Known and Resolved Issues
The following table lists known issues in all released versions of the Luna HSM firmware
| Issue | Synopsis | ||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| LUNA-15696 | Problem: When trying to add a high number of members to an HA group, approximately eight, sometimes the addmember command throws an error CKR_DATA_INVALID. Workaround: Restart LunaCM. |
||||||||||||||
| LUNA-15528 | Problem: Universal Client 10.3 does not support Luna Backup HSM (G5) backup and restore for 6.0.8 firmware. Workaround: Use previous Client versions or use Luna Backup HSM (G7). |
||||||||||||||
| LUNA-15461 | Problem: CKR_PED_ERROR when switching the PED between different HSMs Workaround: The error occurs on first login after switching to different HSM; redo the login to clear the error. |
||||||||||||||
| LUNA-15389 | Problem: Backup: upgrading Luna Backup HSM (G5) containing a large number of objects to firmware 6.28.0, fails at driver timeout Workaround: Power cycle the Luna Backup HSM (G5). |
||||||||||||||
| LUNA-15375 | Problem: Callback Service (cbs) stops transferring audit log data from Network HSM to appliance hard disk Workaround: Perform the audit log tar and clean to remove the file from the system, The logs can be SCP'd off the appliance . |
||||||||||||||
| LUNA-14728 | Problem: Unable to compile Luna drivers in RHEL/CentOS 8.2 DMA remapping is now disabled by default on Red Hat Enterprise Linux 8 Workaround:None |
||||||||||||||
| LUNA-14671 |
Problem: Needed to remove DSA Key length 1024, which is weak and could present a security issue |
||||||||||||||
| LUNA-14571 |
Problem: Memory leak issue in luna client 10.1 with suse linux. Workaround: FIXED in Release 7.7.0 |
||||||||||||||
| LUNA-14516 |
Problem: User Interface issue: After factory reset of Luna Backup HSM (G5) "-iped " prompt is missing from LunaCM "hsm init" command. Workaround: Restart LunaCM; the "-iped" parameter reappears. |
||||||||||||||
| LKX-6075 |
Problem: First login after audit login lock timeout expires fails. Subsequent login passes. Workaround: Just try again after lockout clears |
||||||||||||||
| SH-4987 |
Problem: When creating a self-signed certificate with cmu selfsigncertificate, additional characters are added to the specified serial number. Workaround: None. Use cmu getattribute to note the actual serial number assigned to the certificate. |
||||||||||||||
| LUNA-14009 |
Problem: When running cmu verifyhsm, the interactive mode does not prompt for a challenge string, and fails with "Parameters missing". Workaround: Always specify a challenge string: cmu verifyhsm -challenge "<string>" |
||||||||||||||
| LUNA-13907 |
Problem: When requesting a certificate (cmu requestcertificate) using the wrong attribute to specify the private key, an incorrect error message is thrown ("Signing key not found"). Workaround: Use -privatehandle to specify a key on a Luna partition, and -privateouid on a Luna Cloud HSM service. |
||||||||||||||
| LUNA-13780 |
Problem: Importing a DSA public key to a partition using cmu import fails with "Certificate invalid" error. Workaround: None. |
||||||||||||||
| LUNA-13762 |
Problem: The Windows Device Manager sometimes displays incorrect driver version 10.2.0.1 for Luna PCIe HSM and Luna Backup HSM. Workaround: Can be safely ignored. The correct driver version is 10.2.0.111. |
||||||||||||||
| LUNA-13761 |
Problem: On Linux clients, when running cmu selfsigncertificate with no arguments specified, cmu fails to prompt the user for the relevant object handles/OUIDs, even if multiple valid keypairs exist on the partition. Workaround: Always specify the object handles/OUIDs of the desired keypair using -publichandle and -privatehandle or -publicouid and -privateouid. |
||||||||||||||
| LUNA-13144 |
Problem: Using Luna HSM Client 10.2.0, some of the new mechanisms available in Luna firmware 7.4.2 appear in LunaCM and ckdemo as "Unknown Mechanism Type". They are listed correctly in multitoken. Workaround: In the Luna API, you can always call mechanisms by name or by vendor code. The unknown mechanisms are listed by vendor code below:
|
||||||||||||||
| LUNA-12822 |
Problem: CKDEMO option (39) Get OUID reports object OUIDs with extra zeroes appended. Workaround: Use option (24) Get Attribute to view the correct OUID. |
||||||||||||||
| LUNA-12471 |
Problem: In LunaProvider, some operations prohibited in FIPS mode (insufficient key size, for example) fail with an unhelpful NULL error. Workaround: Consult documentation for permitted FIPS mode operations. |
||||||||||||||
| LGX-2032 |
Problem: The Luna Backup HSM (G7) driver fails to uninstall on Windows, causing subsequent client install/uninstall issues. Workaround: If you encounter this issue, contact Thales Customer Support (Known and Resolved Issues). |
||||||||||||||
| LUNA-11724 |
Problem: When setting up a DPoD Luna Cloud HSM service on Windows, running the setenv script by right-clicking and selecting "Run as Administrator" causes the operation to fail with the error: The argument `setenv.ps1` to the -File parameter does not exist. Provide
Workaround: Run the setenv script in an already-open Administrator command prompt. On Windows Server, the command prompt is always opened with Administrator privileges. |
||||||||||||||
| LUNA-11616 |
Problem: If the client fails to resolve the DPoD service's DNS hostname, other client slots fail to load in LunaCM. Workaround: Ensure that your DNS network is stable before deploying a Luna Cloud HSM in an HA group. Ideally, configure multiple DNS nameservers for failover. Resolved: Fixed in Luna HSM Client 10.2.0. |
||||||||||||||
|
LGX-1886 LGX-1306 |
Problem: The output for lunacm:> hsm showinfo displays the Luna Backup HSM (G7) part number as "Not Available". Workaround: None. Resolved: Fixed in Luna Backup HSM (G7) firmware 7.7.1. |
||||||||||||||
| LUNA-11448 |
Problem: Occasionally, after uninstalling the client software, client binaries remain in the installation directory. Workaround: These can be safely deleted. To keep your configuration when updating to a new client version, do not delete the following files/directories: >/cert >/PedClient_service >/softtoken >crystoki.ini/Chrystoki.conf |
||||||||||||||
| LUNA-11447 |
Problem: If an application running against an HA group fails over to the Luna Cloud HSM member and the DNS hostname does not resolve, a segmentation fault can occur. Workaround: Ensure that your DNS network is stable before deploying the Luna Cloud HSM service in an HA group. Ideally, configure multiple DNS nameservers for failover. Resolved: Fixed in Luna HSM Client 10.2.0. |
||||||||||||||
| LUNA-11367 |
Problem: On Solaris, attempting to perform operations on an HSM in Secure Transport Mode returns an unhelpful error (CKR_UNKNOWN) instead of the correct CKR_CMD_NOT_ALLOWED_HSM_IN_TRANSPORT. Workaround: Refer to the documentation for instructions on recovering the HSM from STM. |
||||||||||||||
| LUNA-11363 |
Problem: When using an HA group made up of Luna STC partitions and a Luna Cloud HSM service and restarting the STC service, login to another STC partition in the same session can fail with an error (CKR_STC_NO_CHANNEL). Workaround: Restart LunaCM. |
||||||||||||||
| LGX-1844 |
Problem: Luna Backup HSM (G7) does not appear as a slot in LunaCM if ShowAdminTokens = no in the Luna HSM Client configuration file (Chrystoki.conf/crystoki.ini). Workaround: Edit the configuration file to set ShowAdminTokens = yes. Resolved: Fixed in Luna HSM Client 10.2.0. |
||||||||||||||
| LUNA-11269 |
Problem: When a Luna Cloud HSM service is a member of an HA group, some events (such as the Luna Cloud HSM service member being dropped and its connection then re-established) are not recorded in the HA log file. Workaround: None. |
||||||||||||||
| LUNA-11229 |
Problem: Occasionally, changing the active slot in LunaCM results in objects not being correctly displayed by lunacm:>partition contents, even though the Crypto Officer remains logged in on that slot. The 'Crypto Officer' is currently logged in. Looking for objects
Workaround: Log in as Crypto Officer again and retry lunacm:>partition contents. |
||||||||||||||
| LUNA-13176 |
Problem: On Linux, selecting only the PEDserver component during client installation installs all available client components. Workaround: Uninstall the undesired components. |
||||||||||||||
| LUNA-11141 |
Problem: If you installed the Windows client downloaded from the DPoD portal, LunaCM returns a missing DLL error (MSVCP140.dll). Workaround: Use the Luna HSM Client 10.1 installer, which includes all prerequisite files. Otherwise, refer to the DPoD documentation (Services > Luna Cloud HSM Services > Luna Cloud HSM service supported client platforms) for prerequisites to install manually. |
||||||||||||||
| LUNA-11117 |
Problem: When using a Luna Cloud HSM service with an Entrust integration on Windows, the entsh session times out after 4 minutes (this does not occur on Linux). Workaround: Log in to the Entrust session again and rerun the command. |
||||||||||||||
| LUNA-13175 |
Problem: Code comment mistakenly appears in the output for some vtl commands: Note: Aux cert printing function deprecated in OpenSSL 1.1.0 - reimplement
Workaround: Message can be safely ignored. |
||||||||||||||
|
LUNA-11017 SH-4282 |
Problem: When using an HA group made up of Luna partitions and a Luna Cloud HSM service in FIPS mode, if the Luna partition is unavailable, ms2luna fails to migrate keys from the Microsoft CA to the HA slot. Workaround: Ensure that all HA group members are available before you run ms2luna. |
||||||||||||||
| LUNA-10992 |
Problem: When using an HA group made up of Luna partitions and a Luna Cloud HSM service in FIPS mode, if the Luna partition is unavailable, 3DES keygen fails with CKR_MECHANISM_INVALID error. Workaround: Ensure that all HA group members are available before initiating 3DES keygen. |
||||||||||||||
| LUNA-10985 |
Problem: With appliance software 7.4.0 installed, RSA sign/verify operations show decreased performance when less than 20 threads are used. Workaround: None. |
||||||||||||||
| SH-4194 |
Problem: If you perform cmu getpkc on a Luna Cloud HSM service to confirm a public key, the operation can sometimes fail. Workaround: To confirm your key pair's origins and security in an HSM, run CKDemo's Display Object (27) function. If the CKA_NEVER_EXTRACTABLE attribute is present, this confirms that the private key was created in the HSM and never extracted. |
||||||||||||||
| LGX-1484 |
Problem: Running lunash:>token backup show with an uninitialized Luna Backup HSM (G7) connected returns a confusing message: Error: This is a Luna SA with Password Authentication but
the token attached is for a Luna SA with
Trusted Path Authentication.
Workaround: This message can be safely ignored. The Backup HSM can be initialized as desired. |
||||||||||||||
| LUNA-10803 |
Problem: Luna Network HSM LCD can freeze on reboot - periodic update of displayed messages ceases (i.e., stuck on a single message), and lcdController messages appear in system log messages. Software-initiated restart/reboot does not fix the problem. Attempting to stop/start the LCD service does not fix the problem. This is a rare, intermittent issue, and does not affect other HSM appliance functions. Workaround: If the LCD freezes, perform a hard shutdown and restart using the appliance's power switch, or disconnecting and reconnecting the power cable (both power cables on dual-power-supply models). Wait about 30 seconds between power off and power on. |
||||||||||||||
|
LUNA-10348 |
Problem: Multiple issues related to network default gateway. Resolved: Fixed in Luna Network HSM appliance software 7.3.3. |
||||||||||||||
| LGX-1295 |
Problem: When using a one-time password to initialize the Luna Backup HSM (G7)'s RPV (orange PED key), including the -pwd option before -ip or -hostname causes the command to fail. Workaround: Specify the -ip or hostname before the -pwd option in the command: lunacm:>ped connect -ip <IP_address> -pwd Resolved: Fixed in Luna HSM Client 10.2.0. |
||||||||||||||
|
LUNA-9040 |
Problem: With bonding interface configured, unable to reach through SSH after reboots. Bonding interface MAC address changing randomly after reboots. Resolved: Fixed in Luna Network HSM appliance software 7.3.3. NOTE: Resolution not confirmed but bonding interface MAC address no longer changes after reboots. |
||||||||||||||
| LGX-1203 |
Problem:Running slot list after disconnecting and reconnecting the G7-based Backup HSM may cause LunaCM to exit. For example: 1.Connect the G7-based Backup HSM and let it complete the boot sequence. 2.Disconnect it after it has completed the boot sequence and run slot list. The backup HSM is not listed. 3.Reconnect the backup HSM and let it complete the boot sequence. 4.Run slot list. LunaCM exits. Workaround: Do not disconnect the G7-based Backup HSM during a LunaCM session, unless you are finished using it. Resolved: Fixed in Luna HSM Client 10.2.0. |
||||||||||||||
| LUNA-8881 |
Problem: Application cannot change CKA_EXTRACTABLE default value via JSP. Workaround: None. Resolved: Fixed in Luna HSM Client 10.1.0. |
||||||||||||||
|
LUNA-8833 LUNA-8810 |
Problem: Minimal Luna HSM Client tar file has an additional character that could affect customer scripts. Workaround: Change filename from LunaClient-Minimal-v7.4.0-226.x86_64.tar to LunaClient-Minimal-7.4.0-226.x86_64.tar before running scripts. Resolved: Fixed in Luna HSM Client 10.1.0. |
||||||||||||||
| LUNA-8789 |
Problem: Restricting SSH traffic to an IPv6-configured ethernet port with lunash:>sysconf ssh device <eth#> still allows SSH connection via IPv4. Workaround: None. |
||||||||||||||
| LUNA-8782 |
Problem: Attempting to change a destructive HSM policy to an already-existing setting (0 to 0 or 1 to 1) results in partitions being renamed to "unknown1", "unknown2", etc. The partitions remain intact and are usable by clients. Workaround: Ensure that your policy change commands are correct. If you did not mean to change the destructive policy and want to keep your existing partitions, you can rename them with lunash:>partition rename. |
||||||||||||||
| LUNA-8780 |
Problem: One-step NTLS fails when the appliance's SSH host key changes or when connecting for the first time. Workaround: Run lunacm:>clientconfig deploy with the -verbose option, and manually enter "y" when PuTTY prompts you to update the cached SSH key. Resolved: Fixed in Luna HSM Client 10.1.0. |
||||||||||||||
|
HAPP-267 LUNA-8756 |
Problem: An FM-ready Luna Network HSM with appliance software version 7.4.0 and HSM firmware 7.0.3 incorrectly displays "Non-FM" in the output from lunash:>hsm show. LunaCM slot information for a partition on this HSM correctly displays "FM Ready". Workaround: Ignore the incorrect output. You must upgrade the HSM firmware to 7.4.0 to use FMs. Resolved: Fixed in Luna Network HSM appliance software 7.7.0. |
||||||||||||||
| LUNA-8760 |
Problem: Registering an IPv6 NTLS client with REST API by POSTing to /api/lunasa/ntls/clients fails with an Workaround: None. Register NTLS clients with LunaSH to avoid this issue. Resolved: Fixed in REST API 9.0.0, included with Luna Network HSM appliance software 7.7.0. |
||||||||||||||
| LUNA-8758 |
Problem: Command output of vtl examineCert and vtl fingerprint are reversed. Workaround: None. Use each command to view the other's output. Resolved: Fixed in Luna HSM Client 10.1.0. |
||||||||||||||
| LUNA-8739 |
Problem: On a 10G-capable appliance, when a 1G ethernet bond is active, lunash:>sysconf config factoryreset produces an incorrect error:
Workaround: The bond is actually reset and this error can be safely ignored. |
||||||||||||||
|
LKX-5745 LUNA-8695 |
Problem: When a Remote PED connection times out, lunacm:>ped connect and lunacm:>ped get indicate that there is an active PED connection, but operations requiring PED authentication produce an error (CKR_CALLBACK_ERROR). Workaround: Run lunacm:>ped disconnect before ped connect or ped get. |
||||||||||||||
| LUNA-8620 |
Problem: NTLS failover on 10G optical ports (bond0) sometimes fails. Workaround: None. Troubleshooting: Luna Network HSM supports active-backup bonding mode only. This mode does not require any specific configuration of the switch. If this problem (Bond0 failover unsuccessful) is encountered, we recommend to: 1.Trace the packet in the network to ensure that the network interface in the Luna Network HSM is discovered properly. 2.Ensure that ARP entry is not incorrectly cached in the network. Such problem could be resolved through manual ping-out from the appliance (network ping command). To execute such command, the operator must directly connect to the Luna Network HSM through the serial port. |
||||||||||||||
| LKX-5545 |
Problem: When simultaneously running a combination of FM and non-FM applications with the HSM, an error: Workaround: Restart the HSM to clear the error ( |
||||||||||||||
| LGX-1149 |
Problem: When backing up objects to a G7-based Backup HSM from user partitions hosted on HSMs running older firmware, differences in the size of the metadata associated with the objects may cause the backup partition to become full before all of the objects are backed up, resulting in the following error message before all of the objects have been backed up: <CKR_CONTAINER_OBJECT_STORAGE_FULL> Workaround: If you receive this message when backing up a user partition to a G7-based Backup HSM, use the LunaCM partition resize command to resize the backup partition so that it has enough space to accommodate the remaining objects, then use the partition archive backup command with the -append option to add the skipped objects to the backup. Resolved: Fixed in Luna HSM Client 10.2.0. |
||||||||||||||
| LUNA-8566 |
Problem: If a tamper state exists on the HSM, the appliance re-image procedure fails without providing a reason. Workaround: Clear any tamper state before executing lunash:>sysconf reimage start. |
||||||||||||||
| LUNA-8619 |
Problem: During HSM initialization, if the PED operation to create the red domain key fails or times out, subsequent attempts to re-initialize the HSM will not prompt you to create the red domain key. Workaround: Zeroize the HSM with lunash:>hsm zeroize before re-initializing. Resolved: Fixed in Luna Network HSM appliance software 7.7.0. |
||||||||||||||
| LUNA-8512 |
Problem: When a client is connected to multiple FM-enabled HSMs, and one HSM goes down for maintenance, is rebooted, or is busy with a long FM process, new FM processes on other HSMs experience a performance slowdown. Existing processes are unaffected. Workaround: None. The slowdown only lasts as long as the HSM is down, rebooting, or busy. |
||||||||||||||
| LKX-5396 |
Problem: When creating an RSA key using CKDEMO, the user is mistakenly prompted for the Derive attribute (RSA key derivation is not allowed). Workaround: None. The value entered is dropped and can be safely ignored. Resolved: Fixed in Luna HSM Client 10.1.0. |
||||||||||||||
| LUNA-8348 |
Problem: When adding a DNS server using REST API, configured port bonds are broken. If there is no other ethernet interface configured, you must use a serial connection to reconfigure the port bond. Workaround: None. Use LunaSH to configure the DNS servers. |
||||||||||||||
| LUNA-8343 |
Problem: On rare occasions, the appliance fails to load the K7 card driver and the HSM appears unavailable. Workaround: Reboot the appliance. Resolved: Fixed in appliance software version 7.3.0. |
||||||||||||||
| LGX-1118 | Problem: After creating the orange (Remote PED Vector) key for a G7-based backup HSM using the single-session, one-time password authenticated PED connection that is used to create the key, the PED prompts for the one-time password when you end the session using ped disconnect. Workaround: You can ignore the prompt. The PED session is disconnected properly by pressing the Enter key on the PED, without entering the password. |
||||||||||||||
| LKX-5353 |
Problem: When a Remote PED connection times out, lunacm:>role login fails with a confusing error (CKR_FUNCTION_FAILED). Workaround: Run lunacm:>ped disconnect before ped connect. |
||||||||||||||
| LKX-5351 |
Problem: When partition policy 29: Perform RSA signing without confirmation is set to 0 (OFF), all RSA sign operations fail with an error (CKR_DATE_LEN_RANGE). Workaround: If you use RSA signing, do not turn off partition policy 29. |
||||||||||||||
| LKX-5263 |
Problem: When audit logs fill up the HSM memory, HSM functions continue when they should be halted until audit logging is properly configured. Affects FM log entries only. Workaround: Configure audit logging on the HSM as described in documentation to prevent HSM memory from filling up. |
||||||||||||||
| LKX-5259 |
Problem: FM Capability license can be applied on non-FM-ready hardware. Workaround: Ensure your hardware is FM-ready before applying an FM license to the HSM. |
||||||||||||||
| LUNA-7979 |
Problem: Updating the appliance software resets SSH port info to default value 22, causing loss of SSH connection. Workaround: Reconnect SSH by specifying port 22, or connect to appliance via serial port to reset SSH settings. Resolved: Fixed in appliance software version 7.4.0. |
||||||||||||||
| LUNA-7791 |
Problem: REST API DELETE /api/lunasa/ntp/servers or DELETE /api/lunasa/ntp/servers/<default local ntp server addr> deletes default NTP server. Resolved: Fixed in Luna Network HSM appliance software 7.3.1. Default NTP server can no longer be deleted. |
||||||||||||||
| LUNA-7436 |
Problem: Encrypt operations using DES3_CBC_PAD and specifying a NULL buffer fail (CKR_BUFFER_TOO_SMALL). Workaround: Manually specify a buffer size for these operations. |
||||||||||||||
|
LUNA-7585 LUNA-7533 |
Problem: Java DERIVE and EXTRACT flag settings for keys injected into the HSM were forced to "true" in the JNI, which overrode any values passed by applications via Java. Resolved: Fixed in Luna HSM firmware 7.3.0 and Luna HSM Client 7.3.0. |
||||||||||||||
| LUNA-7499 |
Problem: Private BIP32 Key Injection (combination of private key encryption and unwrapping operations) was not implemented in Luna 7.3. Resolved: The call has been included; requires Luna HSM firmware 7.4.0 and Luna HSM Client 7.4.0. |
||||||||||||||
| LKX-4868 |
Problem: On a 64-bit client operating system, running multitoken with different BIP32 modes against an STC HA virtual slot causes multitoken to fail with an error (CKR_TOKEN_NOT_PRESENT). Workaround: Do not use BIP32 modes with STC HA groups; use NTLS instead. |
||||||||||||||
| LKX-4852 |
Problem: Reset timestamp displayed when reporting metrics via LunaSH or REST can vary, each time the commands are used, by approximately 6s. Workaround: Reset the timers. This causes the value to be written to a file, so that the reported reset time remains constant until the next reset. |
||||||||||||||
| LKX-4817 |
Problem: FM sample applications built on a Windows platform do not automatically locate the Cryptoki library. Workaround: Move or copy the sample .exe to the main Lunaclient directory where the library is located. |
||||||||||||||
| LKX-4776 |
Problem: When running a combination of high-traffic FM and standard Luna applications, a rare SMFS failure can occur. Standard Luna processes are unaffected. Workaround: Erase the SMFS using |
||||||||||||||
| LUNA-7438 |
Problem: When using CKdemo to perform a multipart sign/verify operation with a key that has exceeded its specified usage count, an expected error is returned (CKR_KEY_NOT_ACTIVE). The next sign/verify operation with an active key fails with an unexpected error (CKR_OPERATION_ACTIVE). Workaround: Restart CKdemo and attempt the operation again. |
||||||||||||||
| LUNA-7430 |
Problem: When running commands in some Luna utilities on Windows 10, password characters are duplicated. Workaround: Contact Thales Customer Support. Resolved: Fixed in Luna HSM Client 7.4.0. |
||||||||||||||
| LUNA-7418 |
Problem: When logged in to LunaSH as a custom user, resetting the appliance users to factory condition (lunash:>sysconf config factoryreset -service users) does not delete the currently logged-in user. Workaround: Log in to LunaSH as admin to reset the appliance user configuration. |
||||||||||||||
| LKX-4716 |
Problem: The wrapcomptest sample application hangs if it is used to query a non-FM slot or an invalid slot number. Workaround: Interrupt the hanging application with CTRL+C. Use the correct slot for the FM partition. |
||||||||||||||
|
LUNA-10915 SH-3162 |
Problem: When you delete a key from a Luna Cloud HSM service, CKlog displays an incorrect object handle. Resolved: Fixed in Luna HSM Client 10.1.0. |
||||||||||||||
| LKX-4543 |
Problem: After a firmware update, duplicate entries are produced in the audit logs. These duplicate entries cause log verification to fail with an error (CKR_LOG_BAD_RECORD_HMAC). Workaround: There is no way to avoid the duplicate entries. However, the other entries in the log file can be verified without error. When verifying the logs, specify a range that excludes the duplicate entries: lunash:>audit log verify -file <log_file> -start <first_entry> -end <last_entry> lunacm:>audit verify file <log_file> start <first_entry> end <last_entry> Resolved: Fixed in Luna HSM firmware 7.4.0. |
||||||||||||||
| LUNA-7258 |
Problem: When running cmu commands on Windows 10, password characters are duplicated. Resolved: Fixed in Luna HSM Client 7.3.0. |
||||||||||||||
| LUNA-7164 |
Problem: When a bad remote logging host is added, existing hosts that were functioning correctly stop receiving logs. Workaround: Ensure that all remote logging hosts are reachable and configured correctly before adding them. Resolved: Fixed in Luna Network HSM appliance software 7.4.0. |
||||||||||||||
| LUNA-7074 |
Problem: In LunaCM, when switching the active slot between partitions on different HSMs, ped connect and ped get sometimes report an active Remote PED connection, even though the connection is broken. Authentication commands fail. Workaround: Use ped disconnect on the active slot before switching to a different slot and running ped connect. Resolved: Fixed in Luna HSM Client 7.4.0. |
||||||||||||||
|
LUNA-7000 |
Problem: Using REST API, open application IDs sometimes cause the HSM to stop responding. Resolved: Fixed in REST API 7.0.0, included with Luna Network HSM appliance software 7.3.0. |
||||||||||||||
| LKX-4266 |
Problem: LunaCM incorrectly allows the user to add FM-enabled partitions to the same HA group as non-FM partitions. Workaround: HA groups with a combination of FM and non-FM members are not supported. |
||||||||||||||
| LUNA-4134 |
Problem: When the Luna Network HSM is configured for IPv6 connections, a missing file error is displayed in the output from lunash:>network show ( Workaround: This error can be safely ignored. |
||||||||||||||
| LUNA-4133 |
Problem: NTLS connection fails when the appliance has the default hostname Workaround: Assign a unique hostname to the appliance (lunash:> network hostname <hostname>). |
||||||||||||||
| LKX-4250 |
Problem: CA_DeriveKeyAndWrap does not handle AES_KW, AES_KWP, or AES_CTR mechanisms. Workaround: None. |
||||||||||||||
| LUNA-3683 |
Problem: On Linux clients, when a non-root user attempts to uninstall the Luna HSM Client software, the process fails and the client software remains installed, but " Workaround: Ignore this message and log in as the root user to uninstall the Luna HSM Client software. Resolved: Fixed in Luna HSM Client 7.4.0. |
||||||||||||||
| LUNA-3511 |
Problem: After performing a factory reset, the Audit configuration is reset, and the subsequent HSM zeroization event is not logged. Workaround: None. |
||||||||||||||
| LUNA-3429 |
Problem: Error: pedClient is not currently running error is displayed when trying to connect with PEDserver using lunash:>hsm ped connect, even though the cbs service is shown to be running. Workaround: Restart the cbs service on the appliance. |
||||||||||||||
| LUNA-3423 |
Problem: A failed C_WrapKey call on an STC partition configured for Cloning returns the error CKR_BUFFER_TOO_SMALL, while the same failure on an NTLS Cloning partition returns the error CKR_KEY_NOT_WRAPPABLE. Workaround: If you are checking logs for one of these exact errors, ensure that you search for the error associated with your connection type. |
||||||||||||||
| LUNA-3422 |
Problem: A failed C_WrapKey call on an STC partition configured for Key Export returns the error CKR_BUFFER_TOO_SMALL, while the same failure on an NTLS Cloning partition returns the error CKR_MECHANISM_INVALID. Workaround: If you are checking logs for one of these exact errors, ensure that you search for the error associated with your connection type. |
||||||||||||||
| LUNA-3421 |
Problem: A C_CloseAllSessions call on an STC partition configured for Key Export returns CKR_UNKNOWN, while the same call on an NTLS Key Export partition returns CKR_OK. Workaround: None. |
||||||||||||||
| LUNA-3416 |
Problem: When performing AES encryption on an HA group using AIX and SPARC clients, failover occasionally fails with an error (CKR_TOKEN_NOT_PRESENT). Workaround: None. |
||||||||||||||
| LUNA-3414 |
Problem: One-step Network Trust Link (NTLS) setup fails on Windows with error code CKR_CANCEL when SO Login Enforcement is enabled. Workaround: Use the multi-step NTLS setup procedure to create a connection to the Luna Network HSM appliance. Resolved: Fixed in Luna Network HSM appliance software 7.7.0. |
||||||||||||||
| LUNA-3364 |
Problem:After running sysconf appliance reboot from LunaSH, the appliance occasionally gets stuck with a "Rebooting" message on the LCD screen. Workaround: Remove all power from the appliance (by removing the cable from the power supply units), then reconnect power and restart the appliance. Resolved: Download and install Luna 7 Appliance Reboot Patch 1.0.0 from the Thales Customer Support Portal. The content of this patch is included in Luna Network HSM appliance software 7.7.0. |
||||||||||||||
| LUNA-3343 |
Problem: When using STC in a high traffic or high multi-threaded application scenario, the error CKR_STC_RESPONSE_REPLAYED is occasionally generated and causes subsequent commands to fail. Workaround: Restart the client application, and the error will clear. |
||||||||||||||
| LUNA-3307 |
Problem: In LunaCM, clientconfig deploy (one-step NTLS) fails if the partition name contains spaces. Workaround: Use the multi-step NTLS connection procedure to assign the partition to the client. |
||||||||||||||
| LUNA-3298 |
Problem: When installing Backup HSM and Luna PED drivers from Luna HSM Client software on a host machine with a fresh, non-upgraded version of Windows 10, Windows reports an error with the driver signatures. Workaround: Resolved: Fixed in Luna HSM Client 7.3.0. |
||||||||||||||
| LUNA-3291 |
Problem: When uninstalling the client software and reinstalling in a new file location, ipv6 certificates are not copied from the original location, and NTLS connections are lost. Workaround: Manually copy the certificates from the old client install location to the new one. |
||||||||||||||
| LUNA-3276 |
Problem: On Linux, client software cannot be installed to a directory that includes a space character. If such an install path is specified, the path is cut off at the space (for example, specifying "/luna client/" creates install directory /luna). Workaround: Do not specify an install directory that includes spaces. |
||||||||||||||
| LUNA-3275 |
Problem: When using CKdemo to query an application partition, the Crypto Officer password is entered in visible plaintext. Workaround: None. Resolved: Fixed in Luna HSM Client 7.3.0. |
||||||||||||||
| LKX-3338 |
Problem: On Luna HSM *700 and *750 models, asymmetric digest-and-sign or digest-and-verify mechanisms produce the wrong result when the data length exceeds 64 kB. Resolved: Fixed in Luna HSM firmware 7.2.0 and 7.0.3. |
||||||||||||||
|
LUNA-3254 |
Problem: Calls to CA_OpenApplicationID fail when certain sequences of calls are run, for example: 1.CA_SetApplicationID(x,y) 2.C_OpenSession() 3.C_CloseSession() 4.CA_OpenApplicationID(x,y) Resolved: Fixed in Luna Network HSM appliance software 7.3.0. |
||||||||||||||
| LUNA-3167 |
Problem: Cannot migrate keys using ms2Luna.exe for CSP. Workaround: Copy a version of ms2Luna.exe from an older client package (6.2 or older). Resolved: Fixed in Luna HSM Client 7.3.0. |
||||||||||||||
| LUNA-3126 |
Problem: After running lunash:> hsm ped connect on an uninitialized Luna Network HSM, hsm ped show may incorrectly display Workaround: None necessary; this behavior does not affect the functioning of Remote PED. |
||||||||||||||
| LUNA-3108 |
Problem: If you uninstall Luna HSM Client and reinstall it in a custom directory, HA logging stops working. Workaround: Open crystoki.conf/crystoki.ini and edit |
||||||||||||||
| LUNA-3107 |
Problem: If you uninstall Luna HSM Client and reinstall it in a custom directory, RBS stops working. Workaround: Copy the two certificate files serverkey.pem and server.pem from the original rbs directory to the new rbs directory. |
||||||||||||||
| LUNA-3071 |
Problem: When LunaCM is launched in Luna Minimal Client, an unexpected error is displayed (Error: Failed to initialize remote PED support). Workaround: Edit Chrystoki.conf/crystoki.ini and remove Toolsdir from the Misc section. Resolved: Fixed in Luna HSM Client 7.3.0. |
||||||||||||||
| LUNA-3070 |
Problem: vtl cklog enable/disable command not working if LibUNIX and LibUNIX64 are in different folders. Workaround: Enable cklog manually by editing Chrystoki.conf/Chystoki.ini. Refer to the SDK Reference for details. |
||||||||||||||
| LUNA-3015 |
Problem: Appliance command sysconf config factoryReset does not remove port bonding. Resolved: Fixed in Luna Network HSM appliance software 7.2.0. |
||||||||||||||
| LUNA-2983 |
Problem: CMU Export Public Key - Incorrect formatting of exported key. A public key, exported with command cmu export -handle <handle#> -outputfile <filename> -key has incorrect header and footer text. Workaround: Edit the exported public key file, replacing Resolved: Fixed in Luna HSM Client 7.3.0. |
||||||||||||||
| LUNA-2947 |
Problem: When using Luna Network HSM appliance software 7.2 with earlier Luna HSM Client software, cmu getpkc fails with an error ("Could not retrieve the PKC"). Resolved: Fixed in Luna HSM Client 7.2.0. |
||||||||||||||
|
LUNA-2677 |
Problem: Unable to change CKA_EXTRACTABLE key attribute via Java (LunaProvider/JSP). Workaround: Download and apply the Luna HSM 7.1 Java Patch from the Thales Customer Support Portal. Follow the README instructions to ensure that your Java application sets the appropriate key attributes. Resolved: Fixed in Luna HSM Client 7.2.0. |
||||||||||||||
| LUNA-2663 |
Problem: In LunaSH, hsm firmware upgrade fails with errors (LUNA_RET_UNKNOWN_COMMAND and RC_GENERAL_ERROR) if STC is enabled on the Admin channel. It is then necessary to decommission the HSM in order to update the firmware. Workaround: Disable STC on the Admin channel before updating the HSM firmware. Resolved: Fixed in Luna Network HSM appliance software 7.2.0. If STC is enabled on the Admin channel, the user is prevented from updating the HSM firmware. |
||||||||||||||
| LUNA-2646 |
Problem: One-step NTLS can fail after installing, uninstalling, and reinstalling the Luna HSM Client on Windows. Workaround: Use the multi-step NTLS setup procedure to create a connection to the Luna Network HSM appliance. |
||||||||||||||
| LGX-358 |
Problem: Connecting a Luna Backup HSM (G7) to a USB 3.0 (SuperSpeed) port may result in error messages being displayed by the host operating system. This behavior occurs in both Windows and Linux. For example, in Windows, the following notification may be displayed:
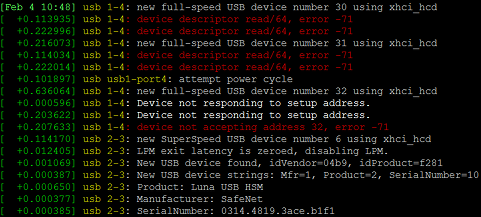
In Linux, messages similar to the following may be displayed (visible with dmesg or in /var/log/messages):
Workaround: You can ignore these messages, as they have no effect on the normal operation of the Luna Network HSM. Resolved: Resolved in Luna Backup HSM (G7) with firmware 7.7.x installed from the factory. Backup HSMs upgraded to firmware 7.7.x still display the messages. |
||||||||||||||
| LUNA-2445 |
Problem: The default maximum length for HA log files is incorrectly set to 40000 bytes, and misreported in LunaCM as 262144 bytes (the intended minimum). This can lead to many small HA log files being rotated frequently. Workaround: Manually set the HA log maximum file size using lunacm:>hagroup halog -maxlength <bytes> the first time you configure HA logging. |
||||||||||||||
| LUNA-2347 |
Problem: Extraneous entry for partitionpolicytemplatepath is present in the MISC section of the Chrystoki.conf. Workaround: Ignore. This entry is not used by Luna 7 policy templates. |
||||||||||||||
|
LKX-3233 LKX-3201 |
Problem: Value for HSM policy 46 (Disable Decommission) cannot be changed. Attempting to change it returns an error (CKR_CONFIG_FAILS_DEPENDENCIES). Workaround: None. Resolved: Fixed in Luna HSM firmware 7.2.0. |
||||||||||||||
| LKX-3204 |
Problem: Implementations of SSL/TLS 1.1 or earlier receive CKR_DATA_INVALID error when attempting to sign data with CKA_RSA_PKCS. Workaround: None. Resolved: Fixed in Luna HSM firmware 7.0.2. |
||||||||||||||
| LUNA-2261 |
Problem: "CKR_DATA_INVALID" on wrap/unwrap with multitoken on AIX and Solaris clients. Workaround: None. |
||||||||||||||
| LUNA-2230 |
Problem: If HSM policy 39 (Allow Secure Trusted Channel) is turned off while STC is enabled on the admin channel, the HSM SO is unable to log in using hsm login. Workaround: If this occurs, exit LunaSH and log in again as the admin user. In general, disable STC on the admin channel (hsm stc disable) before setting HSM policy 39 to 0. Resolved: Fixed in Luna Network HSM appliance software 7.2.0. |
||||||||||||||
| LUNA-2224 |
Problem: When you initialize an STC partition by applying a partition policy template, a confusing error (CKR_TOKEN_NOT_PRESENT) is returned. Workaround: None. |
||||||||||||||
| LKX-3178 |
Problem: When you use an older client, and query partition-level capabilities and policies, the HSM returns incorrect policy numbers Workaround: Use the documentation to get the correct policy numbers. Resolved: Fixed in Luna HSM firmware 7.2.0. |
||||||||||||||
| LUNA-2199 |
Problem: LunaCM occasionally freezes in Windows 2016 when a new slot is created or deleted. Workaround: End the LunaCM instance with Task Manager and restart LunaCM. |
||||||||||||||
| LKX-3159 |
Problem: In LunaCM, hsm information monitor incorrectly reports HSM utilization. Workaround: None. Resolved: Fixed in Luna HSM firmware 7.2.0. |
||||||||||||||
| LUNA-2081 |
Problem: Multipart AES_KW operations on non-block-sized-data returns incorrect error code CKR_DEVICE_ERROR. Workaround: None. Resolved: Fixed in Luna HSM Client 7.2.0. |
||||||||||||||
| LUNA-2077 |
Problem: On Windows, one-step NTLS (lunacm:> clientconfig deploy) is very slow and takes almost four minutes to complete the NTLS connection setup. Workaround: None. Resolved: One-step NTLS performance has been improved in Luna HSM Client 7.2.0. |
||||||||||||||
| LUNA-2022 |
Problem: When attempting to restrict SSH access to an individual ethernet device (eth#) that is configured within a port bond (bond0 or bond1), a confusing error is returned. Usage: /bin/grep [OPTION]... PATTERN [FILE]... Try '/bin/grep --help' for more information. Warning: SSH is already restricted to the specified ip address / ethernet card. No changes made. Workaround: This operation is expected to fail. With port bonding configured, restrict SSH to one of the port bonds instead. |
||||||||||||||
| LUNA-2007 |
Problem: Unable to establish NTLS connection using the one-step NTLS procedure on Solaris x86 when there are more partitions(10~15). Workaround: Use the multi-step NTLS connection procedure on a Solaris client. |
||||||||||||||
| LUNA-1927 |
Problem: Unable to add new member to HA group after removing primary member. Workaround: Manually delete the serial number of the deleted Network HSM's partition from the "VirtualToken00Members" field in the Chrystoki.conf/Crystoki.ini file and then add the new partition to the existing HA group. It is added successfully, and the old entry from the LunaCM HA list is also removed. |
||||||||||||||
|
LKX-3042 LKX-2989 |
Problem: When partition policy 39: Allow start/end date attributes is enabled, all start dates must be later than January 01, 1970. Workaround: Ensure that start date attribute is later than January 01, 1970. Fixed: Fixed in Luna HSM firmware 7.2.0. |
||||||||||||||
| LKX-3184 |
Problem: If HSM policy 39: Enable Secure Trusted Channel has been set to 1 (ON) at any time, attempting a firmware rollback will cause the HSM to fail with an error (Unable to communicate with HSM). Workaround: None. If you are using STC, or have enabled HSM policy 39 in the past, do not roll back the HSM firmware. Resolved: Fixed in Luna HSM firmware 7.2.0. |
||||||||||||||
| LKX-2824 |
Problem: C_DeriveKey does not reject templates that contain CKA_VALUE, and uses the CKA_VALUE that is provided in the external template. Workaround: None. Resolved: Fixed in Luna HSM firmware 7.0.2 and 7.1.0. |
||||||||||||||
| LKX-2812 |
Problem: The HSM reports 3072-bit as the maximum allowed key size for the RSA 186-3 mechanisms (CKM_RSA_FIPS_186_3_AUX_PRIME_KEY_PAIR_GEN and CKM_RSA_FIPS_186_3_PRIME_KEY_PAIR_GEN), when it should report 4096-bit. C_GetMechanismInfo will report 3072 as the maximum size for these mechanisms. If your application uses C_GetMechanismInfo to query the maximum key size, it may prevent 4096 operations from working. Workaround: Ignore the reported limit. 4096-length keys will generate successfully. Resolved: Fixed in Luna HSM firmware 7.0.2. |
||||||||||||||
| LUNA-454 |
Problem: Luna Network HSM appliance user names that begin with a non-alphanumeric character (period, dash, or underscore) may cause issues and/or potential system crashes. Workaround: Always use an alphanumeric character as the first character in the user name when creating appliance user accounts. Resolved: Fixed in Luna Network HSM appliance software 7.1.0. |
||||||||||||||
| LUNA-853 |
Problem: On Linux, the Luna HSM Client software fails to install to a directory with spaces in its name. Workaround: Remove spaces from the directory name before installing the Client. Resolved: Fixed in Luna HSM Client 7.1.0. |
||||||||||||||
| CPP-3404 |
Problem: CMU may crash or report a memory allocation error when using a non-FIPS signing mechanism in FIPS mode. Workaround: Specify a FIPS-approved signing mechanism such as sha256withRSA. |
||||||||||||||
| LUNA-169 |
Problem: In LunaSH, network show displays an incorrect IPv6 Mask prefix. Workaround: None. If set correctly, IPv6 works even though the wrong mask is displayed. Resolved: Fixed in Luna Network HSM appliance software 7.1.0. |
||||||||||||||
| LUNA-264 |
Problem: On Linux, non-root users cannot initialize the STC token or create an STC client identity. Workaround: Start LunaCM as root with sudo ./lunacm. Resolved: Fixed in Luna HSM Client 7.1.0. |
||||||||||||||
|
LUNA-7194 CPP-3326 RAPI-1416 |
Problem: Webserver starts even if no SSL key/cert exists, but is not accessible. Workaround: Generate the SSL key/cert before starting the webserver. Resolved: Fixed in REST API 7.0.0, included with Luna Network HSM appliance software 7.4.0. |
||||||||||||||
|
LUNA-263 |
Problem: On Linux, non-root users cannot configure the RBS server. Workaround: As root, run the following commands: 1.chown -R root:hsmusers /usr/safenet/lunaclient/rbs/ 2.chmod g+w -R usr/safenet/lunaclient/rbs/ Resolved: Fixed in Luna HSM Client 7.1.0. |
||||||||||||||
| LUNA-163 |
Problem: When the HSM audit logs are full, audit login appears to succeed, but the user is not actually logged in and cannot perform operations. Workaround: Clear the audit logs by opening an SSH session as audit, and perform the following steps: 1.Tar the audit logs with the command audit log tarlogs. 2.Transfer the tar file out of the appliance. 3.Clear the audit log files to free up space on the audit log partition with the command audit log clear. Resolved: Fixed in Luna Network HSM appliance software 7.1.0. |
||||||||||||||
| CPP-3261 |
Problem: After performing sysconf config factoryreset, the appliance host name is not reset. Workaround: None. |
||||||||||||||
| CPP-3241 |
Problem: Untarred audit log files are not visible to the user. Workaround: Untarred audit log files will not appear in the list of log files generated by the LunaSH command my file list, but they can still be verified using audit log verify -file <filename> -serialsource <serialnum>. |
||||||||||||||
| CPP-3235 |
Problem: In LunaCM, the partition clone command fails the first time if the Partition SO is logged in to the target slot. Workaround: Run the partition clone command again. The second attempt should be successful. |
||||||||||||||
| LUNA-261 |
Problem: On Linux, non-root users cannot add a new HSM server after CAfile.pem has been created by the root user. Workaround: Use the same user account to create the certificate and register the server. Resolved: Fixed in Luna HSM Client 7.1.0. |
||||||||||||||
| LUNA-166 |
Problem: Running package verify and package update with the -useevp option in LunaSH produces a CKR_SIGNATURE_INVALID error. Workaround: None. Resolved: Fixed in Luna Network HSM appliance software 7.1.0. |
||||||||||||||
| CPP-3191 |
Problem: After rebooting the appliance, occasionally clients cannot see partitions on the first connection attempt. Workaround: Run the vtl verify command again. The second attempt should be successful. |
||||||||||||||
| LUNA-266 |
Problem: In LunaCM, clientconfig deleteserver deregisters the HSM server on the Client, but does not delete the HSM server certificate file from the <LunaClient_dir>/cert/server directory. Attempts to re-register the same server with a regenerated certificate fail. Workaround: Manually delete the certificate from the cert/server directory. Resolved: Fixed in Luna HSM Client 7.1.0. |
||||||||||||||
| CPP-2960 |
Problem: LunaCM hangs on exit on Windows 2016. Workaround: End the LunaCM instance using the Task Manager. |
||||||||||||||
|
LUNA-3352 CPP-2954 |
Problem: The hsmCriticalEvent and hsmNonCriticalEvent counters incorrectly track HSM events. Workaround: None. SNMP hsmCriticalEvent and hsmNonCriticalEvent counters are not implemented in this release and will always remain 0. |
||||||||||||||
|
LUNA-801 CPP-3385 |
Problem: On Windows, a system crash can occur when you disconnect a Luna Backup HSM from the computer while the PedClient service is running. Resolved: Fixed in Luna HSM Client 7.1.0. |
||||||||||||||
| CPP-2925 |
Problem: When the cklog library is configured, an error.txt file containing extraneous messages may be created. Workaround: None. |
||||||||||||||
|
CPP-2820 |
Problem: Luna Network HSM 7 attempts to load K6 driver upon rebooting. Workaround: None. SNMP hsmCriticalEvent and hsmNonCriticalEvent counters are not implemented in this release, and will always remain 0. Resolved: Fixed in Luna Network HSM appliance software 7.1.0. |
||||||||||||||
| RAPI-1248 |
Problem: REST API web client shows wrong logout result. Workaround: Use the Custom I/O to manually log out. Resolved: Fixed in REST API 7.0.0, included with Luna Network HSM appliance software 7.4.0. |
||||||||||||||
| LKX-2634 |
Problem: Cannot back up curve25519 key types to the Luna Backup HSM. Workaround: Use cloning or HA to back up your curve25519 key types to another Luna 7.0 HSM. |
||||||||||||||
| RAPI-1211 |
Problem: In REST API, GET /api/lunasa/hsms may return an empty list. Workaround: Another attempt may return a populated list if an HSM is available. |
||||||||||||||
| LUNA-1592 |
Problem: When trying to run the HALogin.java script, a CKR_UNKNOWN error is returned. Workaround: None. Do not use the HALogin.java sample. |
||||||||||||||
|
CPP-2505 LUNA-132 |
Problem: When configuring a network device for IPv6 using SLAAC or DHCPv6, the IPv6 address is retrieved, but the name server and search domain are not. Workaround: Configure the name server and search domain manually, using the LunaSH command network dns add {-nameserver <ip_address> | -searchdomain <net_domain>}. |
||||||||||||||
| CPP-2380 |
Problem: When running the MiscCSRCertificateDemo.java sample, a null pointer exception occurs. Workaround: None. |
||||||||||||||
| CPP-2368 |
Problem: The hagroup list command returns an error. Workaround: Run the hagroup list command again. The second attempt should be successful. |
||||||||||||||
| RAPI-1096 |
Problem: After modifying the webserver settings the apiversion under /api/lunasa becomes 0. Workaround: Restart the webserver service. |
||||||||||||||
| RAPI-1062 |
Problem: In REST API, POST /auth/logout does not return Access-Control-Allow-Credentials and Access-Control-Allow-Origin in the response headers. Workaround: None. Resolved: Fixed in REST API 7.0.0, included with Luna Network HSM appliance software 7.4.0. |
||||||||||||||
| CPP-2376 |
Problem: On the Backup HSM, the hsm init command with the -iped option fails after hsm factoryreset. Workaround: Run the hsm init command again. The second attempt should be successful. Resolved: Fixed in Luna Backup HSM (G5) firmware 6.27.0. |
||||||||||||||
| LUNA-218 |
Problem: You cannot add a host or network route using the LunaSH network route add command without including the gateway value. Workaround: None. |
||||||||||||||
|
LUNA-1948 CPP-1842 |
Problem: Secure NTP server connections using AutoKey authentication do not work. Workaround: Use Symmetric-Key authentication instead. Resolved: Fixed in Luna Network HSM appliance software 7.1.0. |
||||||||||||||
| LUNA-827 |
Problem: During key wrapping/unwrapping, calling with a NULL data pointer to get the data length causes the key to be used twice, incrementing the key usage count both times. Workaround: Specify a buffer size larger than the keys you intend to wrap/unwrap. |
||||||||||||||
|
LUNA-1585 CPP-3384 |
Problem: After zeroization or factory reset, the STC cipher option is set to NULL_ENC. Output from hsm stc status includes "Cipher Name: No Cipher". Workaround: Run the LunaSH command hsm stc cipher enable -all to enable all available STC ciphers. |
||||||||||||||
| LUNA-3621 |
Problem: REST API partition actions contain actions that should be deprecated. Workaround: Do not call these resources. Resolved: Fixed in REST API 7.0.0, included with Luna Network HSM appliance software 7.3.0. |
||||||||||||||
| CPP-1339 |
Problem: In LunaSH, sysconf config restore does not restore the SSH password for the admin user. If the password is not reset immediately, the admin user will be unable to log in to the appliance in subsequent SSH sessions. Workaround: Use sysconf config clear to reset the admin password to the default. You must do this in the same session that you used to run the sysconf config restore command. |
||||||||||||||
| LUNA-339 |
Problem: Some appliance sensor information is missing or incorrectly reported via SNMP. Workaround: Use the LunaSH command status sensors to obtain this information. |
||||||||||||||
|
LUNA-1681 CPP-1249 |
Problem: Remote backup through TCP/IP via the LunaCM command partition archive backup -slot remote -hostname <hostname> -port <portnum> is not recognized. Workaround: Use RBS to backup partitions remotely. |
||||||||||||||
|
LUNA-1423 CPP-902 |
Problem: DSA SSH keypair is not regenerated by sysconf ssh regenkeypair. Workaround: None. DSA keys are deprecated in OpenSSH due to weakness. Use RSA keys for SSH instead. Resolved: Fixed in Luna Network HSM appliance software 7.1.0. |
||||||||||||||
|
CPP-626 CPP-624 |
Problem: If you zeroize an HSM hosting an HA group member partition, all running cryptographic operations against the HA group fail. Workaround: Remove any member partition from the HA group before zeroizing the host HSM. |
||||||||||||||
|
LUNA-7429 CPP-632 |
Problem: When using CKdemo with HA groups, an Attribute type invalid error is returned. Workaround: If you plan to use HA Groups, change your CKdemo settings to use legacy role logins. To do this, select Role Support from the 98) Options in the OTHERS menu. |
||||||||||||||
| CPP-932 |
Problem: If the configured audit logging directory is not found, the PEDclient service fails with error LOGGER_init failed. Workaround: Ensure that the directory you configure for audit logging exists. |
||||||||||||||
| RAPI-383 |
Problem: REST API does not verify the NTLS client's IP against the certificate. Workaround: None. |