Creating Policies
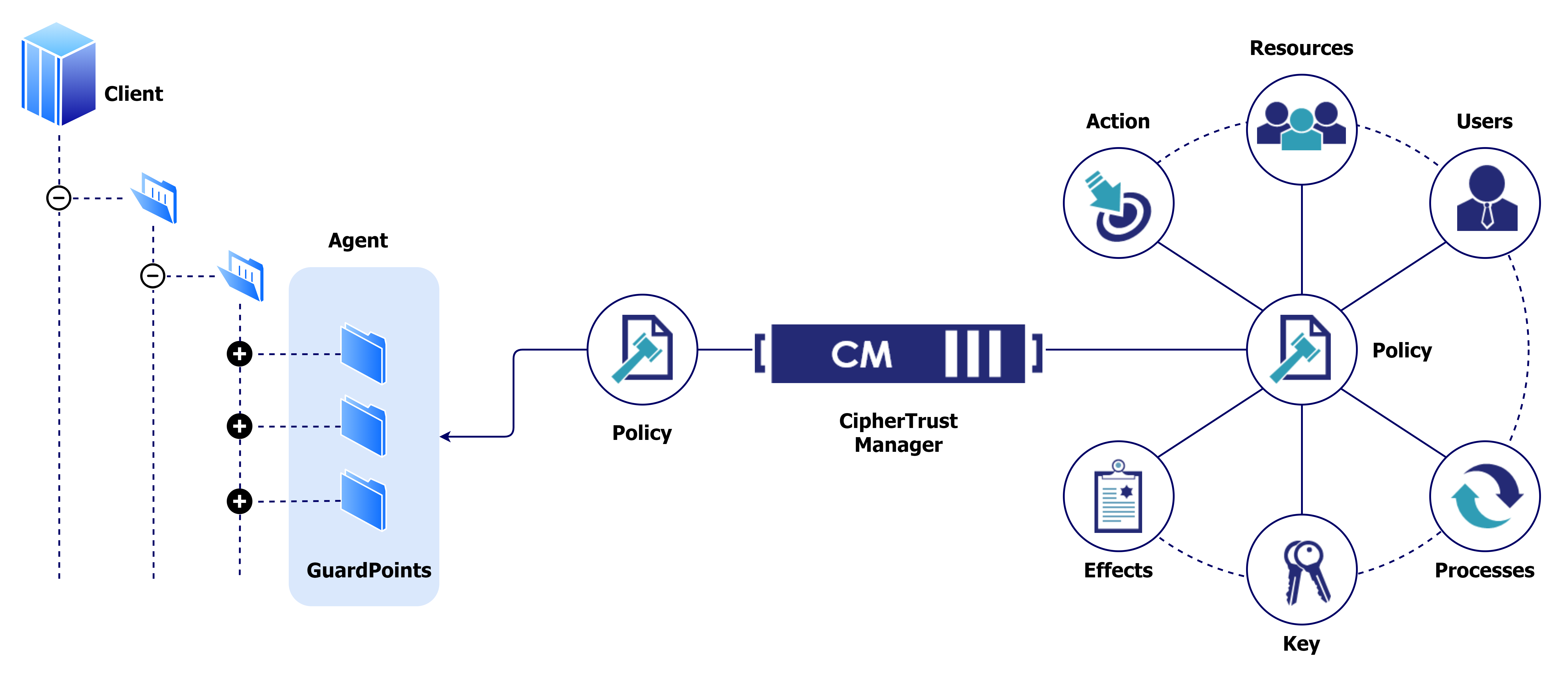
A policy is a collection of rules that govern data access and encryption. Think of a policy as an if-then statement. Policy rules are processed sequentially. If the criteria of rule one are not met, the policy enforcement engine moves on to the second rule and so on.
Policies specify:
Actors: Users, groups, and processes that are permitted/denied access to protected data.
Actions: What actions authorized actors are allowed to perform. For example create/delete, read/write, decrypt, modify permissions, and so on.
Files acted upon: Policy rules may apply to entire directories and mount points, or only to files named in a specific way (for example,
.docxfiles may be encrypted and restricted to read-only access by designated users, while other files may be stored clear and read and written by anyone).
Additionally, every CTE policy specifies one or more encryption keys used to encrypt blocks of file data when applications write them, and decrypt them when they are read.
CTE encryption is transparent to applications. This means that the CTE Agent encrypts blocks of data as they are written, and decrypts data when they are read by authorized users and applications. This architecture separates administration of files from access to the data in them. Backup programs, for example, may be authorized to read files, but not view the data in them. Therefore, data can be backed up and taken offsite while remaining encrypted so that security is not breached.
The following diagram shows policies and how they relate to the GuardPoints, clients, and the CipherTrust Manager.
Before you can create a policy, policy elements should exist on the CipherTrust Manager. This section assumes that you have already created policy elements, as described in Creating Policy Elements.
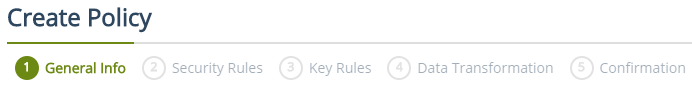
When creating a policy, you can specify security rules, key rules, and data transformation (dataxform) rules that apply to the policy. At least one key or security rule must be added to a policy. Use the Create Policy wizard to create a policy.
Step 1: Specify General Information
To specify general information about policy:
Open the Transparent Encryption application.
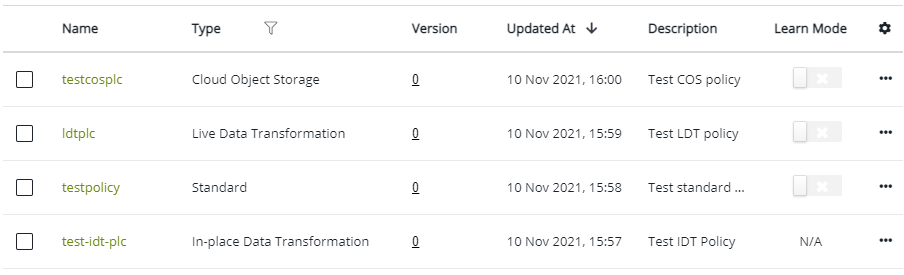
Click Policies. The Policies page shows the list of available policies.
Click Create Policy.
Specify a unique Name for the policy. For example, basic-access-policy or ldt-policy.
The name must start with a character. The maximum length can be 64 characters.
The name can contain alphanumeric characters, underscores (
_), and dashes (-).The name cannot contain the following special characters:
? : ; | ! @ # $ % ^ & * < = > + ( ) { } ~ , \ / [ ] ' "
Select a Policy Type. The options are:
Standard: Access to data is blocked during initial encryption or rekeying of data. This is the default policy type. Refer to Creating Standard GuardPoints for details.
Standard policies are also used for protecting storage arrays. Refer to Creating Standard GuardPoints for Efficient Storage Devices for details.
Live Data Transformation: Encryption and rekeying of data takes place in the background, without disrupting user or application access to that data. The LDT policy is available if you have a valid LDT license.
If you select an LDT policy type, then the first security rule for the policy is created by default. This rule permits key operations on all resources for that policy, without denying user or application access to resources. This allows a rekey operation whenever the encryption key is versioned. This rule is always the first rule in an LDT policy and cannot be edited.
Refer to Enabling Live Data Transformation for more information about LDT.
An LDT policy is needed for creating LDT GuardPoints. Refer to Creating LDT GuardPoints on Clients for details.
Cloud Object Storage: Access to data is blocked during initial encryption or rekeying of data. This policy type is needed for creating GuardPoints for cloud storages. Refer to Creating Cloud Object Storage GuardPoints on Clients for details.
In-place Data Transformation (IDT): Access to data is blocked during encryption or rekeying of data. This policy type is needed for creating GuardPoints for Teradata clusters. Refer to Creating IDT GuardPoints for details.
IDT policies are also used for protecting storage arrays. Refer to Creating IDT GuardPoints for Efficient Storage Devices for details.
(Optional) Turn on the Learn Mode toggle. A warning message is displayed indicating that the policy is in Learn Mode.
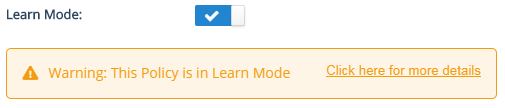
Refer to Learn Mode for details. By default, the toggle is turned off.
Note
Learn Mode is not applicable to In-place Data Transformation policies.
(Optional) Turn on the Restrict Update toggle. This option is used to restrict or allow any changes to the policy. By default, the toggle is turned off. This setting can be changed any time after the policy is created. Refer to Controlling Updates to Policies.
(Optional, applicable to Standard policies) Turn on the Data Transformation toggle. This option is used to create a dataxform policy. By default, the toggle is turned off.
Note
The Data Transformation option is not applicable to LDT, Cloud Object Storage, and In-place Data Transformation policies. For a dataxform policy, the Create Policy wizard shows five steps including the Data Transformation step, as shown below.
Click Next. The Security Rules screen is displayed.
For a standard dataxform policy, a security rule with the Action key_op, the Effect permit,applykey, and Browsing set to Yes is added automatically. Edit or delete the rule, as appropriate. Click the overflow icon ( ) for options.
) for options.
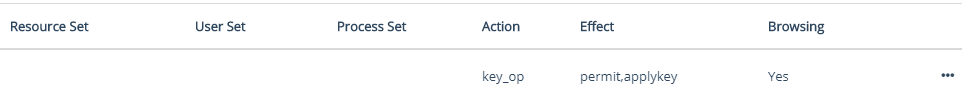
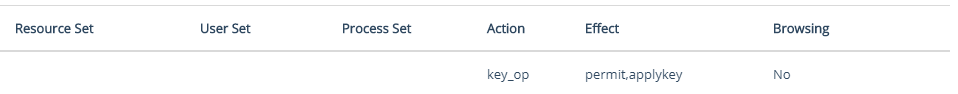
For an LDT policy, the default security rule with the Action key_op, the Effect permit,applykey, and Browsing set to No is added automatically. The rule is read only.
Step 2: Add Security Rules
Click Create Security Rule. The Create Security Rule dialog box is displayed. This dialog box contains the following fields:
Field Description Resource Set (Not applicable to COS policies) Resource set for the rule. User Set User set for the rule. Process Set Process set for the rule. Action Actions for the rule. Refer to Actions for the complete list of supported actions. Effect Effect permission and options for the rule. This is a mandatory field. Allow Browsing (Not applicable to COS policies) Whether browsing of directories under the GuardPoint down to the resources in the rule is allowed. (Optional, not applicable to COS policies) Select a Resource Set.
Click Select next to the Resource Set field. The list of available resource sets is displayed.
Optionally, you can add a new resource set by clicking Create Resource Set. Walk through the Create Resource Set wizard, as described in Creating Resource Sets. The newly created resource set appears in the resource sets list.
Select a resource set.
(Optional) Select Exclude Rule to exclude the resource set from the policy. The security rule does not apply to this resource set.
Click Select. The selected resource set appears in the Resource Set field.
(Optional) Select a User Set.
Click Select next to the User Set field. The list of available user sets is displayed.
Optionally, you can add a new user set by clicking Create User Set. Walk through the Create User Set wizard, as described in Creating User Sets. The newly created user set appears in the user sets list.
Select a user set.
Click Select. The selected user set appears in the User Set field.
(Optional) Select a Process Set.
Click Select next to the Process Set field. The list of available process sets is displayed.
Optionally, you can add a new process set by clicking Create Process Set. Walk through the Create Process Set wizard, as described in Creating Process Sets. The newly created process set appears in the process sets list.
Select a process set.
(Optional) Select Exclude Rule to exclude the process set from the policy. The security rule does not apply to this process set.
Click Select. The selected process set appears in the Process Set field.
(Optional) Select an Action. Specify the type of file and directory action allowed on a GuardPoint. To specify all actions, leave the Action field blank.
Click Select next to the Action field. By default, the Select Action(s) dialog box displays basic actions.
To view advanced actions, expand Advanced Options by clicking +. The Select Action(s) dialog box provides the names and brief description of actions. Refer to Actions for the complete list of supported actions.
Select the desired actions.
Note
• For a data transformation policy, the action
key_opis selected automatically. If you selectkey_op, then you must add a data transformation rule.
• For an IDT policy, the allowed actions areread,write, andall_ops.Click Select. The selected actions appear in the Action field.
Select an Effect. Effect is the action that occurs when the attempted access matches all the criteria in the rule. This is a mandatory field. The default action is Deny.
Click Select next to the Effect field. The Select Effect dialog box displays the available Effect Permissions and Effect Options.
From the Effect Permissions list, select a permission. An effect must have a permission. The available options are:
Deny: Denies the access attempts to a resource. For example, you can specify an effect that denies any attempts to access a resource.
Permit: Allows the access attempt to a resource. For example, you can specify an effect that allows writing to a resource.
From the Effect Options list, select appropriate options. The available options are:
ApplyKey: Applies an encryption key to data in a GuardPoint. When applied, data copied to the GuardPoint is encrypted with the key specified on the Create Key Rule screen and data that is accessed in the GuardPoint is decrypted using the same key. It allows the access attempt to the resource. For example, you can specify an effect that allows writing to a directory.
Note
If you select ApplyKey, you must also specify the key rules to apply for encrypting and decrypting the resources. Refer to Step 3: Add Key Rules for details.
Audit: Creates a message log entry for each qualifying event. It records what, when, and who is accessing the information.
Click Select. The selected effects appear in the Effect field.
(Optional, not applicable to COS policies) Specify whether to Allow Browsing the directories under the GuardPoint down to the resources in the rule.
By default, the Allow Browsing toggle is on. Users that match the criteria set by the security rule can access the directories between the GuardPoint and the resource. If you define a resource, then that resource should exist in the GuardPoint. The files in these directories can be listed like any file in a browser, but they cannot be modified, copied, or deleted.
To prevent users from browsing the directories under the GuardPoint, turn off the Allow Browsing toggle.
Click Add. The newly created security rule appears in the list of security rules.
Similarly, you can add multiple security rules to the policy by clicking Create Security Rule. To delete a security rule, click Delete next to the rule.
Note
A security rule with the
ApplyKeyEffect must be supported by at least one key rule. Refer to Step 3: Add Key Rules.Click Next. The Key Rules screen is displayed.
Step 3: Add Key Rules
If you added a security rule with the Effect ApplyKey on the Security Rule screen, then you must add at least one key rule.
Note
For the IDT policies, only one key rule can be specified. So, you only need to specify the Current Key and Transformation Key. You can add a clear_key, XTS, CBC, or CBC_CS1 key as the Current Key. After adding the key, click Next. Verify the policy details on the Confirmation screen. Refer to Step 5: Confirm Details.
To add a key rule:
Click Create Key Rule. The Create Key Rule dialog box is displayed.
(Optional, not applicable to COS policies) Select a Resource Set.
Click Select next to the Resource Set field. The list of available resource sets is displayed.
Optionally, you can add a new resource set by clicking Create Resource Set. The newly created resource set will appear in the resource sets list.
Select a resource set.
Click Select. The selected resource set appears in the Resource Set field.
Select a Key Name. This is a mandatory field. For LDT and Data Transformation policies, the field name is Current Key Name instead of Key Name.
Click Select next to the field. The Select Key dialog box shows the list of available keys. Optionally, you can create a new CBC/CBC-CS1 or XTS key on this dialog box.
To create a CBC or CBC CS1 key
Click Create a New Key. The Key created will be AES 256 section is displayed on the dialog box below.
Specify an optional Name for the key.
Select the Encryption Mode. The default mode is CBC.
Click Create. The newly created key will appear in the keys list.
Alternatively, encryption keys for CTE can be created on the Keys page of the CipherTrust Manager GUI. Refer to Creating a New Key for details.
However, the ESG keys cannot be created on the Keys page of the CipherTrust Manager GUI. They must be created on the Select Key dialog box only, as described below. All the required permissions and properties are automatically applied to the key.
To create an XTS key
Turn on the ESG compatible keys toggle. This toggle filters and shows only the ESG-compatible keys.
Click Create a New Key. The Key created will be AES 256 with XTS as encryption mode section is displayed on the page below.
Specify an optional Name for the key.
Click Create. The newly created XTS key will appear in the keys list.
Note
When creating the ESG keys using the CipherTrust Manager CLI or the API:
• Specify the same value for theidanduuidfields in the UUID format. The UUID can be generated using the tools available online.
• Set thextsflag totrue.
• Set the key as exportable, that is, setunexportabletofalse.
• Share the key with the CTE Users and Key Users groups with theread_keyandexport_keypermissions.Refer to the following sample for creating an ESG key:
{ "name": "CTEESGKey", "algorithm": "aes", "size": 256, "undeletable": true, "unexportable": false, "meta": { "ownerId": "local|59ba6797-e5a6-4427-b11c-a5534b5a975e", "permissions": { "ExportKey": [ "CTE Clients", "Key Users" ], "ReadKey": [ "CTE Clients", "Key Users" ] }, "cte": { "persistent_on_client": true, "encryption_mode": "XTS", "cte_versioned": false } }, "xts": true, "id": "95cc7868-89bf-492b-b868-bbb884a9b379", "uuid": "95cc7868-89bf-492b-b868-bbb884a9b379" }Note
When an XTS key is created, an additional tweak key (
<key-name>_xts) is generated with the original key. Make sure that both the original and the tweak keys are part of the Key Users and CTE Clients groups with the read key (read_key) and export key (export_key) permissions.Select the desired key.
Note
The Select Key page provides options to create, filter, and select ESG compatible keys. These are AES-256 keys with XTS as the encryption mode. An ESG compatible key must be used when creating a policy for CTE-Efficient Storage devices. Refer to Creating GuardPoints for Efficient Storage Devices for details.
Click Select. The selected key appears in the Key Name / Current Key Name field.
The next two steps are specific to LDT policies.
(Applicable to LDT policies) Select a Transformation Key Name. This is a mandatory field.
Click Select next to the field. The list of available keys is displayed.
Optionally, you can create a new key by clicking Create a New Key. Optionally, specify a Name for the key and click Create. The newly created key will appear in the keys list.
Alternatively, encryption keys for CTE can be created on the Keys page of the CipherTrust Manager GUI. Refer to Creating a New Key for details.
Select the desired key.
Click Select. The selected key appears in the Transformation Key Name field.
Click Add. The newly created key rule appears in the list of key rules.
Similarly, you can add multiple key rules to the policy by clicking Create Key Rule. To delete a key rule, click Delete next to the rule.
Click Next.
For Live Data Transformation, Cloud Object Storage, and In-place Data Transformation policies, the Confirmation screen is displayed. Verify policy details, as described in Step 5: Confirm Details.
For Standard policies, the following screen is displayed:
Data Transformation: If you selected the Data Transformation check box on the General Info screen of the Create Policy wizard. Add data transformation rules, as described in Step 4: Add Data Transformation Rules.
Confirmation: If you cleared the Data Transformation check box. Verify policy details, as described in Step 5: Confirm Details.
Step 4: Add Data Transformation Rules
This step is applicable to Standard policies if you selected the Data Transformation check box on the General Info screen of the Create Policy wizard.
Click Create Data Transformation Rule. The Create Data Transformation Rule dialog box is displayed.
(Optional) Select a Resource Set.
Click Select next to the Resource Set field. The list of available resource sets is displayed.
Optionally, you can add a new resource set by clicking Create Resource Set. The newly created resource set will appear in the resource sets list.
Select a resource set.
Click Select. The selected resource set appears in the Resource Set field.
Select the Transformation Key Name. This is a mandatory field.
Click Select next to the Transformation Key Name field. The Select Key dialog box shows the list of available keys. Optionally, you can create a new CBC/CBC-CS1 or XTS key on this dialog box.
To create a CBC or CBC CS1 key
Click Create a New Key. The Key created will be AES 256 section is displayed on the page below.
Specify an optional Name for the key.
Select the Encryption Mode. The default mode is CBC.
Click Create. The newly created key will appear in the keys list.
Alternatively, encryption keys for CTE can be created on the Keys page of the CipherTrust Manager GUI. Refer to Creating a New Key for details.
However, the ESG keys cannot be created on the Keys page of the CipherTrust Manager GUI. They must be created on the Select Key dialog box only, as described below. All the required permissions and properties are automatically applied to the key.
To create an XTS key
Turn on the ESG compatible keys toggle. This toggle filters and shows only the ESG-compatible keys.
Click Create a New Key. The Key created will be AES 256 with XTS as encryption mode section is displayed on the dialog box below.
Specify an optional Name for the key.
Click Create. The newly created XTS key will appear in the keys list.
Note
When creating the ESG keys using the CipherTrust Manager CLI or the API:
• Specify the same value for theidanduuidfields in the UUID format. The UUID can be generated using the tools available online.
• Set thextsflag totrue.
• Set the key as exportable, that is, setunexportabletofalse.
• Share the key with the CTE Users and Key Users groups with theread_keyandexport_keypermissions.Refer to the following sample for creating an ESG key:
{ "name": "CTEESGKey", "algorithm": "aes", "size": 256, "undeletable": true, "unexportable": false, "meta": { "ownerId": "local|59ba6797-e5a6-4427-b11c-a5534b5a975e", "permissions": { "ExportKey": [ "CTE Clients", "Key Users" ], "ReadKey": [ "CTE Clients", "Key Users" ] }, "cte": { "persistent_on_client": true, "encryption_mode": "XTS", "cte_versioned": false } }, "xts": true, "id": "95cc7868-89bf-492b-b868-bbb884a9b379", "uuid": "95cc7868-89bf-492b-b868-bbb884a9b379" }Note
When an XTS key is created, an additional tweak key (
<key-name>_xts) is generated with the original key. Make sure that both the original and the tweak keys are part of the Key Users and CTE Clients groups with the read key (read_key) and export key (export_key) permissions.Select the desired key.
Note
The Select Key page provides options to create, filter, and select ESG compatible keys. These are AES-256 keys with XTS as the encryption mode. An ESG compatible key must be used when creating a policy for CTE-Efficient Storage devices. Refer to Creating GuardPoints for Efficient Storage Devices for details.
Click Select. The selected key appears in the Transformation Key field.
Click Add. The newly created data transformation rule appears in the list of rules.
Similarly, you can add multiple rules to the policy by clicking Create Data Transformation Rule. To delete a rule, click Delete next to the rule.
Click Next. The Confirmation screen is displayed.
Step 5: Confirm Details
Verify the policy details. The Confirmation screen displays general information about the policy and details of the security and key rules added to the policy.
If the details are incorrect or you want to modify them, click Back and update the details.
Click Save.
The newly created policy appears in the policies list on the Policies page. Similarly, add as many policies as required. A sample list of policies is shown below:
Creating a New Key
When creating a key rule for a policy, you can either select an existing key or create a new key. The list of available keys is displayed on the Select Key dialog box. The new keys that you create on this dialog box appear under the keys list.
Alternatively, encryption keys for CTE can be created on the Keys page of the CipherTrust Manager GUI, as described below. However, the ESG-compatible keys must be created on the Select Key dialog box only.
Note
The ESG keys cannot be created on the Keys page of the CipherTrust Manager GUI.
Note
The CTE keys must be:
• AES-128, AES-256, ARIA-128, or ARIA-256
• Shared with the CTE Clients group
• Set as exportable
Only the clients that support the CBC CS1 encryption mode can have GuardPoints that use a policy with a CBC CS1 key.
To create a new key:
In the top left corner, click the App Switcher icon. The Products page is displayed.
In the left pane, click Keys. The Keys page is displayed.
Click Add Key.
Specify the Key Name.
Select the Algorithm from the drop-down list. The default algorithm is
AES. CTE supportsAESandARIAalgorithms.Select the key Size from the drop-down list. The default size is
256.(Optional) Under Key Properties, select XTS/CBC CS1 if you want to create a key for enhanced encryption mode.
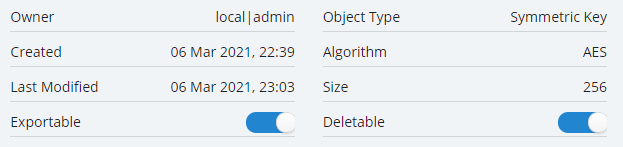
Click Add Key to create the key. The edit view of the key is displayed.
For an enhanced encryption key, a set of two keys is created with names
<key-name>and<key-name>_xts.In the mini detail view, turn on the Exportable toggle. This makes sure the key is displayed in the keys list when you add the key rule to the policy.
Specify whether the key can be deleted. To make the key deletable, turn on the Deletable toggle. By default, the Deletable toggle is turned off, that is, the key cannot be deleted.
Expand the KEY ACCESS section:
On the General tab:
Make sure that the Show All Groups toggle is enabled. It displays the list of available groups.
In the Search groups box, type CTE Clients to filter the groups. The CTE Clients group is displayed.
Select the All check box. All the available permissions are selected.
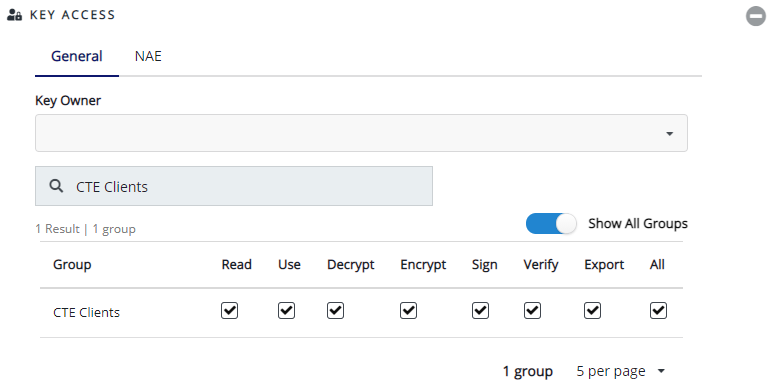
Click Update.
Click the CTE tab. You need to scroll down the page.
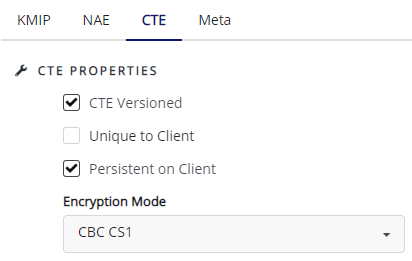
Specify the CTE properties:
CTE Versioned: Specify whether the key is versioned.
For Standard, COS, and IDT policies, clear the CTE Versioned check box. This makes sure that the key is displayed in the keys list when you add the key rule to the policy.
For LDT policies, make sure that the CTE Versioned check box is selected.
Persistent on Client: Specify whether the key is stored in persistent memory on the client.
When the check box is selected, the key is downloaded and stored (in an encrypted form) in persistent memory on the client. This can be used in the event that a connection to the CipherTrust Manager is unreliable.
When the check box is left clear, the key is only stored on disk inside the CipherTrust Manager. When required, the key is downloaded to the CTE client but only cached in memory. Every time the key is needed, the client retrieves it from the CipherTrust Manager.
Encryption Mode: Encryption mode of the key. The options are:
CBC CS1XTSCBC
Note
If you selected the XTS/CBC CS1 check box when creating the key, you must select either
CBC CS1orXTSas the encryption mode. Encryption using theXTSandCBC CS1keys is known as enhanced encryption. Refer to the CTE Agent Advanced Configuration and Integration Guide specific to your platform for details.
Properties of a sample CTE key are shown below:
To set Group Permissions for accessing this key, specify the settings on the General tab under the KEY ACCESS section.
Click Update.
The key is updated for use with CTE.
Note
• Only CTE Administrators (users of the CTE Admins group) can delete the CTE keys.
• An in-use CTE key cannot be deleted. Before you delete a CTE key, make sure that no key rule is using the key.

