Oracle Cloud Deployment
Minimum Requirements
To deploy a CipherTrust Manager instance, the following minimum requirements apply:
Boot Disk: 1 volume, minimum size: (46.6 GB for evaluation purposes, 100 GB for production)
Memory: 16 GB
vCPUs: 2
NICs: 1
Note
These minimum system requirements are for a system with light to moderate load. For applications that heavily load the system, additional memory and CPU allocation are required. The system volume holds all data as well as backups.
Deploying in Oracle Cloud
Steps for deploying a CipherTrust Manager instance in Oracle Cloud:
Log in to Oracle Cloud.
Click menu button on top left corner, then navigate to Core Infrastructure > Compute > Instances.
Click Create Instance.
Create Compute Instance page opens.Specify a name for the instance.
Click Change Image.
Browse All Images popup opens.Go to the Custom Images tab.
Select the desired image.
Click Select Image.
Select the desired Availability Domain.
Note
To learn more about Availability Domains, click here.
Select the desired Shape.
Note
To learn more about Compute Shapes, click here.
In the Configure Networking section, specify/select the following settings:
Virtual Cloud Network Compartment
Select a Virtual Cloud Network
Subnet Compartment
Subnet
Use Network Security Groups to control traffic (optional)
Note
It is recommended to use a Network Security Group to monitor/control the network traffic. To learn more about Network Security Groups, click here.
Depending on your requirements, select one of the following:
Assign a Public IP Address
To make this instance accessible through internet.Do Not Assign a Public IP Address
To make this instance accessible through private network only.
In the Boot Volume section, specify/select the following options:
Specify a Custom Boot Volume Size
To deploy a Thales CipherTrust Manager instance, the system volume requirements must be at least 100 GB in a production environment and 46.6 GB when evaluating the product.
Note
Volume Size affects the Boot Volume performance. To learn more, click here.
Use In-Transit Encryption
Note
To read more about Oracle's In-Transit or At-Rest Encryption, click here.
Encrypt this volume with a key that you manage
Select this option if you wish to encrypt the data in this volume using your own Vault service encryption key. After selecting this checkbox, specify the following:Vault compartment
Vault (containing the master encryption key you want to use)
Master Encryption Key Compartment
Master Encryption Key
Note
If this option is enabled, both at-rest encryption and in-transit encryption are performed using this key.
In the Add SSH Keys section, use one of the following options:
Note
We support OpenSSH format for the public key, and OpenSSH, PKCS1, or PKCS8 format for the private key. RSA is the supported key algorithm. We recommend RSA 4096, with RSA 2048 as a minimum size for adequate security.
Generate SSH Keys
Use this option to generate the SSH keys on-the-go. Then download the keys using the links provided.
Use SSH Key Files
If you already have SSH key files, then select this option and then upload the public key file.
Paste SSH Keys
If you already have SSH key files, then paste the contents of the public key file in the field provided.
Note
You can add additional keys, if required. To learn how to generate a SSH Key pair, click here.
Tip
If it is desired to specify custom Cloud-Init configuration, then click Show Advanced Options, go to Management tab, and paste your Cloud-InIt configuration script.
Click Create. The Oracle Cloud Instance will be created. Use its public/private IP to access CipherTrust Manager.
Connect to the CipherTrust Manager Web Page.
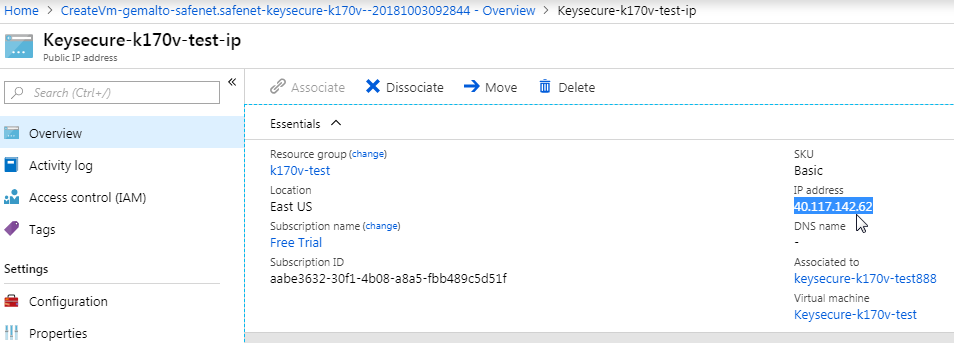
Select the resource with the IP address, in this example: Keysecure-k170v-test-ip.
Browse to this IP address (in this example enter https://40.117.142.62). The Log In screen appears.
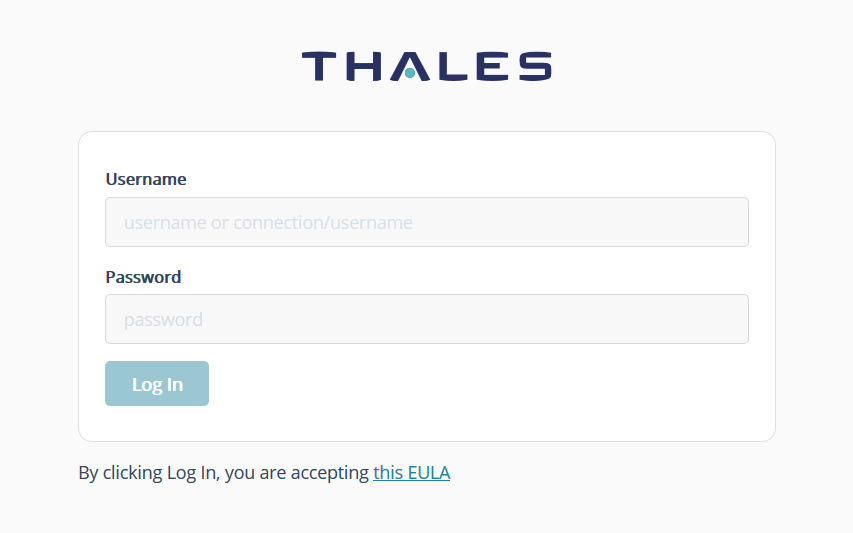
Log in using the initial default credentials: Username = admin, Password = admin
The following notice is displayed:
Note
If the default credentials do not work, you may need to retrieve an autogenerated password, as described in changing the initial password.
Enter a new password using this default Password Policy:
Min length: 8 Max length: 30 Min number of upper cases: 1 Min number of lower cases: 1 Min number of digits: 1 Min number of other characters: 1A new Login screen appears.
Using your new password, log in again. The CipherTrust Manager Web Page appears.
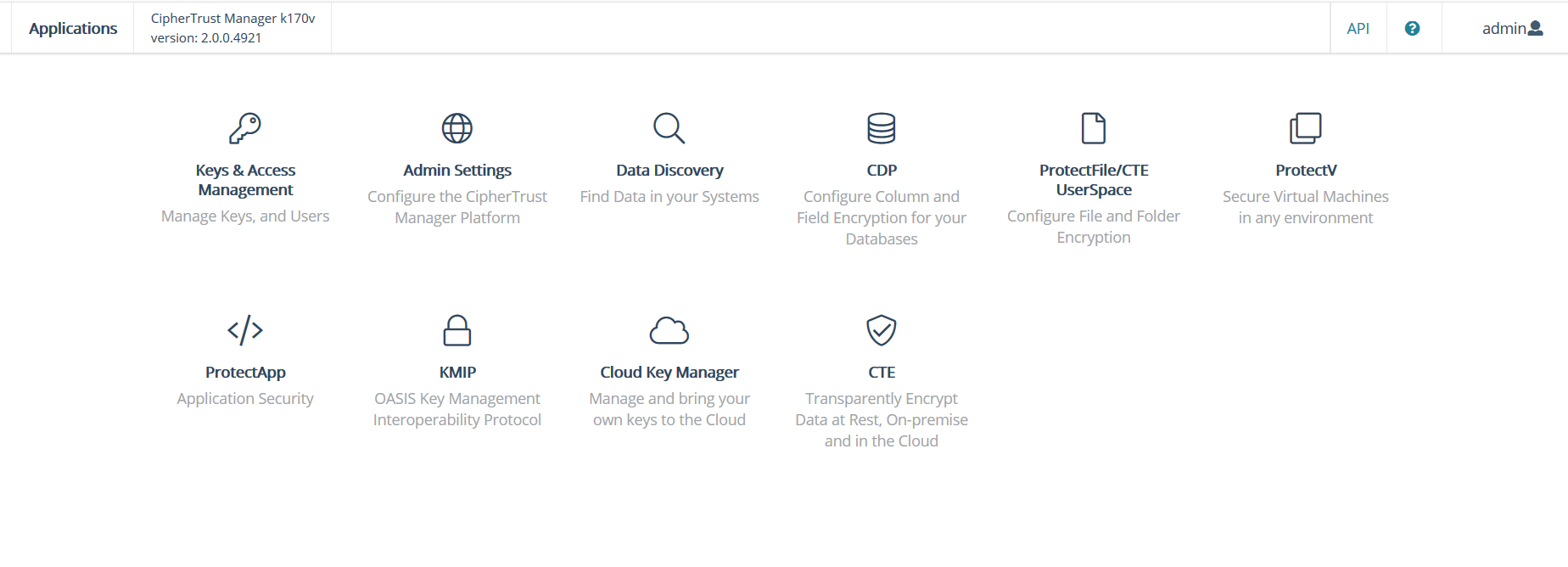
At this point, it's strongly recommended to configure an NTP server.
Navigate to Admin Settings > NTP.
Enter in an NTP Server hostname.
For an authenticated NTP Server, enter in a symmetric key value in the NTP Key field.
Click the +Add NTP Server button.
See Network Time Protocol Server Configuration for more details.
Note
Virtual CipherTrust Manager launches in Community Edition, with some restrictions on functionality. You can activate a 90 day trial evaluation for full functionality. To activate your instance with a trial evaluation, or a term or perpetual license, see Licensing.

