Show the Table of Contents
Create a Client Certificate (Windows)
Begin by creating a certificate and private key for the client, using
the vtl command-line interface.
Before you run the vtl
createCert command, run hostname
to view the hostname of your client computer. Then, when you run the vtl createCert -n <clientHostname>
command (example below), be sure to input the hostname exactly
as reported (uppercase/lowercase). If you create a certificate using a
hostname parameter that is not an exact case-match for the client’s hostname,
you may be unable to create an NTLS link.
c:\Program Files\SafeNet\LunaClient\ >vtl createCert -n <clientHostname>
c:\Program Files\SafeNet\LunaClient > vtl createCert -n myClient1
c:\Program Files\SafeNet\LunaClient\cert\client > dir
vtl
myClient1.pem
myClient1Key.pem
After the createCert command, vtl gives the full pathname to the key
and cert files that were generated.
“-n” (name) is the only mandatory item, and must be the client hostname.
Additional
optional parameters can be added. Refer to the Reference section of this
Help for full command syntax and description.
You might need to surround the entire filespec (path and filename) within quotation marks if Windows stumbles at the space between Program and Files.
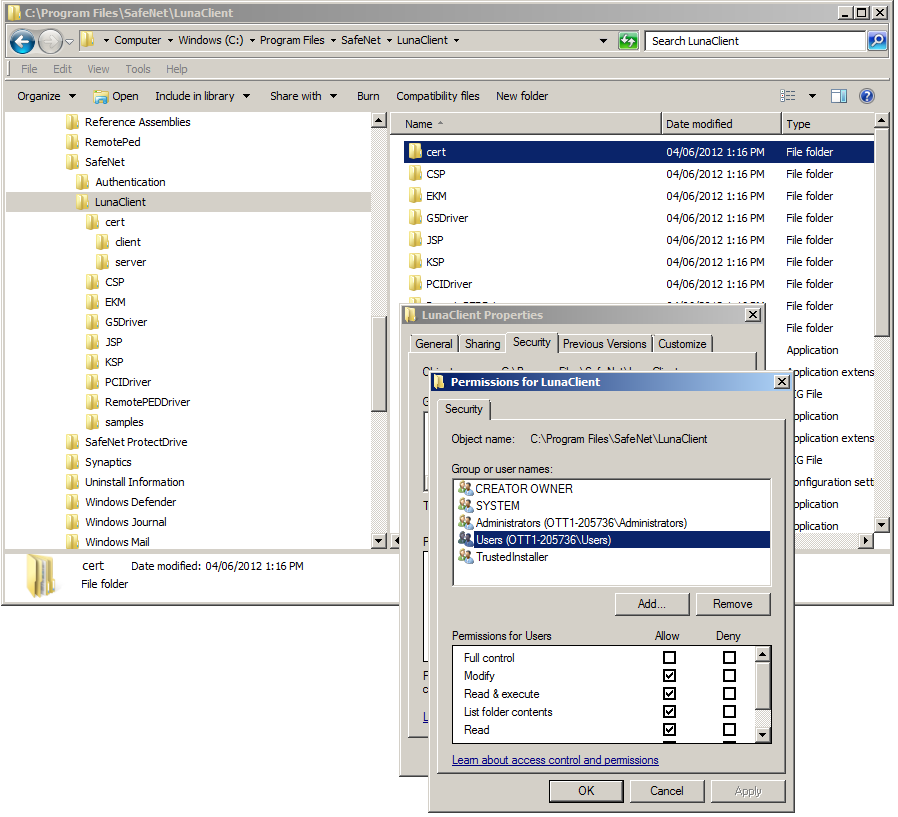
If the operations fail - and you have verified that the commands are typed correctly - then you might lack file permissions in the affected directories. If you lack administrator privileges on your computer, contact your IT department. If you do have the required privileges, then you might need to adjust the permissions for the affected directories [Click Here] (which by default are installed in the protected Windows directory "Program Files").
To adjust the permissions for the directory c:\Program Files\SafeNet\LunaClient\, right-click that directory. In the resulting context menu, select Properties, and in the ensuing dialog select the "Security" tab. Choose the appropriate user or group and adjust as needed. Then repeat the commands in the steps above, which should now work as expected.
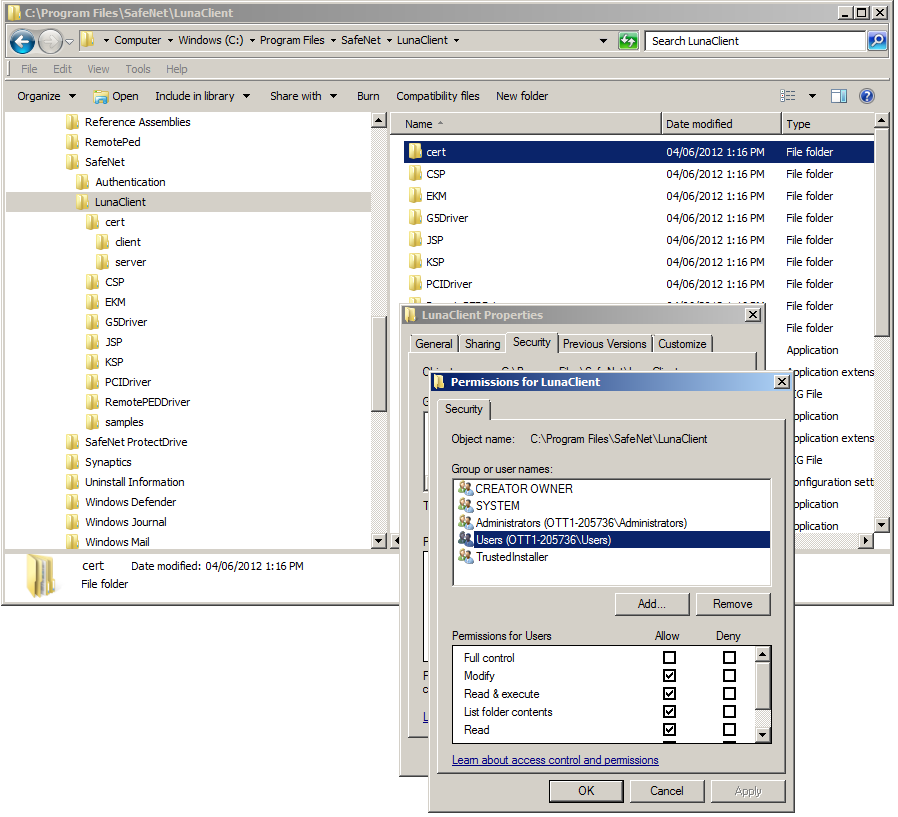
The appearance might vary slightly for different Windows versions. If the permissions change does not propagate to subdirectories, then you might need to repeat the process for the "cert" subdirectory and for the "client" and "server" subdirectories.
 If you are working without DNS, then supply the client IP numerically,
instead:
If you are working without DNS, then supply the client IP numerically,
instead:
c:\Program Files\SafeNet\LunaClient\>vtl createCert -n
<clientIPaddress>
In this case, the key and cert files are created with the filename being the IP address of the Client.
In the createCert
command, provide only the unqualified hostname, rather than the fully
qualified hostname.
Next, "Export a Client Cert to an HSM Appliance (Windows)". This is the other half of the certificate exchange that creates the secure NTLS link.
Show the Table of Contents