Creating Policy Elements
Policy rule criteria consist of resource sets, user sets, signature sets, process sets, action, and effect, and are called policy elements. These elements should exist on the CipherTrust Manager before you can use them in security policies.
Although you can add policy elements when creating policies, it may be a better approach to have them created in advance. This document describes creation of policy elements separately, before creating policies.
A CipherTrust Manager administrator can create, modify, and delete resource sets, user sets, process sets, and signature sets on the CipherTrust Manager. Actions and effects are preconfigured on the CipherTrust Manager.
After you have created policy elements, you can use them in creating and configuring policies. Refer to Creating Policies for details.
Creating Resource Sets
A resource is a combination of a directory, a file, and patterns or special variables. A resource set is a named collection of directories, files, or both, that a user or process will be permitted or denied access to.
Use the Create Resource Set wizard to create resource sets.
Open the Transparent Encryption application.
Click Policies > Policy Elements.
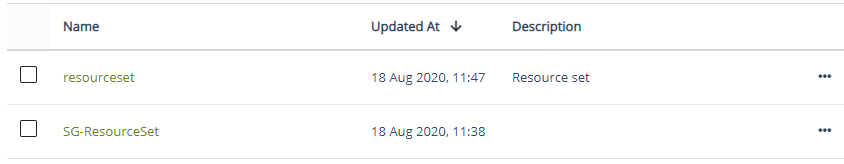
On the Resource Sets tab, click Create Resource Set. The Create Resource Set wizard is displayed.
On the General Info screen:
Enter a unique Name for the set.
The name must start with a character. The maximum length can be 64 characters.
The name can contain alphanumeric characters, underscores (
_), and dashes (-).The name cannot contain the following special characters:
? : ; | ! @ # $ % ^ & * < = > + ( ) { } ~ , \ / [ ] ' "
Make sure that Directory is selected as the Resource Set Type.
Provide a Description for the set.
Click Next. The Add Resources screens is displayed.
Specify the resource Directory.
The path must end with a slash. For example, a Windows path must end with a
\(backward slash). A Linux path must end with a/(forward slash).Specify a File or enter the asterisk (
*). The asterisk acts as a wild card character.Note
An asterisk can be used to include all files of a specific extension in the resource set. For example, to include all text files under a resource directory, specify
*.txt.
Later, a policy with desired permissions can be applied to the resource set. That policy will apply to all files of the specified extension under the specified resource directory.(Optional) Specify whether to include subfolders in the set. Turn on Include Sub Folders. By default, the subfolders are not included.

(Optional, Linux only) Turn on the HDFS File System toggle for an HDFS resource. When you turn on this toggle, ensure that Directory and File contain HDFS paths.
HDFS is applicable to Linux clients. By default, the HDFS File System toggle is turned off. Keep it turned off for a non-HDFS resource.
Note
To protect an HDFS resource, the CTE clients (NameNode and DataNodes in the HDFS cluster) must be configured for HDFS. Refer to the "Installing CTE on Hadoop" section in the CTE Agent for Linux Advanced Configuration and Integration Guide for details.
Note
For the list of supported HDFS systems, refer to the Compatibility Matrix for CTE Agent with Data Security Manager. The matrix also applies to the CTE clients registered with the CipherTrust Manager.
Click Next. The Confirmation screen is displayed.
The screen shows general information about the set and the selected sources.

Verify the resource set details.
If the details are incorrect or you want to modify them, click Back and update the details. To add another resource, click Add Another Resource, and specify the details, as described above.
Click Save. The resource set is created.
The newly created resource set appears on the Resource Sets tab.
Creating User Sets
A user set is a collection of users and user groups that you want to grant or deny access to GuardPoints. User sets are configured in policies. Policies can be applied to user sets, not to individual users.
Use the Create User Set wizard to create user sets. The wizard provides two options to add user sets. Specify a user set either by querying the registered client or by manually entering the members (individual members, groups, or group members). If needed, you can manually add AD users to a user set.
Creating User Sets by Browsing the Client
To create a user set:
Open the Transparent Encryption application.
Click Policies > Policy Elements.
Click the User Sets tab.
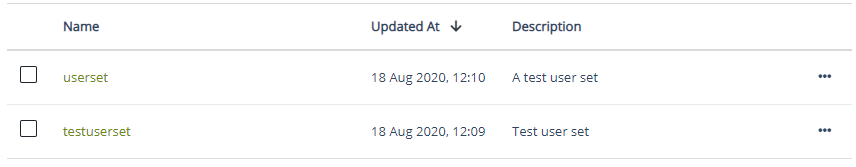
Click Create User Set. The Create User Set wizard is displayed.
On the General Info screen:
Enter a unique Name for the set.
The name must start with a character. The maximum length can be 64 characters.
The name can contain alphanumeric characters, underscores (
_), and dashes (-).The name cannot contain the following special characters:
? : ; | ! @ # $ % ^ & * < = > + ( ) { } ~ , \ / [ ] ' "
Provide a Description for the set.
Click Next. The Add Users screen is displayed.
By default, the Browse to Add Users tab is active. This tab allows you to browse the client for members. To add members manually, refer to Creating User Sets by Adding Members Manually.
Select the Agents option.
Click Select. The list of registered clients is displayed.
Select the desired client. Members, groups, or group members of this client will be added to the set.
Click Select. The IP address or hostname of the selected client is displayed next to the Select button. The Member Choice and Max Entries* to Return fields are also displayed.

From the Member Choice drop-down list, select members. The options are:
Members: Retrieves members (users) of the client. This is the default setting.
Groups: Retrieves user groups of the client.
Group Members: Retrieves group members of the client. When you select this option, the Select Groups field appears. This is a mandatory field. Select a group from the drop-down list. Search will retrieve members of the selected group.
Specify the Max Entries to Return. This is a mandatory field. The default number is
300.Click Submit. The search result based on the specified criteria is displayed on the right. By default, five entries per screen are displayed. Use the on-screen pagination to view more entries.
Select the desired members from the list.

Click Next. The Confirmation screen shows general information about the set and the selected members.

Verify the set details.
If the details are incorrect or you want to modify them, click Back and update the details.
Click Save. The user set is created.
The newly created set appears on the User Sets tab.
Creating User Sets by Adding Members Manually
This method is useful when you already know the names of users and groups that should be added to a user set. Also, use this method to add AD users and groups to the user set.
To create a user set:
Open the Transparent Encryption application.
Click Policies > Policy Elements.
Click the User Sets tab.
Click Create User Set. The Create User Set wizard is displayed.
On the General Info screen:
Enter a unique Name for the set.
The name must start with a character. The maximum length can be 64 characters.
The name can contain alphanumeric characters, underscores (
_), and dashes (-).The name cannot contain the following special characters:
? : ; | ! @ # $ % ^ & * < = > + ( ) { } ~ , \ / [ ] ' "
Provide a Description for the set.
Click Next. The Add Users screen is displayed.
By default, the Browse to Add Users tab is active. This tab allows you to browse the client for members. Refer to Creating User Sets by Browsing the Client for details.
Click the Manually Add Users tab.
Specify the following details, as appropriate:
Element Description uname Login name of the user. UID (AIX/Linux only) ID of the user. gname Comma-separated list of group names. GID (AIX/Linux only) Group ID of the user. Specify only the primary group ID. OS domain (Windows only) Network domain of the user. Multiple domain names, separated by commas, can be entered. Specify the string localhostto configure a generic domain.Click Next. The Confirmation screen shows general information about the set and the selected members.
Verify the set details.
If the details are incorrect or you want to modify them, click Back and update the details.
Click Save. The user set is created.
The newly created set appears on the User Sets tab.
Creating Signature Sets
A signature set is a collection of hashes of processes and executables that you want to grant or deny access to GuardPoints. A signature set can be configured in a policy as part of a process set to verify the integrity of a process before it is allowed access to guarded data. Policies are applied to signature sets, not to individual signatures.
To create a signature set:
Open the Transparent Encryption application.
Click Policies > Policy Elements.
Click the Signature Sets tab.
Click Create Signature Set. The Create Signature Set wizard is displayed.
On the General Info screen:
Enter a unique Name for the set.
The name must start with a character. The maximum length can be 64 characters.
The name can contain alphanumeric characters, underscores (
_), and dashes (-).The name cannot contain the following special characters:
? : ; | ! @ # $ % ^ & * < = > + ( ) { } ~ , \ / [ ] ' "
Provide a Description for the set.
Click Next. The Add Sources screen is displayed. On this screen, you can add files to be signed, as described below.
Adding Files to a Signature Set
Specify path of the directory or file to be signed. If a directory is specified, all files in the directory and its subdirectories are signed.
The CipherTrust Manager provides an option to add multiple sources. A maximum of 200 sources can be added at once.
Click Add Source.
Click Select Client. The list of registered clients is displayed.
Select the desired client.
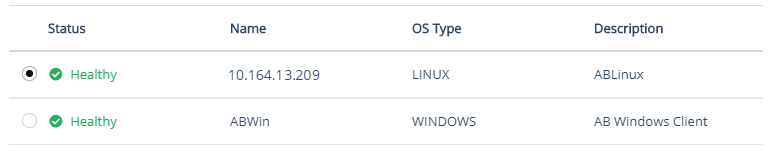
Click Select. The selected client appears next to the Change Client button (previously Select Client).
If needed, change the client by clicking Change Client.
Specify the path to be signed by either typing manually or using the browser.
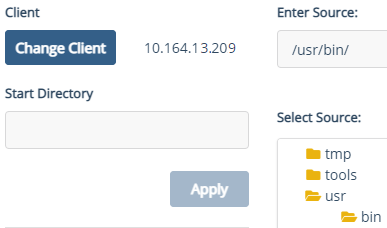
To jump to a specific directory, enter the directory path in the Start Directory field and click Apply. The browser shows the subdirectories and files, as shown below.
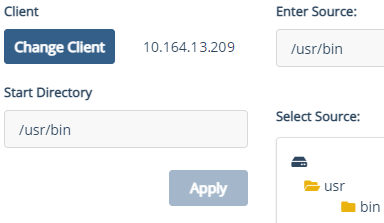
You cannot browse above the Start Directory. Enter a start point that is higher in the directory hierarchy than all the directories and files that you want to select, or you will have to re-enter start points to locate and select the desired files. The default is the top-level, either slash (Linux) or backslash (Windows).
Alternatively, if you know the directory path, you can enter it manually in the Path field.
Click Add Source. The selected source is displayed in the SELECTED SOURCES list.
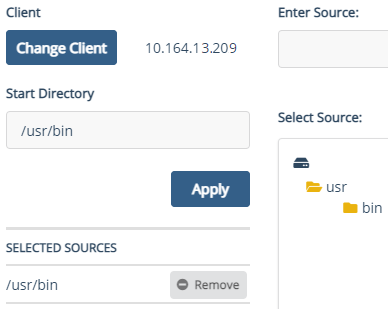
Optionally, you can add a new source by clicking Add Source. To remove a source, click Remove to the right of the source. A signature set must contain at least one source.
Click Add. The selected source is displayed in the Source Directory list.
Optionally, you can add a new source by clicking Add Source. To remove a source, click the overflow icon (
 ) corresponding to the source and click Remove.
) corresponding to the source and click Remove.Click Next. The Confirmation screen shows general information about the set and the selected sources.
Verify the set details. If the details are incorrect or you want to modify them, click Back and update the details.
Click Save.
The newly created set appears on the Signature Sets tab. By default, the signature set has the status UNSIGNED.
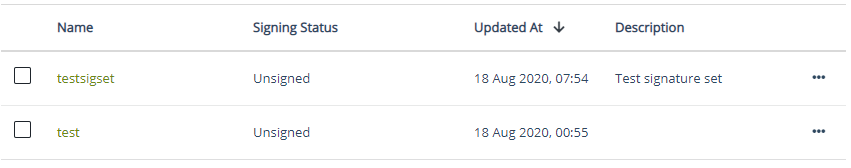
It is recommended that the signature set is signed before you apply policies to processes. This ensures that a tampered with or compromised process executable is not granted permissions to access protected GuardPoints. Refer to Signing Files in a Signature Set for details.
Creating Process Sets
A process set is a collection of processes (executables) that you want to grant or deny access to GuardPoints. Like user sets, process sets can be configured in policies. Policies can be applied to process sets, not to individual processes.
Optionally, file signing can be configured to check the authenticity and integrity of executables and applications before they are allowed to access GuardPoint data. A signature set must already exist before you can configure file signing in a policy for a process set.
Use the Create Process Set wizard to create process sets.
To create a process set:
Open the Transparent Encryption application.
Click Policies > Policy Elements.
Click the Process Sets tab.
Click Create Process Set. The Create Process Set wizard is displayed.
On the General Info screen:
Enter a unique Name for the set.
The name must start with a character. The maximum length can be 64 characters.
The name can contain alphanumeric characters, underscores (
_), and dashes (-).The name cannot contain the following special characters:
? : ; | ! @ # $ % ^ & * < = > + ( ) { } ~ , \ / [ ] ' "
Provide a Description for the set.
Click Next. The Add Processes screen is displayed.
Specify the process path.
Click Browse next to the Directory field. The list of registered clients is displayed.
Select the desired client.
Click Next. The Browse Path dialog box is displayed.
Browse the process.
Alternatively, specify the process name (with its path) in the Path field. For a Windows path, use
\(backward slashes), for a Linux path, use/(forward slashes). A directory path must end with a slash.Click Add.
The selected directory and process appear in the Directory and File fields. If a process is not selected, the File field shows an (
*) asterisk. The asterisk acts as a wild card character.Alternatively, specify the directory and process in the Directory and File fields. For a Windows path, use
\(backward slashes), for a Linux path, use/(forward slashes). A directory path must end with a slash.Link the desired signature set to the process set.
Click Select next to the Signature field. The list of signature sets is displayed.
Select the desired signature set.
Click Next.
The selected signature set appears in the Signature field.
Click Next. The Confirmation screen shows general information about the set.

Verify the set details.
If the details are incorrect or you want to modify them, click Back and update the details. To add another process, click Add Another Process, and specify the details, as described above.
Click Save. The process set is created.
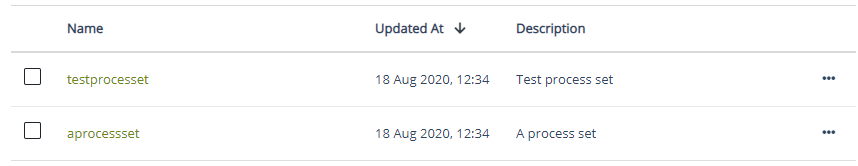
The newly created set appears on the Process Sets tab.
After you have created policy elements, you can use them in creating and configuring policies. Refer to Creating Policies for details.

