Managing Google EKM Endpoints
After meeting some prerequisites to allow Google Cloud External Key Manager (EKM) Service to access CipherTrust Manager, you can create and manage an endpoint in CipherTrust Manager for Google Cloud EKM service to access a Key Encryption Key (KEK) using CipherTrust Manager's GUI and REST API.
After you have created an endpoint, you can:
Edit the default policies
Enable or disable the wrapping and unwrapping operation. This allows you to avoid deleting the endpoint, and temporarily suspend Google Cloud EKM's ability to use the KEK.
View activity for a wrap or unwrap endpoint. Google Cloud Key Management Service (KMS) consumes these endpoints.
Prerequisites
To allow a connection between CipherTrust Manager and Google Cloud External Key Manager Service, some network and security configuration must be in place in both entities.
CipherTrust Manager Prerequisites
The CipherTrust Manager must have a public IP address with the 443 HTTPS port open. See Network Interface Configuration for details.
The CipherTrust Manager must be reachable through a Fully Qualified Domain Name (FQDN). Use the format
ciphertrust.<your_domain>.com, for exampleciphertrust.mycompany.com. Google Cloud recognizes theciphertrustprefix and allows traffic to that domain.The web interface must have a TLS certificate signed by an external Certificate Authority (CA) trusted by Google Cloud Platform. Google Cloud trusts certificates issued by well-known public CAs such as Verisign. Alternatively, you can create a certificate chain with Google's Certificate Authority Service and upload the chain to CipherTrust Manager.
Google Cloud Platform Prerequisites
- The default policy for endpoints requires Key Access Justifications. Key Access Justifications must be enabled in the Google Account before Google services can access the endpoint.
Create an endpoint
Below, we provide steps to create a Google endpoint in the CipherTrust Manager GUI and to make the endpoint available to Google Cloud EKM. You can also use the /v1/cckm/ekm/endpoints endpoint in the REST API to associate meta information with the endpoint.
Login to the CipherTrust Manager products page.
Navigate to Cloud Key Manager>Services>Google Cloud EKM
Click Create Endpoint
Provide a Name and a Key URI Hostname for your endpoint. The Key URI Hostname should be the FQDN of the CipherTrust Manager instance.
An AES-256 Key Encryption Key (KEK) is created, with a unique URI, that acts as the Google EKM endpoint key. The hostname is applied to the URI, to create a path that Google Cloud can access.
Caution
Do not edit this KEK through the general CipherTrust Manager key management functions. Do not modify the KEK through the Keys menu in the GUI, ksctl keys commands in the CLI, or the
/v1/vault/keys2endpoint in the REST API. This can result in the KEK becoming unavailable to the Google Cloud EKM service unexpectedly.Edit the endpoint policies, if desired. By default, the endpoint allows all clients and all supported justification reasons.
Enable Key Access Justifications in your Google Account, if you have not already.
On Google Cloud, create a Cloud EKM key, matching the URI for the KEK. Provide the full URI, including hostname. For the location, choose the region geographically closest to where the CipherTrust Manager instance is deployed.
Consult documentation for your desired Google CMEK service integrated with Cloud EKM to grant permissions for the CMEK service to use the KEK in Cloud KMS. Consult this documentation as well for particular encryption and decryption usecases for the CMEK service.
For example:
Change the base hostname
You can patch the /v1/cckm/ekm/endpoints/{id} REST API endpoint, as described in the API Guide.
In the GUI:
Login to the CipherTrust Manager products page.
Navigate to Cloud Key Manager>Services>Google Cloud EKM
Find the endpoint in the list, and click the ellipsis icon (...) at the far right for options.
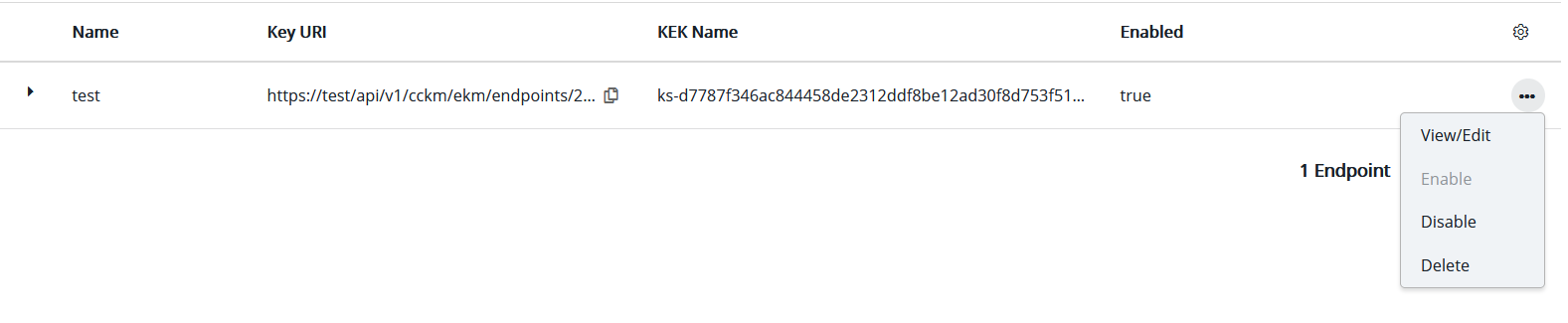
Click View/Edit
In the Edit Endpoint window, enter a new Key URI hostname and click Save.
Enable or Disable Key Wrapping
You can post to the /v1/cckm/ekm/endpoints/{id}/enable and /v1/cckm/ekm/endpoints/{id}/disable REST API endpoints, as described in the API Guide.
In the GUI:
Login to the CipherTrust Manager products page.
Navigate to Cloud Key Manager>Services>Google Cloud EKM
Find the endpoint in the list, and click the ellipsis icon(...) at the far right for options.
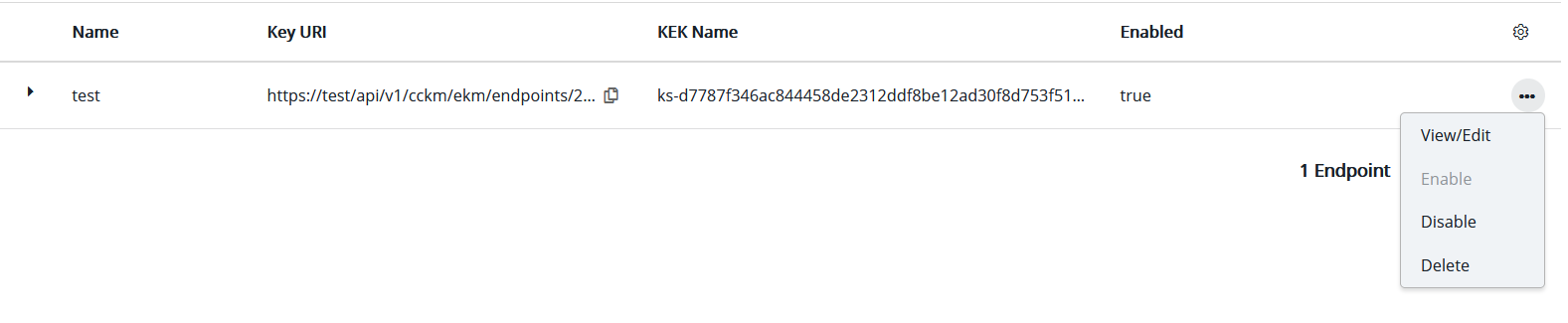
Click Enable or Disable.
Delete the Endpoint
You can delete the /v1/cckm/ekm/endpoints/{id}/ REST API endpoint, as described in the API Guide.
In the GUI:
Login to the CipherTrust Manager products page.
Navigate to Cloud Key Manager>Services>Google Cloud EKM
Find the endpoint in the list, and click the ellipsis icon(...) at the far right for options.
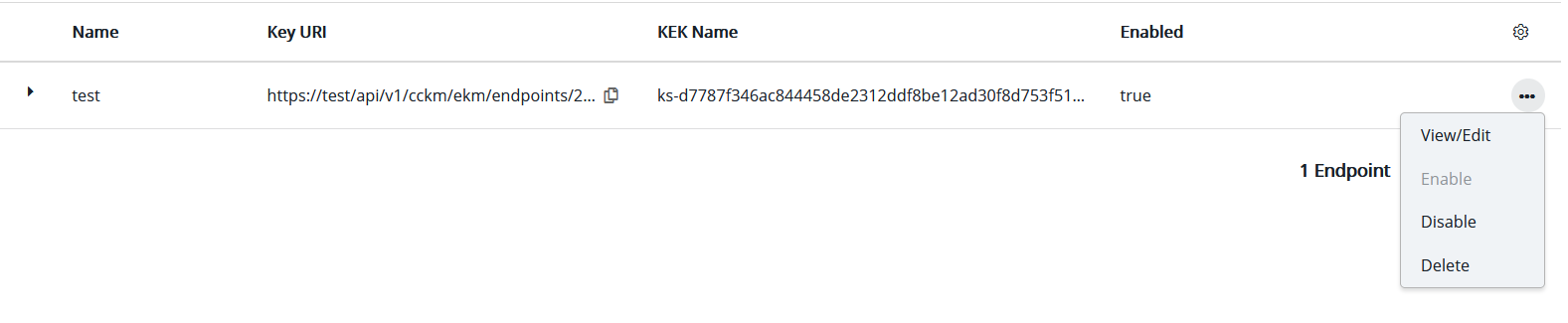
Click Delete.
View Activity for a Wrap or Unwrap Endpoint
Google Cloud KMS calls these endpoints to perform a wrap or unwrap operation on a base64 blob, and therefore protect some data on behalf of a CMEK service integrated with Cloud EKM such as BigQuery or Compute Engine.
This functionality is available with the /v1/cckm/ekm/endpoints/{id}:wrap and /v1/cckm/ekm/endpoints/{id}:unwrap REST API endpoints, as described in the API Guide.
Google Cloud KMS can find and make calls to these endpoints without user intervention, if Google Cloud KMS has correctly configured the Cloud EKM key, and the CMEK service is correctly configured to access the key on Google Cloud KMS. This configuration happens as part of creating a new endpoint.
Requests to these endpoints generate a record under Records> Server Records in the GUI, and the /v1/audit/records endpoint in the API. These records can be helpful to monitor CMEK activity or troubleshoot CMEK problems.

