![]()
![]()
This section is HSM Partition setup for PED (Trusted Path) Authentication. The activities in this section are required in these circumstances.
About HSM Partitions on the Initialized HSM
At this point, the HSM appliance should already:
Within the HSM, separate cryptographic workspaces must be initialized and designated for clients. A workspace, or Partition, and all its contents are protected by encryption derived (in part) from its authentication. Only a Client that presents the proper authentication is allowed to see the Partition and to work with its contents.
In this section, you will:
First, Establish a Connection to your HSM Appliance
Then, Login as HSM Admin / SO
HSMsh:> hsm login
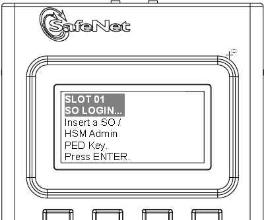
You must provide the blue HSM Admin PED Key that has been imprinted (initialized) for this HSM.
If you had set a PED PIN, you are prompted
for that, as well.
If you fail three consecutive login attempts as HSM Admin (also called SO), the HSM is zeroized and cannot be used — it must be re-initialized. Re-initializing zeroizes the HSM contents. Zeroizing destroys all key encryption material. Please note that the HSM must actually receive some information before it logs a failed attempt, so if you forget to insert a PED Key, or if you insert the wrong kind (for example, if you insert a black key when a red key is called for), that is not logged as a failed attempt. Also, when you successfully login, the counter is reset to zero.
If you are not sure that you are currently logged in as HSM Admin, perform an ‘hsm logout’, then login again.