Creating a CTE-LDT Policy for DFSR
How you create policies for DFSR depends on the key manager that you are using.
Procedure Using CipherTrust Manager
-
Log into the CipherTrust Manager Console and switch to the correct domain if required.
-
If you do not know which versioned key you want to use to encrypt the data or you want to create a new key to use for the DFSR namespace, launch the Keys & Access Management application and locate an existing versioned key or create a new versioned key. For details on creating a versioned key for CTE-LDT, see CTE-Live Data Transformation with CipherTrust Manager.
-
Launch the Transparent Encryption application.
-
In the left-hand menu bar, click Policies.
-
Click Create Policy.
-
Enter a name for the policy in the Name field.
-
In the Policy Type field, select Live Data Transformation.
-
Click Next.
-
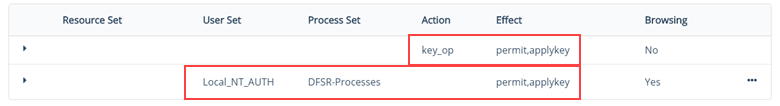
On the Security Rules page, make sure there is a security rule with the action key_op and the effect permit,applykey. If CipherTrust Manager did not add this security rule automatically, go back to the General Info page and make sure that the policy type is set to Live Data Transformation.
-
On the Security Rules page, click Create Security Rule and add the following security rule:
-
In the User Set field, select the user set you created that contains NT AUTHORITY. For details, see Creating Required DFSR Policy Components.
-
In the Process Set field, select the process set you created that contains the required DFSR processes
dfsrs.exeandntoskrnl.exe. -
In the Action field, select
all_ops. -
In the Effect field, select
PermitandApply Key.
When you are done, click Add to save the security rule.
-
-
Add any other security rules you need to your policy. When you are done, click Next.
-
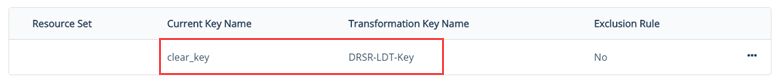
On the Key Rules page, click Create Key Rule and add the following key rule:
-
In the Current Key field, select
clear_key.In a DFSR environment, you must apply the CTE-LDT policy on unencrypted data ONLY (the current key must be set to
clear_key). If your data is already encrypted, you must decrypt it and completely remove the existing GuardPoint before re-encrypting the data with a new key from scratch. For details, see Considerations with DFSR. -
In the Transformation Key field, select the CTE-LDT versioned key you want to use to encrypt the data.
When you are done, click Add to save the key rule.
-
-
Click Next.
-
Verify the policy information and click Save to save the CTE-LDT policy.

