Migration Examples
Migration of Local policies
-
First step to migrating the clients from ProtectFile to CTE or CTE-U v10.x is to use --create / -c option. This creates a sample file.
./pfmigrate -cResults
Flag: --create or -c The option fetches PF clients and shares from ${cm}, and creates input files for the migration. Enter IP address of the CipherTrust Manager from which you are importing ${fuse} data: 192.168.0.5 Enter the port of the CipherTrust Manager from which you are importing ${fuse} data (Default 443): Enter Web Server Certificate Fingerprint of the CipherTrust Manager from which you are importing ${fuse} data: 8FBFD7AD81E468E678B05E2C5CFDC1 07A00BCCD63B 91EEB56D967D29F3A0642 Enter username of the CipherTrust Manager which is part of ${fuse} Admins and ${cteu} Admins group: admin Enter password of the CipherTrust Manager: Enter domain of the CipherTrust Manager (optional):The sample input files are created. Customize the files before running the utility.
-
Run the utility with the
--dryrun / -doption. This checks if all of the clients can be migrated to CTE/CTE-U v10.x../pfmigrate -d -p cte-uResults
Flag: --dryrun or -d The 'dryrun' flag provides a preview of the migration on a given input file. Enter IP address of the CipherTrust Manager from which you are importing ${fuse} data: 192.168.0.5 Enter the port of the CipherTrust Manager from which you are importing ${fuse} data (Default 443): Enter Web Server Certificate Fingerprint of the CipherTrust Manager from which you are importing ${fuse} data: 8FBFD7AD81E468E678B05E2C5CFDC1 07A00BCCD63B 91EEB56D967D29F3A0642 Enter username of the CipherTrust Manager which is part of ${fuse} Admins and ${cteu} Admins group: admin Enter password of the CipherTrust Manager: Enter domain of the CipherTrust Manager (optional): Do you wish to migrate Network Shares configured with ${fuse} linux clients? (Y/N): N Is the source CM, where you are importing ${fuse} data, different from the target server CM where you want to create CTE-UserSpace endpoints? (Y/N): NResponse
Reading the input file pfClientinfo.json The number of ${fuse} Clients in the input file: 8 . Migration Finished Successfully! ------------SUMMARY------------- Number of PF Clients: 8 Number of failed CTE UserSpace Clients: 0 Number of successfully migrated CTE UserSpace Clients: 8 Please check logs for details ...This creates a Dry Run Report log file too. Note that in the above example, network shares were not transformed.
-
After DryRun mode is successful, you need to run the utility in normal mode. Running in normal mode does not require defining any options.
./pfmigrate -p cte-uResults
You have opted to run the utility in normal mode. We recommended to perform a dryrun on a your input file before doing actual migration. Enter 'YES' if want to continue in running the utility in the normal mode? Enter IP address of the CipherTrust Manager from which you are importing ${fuse} data: 192.168.0.5 Enter the port of the CipherTrust Manager from which you are importing ${fuse} data (Default 443): Enter Web Server Certificate Fingerprint of the CipherTrust Manager from which you are importing ${fuse} data: 8FBFD7AD81E468E678B05E2C5CFDC1 07A00BCCD63B 91EEB56D967D29F3A0642 Enter username of the CipherTrust Manager which is part of ${fuse} Admins and ${cteu} Admins group: admin Enter password of the CipherTrust Manager: Enter domain of the CipherTrust Manager (optional): Do you wish to migrate Network Shares configured with ${fuse} linux clients? (Y/N): N Is the source CM, you are importing ${fuse} data, different from the target server CM where you want to create CTE UserSpace endpoints? (Y/N): NResponse
Reading the input file pfClientinfo.json The number of ${fuse} Clients in the input file: 8 . Migration Finished Successfully! ------------SUMMARY------------- Number of PF Clients: 8 Number of failed CTE UserSpace Clients: 0 Number of successfully migrated CTE UserSpace Clients: 8 Please check logs for details ... -
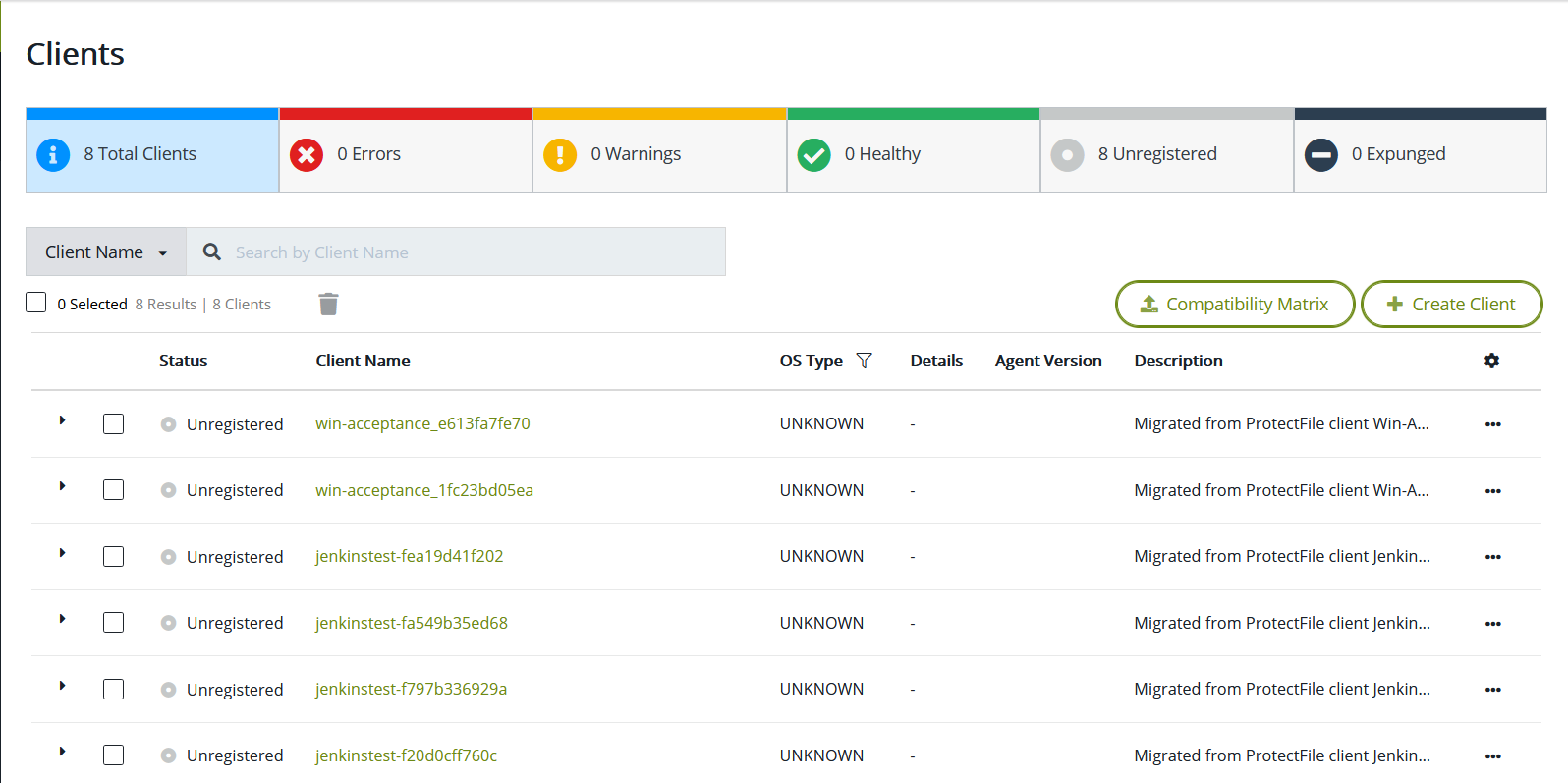
You can now see the clients in CTE-U in CipherTrust Manager:
Migration of NAS policies
Similar to the previous method, you need to follow the steps above and creating, running a dryrun and then running in normal mode.
-
When you use --create/ -c mode, then apart from the
pfClientInfo.jsonfile, amapping.jsonalso must be created. This is the map file for PF clients and the NAS servers associated with it. If there is any network share that you do not want to migrate, then you need to alter the file.cat mapping.jsonResults
[ { "name": "JenkinsTest-Of205fcOc07f", ''id'': "c97c2de3-d830-4c0a-bla7-0615d48c2f38'', "ipHostname": "NOIENC1PFL-VS10", "isBootstrapped": true }, { "name": "Win-Acceptance_lfc23bd05ea", ''id'': "37d32744-f665-4276-878b-d257cc404a95'', "ipHostname": "N0IENC1PFW-afc2", "isBootstrapped": true } ] -
To migrate NAS polices from PF to CTE UserSpace, add the clients to the
pfClientInfo.jsonfile. If any NAS servers are described inmapping.jsonbut the client is not defined inpfClientInfo.json,then the NAS policies will not migrate for those servers. These two files are tightly coupled with each other../pfmigrate -d -p cte-uResults
Flag: --dryrun or -d The 'dryrun' flag provides a preview of the actual migration on a given input file. Enter IP address of the CipherTrust Manager from which you are importing ${fuse} data: 192.168.0.5 Enter the port of the CipherTrust Manager from which you are importing ${fuse} data (Default 443): Enter Web Server Certificate Fingerprint of the CipherTrust Manager from which you are importing ${fuse} data: 8FBFD7AD81E468E678B05E2C5CFDC1 07A00BCCD63B 91EEB56D967D29F3A0642 Enter username of the CipherTrust Manager which is part of ${fuse} Admins and ${cteu} Admins group: admin Enter password of the CipherTrust Manager: Enter domain of the CipherTrust Manager (optional): Do you wish to migrate Network Shares configured with ${fuse} linux clients? (Y/N): N Failed while fetching and parsing PF share to mount point mapping file ERROR: empty ShareName/MountPoint in mapping file Migration Failed!, check logs for details ...By default, the MountPoint parameter is empty. You must fill in the mount points for all of the network shares that you wish to migrate.
./pfmigrate -d -p cteResults
Flag: --dryrun or -d The 'dryrun' flag provides a preview of the actual migration on a given input file. Enter IP address of the CipherTrust Manager from which you are importing ${fuse} data: 192.168.0.5 Enter the port of the CipherTrust Manager from which you are importing ${fuse} data (Default 443): Enter Web Server Certificate Fingerprint of the CipherTrust Manager from which you are importing ${fuse} data: 8FBFD7AD81E468E678B05E2C5CFDC1 07A00BCCD63B 91EEB56D967D29F3A0642 Enter username of the CipherTrust Manager which is part of ${fuse} Admins and ${cteu} Admins group: admin Enter password of the CipherTrust Manager: Enter domain of the CipherTrust Manager (optional): Do you wish to migrate Network Shares configured with ${fuse} linux clients? (Y/N): N Is the source CM, you are importing ${fuse} data, different from the target server CM where you want to create CTE endpoints? (Y/N): N Reading the input file pfClientinfo.json The number of ${fuse} Clients in the input file: 2 . Migration Finished Successfully! ------------SUMMARY------------- Number of PF Clients: 2 Number of failed CTE Clients: 0 Number of successfully migrated CTE Clients: 2 Please check logs for details ... -
After the DryRun mode is successful, you can run it in Normal Mode with the "Y" option when asked for "If you wish to migrate Network Shares..."
./pfmigrate -p cteResults
You have opted to run the utility in normal mode. We recommended to perform a dryrun on a your input file before doing actual migration. Enter 'YES' if want to continue in running the utility in the normal mode? Yes Do you wish to migrate Network Shares configured with ${fuse} linux clients? (Y/N): **Y** Is the source CM, you are importing ${fuse} data, different from the target server CM where you want to create ${cteu} endpoints? (Y/N): N Reading the input file pfClientinfo.json The number of ${fuse} Clients in the input file: 2 . Migration Finished Successfully! ------------SUMMARY------------- Number of PF Clients: 2 Number of failed CTE Clients: 0 Number of successfully migrated CTE} Clients: 2 Please check logs for details ...
Migrating Cluster Policies
Cluster policies are automatically migrated if the clients of the cluster policy are defined in pfClientInfo.json file.
The steps for migration are similar to the steps for local policies.
-
Create
pfClientInfo.jsonfile with cluster clients mentioned in it.cat pfClientinfo.jsonResults
[ { "name": "Clusterl 2Kl9", ''id'': "f3cbb52d-eb08-4481-Beb7-b9b38084b4db", "ipHostname": "WIN-CLSTl .. ' "isBootstrapped": true }, { "name": "Cluster2 2Kl9", ''id'': "b2f9de37-c0e7-45d0-Bf4a-ef4c8060f939", "ipHostname": "WIN-CLST2", "isBootstrapped": true } ] -
Run the utility using DryRun Mode:
cat DryRunReportResults
[DryRun Mode] 2022/01/13 10:56:51 --------------------------DryRun Report------------- [DryRun Mode] 2022/01/13 10:56:51 #################################################### [DryRun Mode] 2022/01/13 10:58:38 The user opted not to migrate network shares. [DryRun Mode] 2022/01/13 10:58:38 ------------SUMMARY--------------------------------- [DryRun Mode] 2022/01/13 10:58:38 Number of PF Clients: 2 [DryRun Mode] 2022/01/13 10:58:38 Number of failed ${cteu} Clients: 0 [DryRun Mode] 2022/01/13 10:58:38 Number of successfully migrated ${cteu} Clients: 2 [DryRun Mode] 2022/01/13 10:58:38 ------------------------------------------------- [DryRun Mode] 2022/01/13 10:58:38 Number of PF Cluster: 1 [DryRun Mode] 2022/01/13 10:58:38 Number of PF Clusters failed to migrate: 0 [DryRun Mode] 2022/01/13 10:58:38 Number of Successfully migrated ${cteu} Clusters: 1 [DryRun Mode] 2022/01/13 10:58:38 #################################################### -
Now run in normal mode:
./pfmigrateResults
You have opted to run the utility in normal mode. We recommended to perform a dryrun on a your input file before doing actual migration. Enter 'YES' if want to continue in running the utility in the normal mode? Yes Enter IP address of the CipherTrust Manager from which you are importing ${fuse} data: 192.168.0.5 Enter the port of the CipherTrust Manager from which you are importing ${fuse} data (Default 443): Enter Web Server Certificate Fingerprint of the CipherTrust Manager from which you are importing ${fuse} data: 8FBFD7AD81E468E678B05E2C5CFDC1 07A00BCCD63B 91EEB56D967D29F3A0642 Enter username of the CipherTrust Manager which is part of ${fuse} Admins and ${cteu} Admins group: admin Enter password of the CipherTrust Manager: Enter domain of the CipherTrust Manager (optional): Do you wish to migrate Network Shares configured with ${fuse} linux clients? (Y/N): N Is the source CM, you are importing ${fuse} data, different from the target server CM where you want to create ${cteu} endpoints? (Y/N): NResponse
Reading the input file pfClientinfo.json The number of ${fuse} Clients in the input file: 8 . Migration Finished Successfully! ------------SUMMARY------------- Number of PF Clients: 8 Number of failed ${cteu} Clients: 0 Number of successfully migrated ${cteu} Clients: 8 Please check logs for details ...

