Amazon Web Services Deployment
You can deploy a CipherTrust Manager image within Amazon Web Services (AWS).
Minimum Requirements
To deploy a CipherTrust Manager instance, the following minimum requirements apply:
System volume: 50 GB for evaluation, 100 GB for production
Memory: 16 GB
vCPUs: 2
NICs: 1
Note
These minimum system requirements are for a system with light to moderate load. For applications that heavily load the system, additional memory and CPU allocation are required. The system volume holds all data as well as backups.
Provisioning the AMI
AWS region-specific, and confidential Virtual CipherTrust Manager images (AMI) are obtained by provisioning. Provisioning places a CipherTrust Manager AMI in your target AWS account in the target region(s).
Use the SafeNet Cloud Provisioning System, to customize a CipherTrust Manager AMI for a specific region.
Note
Only authorized Customer Support Portal users can make provisioning requests.
Login to the Thales Customer Support Portal.
Navigate to the My Provisioning Requests page, through the Tools > Provisioning Requests menu.
Click Create Provisioning Request.
Select CipherTrust Manager from the Product Name dropdown.
Select the desired Product Version from the dropdown.
Note
We recommend deploying the most recent version for the latest security fixes and most current features.
Select the desired AWS Region from the dropdown.
Provide your AWS Account Number.
(Optional) If desired, type in the names of Additional Regions in the text field, to deploy AMIs in more than one region.
(Optional) If desired, adjust the Priority. The default priority is 3-Medium.
Click Submit.
A Thales client services engineer will receive and work on the request.
When your provisioning request is completed, you will an email notification with the subject line Cloud Provisioning Request Complete. Alternatively, you can periodically check the provisioning request status directly on the My Provisioning Requests page.
Retrieve the AMI ID from the completed provisioning request.
Navigate to the My Provisioning Requests page, through the Tools > Provisioning Requests menu.
Click on the name of the completed provisioning request. The Status column indicates requests that are completed.
Proceed to deploy the Virtual CipherTrust Manager image.
Deploying in AWS
This section provides the steps for deploying a Virtual CipherTrust Manager instance in AWS.
Prerequisites
A provisioned Virtual CipherTrust Manager AMI.
If using a Windows client use PuTTY or similar utility to SSH to your CipherTrust Manager instance as KeySecure Administrator (ksadmin).
If needed, use PuTTYgen or similar utility to format the SSH Key Pair. RSA is the supported key algorithm. We recommend RSA 4096, with RSA 2048 as a minimum size for adequate security.
If using a Linux client use SSH to login as KeySecure Administrator (ksadmin).
To launch a CipherTrust Manager instance in AWS
Sign in to your AWS account at the AWS portal at: https://aws.amazon.com
In the Compute group, select EC2 service.
On the AWS top bar and to the right, make sure you select the AWS Region you provisioned for your AMI.

In the left pane, under the Images, select AMIs and search for the provisioned AMI (e.g. ami-1f6b5b60).
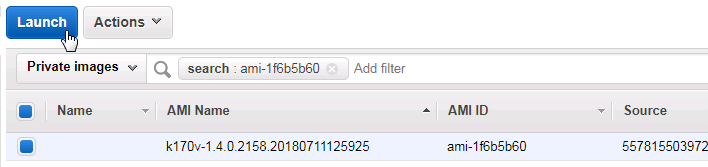
Select your image and then click on Launch.
In the Choose an Instance Type screen, choose a size that meets the minimum requirements and then select Next: Configure Instance Details.
In the Configure Instance Details screen,
Create a new Network and Subnet or select one that you have already created.
At the bottom of the screen there is a section Advanced Details.
Any information that you need configured before the first boot must be entered here in the user data area. See Plan Configuration Settings for Cloud Init.
Select Next: Add Storage.
In the Add Storage screen, select the desired Size (GiB).
Enter 100 GiB if this is for Production.
Enter 30 GiB if this is for lab use.
Select Next: Add Tags.
In the Add Tags screen, select Add Tag
Enter Tag: Name
Value: Something meaningful to the operator; for example "CipherTrust Manager for lab use"
Select Next: Configure Security Group.
In the Configure Security Group screen:
Create a new security group or re-use a previously created group.
Refer to Network Security Groups. Consider adding all of the recommended rules.
Note
To launch the CipherTrust Manager, you need at a minimum Port 22 inbound/outbound for ksadmin's SSH connection and Port 443 for an HTTPS connection to the GUI.
Select the Review and Launch screen.
In the Review Instance Launch screen:
Review your launch configuration settings.
Make any changes by selecting the Edit ... at the right of each section.
After your review, select Launch.
You are presented with this dialog box to select a key pair.
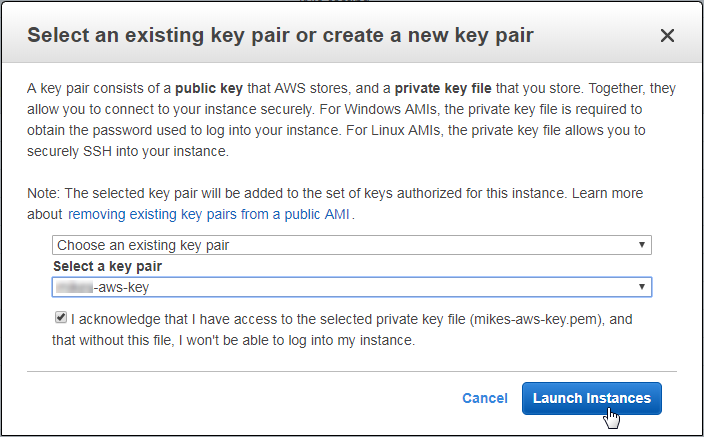
Select which Key Pair option to use. The key pair should be in Linux (PEM) format, not OpenSSH format. Valid options are:
Choose an existing key pair from the drop-down list. If your key pair is not on this list, you can import it here:
Services > EC2 > Network and Security > Key Pairs
Create a new key pair. (This option allows you to download your own key pair.)
After selecting the Key Pair, check off the acknowledge statement at the bottom of the dialog box, confirming that you have access to the selected private key file.
Warning
It is important that you have access to the key pair you select, otherwise you will not have permissions to perform administrator operations like performing upgrades, advanced logging or an appliance reset.
Select Launch Instances.
The Launch Status screen appears. You can review the launch process on this screen.
Note
It can take a several minutes for your instance to launch.
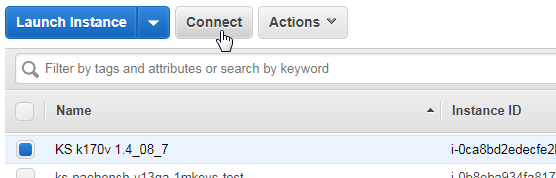
Select View Instances to view the state of your instance as it is being launched. You may need to search for the name of your instance in the Instances table if it is among many others.
At this point, if you wish to connect as System Administrator (ksadmin) to perform system level duties, duties such as performing network configurations, system upgrades, continue with the next step.
Note
Refer to Groups for a more detailed list of ksadmin duties.
Otherwise, browse to step 18 to connect to the CipherTrust Manager Web Page.
Select your instance in the table and then select Connect.
The Connect To Your Instance dialog box appears:
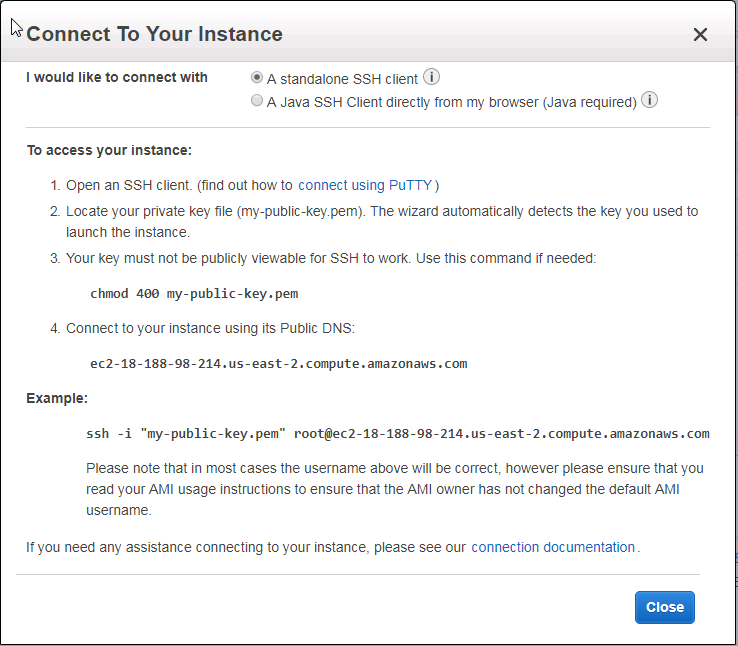
Copy the instance Public DNS string, for example: ec2-54-89-148-184.compute-1.amazonaws.com
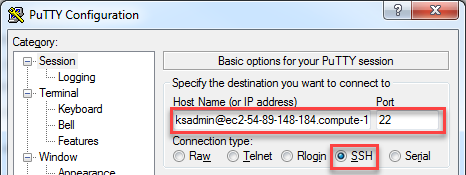
If using PuTTY, begin a new session.
Paste the Public DNS in the Host Name (or IP address) field and preface this string with "ksadmin@".
Set the Connection Type to SSH.
In the Category pane:
Select Connection > SSH > Auth.
Select Browse and navigate to the folder with your Private Key.
Select your Public Key file name. The file name and path is automatically places in the Private key file for authentication field.
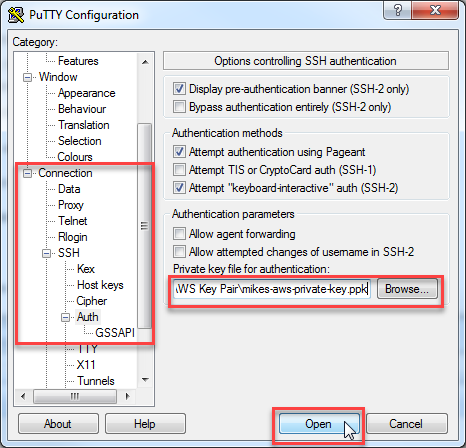
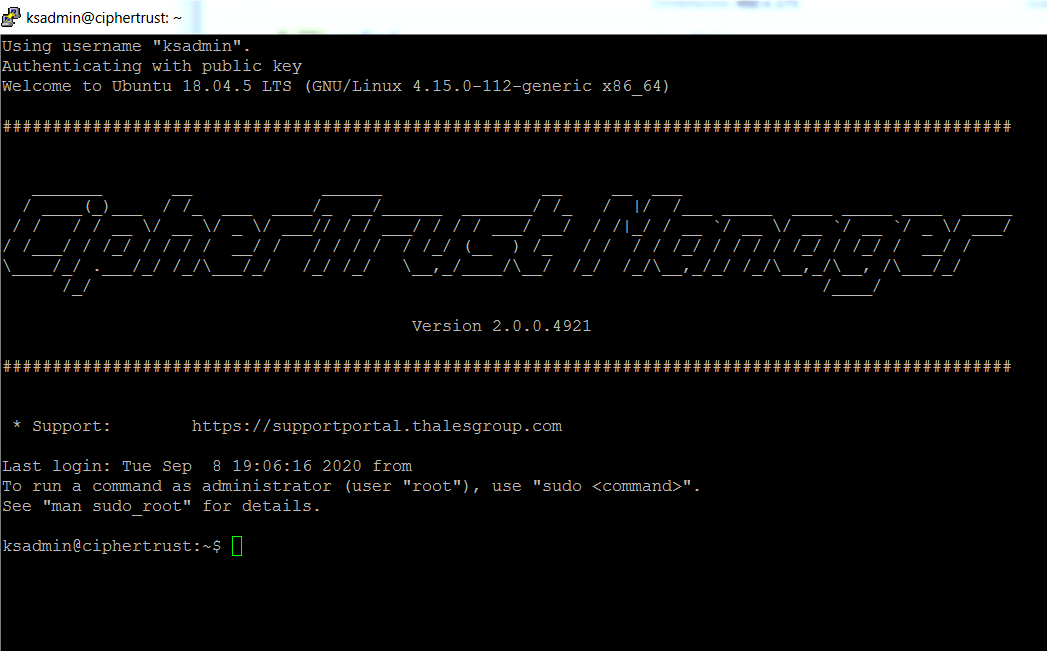
Select Open. The following ksadmin screen appears:
Note
If you are unable to connect to your instance using PuTTY, go to: https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/putty.html for further assistance.
Connect to the CipherTrust Manager Web Page.
Copy the IPv4 Public IP or IPv6 IP address shown in the Instances > Description tab of your AWS instance.
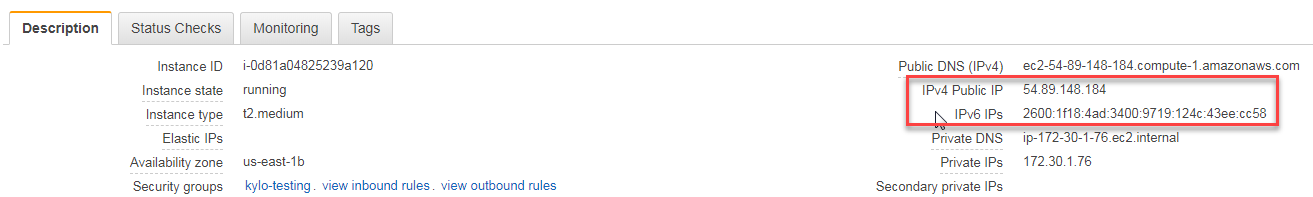
Browse to HTTPS://
. The Log In screen appears. 
Log in using the initial default credentials: Username = admin, Password = admin
The following notice is displayed:
Note
If the default credentials do not work, you may need to retrieve an autogenerated password, as described in Changing the Initial Password.
Enter a new password using this default Password Policy:
Min length: 8 Max length: 30 Min number of upper cases: 1 Min number of lower cases: 1 Min number of digits: 1 Min number of other characters: 1A new Login screen appears.
Using your new password, log in again. The CipherTrust Manager Web Page appears.
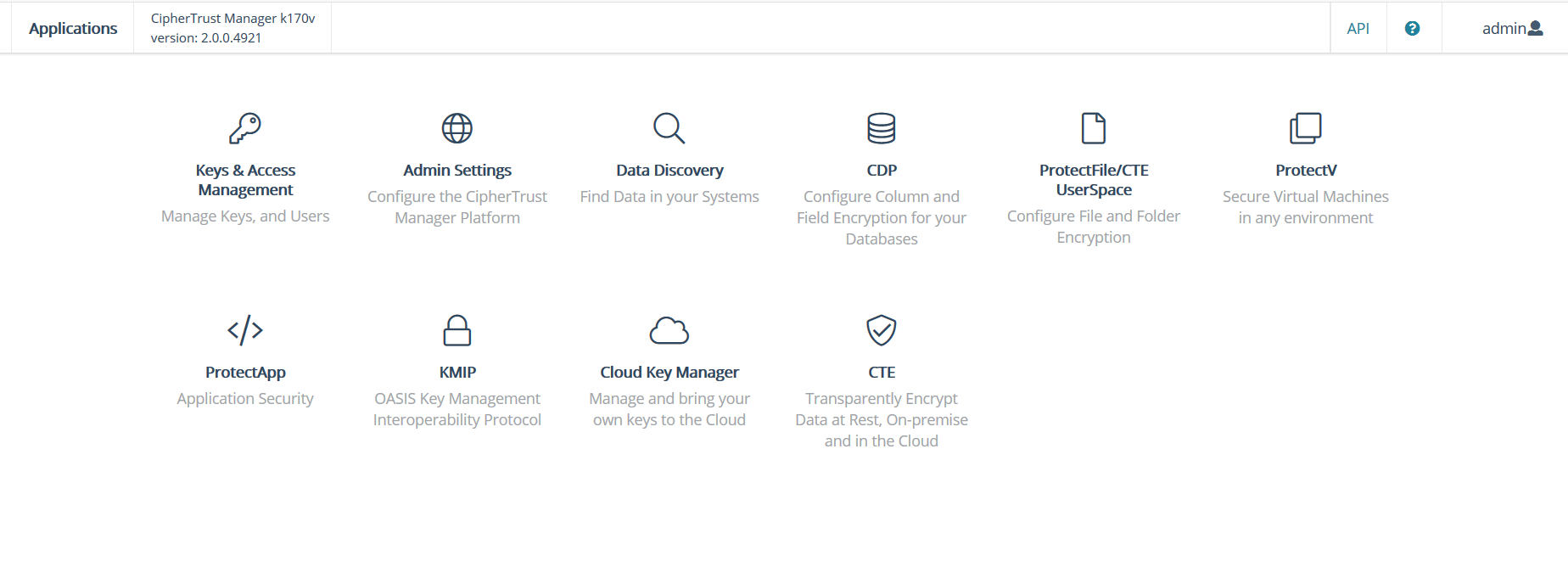
Congratulations! You have successfully deployed your Virtual CipherTrust Manager instance.
Note
Virtual CipherTrust Manager includes a 90 day trial license. To activate your instance with a term or perpetual license, see Licensing.
Enhanced Networking
The CipherTrust Manager AMI ships with Elastic Network Adapter (ENA) enabled. ENA provides high-performance networking on supported EC2 instance types. For more information visit https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/enhanced-networking.html.

