Create a PED Authenticated Legacy-style Application Partition (f/w pre-6.22.0)
This section is HSM Application Partition setup for a SafeNet HSM with PED Authentication, where the partition is to remain under the ownership of the HSM Security Officer.
The activities in this section are required in two circumstances.
•if you just prepared
an HSM for the first time and must now create your first
application Partition, or
•if you have deleted or
zeroized an application Partition and wish to create a new one to replace it.
About Application Partitions on the Initialized HSM
At this point, the SafeNet HSM should already have its Security Officer
assigned.
Within the HSM, a separate cryptographic work-space must be created.
A workspace, or Partition, and all its contents are protected by encryption
derived (in part) from its authentication. Only a User who presents the
proper authentication is allowed to see the Partition and to work with
its contents. That User (or Crypto Officer and Crypto User) and authentication can be separate from the Security
Officer identity, but the application partition is still ultimately owned and administered by the HSM SO, who can modify it at any time.
In this section, you will:
•Create an application Partition
•Set application Partition Policies
(Optional)
These instructions assume that your SafeNet HSM is at a version lower than 6.22.0. The commands available at the SafeNet command line are the traditional ones that have been used with SafeNet HSMs. The outcome of this sequence is the creation of a legacy-style application partition that is owned and managed by the HSM SO and does not have its own independent SO.
If your HSM firmware is at version 6.22.0 or higher, then some of the commands have changed, and are the same as those listed for creation of a PPSO application partition, in another section of this guide. That is, with the newer firmware you can use the newer commands to create either a legacy-style partition or a PPSO partition. With the pre-6.22.0 firmware, you have only the older commands, and you can create only a legacy partition.
For the following procedure, you must have previously initialized the HSM, and logged into the HSM as HSM SO.
Having logged in as HSM SO, you can now use the partition
create command, to create an HSM Partition.
You must supply a label
or name for the new Partition when you issue the command.
lunash:> partition create -partition <name-for-new-Partition>
(The angle brackets “<“ and “>” indicate that you fill in text
of your choice. Do not type the brackets.)
Rules for names and passwords
A partition name or a partition label can include any of the following characters :
!#$%'()*+,-./0123456789:=@ABCDEFGHIJKLMNOPQRSTUVWXYZ[]^_abcdefghijklmnopqrstuvwxyz{}~
No spaces, unless you wish to surround the name or label in double quotation marks every time it is used.
No question marks, no double quotation marks within the string.
Minimum name or label length is 1 character. Maximum is 32 characters.
Valid characters that can be used in a password or in a cloning domain, when entered via LunaSH [1]), are:
!#$%'*+,-./0123456789:=?@ABCDEFGHIJKLMNOPQRSTUVWXYZ[]^_abcdefghijklmnopqrstuvwxyz{}~
(the first character in that list is the space character)
Invalid or problematic characters, not to be used in passwords or cloning domains are
"&';<>\`|()
Valid characters that can be used in a password or in a cloning domain, when entered via lunacm, are:
!"#$%&\'()*+,-./0123456789:;<=>?@ABCDEFGHIJKLMNOPQRSTUVWXYZ[\\]^_`abcdefghijklmnopqrstuvwxyz{|}~
(the first character in that list is the space character)
Minimum password length is 7 characters; maximum is 255 characters in lunash or lunacm.
Minimum domain string length is 1 character; maximum domain length is 128 characters via lunash. No arbitrary maximum domain string length is enforced for domain strings entered via lunacm, and we have successfully input domain strings longer than 1000 characters in testing.
[1] LunaSH on the SafeNet Network HSM has a few input-character restrictions that are not present in LunaCM, run from a client host. It is unlikely that you would ever be able to access, via LunaSH, a partition that received a password or domain via LunaCM, but the conservative approach would be to avoid the few "invalid or problematic characters" generally.
1.Create the application Partition. Type:
lunash:>
partition create -partition myPartition1
(substitute the name of your choice for "myPartition1")
Please ensure that you have purchased licenses for at least this number of partitions: -1
If you are sure you wish to continue then type 'proceed', otherwise type 'quit'
> proceed
Proceeding...
Please ensure that you copy the password from the SafeNet PED and
that you keep it in a safe place.
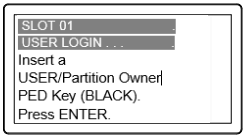
Luna PED operation required to create a partition - use User or Partition Owner (black) PED key.
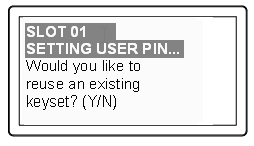
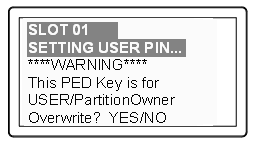
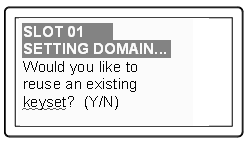
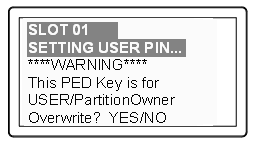
2.The PED inquires if you intend to reuse a pre-existing imprinted black PED Key.
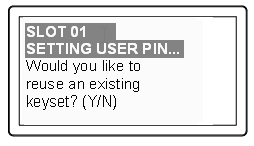
Respond "Yes" if you have a key from another HSM partition with a partition Owner ID already imprinted on it, that you wish to share/reuse. The authentication data on that PED Key will be preserved and used for this partition.
Respond "No" if you have a fresh, never-imprinted key, or if you have a key previously imprinted with an ID that you do not wish to preserve. The authentication data on that PED Key will be overwritten by freshly-generated authentication data.
(See Shared or Group PED Keys of the Administration Guide for more detail)
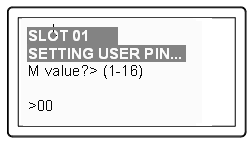
3.The PED requests values for :
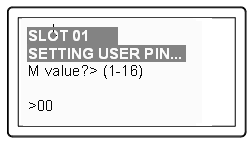
and
(enter "1" for both, unless you wish to invoke MofN split-secret, multi-person access control, then seeUsing MofN of the Administration Guide).
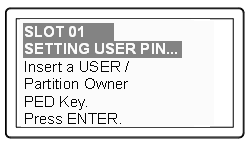
4.The PED then
demands the black Owner PED key with the message
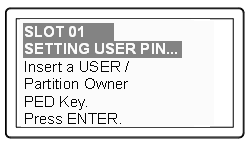
Insert the black HSM Partition Owner PED key [ of course, the unlabeled PED Key is generically black - we suggest that you apply the appropriate color sticker either immediately before or immediately after imprinting the key; before, just to ensure it gets done, or after, as a helpful indicator as to which ones are imprinted (with which secret), and which ones still blank ] and press [Enter]. A unique
Partition Owner PIN is to be imprinted on both the PED key and the HSM
Partition.

5.The PED might continue with:
Decide whether this should be a group PED Key (see Shared or Group PED Keys ), press [YES] or [NO] on the PED keypad, and press [Enter].
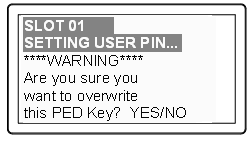
6.This is potentially serious business (if you unintentionally overwrite a PED Key that is needed for other purposes), so SafeNet PED asks one more time if you truly intend to overwrite the key's content.
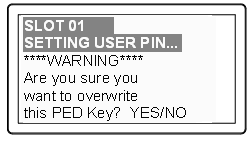
Press [YES] or [NO] on the PED keypad, and press [Enter].
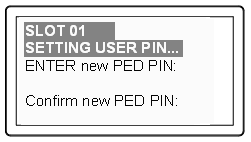
7.Next, you are
asked to provide a PED PIN (optional, see What is a PED PIN? —
can be 4-to-48 digits, or can be no
digits if a PED PIN is not desired).
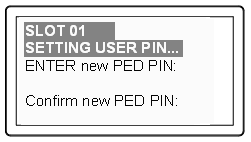
You must press [Enter] to inform the PED that you are finished entering
PED PIN digits, or that you have
decided not to use a PED PIN (no digits entered).
When you provide a PED PIN – even if it is the null PIN (by just pressing
[Enter] with no digits) – the PED requests it a second time, to ensure
that you entered it correctly, as you intended.
Press [ENTER] again.
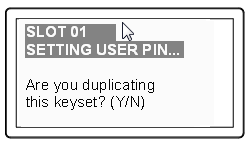
8.You are then
prompted
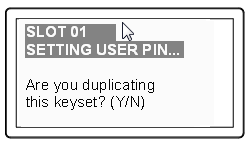
See Duplicating PED Keys.
Respond “No”, if you want the PED to imprint just the one black HSM Admin
PED Key and go on to the next step in creation of the application Partition.
Respond “Yes”, if you want the PED to imprint the first black key and then
ask for more black PED Keys, until you have imprinted (duplicated) as
many as you wish. After each duplicate is made, the PED asks: Would you like to make another duplicate set? Answer "Yes" until you have enough copies, and then press "No".
9.Having created the black key User or Crypto Officer, the HSM needs you to log in as that identity, and prompts:
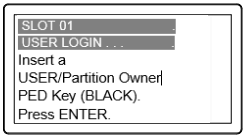
Leave the black key inserted, and press Enter.
At the command-line session, the next part of the sequence is displayed
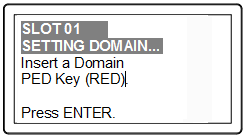
Luna PED operation required to generate cloning domain on the partition - use Domain (red) PED key.
and control once again goes to the SafeNet PED.
10.The PED inquires if you intend to reuse a previously imprinted red Domain PED Key.
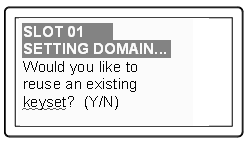
Respond "Yes" if you have a key from another HSM partition with a cloning domain ID already imprinted on it, that you wish to share/reuse.
Respond "No" if you have a fresh, never-imprinted key, or if you have a key previously imprinted with an ID that you do not wish to preserve.
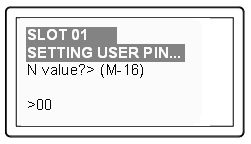
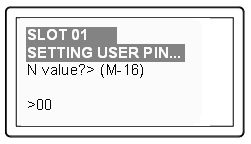
11.As it did for the black key, the PED now requests values for M and N. Again, enter 1 for each unless you wish to invoke MofN splitting of the domain secret.
12.The PED then
prompts for a red Domain PED key with the message
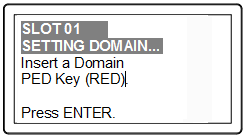
Insert the red HSM Partition Domain PED key [ of course, the unlabeled PED Key is generically black - we suggest that you apply the appropriate color sticker either immediately before or immediately after imprinting the key; before, just to ensure it gets done, or after, as a helpful indicator as to which ones are imprinted (with which secret), and which ones still blank ] and press [Enter]. A
cloning domain is to be imprinted on both the PED key and the HSM
Partition.

13.The PED goes through the same prompts as for the black PED Key. Respond as appropriate.
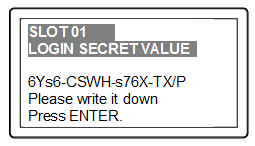
14.SafeNet PED presents the generated partition challenge secret (password), which you must record:
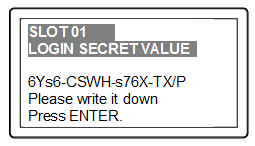
We suggest recording the string in a text editor, which should be more legible than handwriting. The hyphens are inserted for ease of reading, but are not part of the challenge secret. Remove them before pasting the recorded secret.
CAUTION: We recommend that you have at least one backup
set of imprinted PED Keys, stored in a safe place, in case of loss or
damage to the primary keys.
You might wish to adjust "Partition Policies" on page 1 (Optional).
Otherwise, go to Assigning a Client to a Partition.
Partition creation audit log entry
Each time a partition is created, an entry is added to the audit log. Any subsequent actions logged against the partition are identified by the partition serial number that was generated when the partition was created.
Determining the serial number of a created partition from the audit log
An audit log entry similar to the following is generated when a partition is created on the HSM:
5,12/12/17 16:14:14,S/N 150718 session 1 Access 2147483651:2669 SO container operation LUNA_CREATE_CONTAINER returned RC_OK(0x00000000) container=20 (using PIN (entry=LUNA_ENTRY_DATA_AREA))
It is not obvious from this entry what the serial number is for the created partition. This information, however, can be derived from the log entry, since the partition serial number is simply a concatenation of the HSM serial number and the partition container number, which are specified in the log entry, as highlighted below:
5,12/12/17 16:14:14,S/N 150718 session 1 Access 2147483651:2669 SO container operation LUNA_CREATE_CONTAINER returned RC_OK(0x00000000) container=20 (using PIN (entry=LUNA_ENTRY_DATA_AREA))
In the example above, the HSM serial number is 150718 and the partition container number is 20. Note that the partition container number is a three-digit number with leading zeros suppressed, so that the actual partition container number is 020. To determine the partition serial number concatenate the two numbers as follows:
150718020
Use this number to identify the partition in subsequent audit log entiries.