|
Home > |
|---|
This section is HSM application partition setup for PED Authenticated HSMs. The activities in this section are required in these circumstances.
•if you just initialized the HSM for the first time and must now create your first application Partition, or
•if you have deleted an HSM Partition and wish to create a new one to replace it.
At this point, the HSM should already:
•have its HSM SO and its Cloning Domain assigned ( see About Initializing a PED-Authenticated HSM ).
Within the HSM, separate cryptographic work-spaces must be initialized and designated for client operations. A workspace, or Partition, and all its contents are protected by encryption derived (in part) from its authentication. Only a Client that presents the proper authentication is allowed to see the Partition and to work with its contents.
In this section, you will:
•Decide the type of application partition to create
•Create an HSM application partition
1.To create HSM
Partitions, you must login to the HSM as HSM Security Officer or SO.
Ensure that the PED is connected to the PED port on your HSM host , and that
the PED is powered on and "Awaiting command..."
Or, ensure that you have set up a Remote PED connection, and the PED is ready (see Installing and Configuring a SafeNet Remote PED and Configuring Remote PED).
2.At the command prompt, type the login command.
For HSM with pre-6.22.0 firmware
lunacm:> hsm login
For HSM with version 6.22.0 or newer firmware
lunacm:> role login -name SO
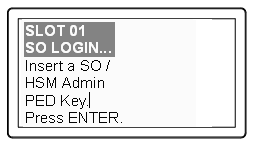
3.Authenticate
as HSM SO:
The PED prompts for the blue PED Key
Provide the blue HSM Admin PED Key that has been imprinted (initialized) for this HSM.
If you had set a PED PIN, you are prompted
for that, as well.
4.At this point, you are about to create an application partition. The options are:
a.a legacy-style partition old firmware
- HSMs with firmware earlier than 6.22.0 (only legacy partitions possible),
- the HSM SO owns and administers the partition
- the remaining partition configuration steps are carried out at the command line, as you have been doing to this point - go to Create a PED Authenticated Legacy-style Application Partition (f/w pre-6.22.0)
b.a legacy-style partitionnewer firmware
- HSMs with f/w 6.22.0 or newer without PPSO capability installed (only legacy partitions possible),
or HSMs with f/w 6.22.0 or newer, with PPSO capability installed, but you choose to create a legacy partition, rather than a PPSO partition
- the HSM SO owns and administers the partition
- the remaining partition configuration steps are carried out at the command line, as you have been doing to this point - go to Create a PED Authenticated Legacy-style Application Partition (f/w 6.22.0 or newer)
c.a PPSO or Per-Partition SO partition
(optional in HSMs with firmware 6.22.0 or newer, and with the PPSO capability installed),
- each partition has its own SO, and the HSM SO has no access other than to delete the application partition
- go to HSM SO Configures PED-authenticated Partition with SO, Local to Client
If you don't remember whether you are logged in as HSM SO, you can use the hsm showinfo command to find out:
lunacm:> hsm showinfo
Partition Label -> mypcie6
Partition Manufacturer -> Safenet, Inc.
Partition Model -> K6 Base
Partition Serial Number -> 150022
Partition Status -> OK
Token Flags ->
CKF_RESTORE_KEY_NOT_NEEDED
CKF_PROTECTED_AUTHENTICATION_PATH
CKF_TOKEN_INITIALIZED
Slot Id -> 4
Tunnel Slot Id -> 5
Session State -> CKS_RW_PUBLIC_SESSION
Role Status -> none logged in (alternatively could show "SO logged in")
Token Flags ->
TOKEN_KCV_CREATED
Partition OUID: 0000000000000000064a0200
Partition Storage:
Total Storage Space: 262144
Used Storage Space: 0
Free Storage Space: 262144
Object Count: 0
Overhead: 9280
Firmware Version -> 6.22.0
Rollback Firmware Version -> 6.21.0
RPV Initialized -> Yes
HSM Storage:
Total Storage Space: 2097152
Used Storage Space: 2097152
Free Storage Space: 0
Allowed Partitions: 1
Number of Partitions: 1
*** The HSM is NOT in FIPS 140-2 approved operation mode. ***
License Count -> 9
1. 621000026-000 K6 base configuration
1. 620127-000 Elliptic curve cryptography
1. 620114-001 Key backup via cloning protocol
1. 620109-000 PIN entry device (PED) enabled
1. 621010358-001 Enable a split of the master tamper key to be stored externally
1. 621010089-001 Enable remote PED capability
1. 621000021-001 Performance level 15
1. 621000079-001 Enable Small Form Factor Backup
1. 621000099-001 Enable per-partition Security Officer
Command Result : No Error
lunacm:>