Provisioning with a Microsoft Azure Dedicated HSM
Microsoft Azure provides a dedicated Hardware Security Module (HSM) service which can be used as a root of trust to a Virtual CipherTrust Manager which is also hosted on Microsoft Azure.
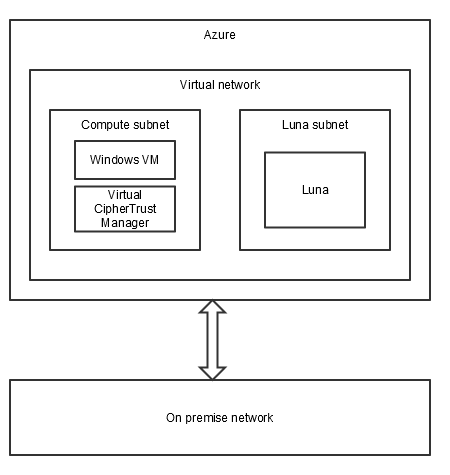
Architecture Overview
To integrate together Virtual CipherTrust Manager and a Dedicated HSM on the Microsoft Azure cloud, you must create and configure the following entities, as shown in the diagram:
Necessary Azure resources, including a virtual network and two subnets within the virtual network.
A dedicated HSM instance within its own subnet, called "Luna" in the diagram.
A Virtual CipherTrust Manager instance in another subnet, called "Compute" in the diagram.
A Windows VM in the "Compute" subnet to host the Luna Client, which can access and configure an HSM partition.
Acquire Permissions to a Dedicated HSM
Contact the Microsoft HSM account HSMrequest@Microsoft.com to request access to a dedicated HSM. Outline your application, the regions you would like HSMs and the volume of HSMs you are looking for. If you work with a Microsoft representative, such as an Account Executive or Cloud Solution Architect for example, then include them in any request.
Once Microsoft is establishes your requirement, they email you a list of documents and schema files that are necessary to deploy a Luna.
Check if permissions have been granted in the Azure console by running:
az feature show --namespace Microsoft.HardwareSecurityModules --name AzureDedicatedHSMThe expected result is that the returned "state" is set to "Registered", as shown in the following example:
{ "id": "/subscriptions/d44a44b4-f4ce-4bb4-b4bc-4444444c444a/providers/Microsoft.Features/providers/Microsoft.HardwareSecurityModules/features/AzureDedicatedHsm", "name": "Microsoft.HardwareSecurityModules/AzureDedicatedHsm", "properties": { "state": "Registered" }, "type": "Microsoft.Features/providers/features" }
Create the Microsoft Azure Resources
We need to create resources on the on Microsoft Azure before provisioning the Luna HSM.
We will be creating the following resources:
- A resource group to place all the resources
- A virtual network (vnet) that will be used for network communications.
- A subnet called "Compute", to later contain the Windows VM lunaclient host and Virtual CipherTrust Manager instances.
- A subnet dedicated to the HSM
- A gateway
Refer to Microsoft Azure documentation for more advanced configuration options.
To create a resource group
Open the left sidebar.
Hover over Resource groups.
A popup opens to the right.
Click on the + Create icon.
This opens a new page to create the resource group
Enter the Subscription name and the Resource group name.
Select an appropriate region from the Region dropdown.
Click on Review + create
Once the validation passes, click on the Create button to create the resource group.
To create a virtual network (vnet)
On your resource group page click on the button Create resources.
Click on the Networking button.
Click on Virtual network.
Select a Subscription and Resource group.
Select a Name and Region for the vnet instance.
Click on Next: IP Addresses >
To create a Compute subnet
Click on the default subnet name and rename it to the "Compute" subnet.
Click on Save.
To create a subnet for the HSM
Click on the + Add subnet button.
Provide a name for the HSM subnet.
Provide a subnet address range and mask.
Click on Add.
Once the subnet is added, click on Next: Security >.
Leave the default option and click on Next: Tags >.
Create an optional tag.
Click on Next: Review + create >.
Once the validation passes, click on the button Create to create the virtual network and the subnets.
To delegate the HSM subnet to the dedicated HSM
Navigate to the Subnets section.
Select the HSM subnet.
A panel to the right opens up
In the right panel, under SUBNET DELEGATION, click on Delegate subnet to a service.
Select Microsoft.HardwareSecurityModules/dedicatedHSMs
Click OK.
To create a gateway
Navigate to the Subnets section.
Click on the + Gateway subnet.
Choose a Name and Subnet address range.
Click on OK.
Deploy the Dedicated Luna HSM in the Subnet
After you have delegated the HSM to the subnet, you have to deploy the HSM.
Copy the example text into a
Deploy-1HSM-toVNET-Params-v1.1.jsonfile. Edit the file to provide your previously configured values for the vnet and HSM subnet.{ "$schema": "https://schema.management.azure.com/schemas/2015-01-01/deploymentTemplate.json", "contentVersion": "1.0.0.0", "parameters": { "ResourcePrefix": { "value": "HSMLuna" }, "ExistingVNetName": { "value": "Luna_kylo_vnet" }, "ExistingHSMSubnetName": { "value": "Luna_kylo_HSM_subnet" }, "HSMResourceName": { "value": "kylo-luna-hsm" } } }Copy the provided
Deploy-1HSM-toVNET-Template-v1.1.jsonfile and do not edit it:Open an Azure powershell terminal.
Click on the Upload/Download button on the terminal
Upload the two files.
Run the following command on the powershell terminal to deploy the dedicated Luna HSM:
New-AzResourceGroupDeployment -ResourceGroupName Luna_kylo_rg -TemplateFile .\Deploy-1HSM-toVNET-Template-v1.1.json -TemplateParameterFile .\Deploy-1HSM-toVNET-Params-v1.1.json -Name HSMdeploy -VerboseIt takes approximately 30 minutes to deploy. You receive a
ProvisioningState: Succeededwhen completeVerify the deployment by running the following commands:
PS> $subid = (Get-AzContext).Subscription.Id PS> $resourceGroupName = "Luna_kylo_rg" PS> $resourceName = "kylo-luna-hsm" PS > Get-AzResource -Resourceid /subscriptions/$subId/resourceGroups/$resourceGroupName/providers/Microsoft.HardwareSecurityModules/dedicatedHSMs/$resourceNameThe expected result looks like:
Name : kylo-luna-hsm ResourceGroupName : Luna_kylo_rg ResourceType : Microsoft.HardwareSecurityModules/dedicatedHSMs Location : westus2 ResourceId : /subscriptions/d44a44b4-f4ce-4bb4-b4bc-4444444c444a/resourceGroups/Luna_kylo_rg/providers/Microsoft.HardwareSecurityModules/dedicatedHSMs/kylo-luna-hsm Tags : Name Value ============ ===== Environment prod resourceType Hsm
Create a Windows instance
A windows instance is necessary to access the Dedicated Luna HSM. From the windows instance, you can SSH into the HSM to perform general HSM configuration, and you can install the Luna client to configure an HSM partition.
Consult Azure Documentation for more detail on provisioning this resource if necessary.
Create a Windows 10 Pro instance on the Compute subnet with a Standard HDD disk. Be sure to use the Resource group you created for the Windows VM, Dedicated HSM, and Virtual CipherTrust Manager.
Get the public IP address of the Windows instance and use it with the Remote Desktop Client (RDP) to access the Windows instance.
Configure the Dedicated Luna HSM
You must perform some configuration on the Dedicated Luna HSM instance to ensure its passwords and policies are secure enough, and to create a partition to act as a root of trust for Virtual CipherTrust Manager.
Consult Luna Network HSM 7.2 Documentation for more information on these commands, if necessary.
To configure the HSM
To find the HSM's IP address, go to the Azure portal, and click on
HSMLuna-ergwpip.Use the IP address to SSH to the HSM from your Windows VM. The default user name is tenantadmin and the default password is PASSWORD.
You are brought into the Luna Shell (LunaSH) utility.
PS > ssh tenantadmin@172.22.1.4 The authenticity of host '172.22.1.4 (172.22.1.4)' can't be established. ECDSA key fingerprint is SHA256:vf96hinpthrML150b4jNGFlaf1oJT0+QQjdfz/B0+yQ. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '172.22.1.4' (ECDSA) to the list of known hosts. tenantadmin@172.22.1.4's password: Last login: Wed Oct 7 19:28:44 2020 Luna Network HSM Command Line Shell v7.2.0-220. Copyright (c) 2018 SafeNet. All rights reserved.Change your password immediately, as prompted.
Run
network showto confirm the IP address for eth0.Warning
Do not change the IP address on eth0. The access to the Luna would be lost.
Run
hsm showto view the current state of the HSM. This command also displays firmware version, software version, and FIPS (Federal Information Process Standards) operating mode.Initialize the HSM with a label. Take care to remember your password.
lunash:>hsm init -label LunaHSM -password mystrongpassword -domain domain1hsm shownow shows the HSM label.Run
hsm loginto login to the HSM. Use the password set in the previous step.If your organization requires FIPS compliance, you need to set the HSM to
FIPS 140-2 Operationmode.To change the FIPS mode and restrict non-FIPS algorithms, set the policy 12 to value 0.
Warning
Setting the HSM to the FIPS mode zeroizes the HSM. All the data on the HSM is lost.
lunash:>hsm changePolicy -policy 12 -value 0
Run
hsm showto confirm theFIPS 140-2 Operationmode is on.
Create the partition using
partition create. Provide a name and a slot number.lunash:>partition create -p luna_part -s 10000Run
partition listto verify the partition was created. You can also get more details about the partition usingpartition show -p <partition_name>
Access and Configure the HSM Partition
Consult Luna Network HSM 7.2 Documentation for more information on lunaCM commands and partition roles, if necessary.
Obtain the Luna Client (version 7.4 or higher) from the Thales Customer Support Portal.
Transfer the client package to the Windows instance.
Install the client with all options and features.
Open powershell in Administrator mode and b to the location where Lunaclient is installed.
Run
luna.exe. No HSMs are currently registered with the client.Use
clientconfig deployto register the HSM with the Luna client and to secure the connection. Provide the HSM's IP address, user and password, and the partition name.lunacm:> clientconfig deploy -server <HSM_IP> -client <Windows_VM_IP> -partition <partition_name> -user tenantadmin -password <password> -verbose Please wait while we set up the connection to the HSM. This may take several minutes...Initialize the partition, providing a label. You are prompted for a password for the Partition Security Officer, and a domain name.
partition init -label <partition_name>Login as the Partition Officer (PO) and initialize the Crypto Officer (CO) with a temporary password.
lunacm:> role login -name po enter password: ******** lunacm:> role init -name co enter new password: ******** re-enter new password: ********Login as the Crypto Officer and change the temporary password.
lunacm:> role login -name co enter password: ******** lunacm:> role changepw -name co enter existing password: ******** enter new password: ******** re-enter new password: ********To verify the partition is active, return to the Luna Shell on the Dedicated HSM instance, and run
partition show -p <partition_name>.
Deploy the Virtual CipherTrust Manager on Azure
Sign in to the Azure or Azure Government portal.
Search for Thales Virtual CipherTrust Manager on Azure Marketplace. You can also use the Azure CLI command
Get-AzVMImage -location eastus2 -PublisherName thalesdiscplusainc1596561677238 -Offer cm_k170v -sku ciphertrust_manager.Note
Older versions of Virtual CipherTrust Manager have been removed from Azure Marketplace.
If you want a version that is unavailable on Azure Marketplace, contact Thales Customer Support for a CipherTrust Manager VHD file.
Upload the VHD file to Azure and create a virtual machine, following Microsoft documentation.
On the Azure or Azure Government portal, select the Virtual CipherTrust Manager image from the Virtual Machines group.
Note
The following steps apply to the Azure recommended 'Resources Manager' deployment model.
Click Create. The first screen of the Create virtual machine page is displayed.

Change the Subscription type if desired.
Select an existing Resource group or enter the name for a new one.
Note
For deployments with Azure Dedicated HSMs, this must be the same resource group as for Luna client host VM and the Dedicated HSM.
Specify the Region of an Azure Datacenter. For example, East US.
Note
For Azure government, this must be one of USGov Arizona, USGov Iowa, USGov Virginia, or USGov Texas.
Enter a Virtual machine name, which is the hostname for the virtual machine your are creating, for example, "mycompany-ciphertrust".
Select the Size for the VM that supports the Minimum Requirements.
Select the SSH Public Key for the Authentication type.
Note
SSH Public Key authentication must be used. Password authentication is not allowed when connecting as the initial user. We support OpenSSH format for the public key, and OpenSSH, PKCS1, or PKCS8 format for the private key. RSA is the supported key algorithm. We recommend RSA 4096, with RSA 2048 as a minimum size for adequate security.
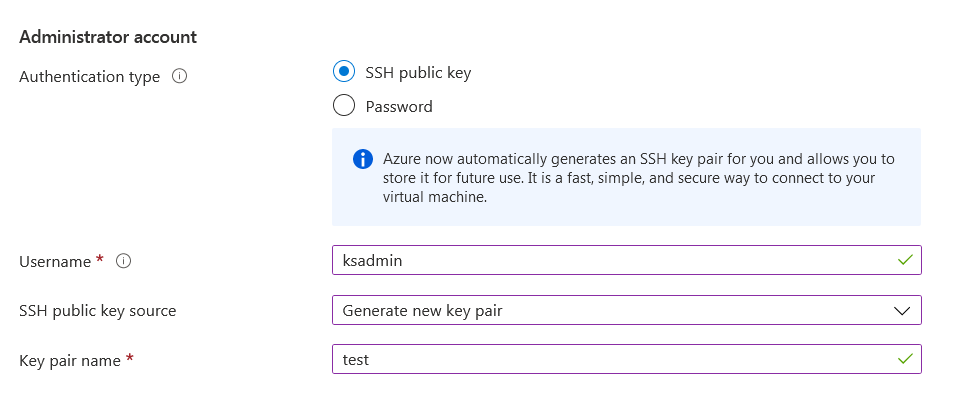
For the Username, enter "ksadmin", the default name for the System Administrator.
Note
You MUST use the name “ksadmin” for this initial user.
For the SSH public key source, select one of "Generate new key pair", "Use existing public key", "Use existing public key stored in Azure". We support OpenSSH format for the public key, and OpenSSH, PKCS1, or PKCS8 format for the private key. RSA is the supported key algorithm. We recommend RSA 4096, with RSA 2048 as a minimum size for adequate security.
Warning
It is important that you have access to the key pair you select, otherwise you will not have permissions to perform administrator operations like performing upgrades, advanced logging or an appliance reset.
In the SSH Public Key field, provide the necessary information for the SSH public key source selected in the last step.
Select Next: Disks >. The Disks screen is displayed.
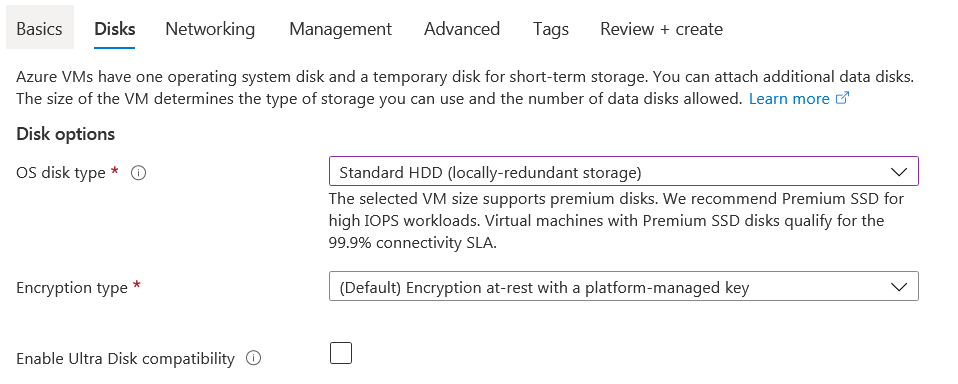
Change the OS disk type to "Standard HDD", unless you desire a faster disk.
Select an Encryption type depending on the Azure-level disk encryption you prefer.
Select Next: Networking >. The Networking screen is displayed.
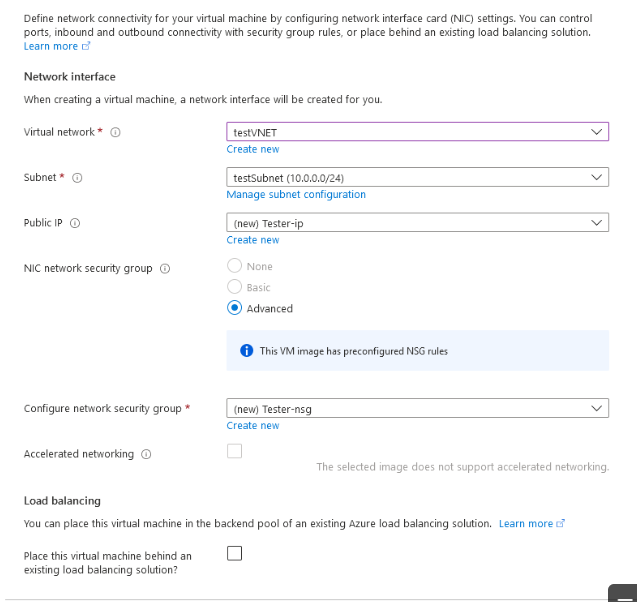
The Virtual Network, Subnet, Public IP and Configure network security group fields are populated with default values for this VM, if you have preset networking values for other Azure VMs. Create new values if needed.
For deployments with Azure Dedicated HSMs, the virtual network must also include the Dedicated HSM instance, and the lunaclient host instance. The subnet must also include the lunaclient host instance; this is subnet is referred to as the "Compute" subnet.
For a list of security groups/ports, refer to Network Security Groups.
Select Next: Management >. The Management screen is displayed.
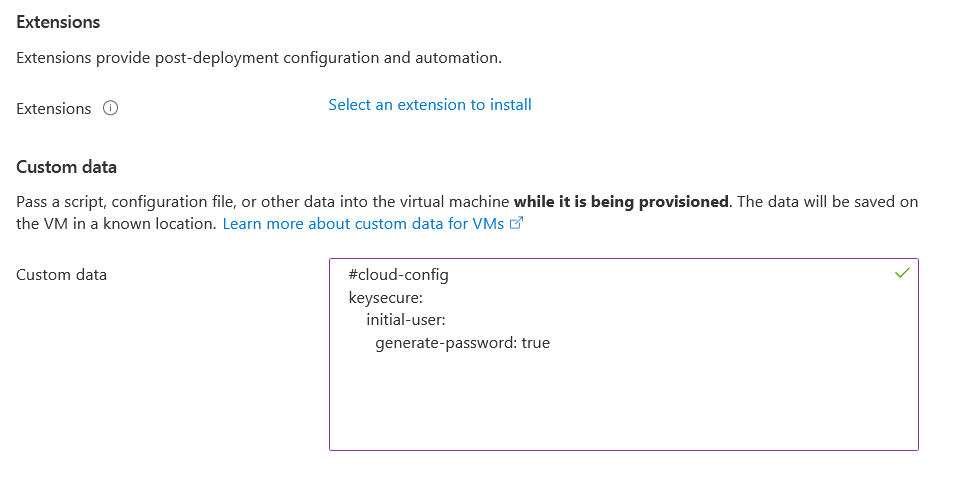
Select Next: Advanced > The Advanced screen is displayed.
If desired, you can apply cloud-init configuration. Paste cloud-init configuration in the Custom Data field.
Select Next: Tags >. The Tags screen is displayed.
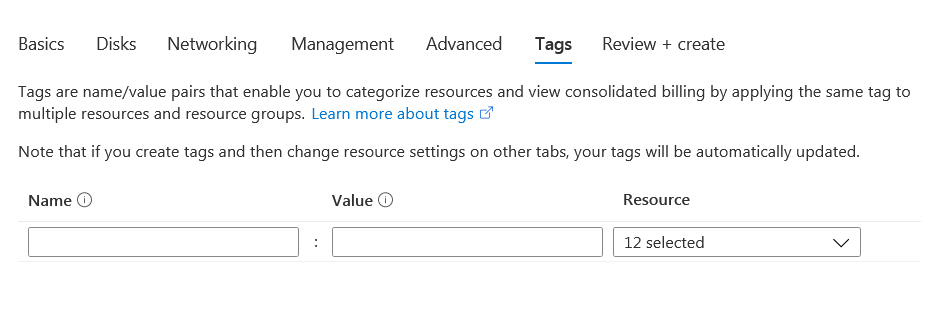
Enter any desired tags.
Select Next: Review + create >. This is the final screen. Enter an email address, and click Create to launch the VM.
Azure will run an evaluation of your virtual machine creation configuration.
If the validation was not successful, a Validation failed message is displayed:
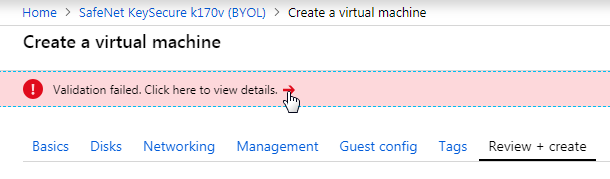
Click on the arrow for details and precede to correct the cause of the validation error.
If the validation is successful, a Validation passed screen is displayed, listing all VM details:
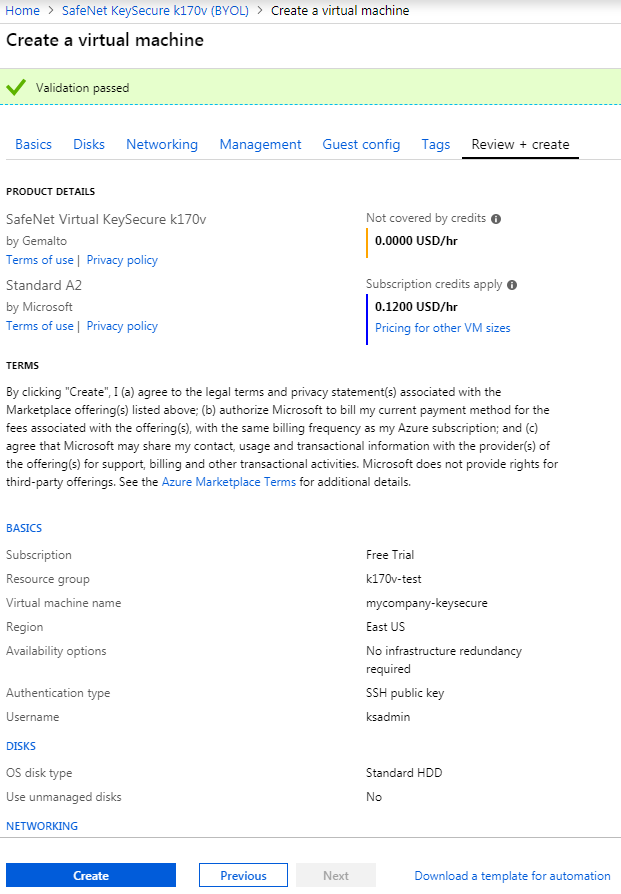
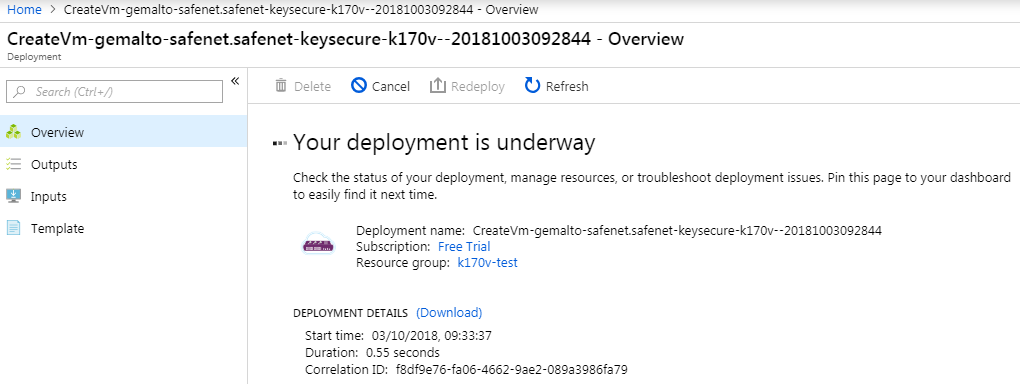
Select Create to begin deployment of this VM. This screen is displayed indicating that deployment is in process.
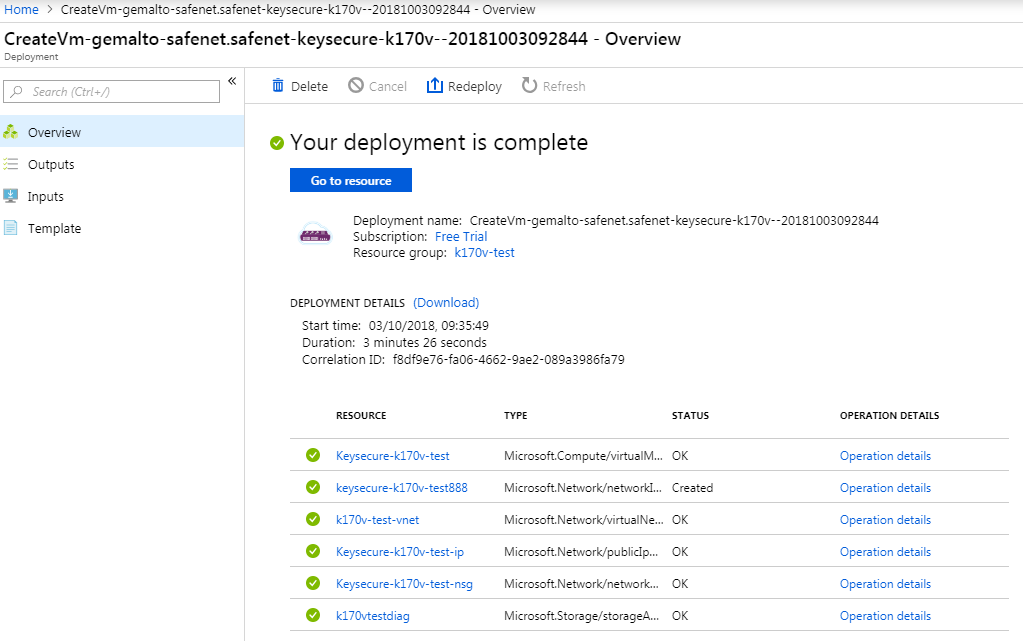
When deployment completes, this screen is displayed, providing access to all resources supporting the new VM.
Connect to the CipherTrust Manager Web Page.
Select the resource with the IP address, in this example: Keysecure-k170v-test-ip.
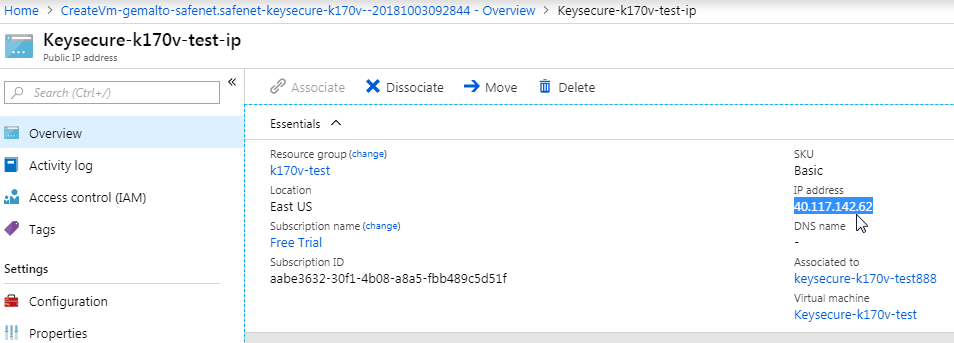
Browse to this IP address (in this example enter https://40.117.142.62). The Log In screen appears.
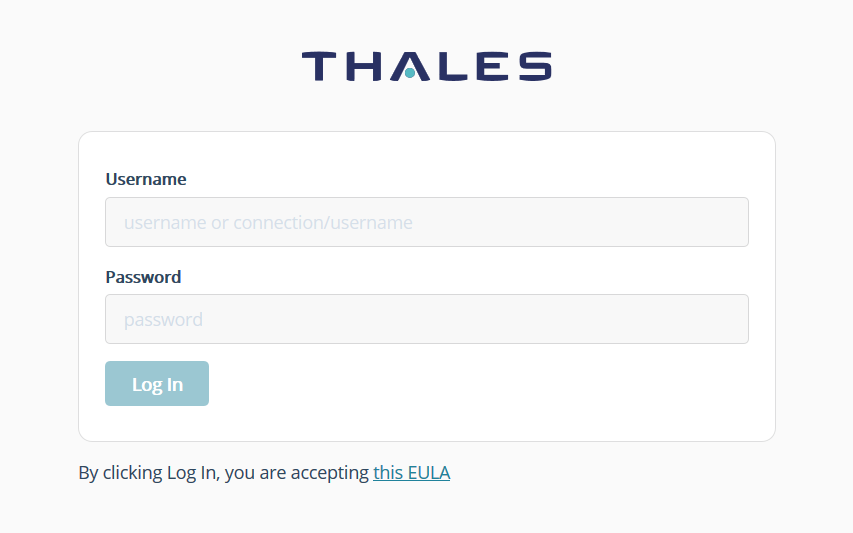
Log in using the initial default credentials: Username = admin, Password = admin
The following notice is displayed:
Note
If the default credentials do not work, you may need to retrieve an autogenerated password, as described in changing the initial password.
Enter a new password using this default Password Policy:
Min length: 8 Max length: 30 Min number of upper cases: 1 Min number of lower cases: 1 Min number of digits: 1 Min number of other characters: 1A new Login screen appears.
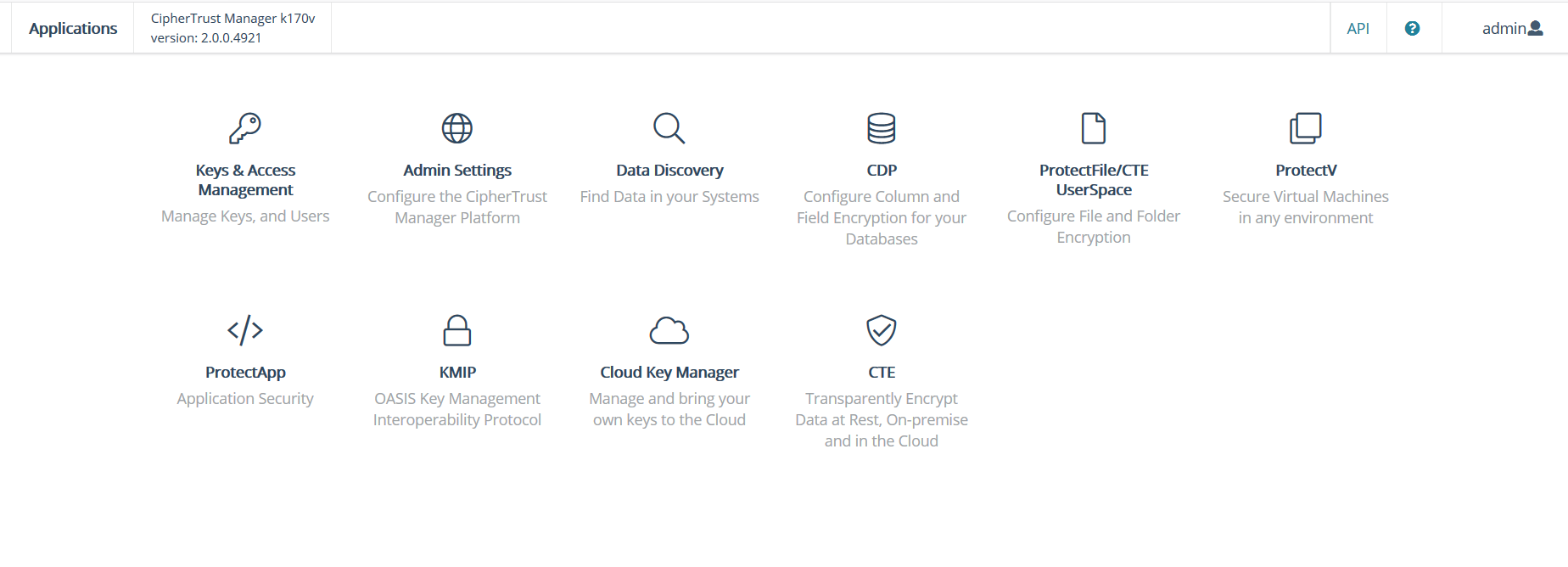
Using your new password, log in again. The CipherTrust Manager Web Page appears.
Note
Virtual CipherTrust Manager includes a 90 day trial license. To activate your instance with a term or perpetual license, see Licensing.
Congratulations! You have successfully deployed a virtual CipherTrust Manager instance.
Configuring the HSM Partition as the Root of Trust for Virtual CipherTrust Manager
To configure the HSM Partition as a root of trust for the CipherTrust Manager, you must first register the Virtual CipherTrust Manager as a client to the HSM partition. Then, you must provide some HSM partition authentication values and certificates to the Virtual CipherTrust Manager to establish a connection.
To register the Virtual CipherTrust Manager as a client to the HSM
RDP to the Windows client.
Download a version 7.2 Luna client from the Support Portal. Copy the client installer into the Windows remote desktop.
Fetch the
server.pemcertificate from the Dedicated HSM instance with SCP.scp.exe tenantadmin@<dedicated_HSM_IP>:server.pem . tenantadmin@<dedicated_HSM_IP>'s password: server.pem 100% 1159 1.1KB/s 00:00Use the VTL tool to create a client certificate and key for the Virtual CipherTrust Manager instance.
./vtl createcert -n <Virtual_CipherTrust_IP_address> -d 10 -vThe client certificate and key are available in the cert/client folder
Use
partition showinfoon LunaCM to view the partition name and serial number.Copy the client certificate to the HSM with SCP.
PS C:\Users\LunaAdmin\Desktop> scp client.pem tenantadmin@<dedicated_HSM_IP>: tenantadmin@<dedicated_HSM_IP>'s password: 172.22.0.5.pem 100% 1184 1.2KB/s 00:00SSH into the Dedicated HSM.
With the LunaSH utility, register the client to the HSM, setting a client name and providing the Virtual CipherTrust Manager IP address.
lunash:>client register -client <client_name> -ip <Virtual_CipherTrust_IP_address>Assign the HSM partition to the client.
lunash:>client assignPartition -client <client_name> -partition <partition_name>Run
client show -c <client_name>to verify that the partition has been assigned to the client.
To add the HSM connection to the Virtual
Login to the Virtual CipherTrust Manager.
Navigate to System> HSMs.
Select SafeNet Luna SA 5, 6, or 7 - Network HSM
Enter the following values:
Partition label
Partition Password: This is the Crypto Officer password created above
Partition Serial Number,
IP of the Dedicated HSM
HSM server certificate,
Client certificate,
Client certificate key.
Click Next to be taken to a validation page.
If the validation is successful the server will restart and you will be prompted to login again.
Login with the default credentials (username: admin , password: admin).
Change the password and login.
Verify that the HSM has been added on System> HSMs.

