|
Home > |
|---|
For integration with Microsoft Certificate Services and other applications, the LunaCSP.dll library accepts Crypt calls and gives access to token functions (via CP calls) as listed in this section. Key pairs and certificates are generated, stored and used on the Luna HSM.
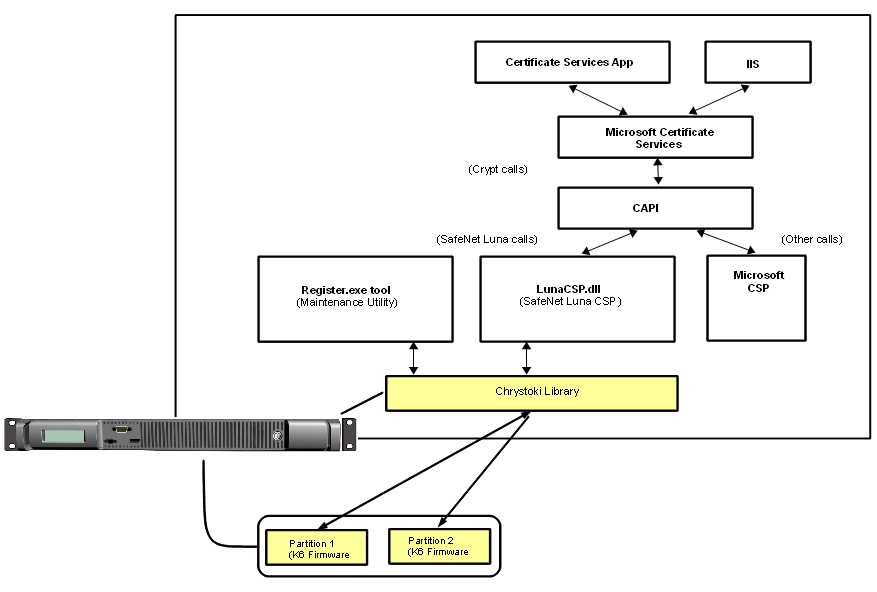
The diagram below depicts the relationship of the SafeNet components to the other layers in the certificate system.
Figure 1: Luna CSP architecture
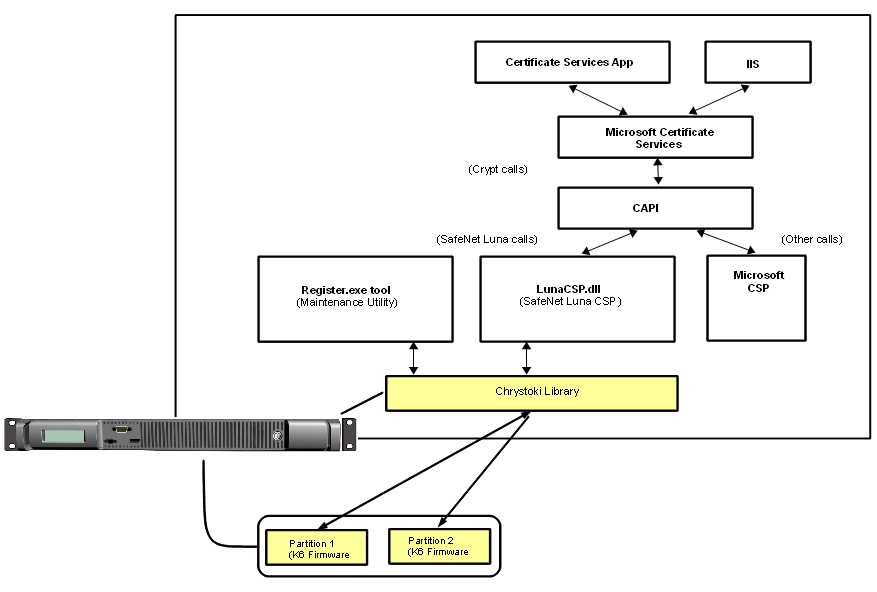
Note, in the diagram, that the SafeNet Luna CSP routes relevant calls through the statically linked Crystoki library to the HSM via CP calls. Other calls from the application layer – those not directed at the token/HSM, and not matching the Luna CSP supported functions (see next section) – are passed to the Microsoft CSP.
The Luna CSP DLL exports the following functions, each one corresponding to an equivalent (and similarly named) Crypt call from the application layer:
•CPAcquireContext
•CPGetProvParam
•CPSetProvParam
•CPReleaseContext
•CPDeriveKey
•CPDestroyKey
•CPDuplicateKey
•CPExportKey
•CPGenKey
•CPGenRandom
•CPGetKeyParam
•CPGetUserKey
•CPImportKey
•CPSetKeyParam
•CPDecrypt
•CPEncrypt
•CPCreateHash
•CPDestroyHash
•CPGetHashParam
•CPHashData
•CPHashSessionKey
•CPSetHashParam
•CPSignHash
•CPVerifySignature
Note: The CPVerifySignature function is able to verify signatures of up to 2048 bits, regardless of the size of the signatures produced by CPSignHash. This ensures that the CSP is able to validate all compatible certificates, even those signed with large keys.
Note: The MSDN (Microsoft Developers Network) web site provides syntax and descriptions of the corresponding Crypt calls that invoke the functions in the above list.
Luna CSP supports the following algorithms:
•CALG_RSA_SIGN [RSA Signature] [256 - 4096 bits]. The CSP uses the RSA Public-Key Cipher for digital signatures.
•CALG_RSA_KEYX [RSA Key Exchange] [256- 4096 bits] The CSP must use the RSA Public-Key Cipher key exchange. The exchange key pair can be used both to exchange session keys and to verify digital signatures.
•CALG_RC2 [RSA Data Securities RC2 (block cipher)] [8 - 1024 bits].
•CALG_RC4 [RSA Data Securities RC4 (stream cipher)] [8 - 2048 bits].
•CALG_RC5 [RSA Data Securities RC5 (block cipher)] [8 - 2048 bits].
•CALG_DES [Data Encryption Standard (block cipher)] [56 bits].
•CALG_3DES_112 [Double DES (block cipher)] [112 bits].
•CALG_3DES [Triple DES (block cipher)] [168 bits].
•CALG_MAC [Message Authentication Code] (with RC2 only).
•CALG_HMAC [Hash-based MAC].
•CALG_MD2 [Message Digest 2 (MD2)] [128 bits].
•CALG_MD5 [Message Digest 5 (MD5)] [128 bits].
•CALG_SHA [Secure Hash Algorithm (SHA-1)] [160 bits].
•CALG_SHA224 [Secure Hash Algorithm (SHA-2)] [224 bits].
•CALG_SHA256 [Secure Hash Algorithm (SHA-2)] [256 bits].
•CALG_SHA384 [Secure Hash Algorithm (SHA-2)] [384 bits].
•CALG_SHA512 [Secure Hash Algorithm (SHA-2)] [512 bits].
Note: If you intend to perform key exchanges between the SafeNet CSP and the Microsoft CSP with RC2 keys, the attribute KP_ EFFECTIVE_KEYLEN must be set to 128 bits. For RC2 and RC4, the salt value of the keys must be transferred by making a call to get the salt value of the original key and to set the salt value of an imported key. This is done with the CryptGetKeyParam( KP_ SALT) and CryptSetKeyParam( KP_ SALT) functions respectively.