Configuration Elements
Configuration Elements
The pfmigrate utility migrates the following ProtectFile configuration elements:
-
Keys
-
Clients
-
Access policies
-
Access policy groups
-
NAS shares
-
Clusters
-
Encryption rules
The utility creates equivalent CTE or CTE-U v10.x configuration elements and sets up the necessary linkage between them.
Production Policies
In this section we describe all of the configuration elements on CM used by ProtectFile and CTE-Userspace (9.x and lower) and how they would be mapped to their equivalent configuration elements for CTE-U v10.x.
Policies
To migrate ProtectFile data, you will use two different policies:
-
Data Transform Policy (PF to CTE migration only)
-
Production Policy
Keys
ProtectFile uses AES-256 keys only. The pfmigrate utility creates the required CTE keys as AES-256 with CBC encryption mode.
The pfmigrate utility creates new keys and renames them with a CTE prefix.
Example:
-
ProtectFile Key name: ClassicKSPFKey1
-
CTE Key name: CTE_ClassicKSPFKey1
Client Mapping
The CTE configuration elements consist of the client names and their properties. Navigating to the Transparent Encryption section on CipherTrust Manager presents the list of clients and their properties. Use the following table to map the properties of the ProtectFile clients to CTE or CTE-U v10.x clients:
| ProtectFile Clients | CTE/CTE-U v10.x Clients | Note |
|---|---|---|
| Client name | Client name | |
| IP or host name | N/A | CTE-U uses only the client names |
| OS Type | OS Type | Populated during registration |
| N/A | Kernel Version | Populated during registration |
| Client Profile | Client Profile | |
| Updated | N/A | Last synchronize time with the client |
| N/A | Status | Health status |
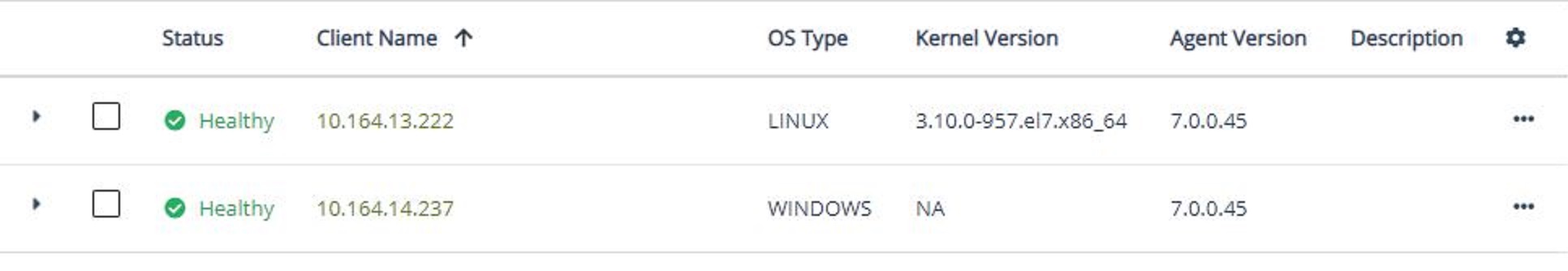
The Transparent Encryption clients section in CipherTrust Manager shows the client entries as in the screenshot below:
Network Shares
ProtectFile configures network shares explicitly and allows their grouping in network share profiles. You can apply encryption rules at the share level. All participating clients are added to the same network share profile.
CTE and CTE-U v10.x define encryption policies, on network share, from within the client. All participating clients are configured in client groups. The pfmigrate utility migrates all of the participating clients from a ProtectFile network share profile and creates a CTE/CTE-U v10.x client group for them.
CIFS network share path migrations are not supported.
Clusters
ProtectFile configures clusters explicitly in its own section on CM. Encryption policies can be applied at the cluster level.
To access the Cluster section:
-
From the products page, click ProtectFile and Transparent Encryption Userspace.
-
Click Clusters in the navigation panel.
Client Profiles
Client profiles are used to group common configuration values for multiple clients in both ProtectFile and CTE. However, ProtectFile client profiles are different from CTE/CTE-U v10.x client profiles, and the pfmigrate utility does not migrate them. We do not describe their mapping here, however, for ProtectFile Linux clients, if their associated client profile has the enable su property set, enable the CTE-U v10.x su_root_no_auth authenticator in the client settings on the CTE-U v10.x client.
Access Policies and Groups
In this section, we discuss the mapping of ProtectFile access policies to CTE/CTE-U v10.x policies.
-
An access policy in ProtectFile consists of a user/group/process and the access allowed to it.
-
An access policy group in ProtectFile is composed of one or more access policies. An access policy group is migrated to a CTE/CTE-U v10.x Standard Policy using the
pfmigrateutility. -
A CTE/CTE-U v10.x standard policy consists of one or more security rules, key rules and data transformation rules (for offline policies).
-
A CTE/CTE-U v10.x security rule describes actions and effects for a specific resource set, user set, process set and time set, basically performing what-who-how-when security operations.
-
A resource in a resource set is a file, a file extension, or sub-folder relative to the &{gp}.
-
A user in a user set can be defined as a user or a user group.
-
A key selection rule consists of a key and optionally a resource set on which the key operates.
-
The data transformation rules section is available only if the policy is set for data transformation. This is defined as having:
-
Action:
key_op -
Effects:
Apply KeyandPermitin the first security rule
-
-
The following table describes how the elements of a ProtectFile access policy group are migrated to CTE/CTE-U v10.x. The
pfmigrateutility does this migration for you.
Access Policies Mapping
| ProtectFile Access Policies | CTE/CTE-U v10.x Security Rules | Note |
|---|---|---|
| Access | See the next table | |
| Name | Name | |
| User name | User Set | |
| User group name | User Set | |
| Process name | Process Set | |
| Fingerprint | Signature Set | The signature set is not migrated by the pfmigrate utility. It must be created manually. |
In CTE/CTE-U v10.x, the access rules are a combination Action and Effects. The following table shows the mapping from ProtectFile access to CTE/CTE-U v10.x as performed by the pfmigrate utility.
Access Rules
| ProtectFile Access | CTE/CTE-U v10.x Action | CTE/CTE-U v10.x Effects |
|---|---|---|
| ReadWrite | all_ops | Permit, Apply Key |
| Write | f_wr | Permit, Apply Key |
| Read | f_rd | Permit, Apply Key |
| ReadWriteCipher | all_ops | Permit |
| ReadCipher | f_rd | Permit |
| NoAccess | all_ops | Deny |
ProtectFile Encryption Rules
An Encryption rule in ProtectFile is a tuple consisting of a path, a key and an access policy group. Additional rule attributes are available (listed below) to fine tune the encryption rule.
The CTE/CTE-U v10.x equivalent is a GuardPoint. Each GuardPoint consists of a policy (as described in the previous section), a guard type, a guard path, and additional GuardPoint attributes.
For every ProtectFile encryption rule, two CTE GuardPoints are created:
-
One for data transformation
-
One for applying the production policy
For CTE-U v10.x, only production policy is created. There is no need for data transformation during migration.
Following are the properties of CTE/CTE-U v10.x GuardPoints:
-
CTE/CTE-U v10.x guard path must be a directory path.
-
CTE/CTE-U v10.x Guard Types can be one of the following:
-
Directory (Auto Guard)
-
Directory (Manual Guard)
-
Raw or Block Device (Auto Guard)
-
Raw or Block Device (Manual Guard)
For migration, only use the Directory(Auto Guard) type.
-
-
A CTE/CTE-U v10.x GuardPoint must be associated with a policy as described above.
-
Regardless of the encryption approach used in the ProtectFile encryption rule, the CTE GuardPoint must be configured with offline data transformation.
The following table depicts how the ProtectFile encryption rule properties are mapped to CTE/CTE-U v10.x GuardPoints by the pfmigrate utility.
Encryption Rules Mapping
| ProtectFile Encryption Rules | CTE/CTE-U v10.x GuardPoints | Note |
|---|---|---|
| Rule name (optional) | N/A | |
| Folder | Folder | The guard type is directory(auto guard). |
ProtectFile encryption rules can use attributes for fine tuning. The following sections describe how they would be mapped to CTE/CTE-U v10.x GuardPoint properties by the pfmigrate utility.
Only the specific rule being migrated goes offline while being migrated. All other rules are available.
File Level Rules
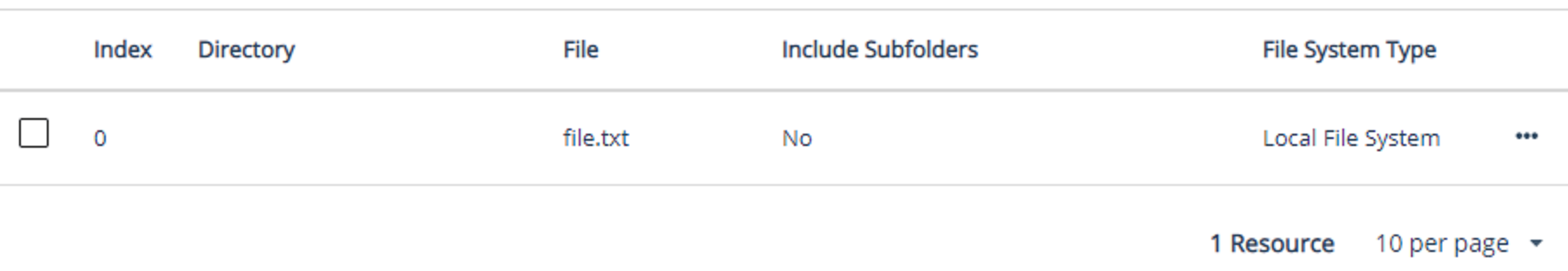
A ProtectFile encryption can be applied on an individual file. To achieve the same in CTE/CTE-U v10.x, create a resource set with the file name to be encrypted relative to the GuardPoint. This resource set is used n the security rule of the policy with the apply_key effect enabled. The following screenshot provides an example of the resource set:
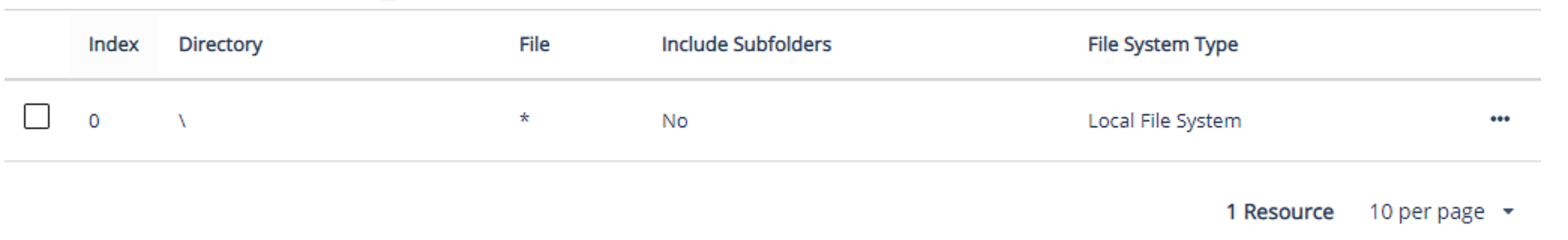
Non Recursive Rules
A ProtectFile encryption rule can be applied to a folder non recursively. To achieve the same in CTE/CTE-U v10.x, create a resource set with the ‘Include Subfolders’ property unchecked. This resource set is used in the security rule of the policy with the apply_key effect enabled. The following screenshot provides an example of the resource set:
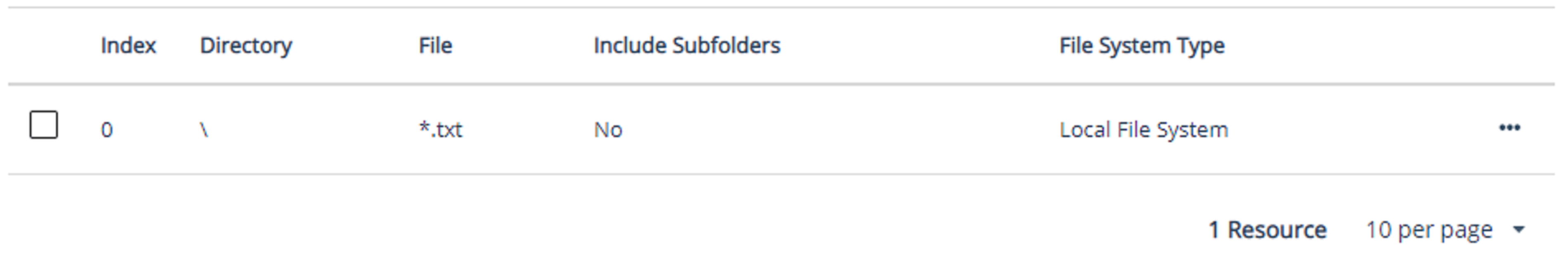
Include File Extension
A ProtectFile encryption rule can be applied only to selected file extensions. To achieve the same in CTE/CTE-U v10.x, create a resource set with the *.ext in the File property, where ext is the extension. This resource set is used in the security rule of the policy with the apply_key effect enabled. The following screenshot provides an example:
Access Only
An encryption rule in ProtectFile can bypass encryption and only enforce access. To achieve this in CTE/CTE-U v10.x, the GuardPoint policy cannot have a key rule. Choose the following:
Action: all_ops
Effect: permit, audit
Resources Names Conversion During Migration of PF Configuration to CTE/CTE-U v10.x Configuration
| ProtectFile Encryption Resource | CTE/CTE-U v10.x Resource type | Migrated resource naming convention |
|---|---|---|
| Access Policy |
Access policy becomes UserSet or ProcessSet depending upon the type of PF access policy:
|
<pf_access_policy_name> |
| <pf_access_policy_name> | ||
| Access Policy Group |
Access policy group becomes two CTE policies: one for initial data transformation and the other for production:
Data transformation policy is for the initial migration of PF encrypted data to CTE encryption format. Once data is migrated, Production policy must be applied. NOTE: For CTE-U v10.x, the access policy group becomes one production policy. |
transform_<pf_rule_name> _<pf_access_policy_group_name> _CTE<pf_key_name> |
| <pf_rule_name> _<pf_access_policy_group_name> _CTE<pf_key_name> |
||
|
Client |
CTE Client |
<pf_client_name> |
| Client Profiles | CTE has profiles similar to ${fuse} | PFMigrate utility is not migrating profiles. You MUST create CTE/CTE-U profiles manually. |
| Clusters | ClientGroup | <pf_cluster_name> |
| Encryption Rules |
GuardPoints GuardPoints are created corresponding to all PF encryption rules. |
GuardPoints are associated with CTE/CTE-U clients. Verify these GuardPoints. |
|
Resource Set Resource sets are conditionally created only if PF encryption rules have additional qualifiers to identify files.
For example, include or exclude extensions or folders, non-recursive rules etc. In general, if rules do not have qualifiers, then only GuardPoints are created. |
Resource set (if created) For Local rule: <pf_client_name>_<pf_rule_name> For NAS share rule: <pf_share_name>_<pf_rule_name> For Cluster rule: <pf_cluster_name>_<pf_rule_name> |
|
| Key | CTE Key | CTE_<pf_key_name> |
| NAS Share | ClientGroup | <pf_share_name> |
Caveats for Naming
ProtectFile name constraints are different from CTE/CTE-U v10.x constraints. The pfmigrate utility takes proactive actions while creating corresponding names for the CTE/CTE-U v10.x migration.
Client/Host Names
CTE/CTE-U v10.x in CM uses the same name as the PF names for all cases, except when the name contains special characters.
CTE/CTE-U v10.x Client/Host names can begin with an alphabetic or a numeric characters. It can include a period or a colon. Additionally, use only lower case letters for client names.
Acceptable characters:
Numbers, period, underscore, colon. For example:
-
myserver_1.1.1.1
-
1.1.1.1_myserver
-
pfserver
-
testserver_1
-
server_a.b.com
-
pfserver:north_wing
Unacceptable characters
Names with spaces are not allowed.
| ProtectFile Name | CTE/CTE-U v10.x Migrated Name |
|---|---|
| my pfserver | pf_modified_my_pfserver |
User Set, Process Set, and Resource Set Names
Only alphanumeric and underscore allowed. All other characters are considered special characters including a period.
| ProtectFile Name | CTE/CTE-U v10.x Migrated Name | Reason |
|---|---|---|
| User set name | PF_Modified_User_set_name | spaces |
| Process.set | PF_Modified_process_set | period |
| 1Resourceset | PF_Modified_1resourceset | started with a number |
| Resource=set | PF_Modified_resource_set | special char |
| MyUser_1 | MyUser_1 | no change needed |
| ProcessSet | ProcessSet | no change needed |
Conflicting Converted Names
If CM contains conflicting converted names, then the pfmigrate utility appends the “_count” string.
| PF Name | CTE/CTE-U v10.x Migrated Name |
|---|---|
| resource=set | PF_Modified_resource_set |
| resource@set | PF_Modified_resource_set _1 |
| resource#set | PF_Modified_resource_set_2 |
All of the names are modified to PF_Modified_resource_set. They are appended with ’_n’ (where ‘_n’ is a sequential number) to differentiate them from a previous name.

