Tested Platforms
This integration is tested with Luna HSM on the following operating systems:
| Platforms Tested | HAProxy Version | GemEngine / LunaProv Version | OpenSSL Version |
|---|---|---|---|
| RHEL 9 | HAProxy 2.8 | LunaProv 1.7 | OpenSSL 3.5.1 |
| RHEL 8 | HAPEE 3.0r1 HAProxy 2.2 |
GemEngine 1.5 GemEngine 1.3 |
OpenSSL 1.1.1 OpenSSL 1.0.2 |
| Ubuntu 18.04 | HAProxy 1.8 | GemEngine 1.3 | OpenSSL 1.1.1 OpenSSL 1.0.2 |
| RHEL 7 CentOS 7 |
HAProxy 1.8 | GemEngine 1.2 | OpenSSL 1.0.2 |
This integration has been validated with Luna HSM configured in both HA mode and FIPS mode.
Prerequisites
Before proceeding with the integration, ensure the following tasks are completed:
Configure Luna HSM
Follow these steps to set up your on-premise Luna HSM:
Ensure that the HSM is set up, initialized, provisioned, and ready for deployment. For more information, refer to Luna HSM documentation.
Create a partition that will be later on used by HAProxy.
Generate and exchange NTLS certificates between the Luna Network HSM and the client system. Each side must register the other’s certificate to establish mutual trust. After the certificate exchange is complete, register the client with the HSM and assign the required partition to enable the NTLS connection.
Initialize Crypto Officer and Crypto User roles for the registered partition.
Run the following command to verify that the partition has been successfully registered and configured:
/usr/safenet/lunaclient/bin/lunacm
Upon successful execution, you should observe an output similar to the example provided below:
lunacm (64-bit) v10.9.0-65. Copyright (c) 2025 Thales Group. All rights reserved. Available HSMs: Slot Id -> 0 Label -> HAProxy Serial Number -> 1578908117659 Model -> LunaSA 7.9.0 Firmware Version -> 7.9.0 Bootloader Version -> 1.1.5 Configuration -> Luna User Partition With SO (PW) Key Export With Cloning Mode Slot Description -> Net Token Slot FM HW Status -> FM Ready Current Slot Id -> 0
Refer to Luna HSM documentation for detailed steps on creating NTLS connection, initializing the partitions, and assigning various user roles.
For proper configuration of a PED-based Luna HSM, it is recommended to activate partition policies 22 and 23, allowing for both activation and auto-activation.
This integration is fully tested with both HA and FIPS modes.
Managing User Access to Your HSM
Initially, only the root user can access the HSM. However, you can grant access to specific non-root users by including them in the hsmusers group. This group is automatically created when you install the client software. Even if you later uninstall the client software, the hsmusers group remains intact, ensuring you can upgrade your software without losing your user access settings.
To add users to the hsmusers group
If you wish to permit non-root users or applications to interact with the HSM device, you must assign these users to the hsmusers group. Make sure that the users you intend to add to the hsmusers group are already established on the client workstation. Only users added to the hsmusers group will be granted access to the HSM device. Follow these steps to add a user to the hsmusers group:
Ensure that you possess sudo privileges on the client workstation.
Add a user to the hsmusers group using the command:
sudo gpasswd --add <username> hsmusers
Replace username with the actual username you want to include in the hsmusers group.
To remove users from the hsmusers group
If you need to withdraw a user's authorization to access the HSM device, you can remove them from the hsmusers group. Carry out the following steps to remove a user from the hsmusers group:
Confirm that you hold sudo privileges on the client workstation.
Eliminate a user from the hsmusers group using the command:
sudo gpasswd --add <username> hsmusers
Replace username with the specific username you want to exclude from the hsmusers group. To observe the changes, you will need to log in again.
Any user you remove will retain access to the HSM device until the client workstation is rebooted.
Set up Luna HSM in FIPS mode
To configure Luna HSM in FIPS Mode, it's important to ensure that your RSA key generation methods comply with FIPS 186-3/4 standards. Specifically, FIPS 186-3/4 approves two methods for generating keys: 186-3 with primes and 186-3 with aux primes. This means that RSA PKCS and X9.31 key generation methods are no longer allowed when operating your Luna HSM in a FIPS-compliant mode. When using the Luna HSM in FIPS mode, you should make adjustments to your configuration settings by following these steps:
Open the configuration file for your Luna HSM.
Look for the [Misc] section within the configuration file.
Add or modify the following setting within the [Misc] section:
RSAKeyGenMechRemap=1
This setting instructs the Luna HSM to redirect older key generation mechanisms to the newly approved mechanism when the HSM is operating in FIPS mode.
This adjustment is not necessary for the Universal Client.
This configuration change applies exclusively to Luna Client 7.x.
Set up Luna HSM HA group
Refer to Luna HSM documentation for HA steps and details regarding configuring and setting up two or more HSM boxes on host systems. You must enable the HAOnly setting in HA for failover to work so that if the primary goes down due to any reason, all calls get automatically routed to the secondary until the primary recovers and starts up.
Download OpenSSL Toolkit for Luna Provider
Download the OpenSSL toolkit with Luna Provider support from the Thales GitHub repository.
Download OpenSSL Toolkit for Gem Engine
Download the OpenSSL toolkit with Gem Engine support from the Thales Customer Support Portal.
You can also download the toolkit from the Thales GitHub repository and use it to compile and build the Gem Engine. For reference, the Support Portal Doc IDs for GemEngine versions are:
- v1.6 — KB0026742
- v1.5 — KB0024584
- v1.3 — KB0017806
- v1.2 — KB0016309
Set up HAProxy
For this integration, it's recommended to use an Apache web server to serve a static webpage. The following three machines are used in this setup:
- Primary Machine: Acts as the Load Balancer with HAProxy installed. For detailed installation instructions, refer to the HAProxy Documentation.
If you need to install HAProxy with a custom OpenSSL, refer to the Appendix section of this document.
If using Luna HSM in FIPS mode, HAProxy should also be built with OpenSSL that supports the FIPS module.
- Two Secondary Machines: Operate as backend servers with FQDN and IP enabled, running Apache or any other web server.
You can modify this configuration according to your requirements.
Integrating Luna HSM with HAProxy Using Luna Provider
To integrate Luna HSM with HAProxy, complete the following tasks:
Configure OpenSSL/HAProxy to use Luna Provider
To configure OpenSSL/HAProxy to use Luna Provider, follow these steps:
Download the Luna Provider toolkit from the Thales GitHub repository.
Refer to the OpenSSL Integration Guide to compile and install Luna Provider for OpenSSL.
You can also follow the instructions in the README-PQC-BUILD file located in the docs directory of the downloaded toolkit. This document provides details on compiling and building the provider with OpenSSL.
Verify that Luna Provider support is available along with the default OpenSSL provider:
# openssl list -provider lunaprov -provider default -providers
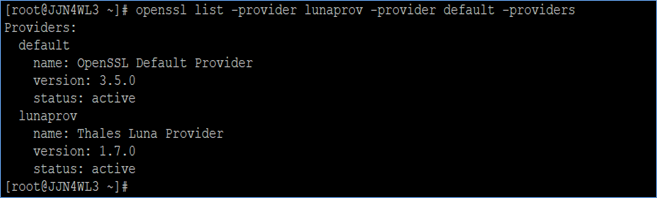
If the output resembles the example above, it indicates that the Luna Provider is successfully installed and active.
Create a passfile and store the partition password in it:
# echo <partition_password> > /tmp/passfile
Replace <partition_password> with the actual password of the partition CO.
Open the /etc/Chrystoki.conffile and add the following section:
GemEngine = {
LibPath = /usr/safenet/lunaclient/lib/libCryptoki2_64.so;
LibPath64 = /usr/safenet/lunaclient/lib/libCryptoki2_64.so;
EnableEcGenKeyPair = 1;
EnableRsaGenKeyPair = 1;
DisablePublicCrypto = 1;
EnableRsaSignVerify = 1;
EnableLoadPubKey = 1;
EnableLoadPrivKey = 1;
DisableCheckFinalize = 0;
IntermediateProcesses = 0;
DisableEcdsa = 0;
DisableRand = 0;
DisableSessionCache = 0;
EngineInit = "<partition_label>":0:0:passfile=<path_to_passfile>;
EnableLoginInit = 1;
}
Replace <partition_label> with the actual label of the physical or virtual slot.
Locate the OpenSSL configuration directory where the openssl.cnf file and provider configuration are defined. Run the following command:
openssl version -d
Review the output to identify the OpenSSL configuration directory. For example:
OPENSSLDIR: "/usr/local/ssl"
Verify that you are using the intended OpenSSL installation by running:
which openssl
The configuration directory shown in the output corresponds to the OpenSSL installation available in the system PATH. Ensure that you update the correct openssl.cnf file when multiple OpenSSL versions are present.
Update the openssl.cnf file as shown below:
a. At the very beginning of the file, add:
openssl_conf = openssl_init
b. Then scroll down a few lines to find the following section and update it:
[openssl_init] providers = provider_sect [provider_sect] lunaprov = lunaprov_sect default = default_sect [default_sect] activate = 1 [lunaprov_sect] activate = 1
If you explicitly activate any other provider (for example, the Luna Crypto Provider), you must also explicitly activate the default provider. Otherwise, the default provider becomes unavailable in OpenSSL, which may cause applications depending on OpenSSL to stop working. This can result in significant system issues, including the inability to remotely access the system.
Verify that the OpenSSL Luna Provider is loading by default without specifying any provider:
openssl list -providers
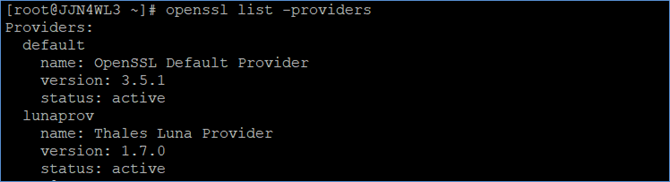
If the output resembles the example above, then the OpenSSL Luna Provider is configured as the default provider for OpenSSL.
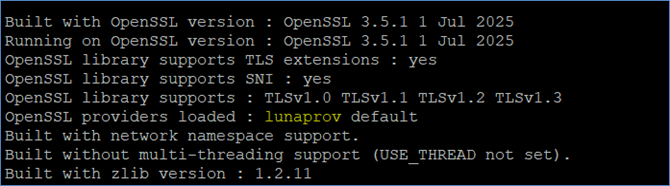
Ensure that HAProxy is loading lunaprov as a provider:
haproxy -vv
Configure HAProxy for SSL termination
To configure HAProxy for SSL termination, follow these steps:
Create a key pair on Luna HSM:
openssl genpkey -algorithm RSA -pkeyopt rsa_keygen_bits:3072 -out key.pem
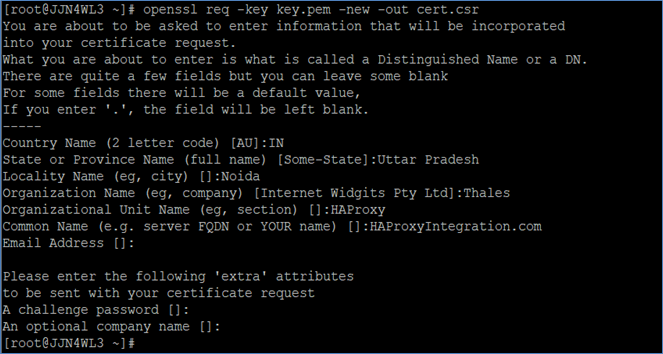
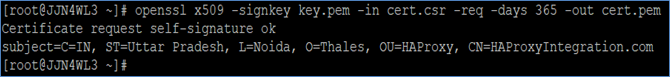
Create a certificate request using the key generated on Luna HSM:
openssl req -key key.pem -new -out cert.csr
Submit the certificate request to your Certificate Authority (CA) and obtain a CA-signed certificate. Alternatively, you can use a self-signed certificate.
Create a self-signed certificate from the certificate request using the private key generated on Luna HSM:
openssl x509 -signkey key.pem -in cert.csr -req -days 365 -out cert.pem
This integration uses self-signed certificates only for test environments. For production environments, always use a certificate authority to issue certificates. Skip this step if you are using a CA-signed certificate.
Copy the private key reference and certificate to a new file at /etc/haproxy/haproxy.pem:
cat key.pem cert.pem > /etc/haproxy/haproxy.pem
Open the /etc/haproxy/haproxy.cfg file in a text editor and update the frontend section to bind the server over TLS using the certificate and keys generated on Luna HSM, as shown in the following example:
As shown in the example configuration below, modify the group directive in the global section to match the operating system group that has permission to access Luna Client resources, and update the bind directive in the frontend section to use the correct IP/interface, TLS port, and certificate bundle path generated using the Luna HSM for your deployment environment.
Example:
# Example /etc/haproxy/haproxy.cfg
global
log 127.0.0.1 local2
pidfile /var/run/haproxy.pid
maxconn 4000
user haproxy
group hsmusers
daemon
defaults
mode http
log global
option httplog
option dontlognull
retries 3
timeout http-request 10s
timeout queue 1m
timeout connect 10s
timeout client 1m
timeout server 1m
timeout http-keep-alive 10s
timeout check 10s
frontend my_frontend
bind *:80
use_backend static
option forwardfor
bind *:443 ssl crt /etc/haproxy/haproxy.pem
backend static
balance roundrobin
server server1.example.com 10.164.76.46:80 check
server server2.example.com 10.164.78.129:80 check
The actual path for haproxy.cfg may vary depending on your HAProxy installation. Options in the file may also differ based on your environment. Refer to the HAProxy documentation for details. Replace the backend server IP/URL with values for your setup.
Check whether SELinux is enabled on the system. If it is enabled, set SELinux to permissive mode to prevent policy restrictions from blocking HAProxy access to Luna Client resources. Run the following command to temporarily set SELinux to permissive mode:
setenforce 0
To make this change permanent, open /etc/selinux/config and update the following parameter:
SELINUX=permissive
Reboot the system for the permanent change to take effect:
reboot
Skip this step if SELinux is not enabled or if the system is running Ubuntu.
Ensure that the HAProxy service is using OpenSSL configured with Luna Provider. If it is not configured with the default OpenSSL, add the Environment variable pointing to the correct OpenSSL libraries:
[Unit] Description=HAProxy Load Balancer After=network.target [Service] Environment="LD_LIBRARY_PATH=/usr/local/ssl/lib/" ExecStart=/usr/sbin/haproxy -f /etc/haproxy/haproxy.cfg . . .
Start the HAProxy service:
systemctl start haproxy.service
Ensure you have also added the HAProxy service to the firewall daemon to allow traffic through the firewall.
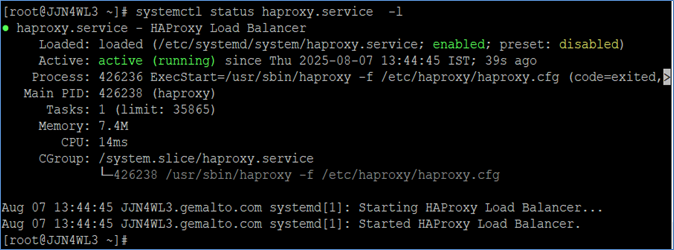
Check the server status and verify it starts without errors:
systemctl status haproxy.service -l
Open a browser and access the HAProxy load balancer:
https://<HostName or IP Address>:443
Accept the certificate and verify its details. The certificate should match the one whose private key is secured on Luna HSM.
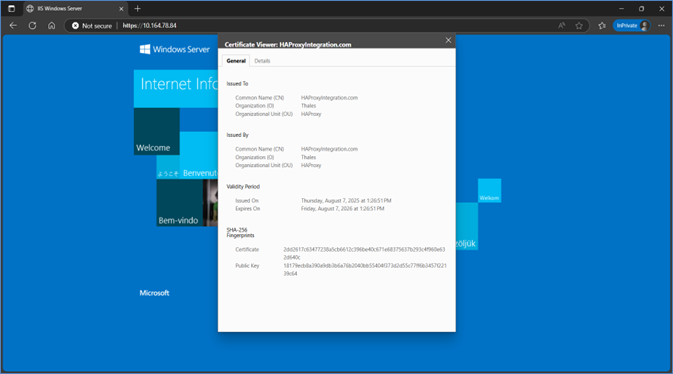
This completes the integration of HAProxy with the Thales Luna HSM using the Luna OpenSSL Provider.
Integrate Luna HSM with HAProxy using Gem Engine
To integrate Luna HSM with HAProxy, you need to perform the following tasks:
Configure OpenSSL to use GemEngine
Follow these steps to configure OpenSSL to use GemEngine:
Copy the GemEngine toolkit to a suitable directory on the client system and navigate to the extracted toolkit location.
Copy the appropriate libgem.so build (matching your OpenSSL version and platform) to the OpenSSL engines directory. For example:
# cp builds/linux/rhel/64/1.0.2/libgem.so /usr/lib64/openssl/engines
Verify that the GemEngine is correctly installed and can be loaded by OpenSSL.
# openssl engine gem -v
If the GemEngine is configured properly, OpenSSL displays output indicating that the gem engine is available along with a list of supported capabilities, similar to the following:
(gem) Gem engine support
enginearg, openSession, closeSession, login, logout, engineinit,
CONF_PATH, ENGINE_INIT, ENGINE2_INIT, engine2init, DisableCheckFinalize,
SO_PATH, GET_HA_STATE, SET_FINALIZE_PENDING, SKIP_C_INITIALIZE,
IntermediateProcesses
Ensure that the GemEngine build used on the system matches the installed OpenSSL version. A version mismatch may prevent the engine from loading.
If OpenSSL is installed from source, refer to the README-GEMBUILD file in the /docs directory of the GemEngine toolkit for detailed build and integration instructions.
Create a passfile to securely store the partition password. For example:
# echo <partition_password> > /tmp/passfile
Ensure that appropriate file permissions are applied so that only the required user can read the passfile.
Edit the /etc/Chrystoki.conf file and add the following GemEngine configuration section:
GemEngine = {
LibPath = /usr/safenet/lunaclient/lib/libCryptoki2_64.so;
LibPath64 = /usr/safenet/lunaclient/lib/libCryptoki2_64.so;
EnableDsaGenKeyPair = 1;
EnableRsaGenKeyPair = 1;
DisablePublicCrypto = 1;
EnableRsaSignVerify = 1;
EnableLoadPubKey = 1;
EnableLoadPrivKey = 1;
DisableCheckFinalize = 0;
IntermediateProcesses = 0;
DisableEcdsa = 1;
DisableDsa = 0;
DisableRand = 0;
EngineInit = <slot_id>:0:0:passfile=<path_to_passfile>;
EnableLoginInit = 1;
}
Replace <slot_id> with the actual physical or virtual slot ID of the partition being used.
Ensure that the passfile path specified in the EngineInit parameter matches the location where the passfile was created.
Configure HAProxy for SSL termination
To configure HAProxy for SSL termination using GemEngine and Luna HSM, perform the following steps.
Generate a private key using GemEngine:
# openssl genrsa -engine gem -out key.pem
Create a self-signed certificate using the generated private key:
# openssl req -engine gem -new -x509 -days 365 -key key.pem -out cert.cer
Self-signed certificates are used in this integration for test or evaluation environments only. For production deployments, obtain certificates issued by a trusted CA.
Combine the private key reference and certificate into a single PEM file for HAProxy:
# cat key.pem cert.cer > /etc/pki/tls/certs/haproxy.pem
Open the HAProxy configuration file in a text editor. The file location varies depending on the HAProxy version and installation method. For example:
/etc/opt/rh/rh-haproxy18/haproxy/haproxy.cfg (Community version) /etc/hapee-3.0/hapee-lb.cfg (Enterprise version)
Update the HAProxy configuration as shown in the following example:
As shown in the example configuration below, update the group directive in the global section to use the appropriate operating system group for Luna Client access, ensure that ssl-engine gem is present in the global section to enable OpenSSL to use GemEngine for cryptographic operations, and modify the SSL-enabled bind directive in the frontend section with the correct IP/interface, TLS port, and certificate bundle path for your deployment.
Example:
global log 127.0.0.1 local2 pidfile /var/run/haproxy.pid maxconn 4000 user haproxy group hsmusers daemon ssl-engine gem tune.ssl.default-dh-param 2048 defaults mode http log global option httplog option dontlognull retries 3 timeout http-request 10s timeout queue 1m timeout connect 10s timeout client 1m timeout server 1m timeout http-keep-alive 10s timeout check 10s frontend https-in bind *:80 option forwardfor use_backend static bind *:443 ssl crt /etc/pki/tls/certs/haproxy.pem backend static balance roundrobin server server1.example.com 10.164.76.117:80 check server server2.example.com 10.164.78.118:80 check
The HAProxy configuration file path and parameters may vary based on installation type and deployment requirements. Refer to HAProxy documentation for detailed information on configuration directives.
Check whether SELinux is enabled on the system. If SELinux is enabled, set it to permissive mode to prevent policy restrictions from blocking HAProxy access to Luna Client resources. Run the following command to temporarily set SELinux to permissive mode:
# setenforce 0
Edit the /etc/selinux/config file to make this change permanent:
SELINUX=permissive
Reboot the system for the change to take effect:
# reboot
Skip this step if SELinux is not enabled or if the system is running Ubuntu.
Start or restart the HAProxy service:
# systemctl start haproxy.service (Community version) # systemctl restart hapee-3.0-lb.service (Enterprise version)
Ensure that the HAProxy service is allowed through the firewall so that traffic can reach the load balancer.
Check the HAProxy service status and verify that it starts without errors:
# systemctl status haproxy.service -l
Example:
rh-haproxy18-haproxy.service - HAProxy Load Balancer
Loaded: loaded (/usr/lib/systemd/system/rh-haproxy18-haproxy.service; disabled; vendor preset: disabled)
Active: active (running) since Fri 2019-03-01 12:08:44 IST; 3s ago
Process: 17181 ExecStartPre=/opt/rh/rh-haproxy18/root/usr/sbin/haproxy -f $CONFIG -c -q (code=exited, status=0/SUCCESS)
Main PID: 17189 (haproxy)
Tasks: 2
CGroup: /system.slice/rh-haproxy18-haproxy.service
+-17189 /opt/rh/rh-haproxy18/root/usr/sbin/haproxy -Ws -f /etc/opt/rh/rh-haproxy18/haproxy/haproxy.cfg -p /run/rh-haproxy18-haproxy.pid
+-17197 /opt/rh/rh-haproxy18/root/usr/sbin/haproxy -Ws -f /etc/opt/rh/rh-haproxy18/haproxy/haproxy.cfg -p /run/rh-haproxy18-haproxy.pid
Mar 01 12:08:42 localhost.localdomain systemd[1]: Starting HAProxy Load Balancer...
Mar 01 12:08:43 localhost.localdomain haproxy[17181]: STC client identity not configured
Mar 01 12:08:44 localhost.localdomain haproxy[17189]: STC client identity not configured
Mar 01 12:08:44 localhost.localdomain systemd[1]: Started HAProxy Load Balancer.
Open a web browser and access the HAProxy load balancer:
https://<HostName_or_IP_Address>:443
Accept the certificate warning (for self-signed certificates) and verify the certificate details.
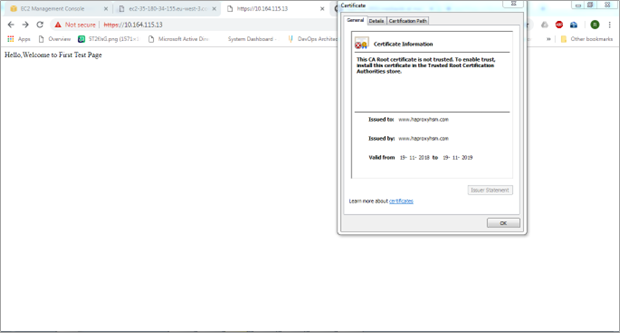
This completes the integration of HAProxy with the Thales Luna HSM using GemEngine.
Integrate Luna HSM with HAProxy by migrating existing SSL keys
To integrate Luna HSM with HAProxy using existing SSL keys, ensure that the HAProxy server is already configured and running with SSL, where the SSL certificate and keys were generated by OpenSSL and stored in a directory. Follow these steps to migrate your existing SSL keys:
Execute the steps outlined in the Configure OpenSSL to use GemEngine section to set up OpenSSL with GemEngine.
Find the directory where your SSL private key and certificate are stored.
Run the following command to extract the public key from your private key:
openssl rsa -in server.key -pubout -out pubkey.pem
Replace server.key with the name of your private key file.
Use the following command to convert your private key to PKCS#8 format:
openssl pkcs8 -in server.key -topk8 -nocrypt -out privatekey.pem
Replace server.key with the name of your private key file.
Use the CMU utility provided with Luna Client to import the public key and private key to the HSM.
- For the public key:
/usr/safenet/lunaclient/bin/cmu import -inputFile pubkey.pem -label haproxy_public_key -pubkey=rsa
- For the private key:
/usr/safenet/lunaclient/bin/cmu importkey -PKCS8 -in privatekey.pem -keyalg RSA
When prompted, provide the partition password.
Verify keys on Luna HSM partition:
- Check that the keys are generated on the Luna HSM partition and note the private key handle:
/usr/safenet/lunaclient/bin/cmu list
- An example output is shown below:
Certificate Management Utility (64-bit) v10.3.0-275. Copyright (c) 2020 SafeNet. All rights reserved. Please enter password for token in slot 0 : ******* handle=2000001 label=CMU Unwrapped RSA Private Key handle=2000002 label=haproxy_public_key
If you have multiple keys, you can recognize the private key by providing it a label. Use the following command:
/usr/safenet/lunaclient/bin/cmu setattribute -handle=2000001 -label=haproxy_private_key
Ensure that the private key label matches the label of the public key:
/usr/safenet/lunaclient/bin/cmu list
An example output is shown below:
Certificate Management Utility (64-bit) v10.3.0-275. Copyright (c) 2020 SafeNet. All rights reserved. Please enter password for token in slot 0 : ******* handle=2000001 label=haproxy_private_key handle=2000002 label=haproxy_public_key
Copy the SAUTIL utility provided with the OpenSSL toolkit to create the private key reference in software:
cp /home/gemengine-1.2/builds/linux/rhel/64/1.0.2/sautil /usr/bin/
Create private key reference:
- Run the SAUTIL utility to create a private key reference to the actual private key imported in Luna HSM:
sautil -v -s 0 -i 0:0 -a 0:RSA -f HSMKey_ref.pem -o -q -c
- Provide the HSM partition password and key handle when prompted. After successful execution of the SAUTIL command,
HSMKey_ref.pemwill be generated.
Delete the private key generated by OpenSSL and the PKCS#8 format key that was used before importing the key into Luna HSM:
rm -rf server.key privatekey.pem
Create the combined certificate file:
- Combine the private key reference and the existing certificate into a new file at
/etc/pki/tls/certs/haproxy.pem:
cat HSMKey_ref.pem softcert.cer > /etc/pki/tls/certs/haproxy.pem
- Replace
softcert.cerwith your existing certificate file that was generated using the software key.
Open the HAProxy configuration file in a text editor and ensure the following configuration is included:
As shown in the example configuration below, update the group directive in the global section to use the appropriate operating system group for Luna Client access, ensure that ssl-engine gem is configured in the global section, and modify the SSL-enabled bind directive in the frontend section with the correct IP/interface, TLS port, and certificate bundle path for your environment.
Example:
global
log 127.0.0.1 local2
pidfile /var/run/rh-haproxy18-haproxy.pid
maxconn 4000
pidfile /var/run/haproxy.pid
user haproxy
group hsmusers
daemon
ssl-engine gem
tune.ssl.default-dh-param 2048
defaults
mode http
log global
option httplog
option dontlognull
retries 3
timeout http-request 10s
timeout queue 1m
timeout connect 10s
timeout client 1m
timeout server 1m
timeout http-keep-alive 10s
timeout check 10s
frontend https-in
bind *:80
use_backend static
option forwardfor
bind *:443 ssl crt /etc/pki/tls/certs/haproxy.pem
backend static
balance roundrobin
server server1.example.com 10.164.76.117:80 check
server server2.example.com 10.164.78.118:80 check
The path to haproxy.cfg may differ based on your HAProxy installation. Adjust fields as needed according to your setup. Ensure you add ssl-engine gem to the global section so that OpenSSL uses GemEngine and the correct certificate location is specified.
Configure SELinux:
- Check the SELinux setting and temporarily set it to permissive mode:
setenforce 0
- To make this change permanent, edit
/etc/selinux/configand set:
SELINUX=permissive
- Reboot the system to apply the changes:
reboot
If you are using Ubuntu, this step is not required.
Restart the HAProxy service to apply the new configuration:
systemctl restart haproxy.service
Ensure that the HAProxy service is added to the firewall rules to allow traffic through the firewall.
Check the status of the HAProxy service to confirm that it is running without errors:
systemctl status haproxy.service
Example:
haproxy.service - HAProxy Load Balancer
Loaded: loaded (/usr/lib/systemd/system/haproxy.service; disabled; vendor preset: disabled)
Active: active (running) since Tue 2021-02-23 14:40:21 IST; 1h 35min ago
Docs: man:haproxy(1)
file:/usr/share/doc/haproxy/configuration.txt.gz
Process: 164765 ExecStart=/usr/sbin/haproxy -W -f $CONFIG -p $PIDFILE $EXTRAOPTS (code=exited, status=0/SUCCESS)
Process: 164754 ExecStartPre=/usr/sbin/haproxy -f $CONFIG -c -q $EXTRAOPTS (code=exited, status=0/SUCCESS)
Main PID: 164775 (haproxy)
Tasks: 3 (limit: 23814)
Memory: 24.9M
CGroup: /system.slice/haproxy.service
├─164775 /usr/sbin/haproxy -W -f /etc/haproxy/haproxy.cfg -p /run/haproxy.pid
└─164776 /usr/sbin/haproxy -W -f /etc/haproxy/haproxy.cfg -p /run/haproxy.pid
Feb 23 14:40:21 localhost.localdomain haproxy[164765]: [NOTICE] 053/144021 (164775) : New worker #1 (164776) forked
Feb 23 14:40:21 localhost.localdomain systemd[1]: Started HAProxy Load Balancer.
Open a browser and navigate to the HAProxy load balancer:
https://<HostName or IP Address>:443
Accept the certificate and verify its details to ensure the integration is complete.
Appendix
This section provides detailed instructions and procedures for:
Install HAProxy with custom OpenSSL
To install HAProxy with custom OpenSSL:
Install required packages:
apt install make gcc perl libpcre3-dev zlib1g-dev -y
Download HAProxy source:
wget https://www.haproxy.org/download/1.8/src/haproxy-1.8.8.tar.gz
Extract the source archive:
tar xzf haproxy-1.8.8.tar.gz
Navigate to the extracted directory:
cd haproxy-1.8.8
Compile HAProxy with custom OpenSSL:
make TARGET=generic USE_OPENSSL=1 SSL_INC=/usr/local/ssl/include SSL_LIB=/usr/local/ssl/lib USE_PCRE=1 USE_ZLIB=1 USE_GETADDRINFO=1 USE_REGPARM=1 USE_PCRE_JIT=1 USE_NS=1
Ensure the SSL_INC and SSL_LIB paths match the location where Custom OpenSSL is installed.
Install HAProxy:
make install
Copy the HAProxy binary:
cp /usr/local/sbin/haproxy /usr/sbin/haproxy
Check that HAProxy is using the desired Custom OpenSSL version:
haproxy -vv
Create the service file /lib/systemd/system/haproxy.service with the following content:
[Unit]
Description=HAProxy Load Balancer
Documentation=man:haproxy(1)
Documentation=file:/usr/share/doc/haproxy/configuration.txt.gz
After=network.target rsyslog.service
[Service]
EnvironmentFile=-/etc/default/haproxy
Environment="CONFIG=/etc/haproxy/haproxy.cfg" "PIDFILE=/run/haproxy.pid"
Environment="LD_LIBRARY_PATH=/usr/local/ssl/lib/"
ExecStartPre=/usr/sbin/haproxy -f $CONFIG -c -q $EXTRAOPTS
ExecStart=/usr/sbin/haproxy -W -f $CONFIG -p $PIDFILE $EXTRAOPTS
ExecReload=/usr/sbin/haproxy -f $CONFIG -c -q $EXTRAOPTS
ExecReload=/bin/kill -USR2 $MAINPID
KillMode=mixed
Restart=always
SuccessExitStatus=143
Type=forking
[Install]
WantedBy=multi-user.target
Ensure the Environment="LD_LIBRARY_PATH" points to the custom OpenSSL library folder.
Create /etc/haproxy/haproxy.cfg with the following content:
global
log /dev/log local0
log /dev/log local1 notice
stats socket /run/haproxy/admin.sock mode 660 level admin expose-fd listeners
stats timeout 30s
user haproxy
group haproxy
daemon
defaults
log global
mode http
option httplog
option dontlognull
Create the haproxy user if it doesn’t already exist:
id -u haproxy &> /dev/null || useradd -s /usr/sbin/nologin -r haproxy
Create the HAProxy directory:
mkdir -p /run/haproxy
Reload the systemd daemon and start the HAProxy service:
systemctl daemon-reload systemctl start haproxy.service
Ensure that the HAProxy service starts successfully. Follow the instructions in the Integrate Luna HSM with HAProxy section to complete the setup.
Configure backend servers for HAProxy
To configure backend servers for HAProxy:
Install Apache server:
apt install httpd -y
Modify your webpage content in the /var/www/html/index.html file as needed.
Start the Apache service:
systemctl start httpd
Configure HAProxy server to run in chroot
To configure the HAProxy server to run in chroot:
This guide assumes the chroot directory is /var/lib/haproxy. If you are using a different directory, adjust the paths accordingly.
Follow the steps in the Integrate Luna HSM with HAProxy section to ensure integration is complete.
Stop the HAProxy service if it is currently running.
systemctl stop haproxy.service
Create the directory for chroot.
mkdir -p /var/lib/haproxy
Create the /usr/safenet directory within the chroot directory.
mkdir -p /var/lib/haproxy/usr/safenet
Mount the existing /usr/safenet directory to the chroot directory.
mount --bind /usr/safenet /var/lib/haproxy/usr/safenet
Create the /etc directory within the chroot directory and copy the Chrystoki.conf file to it.
mkdir /var/lib/haproxy/etc cp /etc/Chrystoki.conf /var/lib/haproxy/etc/
Provide the HAProxy user with the necessary permissions for the Chrystoki.conf file.
setfacl -m u:haproxy:rwx /var/lib/haproxy/etc/Chrystoki.conf
Create the /tmp directory within the chroot directory.
mkdir /var/lib/haproxy/tmp
Mount the existing /tmp directory to the chroot directory.
mount --bind /tmp /var/lib/haproxy/tmp
Add the following line to the global section of the /etc/haproxy/haproxy.cfg file to specify the chroot directory.
chroot /var/lib/haproxy
Reload the system daemon and start the HAProxy service.
systemctl daemon-reload systemctl start haproxy.service
The above mounts are temporary and will be lost after a reboot. To make these mounts persistent, add them to the /etc/fstab file.

